引言
2022年6月16日,Inverse Finance遭受攻击,损失超过100万美元。攻击交易为https://versatile.blocksecteam.com/tx/eth/0x958236266991bc3fe3b77feaacea120f172c0708ad01c7a715b255f218f9313c。根本原因是Inverse Finance使用的价格预言机被操纵。
攻击分析
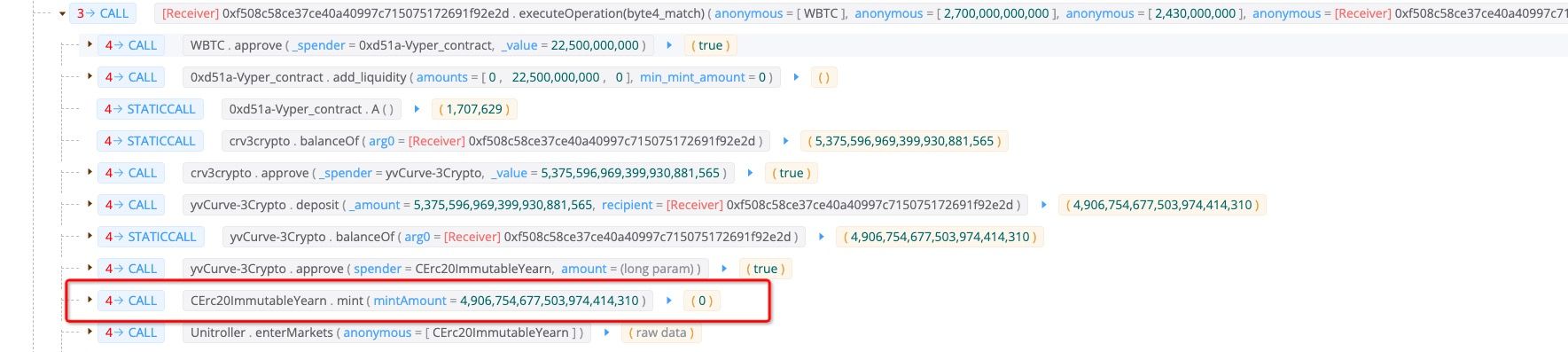
攻击者首先通过闪电贷从Aave借出27,000 WBTC。之后,将其中225枚存入Curve,并铸造了5,375枚crv3crypto。攻击者将这5,375枚crv3crypto存入yvCurve-3Crypto,获得了4,906枚Yearn cToken,这将作为Inverse Finance的抵押品。
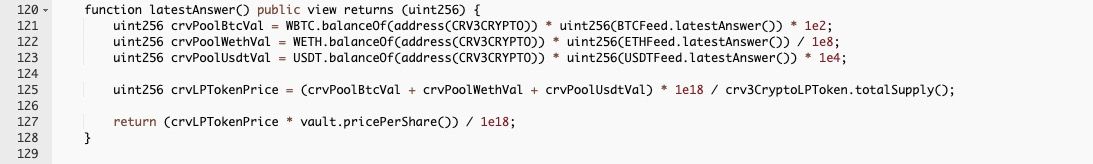
剩余的26,775 WBTC被用于操纵抵押品的价格。攻击者通过交易26,775 WBTC,获得了75,403,376 USDT。此次交易将预言机的价格从979抬升至2,831。

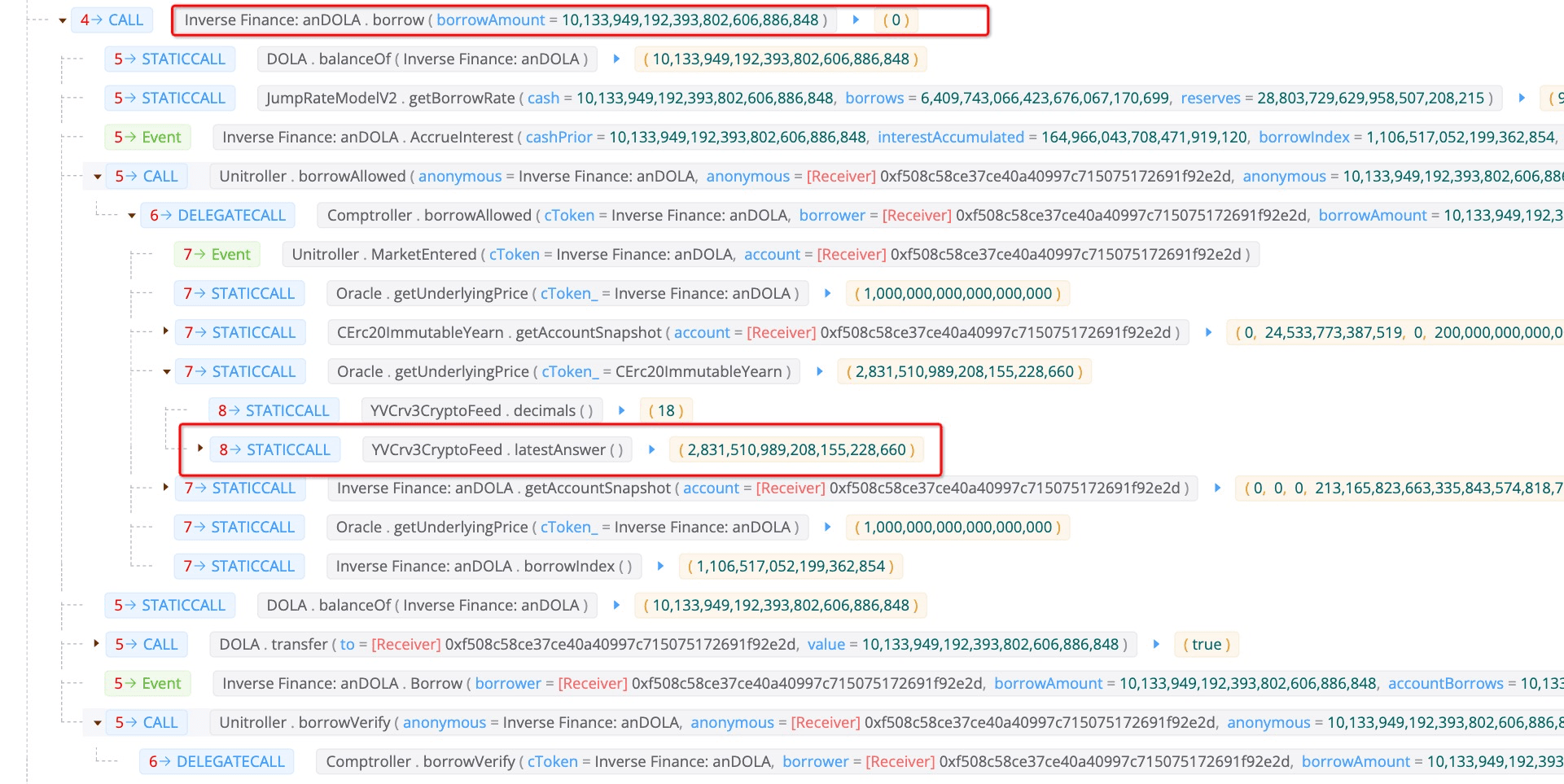
从borrowAllowed函数可以看出,它会检查用户是否可以用抵押品借入指定数量的代币。
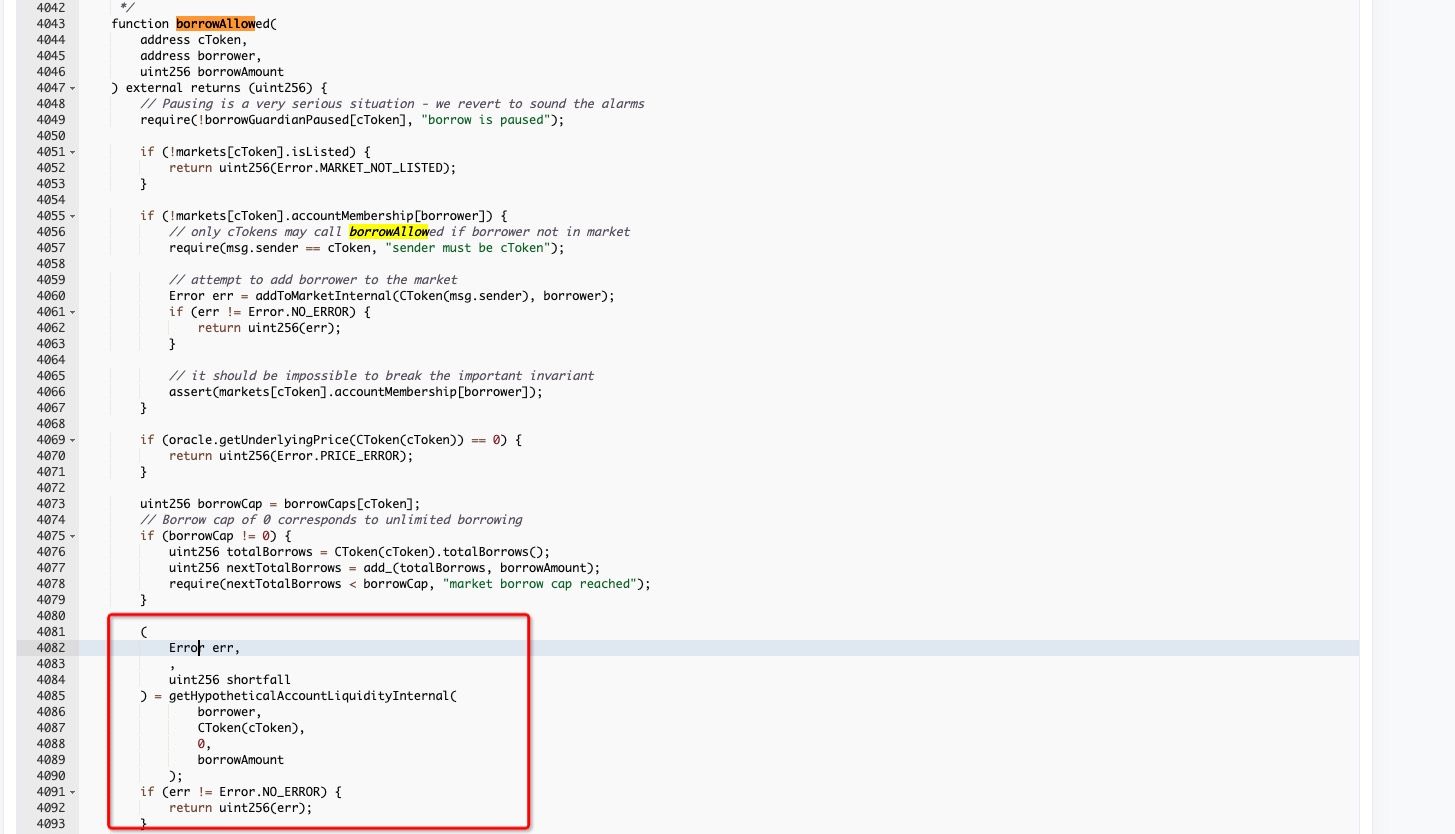
具体来说,getHypotheticalAccountLiquidityInternal函数用于检查借款行为是否安全。抵押品的价格是通过getUnderlyingPrice获得的。
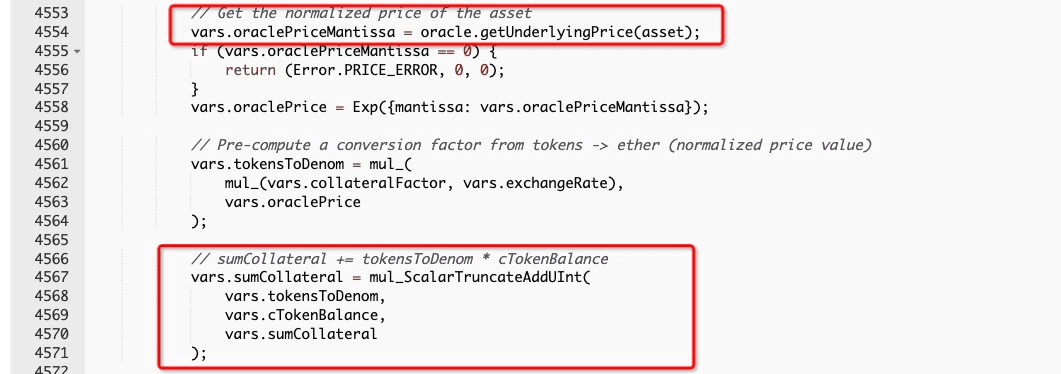
getUnderlyingPrice函数会调用latestAnswer来获取结果。如前所述,26,775 WBTC被用于交易USDT,从而抬升了抵押品的价格。
在这种情况下,攻击者可以借入大量(例如,10,133,949)DOLA,其价值超过了存入的抵押品。
最后,攻击者将75,403,376 USDT交易回2,662,649 WBTC,并将借来的10,133,949 DOLA交易为9,881,355 3Crv,然后将其从流动性池中取出,获得了10,099,976 USDT。
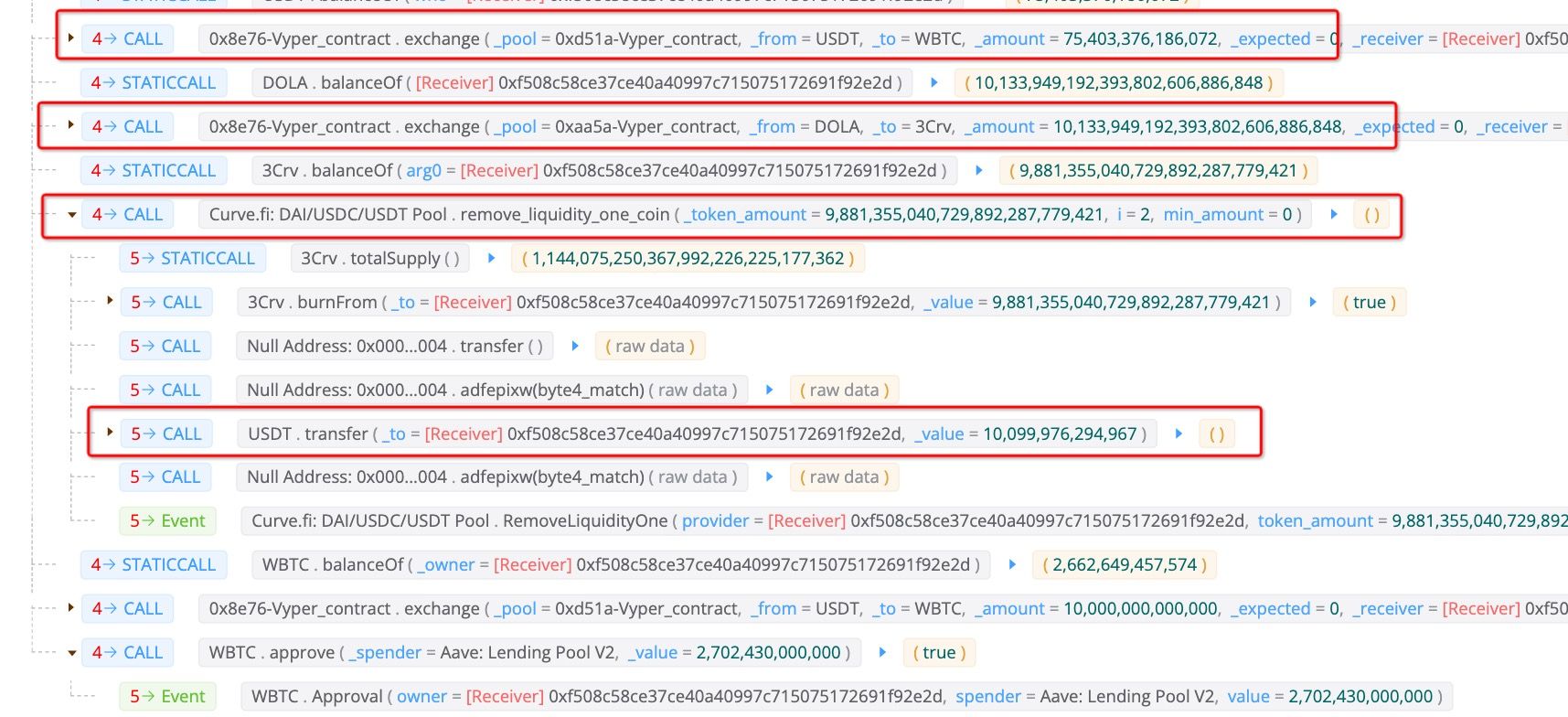
之后,将10,099,976 USDT中的10,000,000 USDT再次交易为WBTC,并用于偿还闪电贷。至此,攻击完成。攻击者从此次攻击中获利99,976 USDT和53.2 WBTC。

总结
这是一次典型的价格操纵攻击。令人惊讶的是,这种攻击在如今仍然发生,此次事件为DeFi协议加强安全系统敲响了警钟。
关于BlockSec
BlockSec是一家开创性的区块链安全公司,由一群全球顶尖的安全专家于2021年创立。公司致力于提升新兴Web3世界的安全性和可用性,以促进其大规模采用。为此,BlockSec提供智能合约和EVM链安全审计服务,Phalcon平台用于安全开发和主动威胁拦截,MetaSleuth平台用于资金追踪和调查,以及MetaDock扩展,帮助Web3开发者高效地探索加密世界。
至今,公司已服务超过300家知名客户,如MetaMask、Uniswap Foundation、Compound、Forta和PancakeSwap,并在两轮融资中获得Matrix Partners、Vitalbridge Capital和Fenbushi Capital等知名投资者的数千万美元投资。
官方Twitter账号:https://twitter.com/BlockSecTeam




