什么是 Four.meme
Four.meme 是一个在 BNB Chain 上的公平启动平台,它取消了 memecoins 的预售、种子轮和团队分配,确保每个人都能在公平的起点参与。该平台利用 BNB Chain 低成本的交易和强大的基础设施,提供了多代币交易、流动性激励和社区驱动计划(空投、推荐等)等功能,简化了发现、启动和投资新 memecoins 的流程。
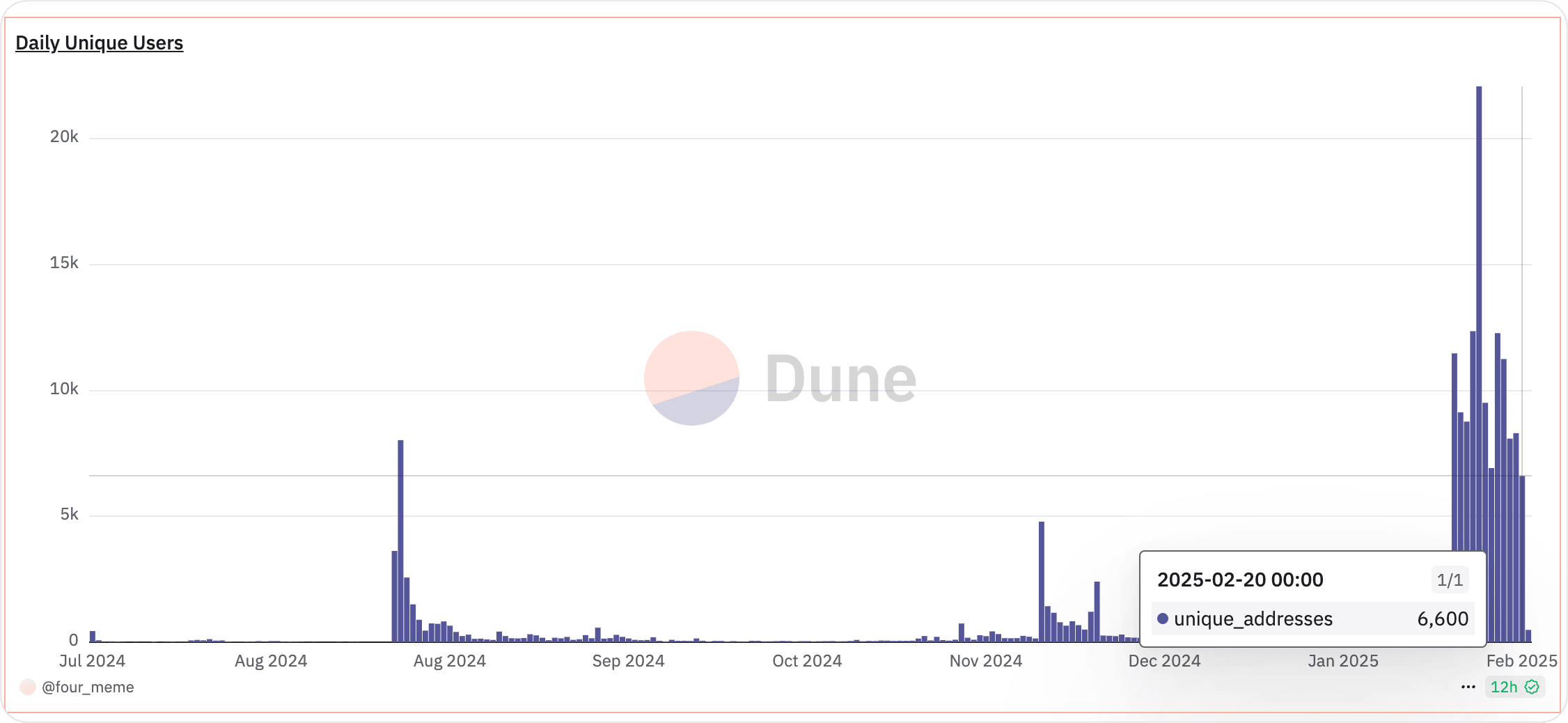
此外,如下所示,其交易量最近不断创下新高,反映出其日益增长的受欢迎程度。
三明治攻击
与此同时,三明治攻击日益增多,恶意交易者利用区块链的交易排序来最大化自身利润,而牺牲不知情的用户。
三明治攻击的原理
在三明治攻击中,攻击者会扫描内存池(mempool)寻找一个大型或有影响力的交易。然后,他们迅速在该目标交易之前插入一个交易(抢跑,front-running),推高价格,让受害者的交易以不利的价格执行,最后立即在受害者交易之后插入另一个交易(跟跑,back-running),以当前被抬高的价格出售。这种交易的“三明治”让攻击者能够赚取价格差。
真实案例
在接下来的部分,我们将使用一个最近发生的真实案例。
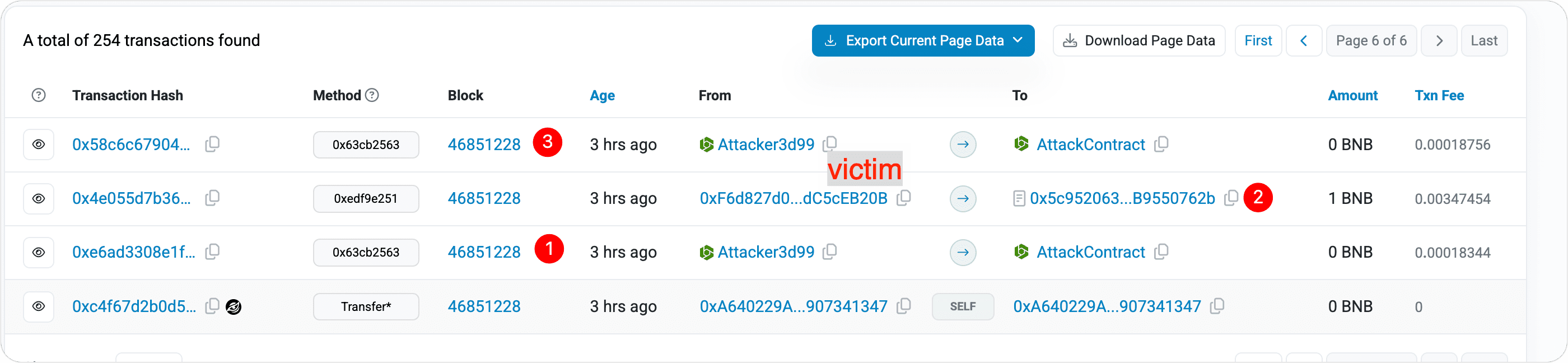
交易 1 (Tx1)
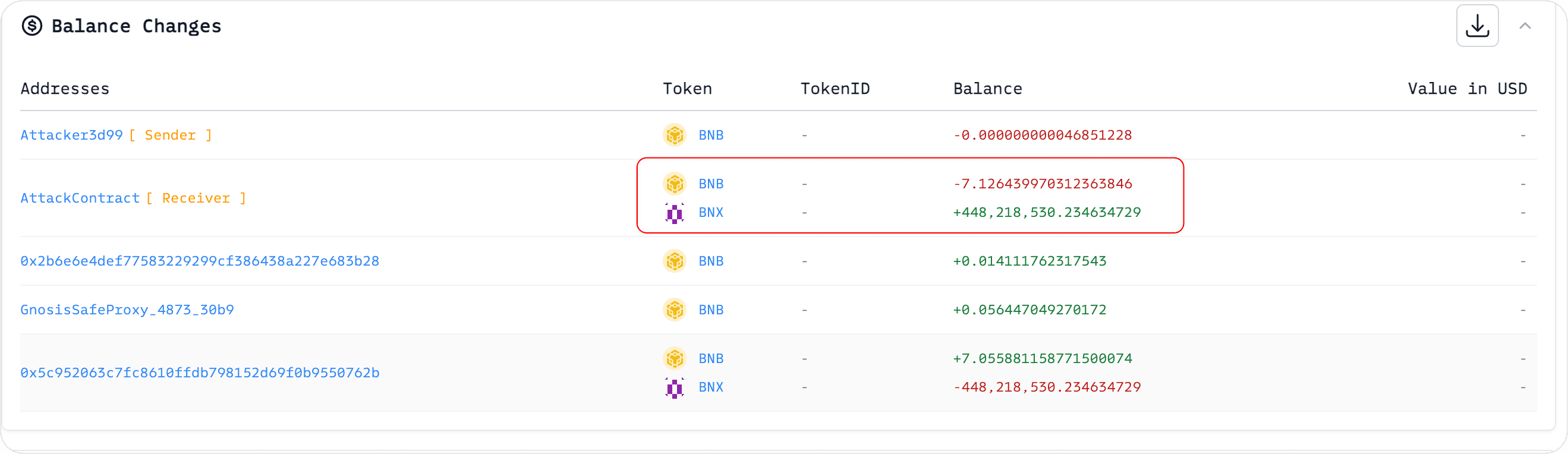
攻击者在得知受害者打算购买 BNX 后,提前花费 7.126439970312363846 BNB,预先购买了 448,218,530.234634729 个 BNX 代币。
交易 2 (TX2)
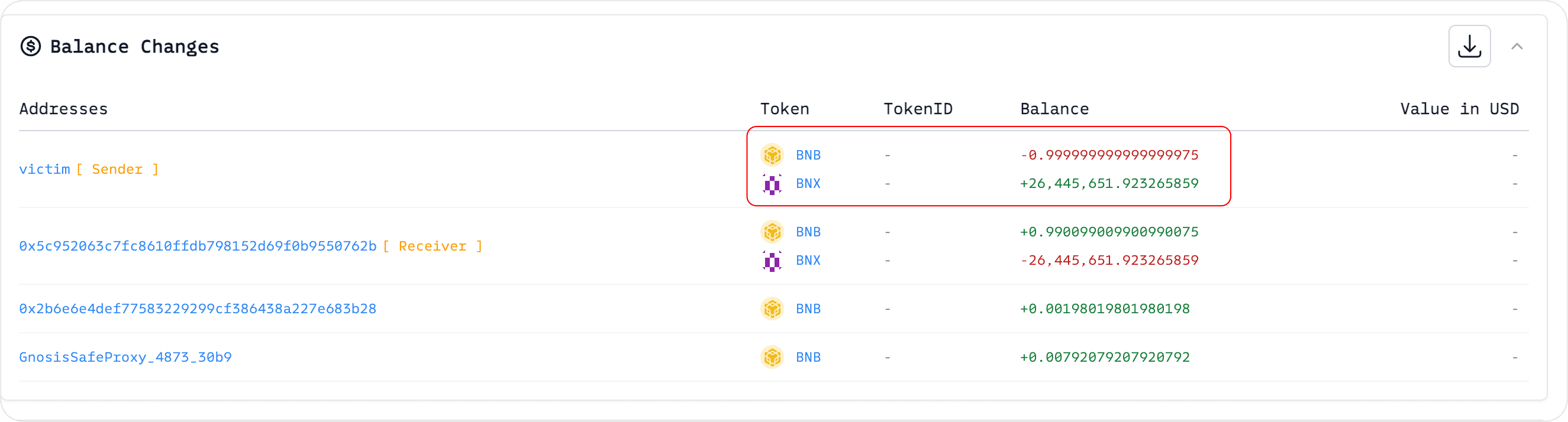
受害者花费 1 BNB 购买了 26,445,651.923265859 个 BNX 代币。
交易 3 (TX3):
由于受害者使用 BNB 购买推高了 BNX 的价格,攻击者随后以更高的价格出售 BNX 以获利。通过这次三明治攻击,攻击者获得了 7.130040296271196866 BNB - 7.126439970312363846 BNB = 0.00360032595883302 BNB 的利润。
在此情景下,受害者(钱包地址 0xf6d827d0a4ee02a424ec85a3bcb8dc7dc5ceb20b)最终为 BNX 支付了更高的价格,因为如果没有攻击者的第一笔交易,受害者本可以以更低的价格购买 BNX。
如何避免成为三明治攻击的受害者
为了规避三明治攻击,关键在于阻止攻击者在您的交易被包含在链上之前探测到它。一种有效的方法是,通过私有中继(private relays)或受保护的内存池(protected mempools)提交交易,这些交易在被最终确定在区块中之前是隐藏的。这使得恶意行为者更难抢跑和跟跑您的交易。
为了解决这个问题,BlockSec 推出了一个 MEV 保护 RPC,为用户在整个 DeFi 之旅中提供保护。切换到 BlockSec 的 ANTI-MEV RPC 非常简单——只需将您钱包的 RPC 替换为 https://bsc.rpc.blocksec.com。
下面,我们将演示如何配置 MetaMask 使用 BlockSec 的 ANTI-MEV RPC;其他钱包的设置过程也可能类似。
步骤 1:点击左上角显示网络。

步骤 2:编辑网络

步骤 3:点击添加 RPC URL


对于 BSC,输入 https://bsc.rpc.blocksec.com(或对于以太坊,输入 https://eth.rpc.blocksec.com)。
确保默认的 RPC URL 是我们刚刚设置的那个。

总结
三明治攻击会增加不知情交易者(尤其是在 Four.meme 这样的炒作驱动的环境中)的代币成本。攻击者会抢跑待处理的交易并快速出售以获利,导致受害者支付更高的价格。
通过切换到 BlockSec 的 anti-MEV RPC (https://bsc.rpc.blocksec.com),您可以将您的交易数据隐藏在这些恶意机器人之外。这种方法降低了三明治攻击的风险,让您可以在 Four.meme 上更安全地进行交易。



