Wintermute 项目因私钥泄露损失超过 1.6 亿美元。其根本原因是 Wintermute 项目使用的 Profanity 工具存在漏洞,导致其用于生成私钥和以太坊账户的私钥被泄露。
在本博客中,我们将描述 Profanity 工具漏洞的根本原因以及该漏洞是如何被利用的。
以太坊地址
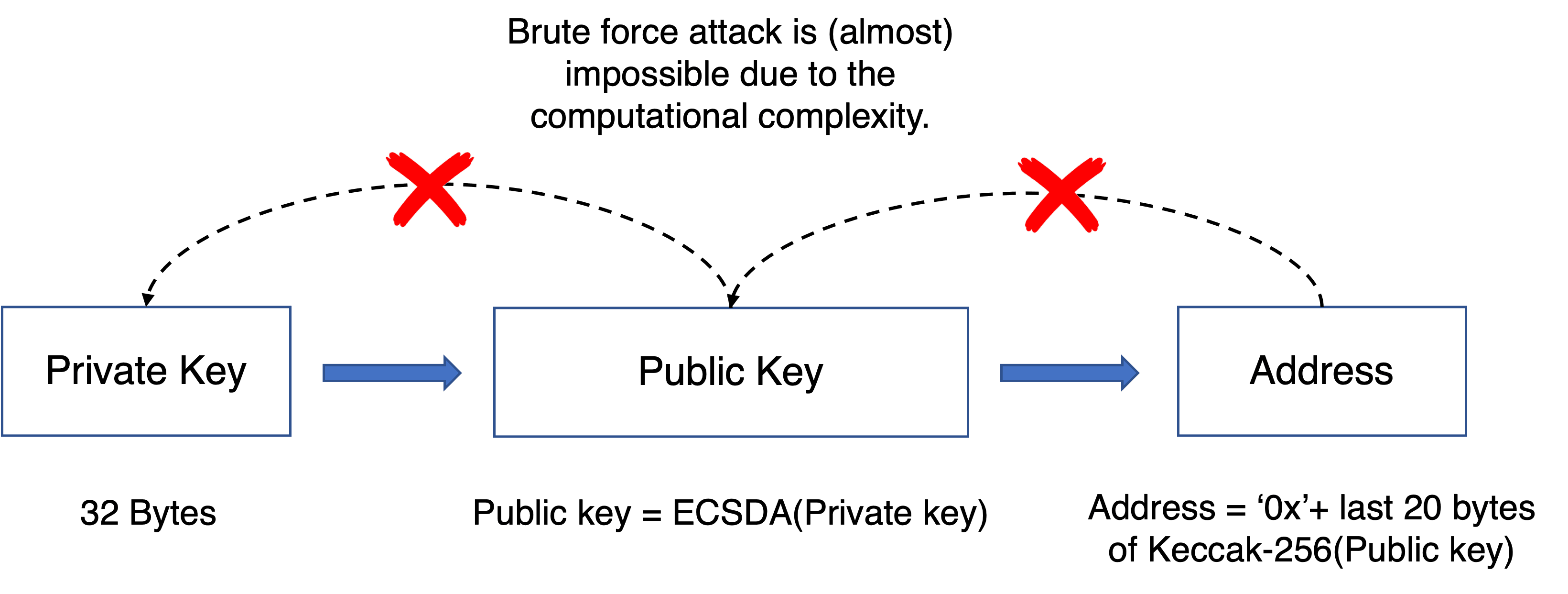
以太坊地址是通过对公钥进行 Keccak-256 哈希计算生成的,并以十六进制数字表示。公钥是通过椭圆曲线乘法从私钥生成的,这个过程是不可逆的。我们可以从私钥得到公钥,但无法在不进行暴力破解的情况下,仅根据公钥找到私钥。请注意,私钥的长度为 256 位。给定一个公钥,最多需要进行 2^256 次计算才能找到对应的私钥。
简而言之,私钥/公钥与以太坊地址之间的关系如下图所示。
漏洞的根本原因
Profanity 工具的目的是找到一个特殊的以太坊地址,例如地址的前导数字是零。为此,Profanity 采用了以下方法。
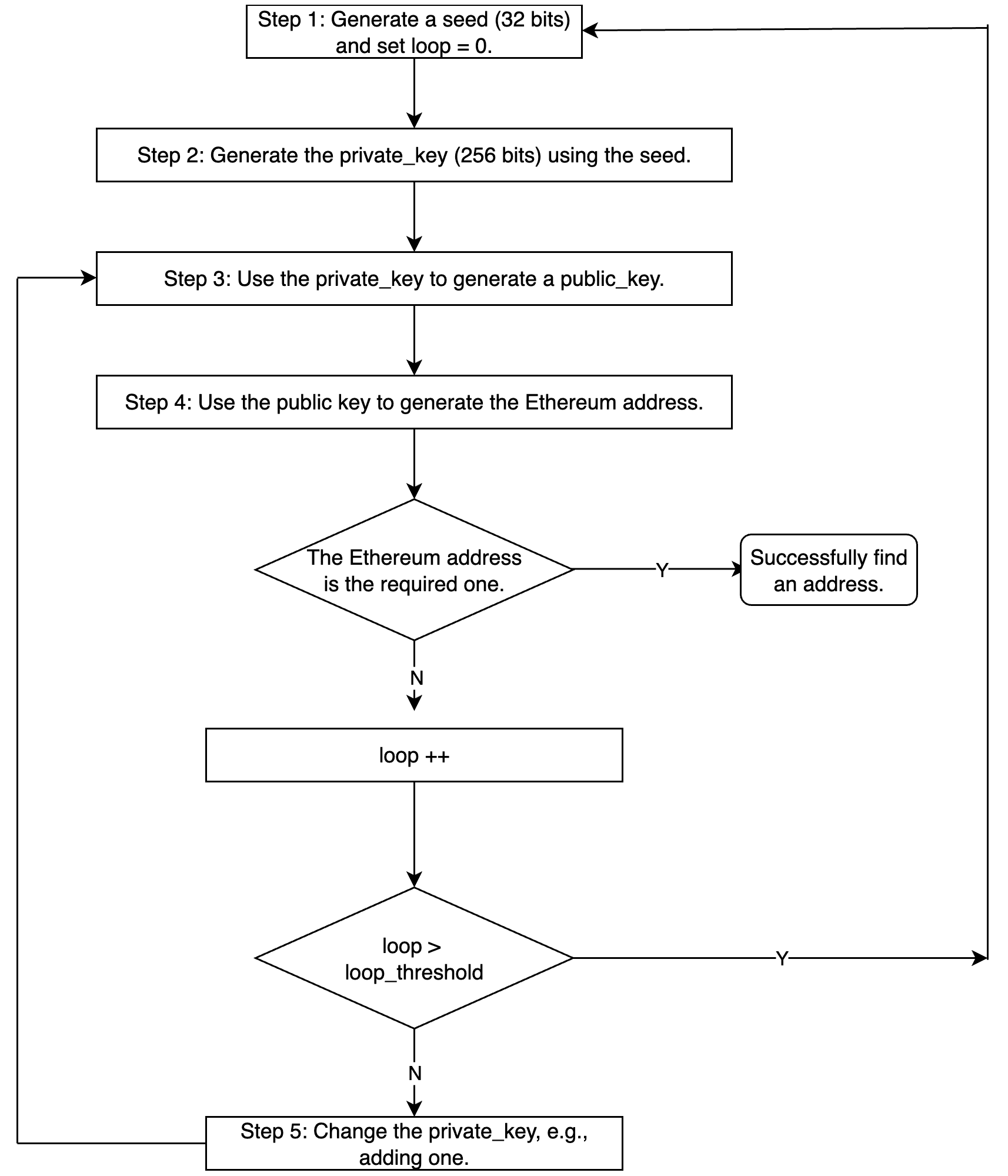
具体实现可能略有不同。
请注意,private_key 的长度是 256 位(2^256 种不同的值)。然而,在生成私钥的过程中存在漏洞。具体来说,种子(步骤 1)只有 32 位,而从种子(步骤 1)到 private_key(步骤 2)的过程是确定性的。
这带来了什么安全影响?
如何利用
假设我们有一个拥有大量有价值资产的以太坊地址。如果我们能获得其私钥,那么我们就可以控制该账户并将所有资产转走。然而,如前所述,我们必须在 2^256 的空间中进行暴力破解才能找到私钥,这几乎是不可能的。
但如果该以太坊地址是由 Profanity 工具生成的呢?我们可以以更低的难度进行暴力破解来定位私钥。我们只需要指定从 0 到 2^32-1 的种子,并重复相同的过程,直到找到可以生成相同公钥(和以太坊地址)的私钥。因为我们最多只需要 2^32 * loop_threashold 次计算。如果拥有强大的 GPU 集群,这可以在几个小时或几天/几周内完成。
但这仍然是一种优化算法。您可以参考 Slowmist 的文章了解更多细节。
总结
确保 DeFi 项目的安全并非易事。除了代码审计,我们认为社区应该采取积极主动的方法来监控项目状态,并在攻击发生之前就将其阻止。
关于 BlockSec
BlockSec 是一家开创性的区块链安全公司,由一群世界顶尖的安全专家于 2021 年创立。公司致力于提升新兴 Web3 世界的安全性和可用性,以促进其大规模采用。为此,BlockSec 提供智能合约和 EVM 链安全审计服务,用于安全开发和主动阻止威胁的Phalcon 平台,用于资金追踪和调查的MetaSleuth 平台,以及供 Web3 构建者高效浏览加密世界的MetaSuites 扩展。
迄今为止,公司已为 MetaMask、Uniswap Foundation、Compound、Forta 和 PancakeSwap 等 300 多家知名客户提供服务,并在两轮融资中从 Matrix Partners、Vitalbridge Capital 和 Fenbushi Capital 等知名投资者那里获得了数千万美元的投资。




