根据 LI.FI 项目的报告和 Daniel Von Fange 的推文,我们注意到 LI.FI 在 2022 年 3 月 20 日遭受了攻击。由于没有对该漏洞进行详细的技术分析,我们将在下面进一步分析此次攻击。我们发现这次攻击的根本原因在于未经检查的外部调用。
攻击交易
我们从攻击交易开始,来说明攻击过程。下面的截图展示了我们的交易可视化系统的分析结果。
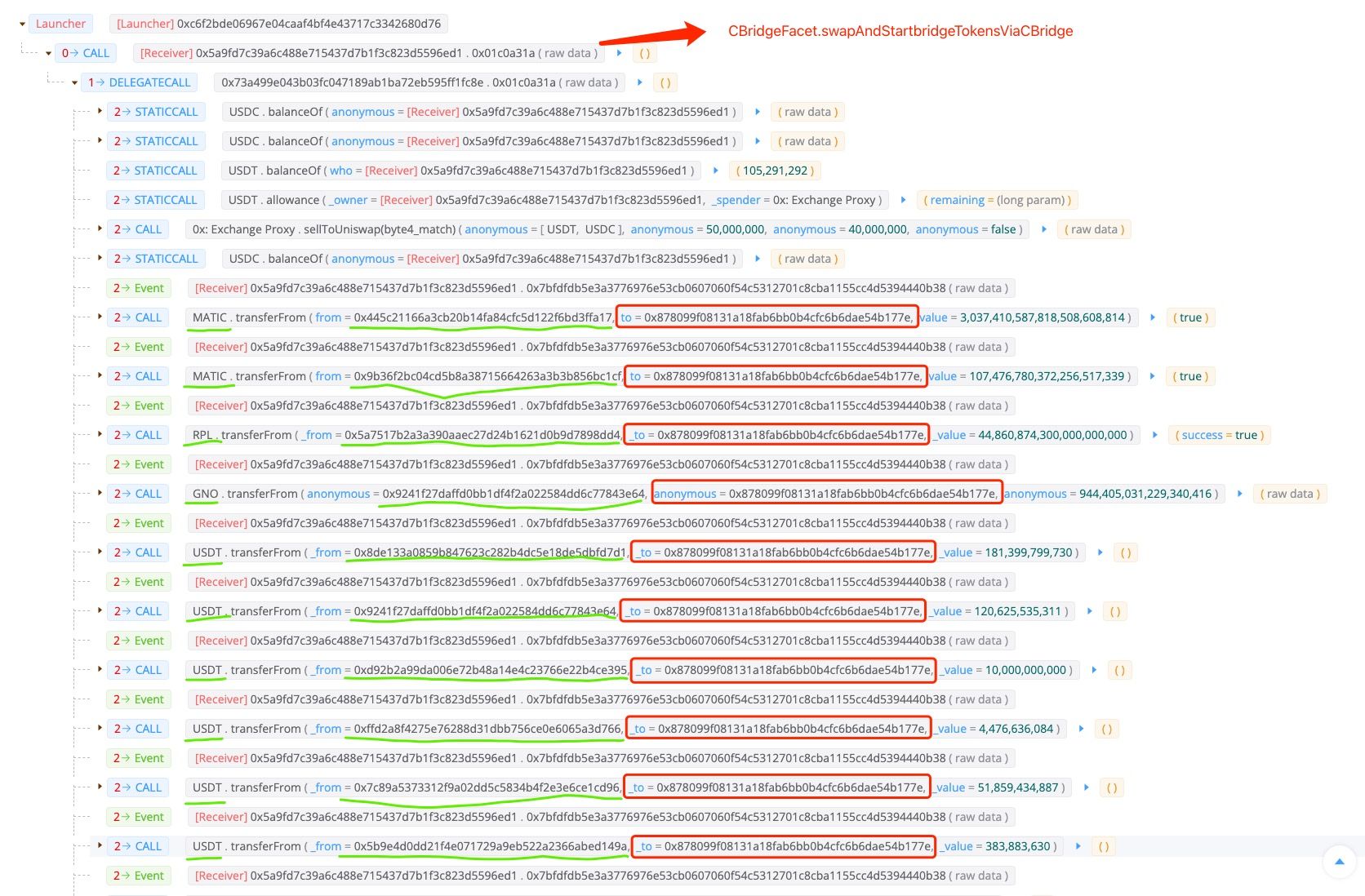
如上图所示,整个攻击过程相当简单,没有部署恶意智能合约,也没有涉及闪电贷。攻击者执行的唯一操作是调用 CBridgeFacet 合约中的 swapAndStartBridgeTokensViaCBridge(0x01c0a31a) 函数,该函数随后将各种代币(例如 USDC、MATIC、RPL、GNO、USDT、MVI、AUDIO、AAVE、JRT 和 DAI)从不同的支出方转移到由攻击者控制的EOA地址。
代码分析
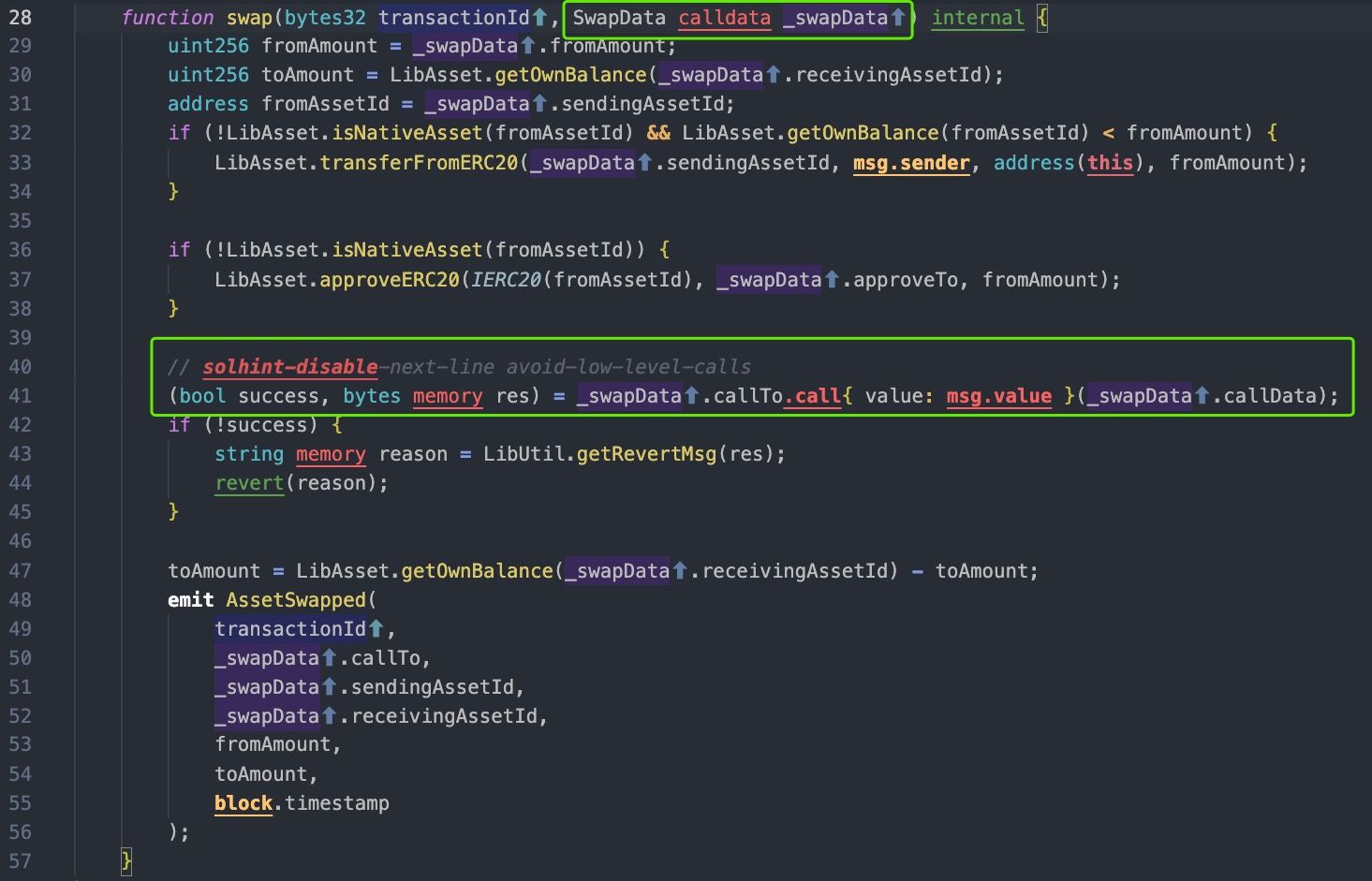
接下来我们深入研究受害者逻辑合约的代码。
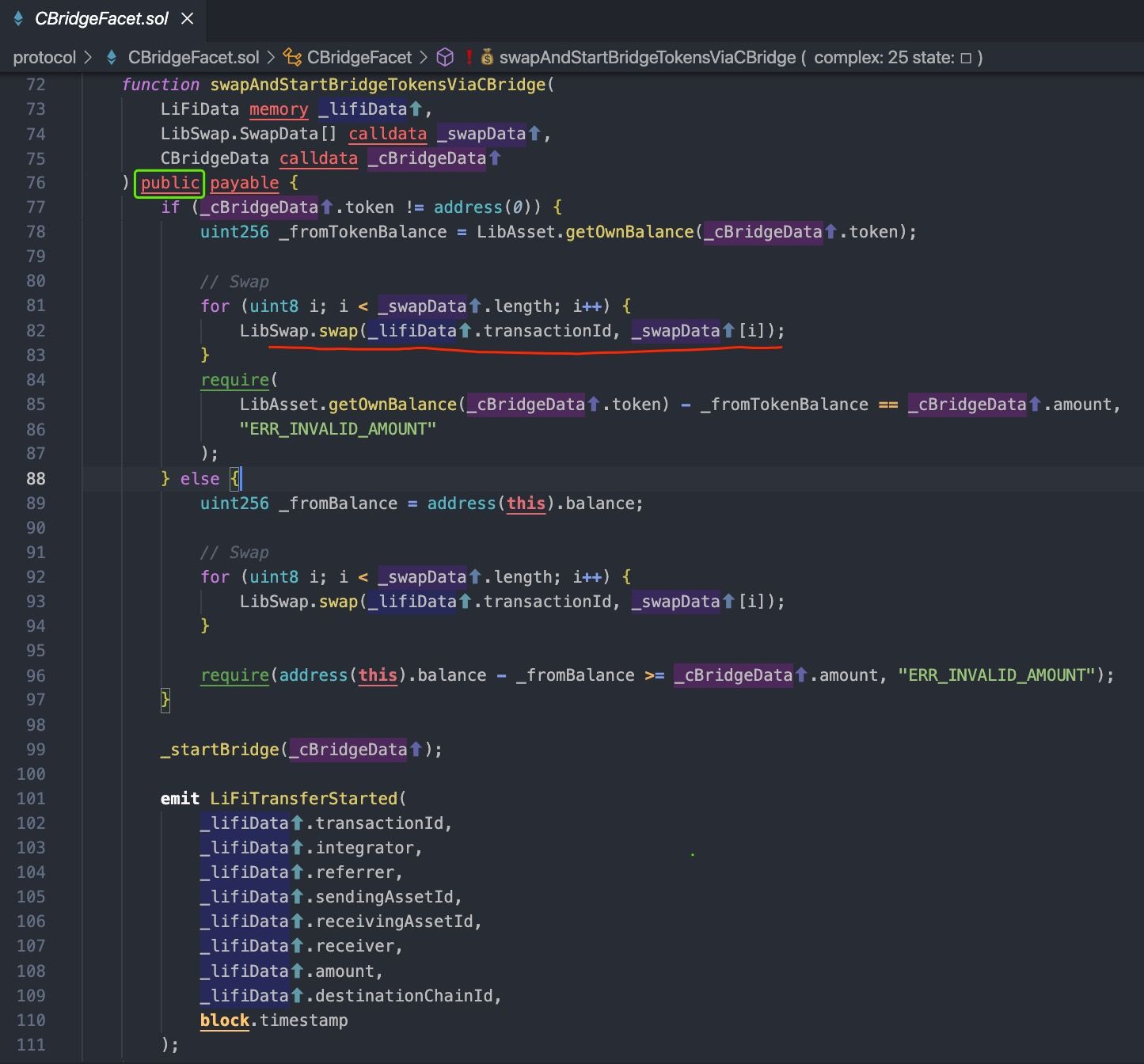
根据以上代码,swapAndStartBridgeTokensViaCBridge 是源链上跨链交易的入口。
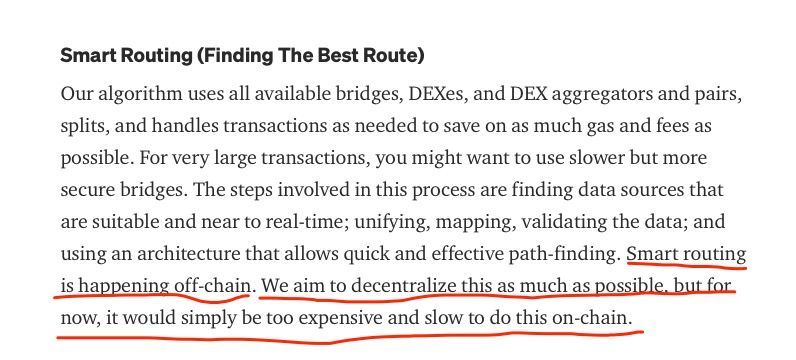
LIFI 项目声称他们能够为用户找到最佳路线,称为 Smart Routing,这是在链下发生的。特别是,前端网站会计算最佳路线,并将参数(包括交换合约和路由路径)编码到 swapAndStartBridgeTokensViaCBridge 函数的参数中。
显然,LIFI 项目没有考虑到该函数可以被区块链上的任何账户调用,因为该函数不对参数进行任何检查,例如白名单和滑点。最严重的问题是 CBridgeFacet 合约要求用户授权代币,这使用户的资金面临风险。
收益
因此,攻击者通过调用 swapAnStartBridgeTokensViaCBridge 函数,窃取了 LIFI 用户授权代币给 CBridgeFacet 合约的资金,然后该函数调用了不同代币的 transferFrom 函数。损失统计如下表所示。总损失约为 59.6 万美元,与 LIFI 项目的统计数据基本一致。
| 代币 | 金额 | 价格 |
|---|---|---|
| GNO | 0.94 | 310.22 |
| USDC | 202,012.28 | 0.999655 |
| MATIC | 3,144.89 | 1.46 |
| AUDIO | 1,202.37 | 1.10 |
| AAVE | 8.99 | 149.99 |
| RPL | 44.86 | 31.2 |
| MVI | 22.95 | 131.82 |
| USDT | 368,745.29 | 1 |
| DAI | 8,421.49 | 0.999847 |
| JRT | 136,805.06 | 0.03789613 |
教训
LIFI 是一个跨链桥聚合器,受害者合约是跨链转移的入口。漏洞并非由于复杂的跨链逻辑,这在之前的跨链桥安全事件中已经有所体现。相反,这次攻击的根本原因在于未经检查的外部调用,这是 Solidity 中最常见的 10 个问题之一。
随着 DeFi 项目变得越来越复杂,项目开发者在编写正确的业务代码之余,还需要更加关注编写安全的代码。我们强烈建议项目不要在区块链上部署未经审计的合约。
关于 BlockSec
BlockSec 是一家开创性的区块链安全公司,于 2021 年由一群全球杰出的安全专家创立。公司致力于增强新兴 Web3 世界的安全性和可用性,以促进其大规模采用。为此,BlockSec 提供智能合约和 EVM 链安全审计服务、用于安全开发和主动拦截威胁的 Phalcon 平台、用于资金追踪和调查的 MetaSleuth 平台,以及用于 Web3 构建者高效浏览加密世界的 MetaDock 扩展。
迄今为止,公司已为 MetaMask、Uniswap Foundation、Compound、Forta 和 PancakeSwap 等 300 多家知名客户提供服务,并已从 Matrix Partners、Vitalbridge Capital 和 Fenbushi Capital 等知名投资者那里获得了两轮数千万美元的融资。




