Solana 是一个快速且可扩展的区块链网络,在加密货币领域广受欢迎。
作为 Solana 用户,您可能出于各种原因想要追踪钱包的活动和交易,例如监控您的持有量、验证近期交易或调查可疑活动。有时您也想追踪 Solana 中的“智能资金”。
一种方法是使用 Solscan。然而,Solscan 只能显示一个跳数的 SoL 或 SPL 代币转移。如果您想追踪更多跳数,它将无法帮助您。
MetaSleuth 是一个有效的工具,可以追踪 Solana 钱包和资金在多跳数的流动。它支持超过 20 种不同的链和跨链交易。
输入地址开始
要开始追踪钱包,请打开 MetaSleuth 的网站 (https://metasleuth.io) 并输入一个地址开始追踪。
让我们以地址 9wAfrMnzrJ1XWXXDDmqh7gH7Q9ZBJjLhgou5GrUcHsZy 为例,输入地址并按回车键。该工具将进行智能分析,显示初始结果(如下图所示)。
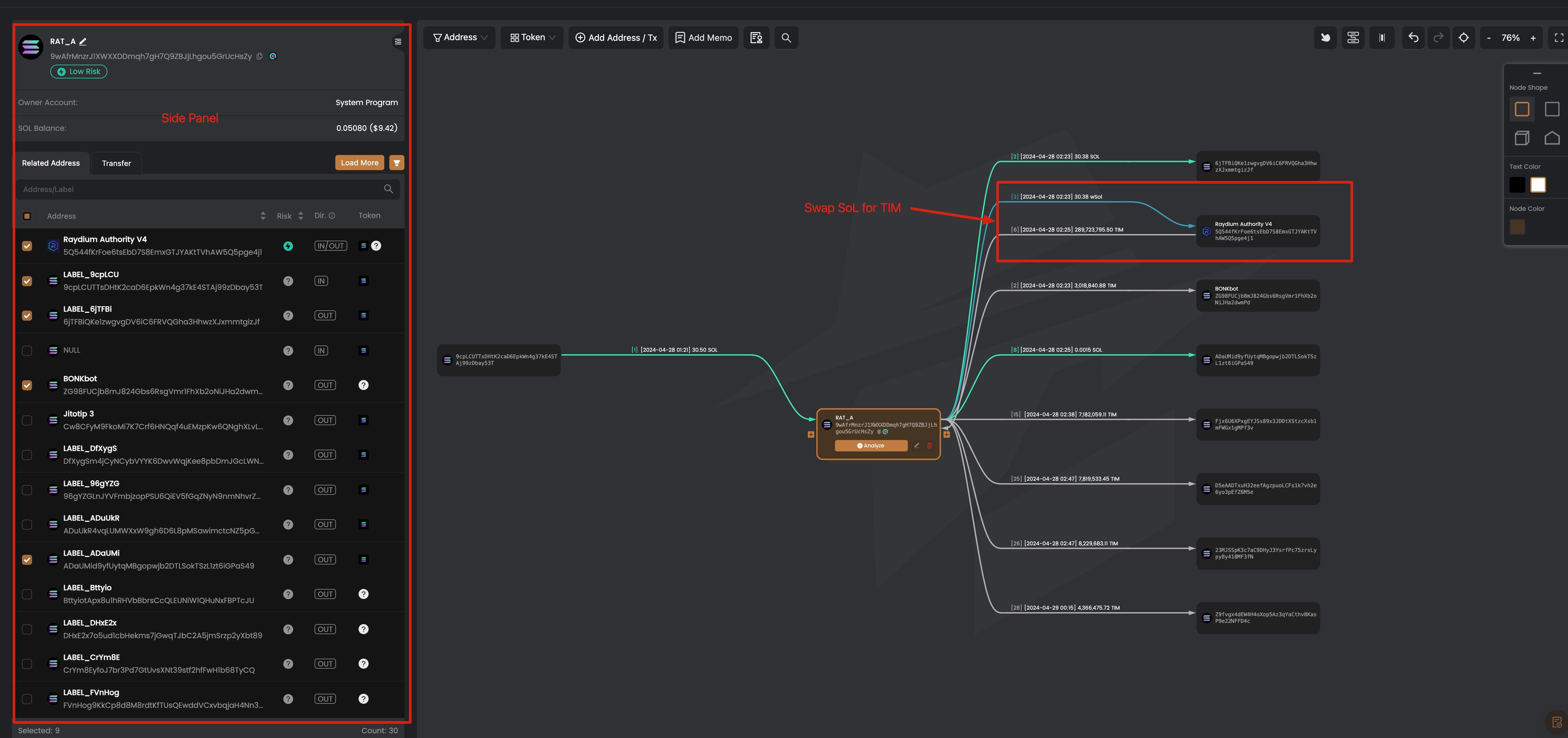
左侧是地址的侧边栏,当您在主画布上单击一个地址时会显示。主画布上的节点代表一个地址,节点之间的边表示每个代币的聚合代币转移。这意味着如果两个节点之间有多个交易来转移一个代币,它们之间将只有一条边。您可以单击边来查看代币转移的详细交易。
结果显示了 Raydium 中的代币兑换,其中有 30.38 wSoL 流入,288,723,795.50 TIM 流出。正如我们刚才所说,边表示聚合的代币转移。我们可以单击边来查看更详细的信息。
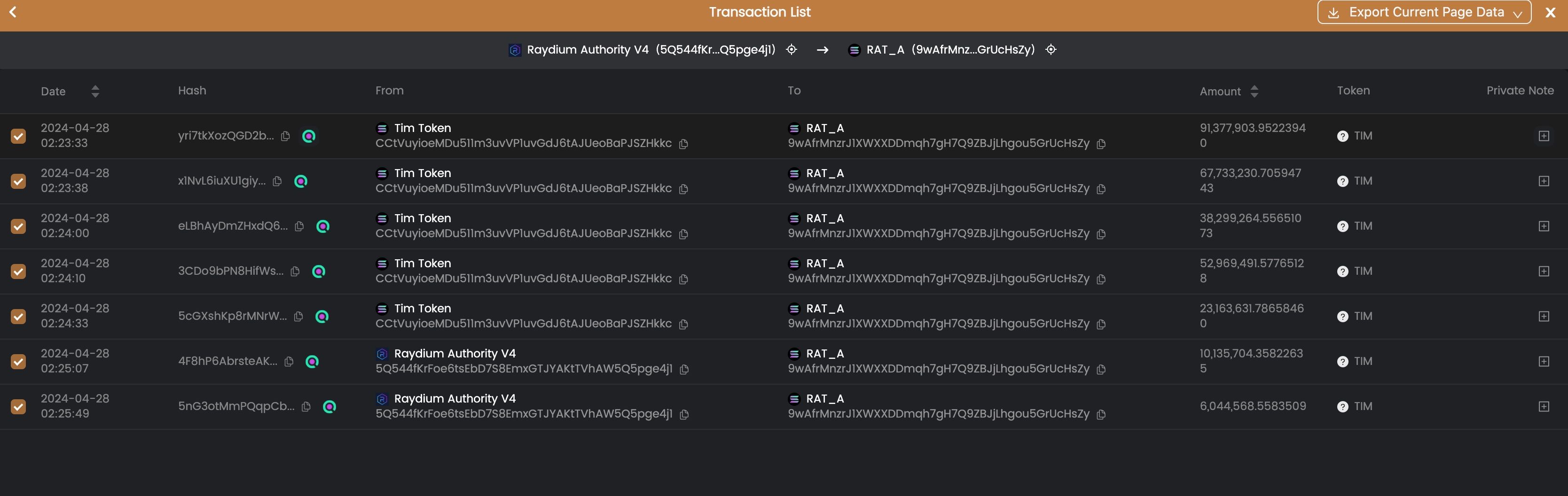
从交易列表中,我们可以看到 9wAfr 在 04-28 02:33:33 到 04-28 02:25:49 的两分钟内,使用 30.38 SoL 兑换了 288,723,795.50 TIM 代币。
追踪资金流动
在收到 TIM 代币后,地址 9wAfr 想要出售 TIM 代币以获利。它没有直接使用 9wAfr 地址出售代币,而是使用了三层地址来隐藏踪迹。这是如何实现的?
要追踪资金流动,我们首先找到从地址 9wAfr 转出的 TIM 代币。我们可以单击地址 9wAfr 来显示侧边栏,并选择所有输出的 TIM 代币。
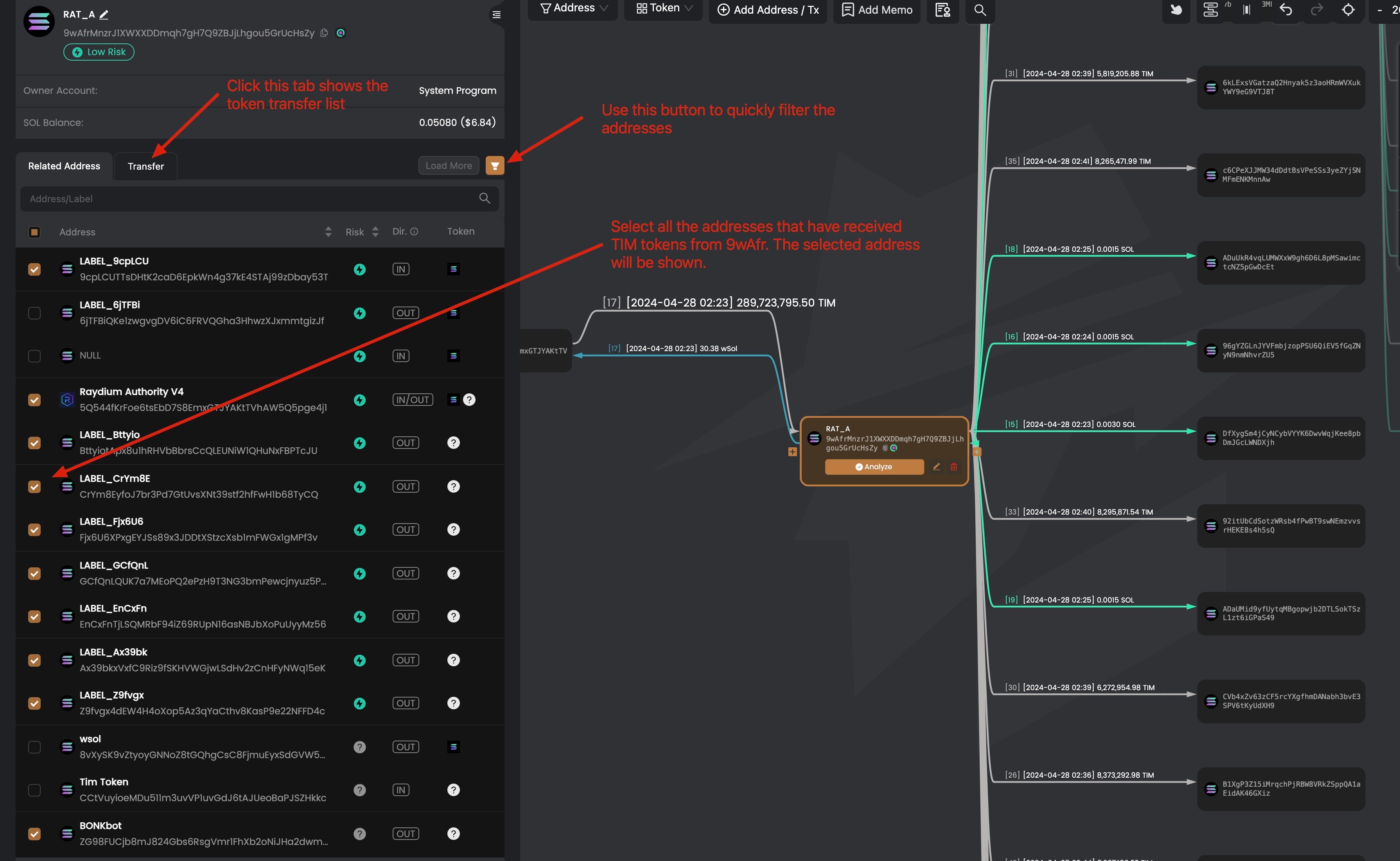
在选择了接收 TIM 代币的地址后,我们可以单击该地址的节点来进一步追踪代币流动。例如,我们可以单击地址 Ax39bkxVxfC9Riz9fSKHVWGjwLSdHv2zCnHFyNWq15eK,发现该地址将收到的 TIM 代币兑换成 SoL,并将 SoL 转账给 DJGiuwGs1WtC1QkEj3GkGtdVoXuEk34uwWmvQvLi72SZ。
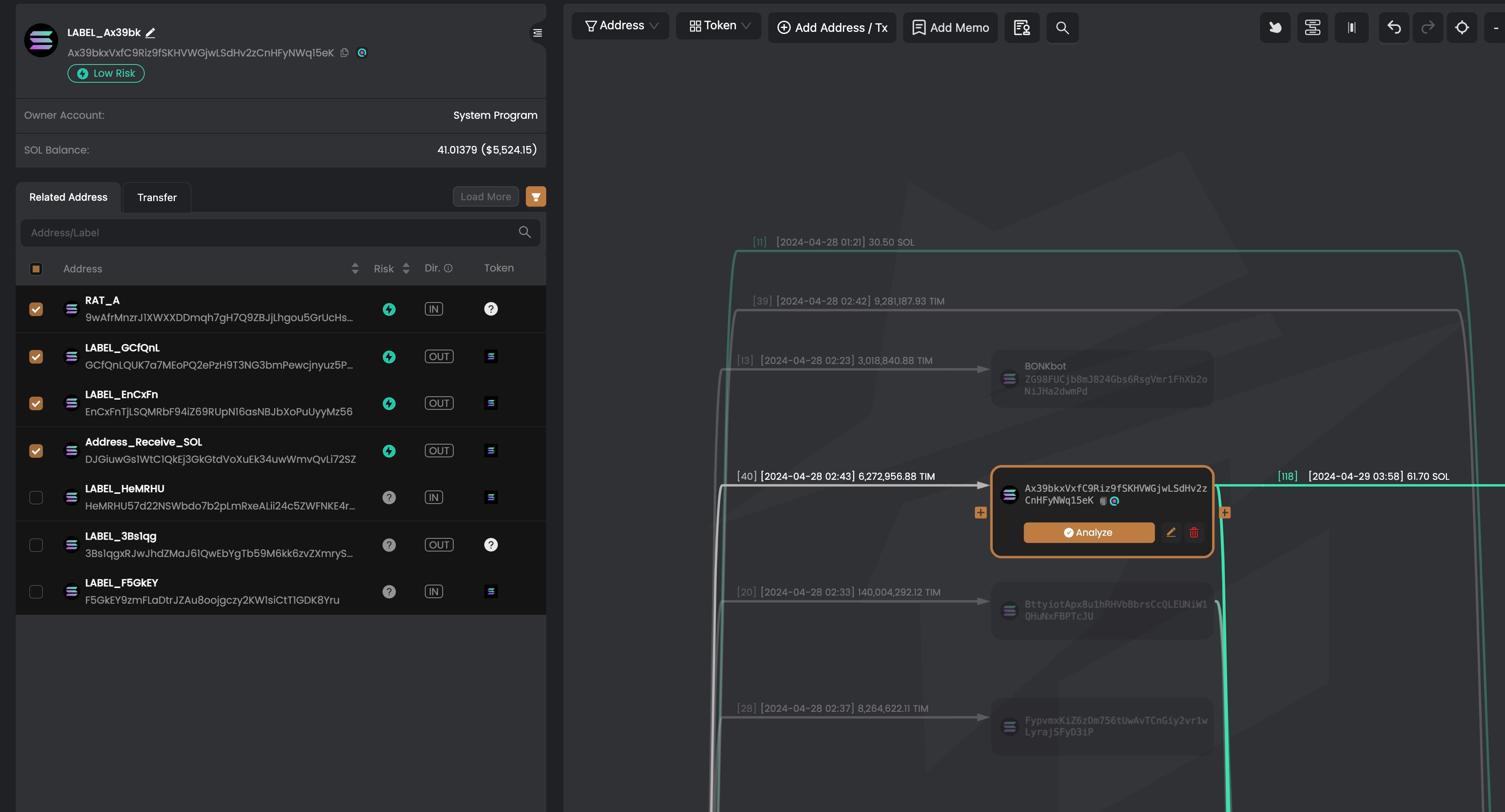
我们可以使用类似的方法追踪其他从 9wAfr 接收 TIM 代币的地址。
订阅并享受 10% 折扣
注册 MetaSleuth 时,使用 BLOCKSEC 作为邀请码,即可享受 10% 的订阅折扣。
https://metasleuth.io/?invite-code=BLOCKSEC





