DeFi 黑客攻击仍在发生。对于 DeFi 项目被盗的资金,通常很难追回。一些项目方通过与黑客协商,提供赏金并承诺放弃法律诉讼。这有时确实有效,但树立了一个坏榜样。这似乎是在鼓励人们通过黑客攻击来获取赏金,而不是进行负责任的沟通。
BlockSec 采取了不同的方式来帮助多个项目追回被盗资金。除了追踪资金流向并配合中心化实体(如交易所)等常规手段外,我们希望分享三个纯粹通过技术手段追回被盗资金的成功案例,包括最近的 Platypus Finance、TransitSwap 和 Saddle Finance。
Platypus Finance:成功挽救 240 万美元
The Block 对我们如何帮助 Platypusdefi 追回资金进行了详尽报道。简单来说,攻击者犯了一个错误,即无法将资金从攻击合约中移出。这是因为攻击者忘记编写将代币从攻击合约中转出的代码逻辑。
然而,我们的团队发现,可以通过利用攻击合约中的现有代码,将 USDC 从攻击合约转移到该项目的合约中。本质上,攻击者合约中有一个函数,一旦被调用,攻击合约就会批准向项目合约转入固定数量的 USDC。这段代码原本是为攻击目的而编写的。但我们可以重用这段代码逻辑将 USDC 批准给项目合约,然后升级项目合约(它是一个代理合约),从而将 USDC 从攻击者合约中移出。
我们通过概念验证(PoC)评估了这个想法,并与 Platypusdefi 分享了相关信息。我们与他们保持密切合作,这种方法奏效了!在随后的交易中,240 万 USDC 被成功追回。
- https://phalcon.blocksec.com/explorer/tx/avalanche/0x5e3eb070c772631d599367521b886793e13cf0bc150bd588357c589395d2d5c3
- https://phalcon.blocksec.com/tx/avax/0x5e3eb070c772631d599367521b886793e13cf0bc150bd588357c589395d2d5c3
我们已成功从被攻击的合约中追回了 240 万 USDC: https://t.co/lpDYQtu9bf
— Platypus 🔺 (🦆+🦦+🦫) (@Platypusdefi) 2023年2月17日
我们要感谢 @BlockSecTeam 在帮助我们实现这一成功结果中所付出的时间和努力。我们衷心感谢他们的协助!
TransitSwap:成功挽救 24.6 万美元
BSC 上的 TransitSwap 于 2022 年 10 月 1 日遭到攻击。一些攻击交易被一个 机器人 (Bot) 抢先交易(Front-run)。
然而,我们发现这个机器人容易受到 Profanity 工具漏洞 的影响。该漏洞是由于生成私钥时随机性不足导致的。我们开发了一个工具,可以恢复此类易受攻击地址的私钥。
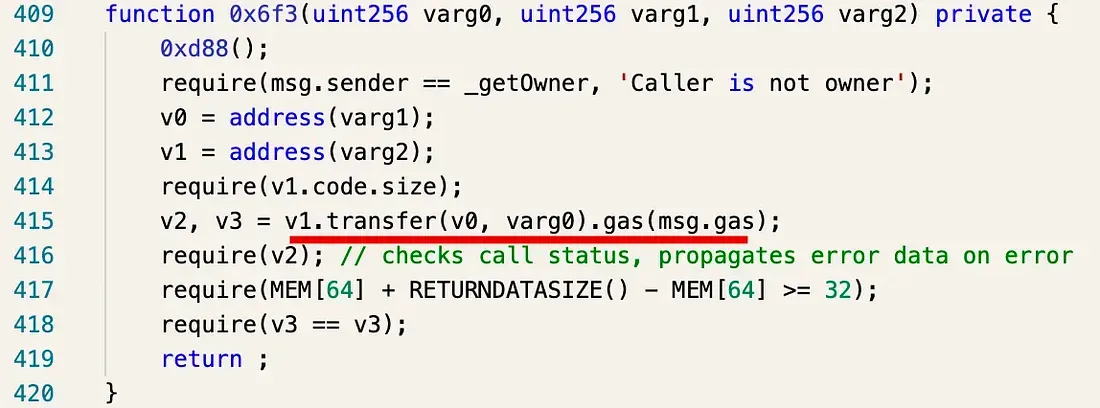
我们成功找回了该机器人的私钥。由于资金位于机器人合约中而非外部账户(EoA)内,我们设法反编译了该合约,并找到了一个可用于转移资金的函数。
我们已将资金转移至 TransitFinance 官方资金接收地址。
📢📢📢 关于 TransitFinance 的更新
— Transit Swap | Transit Buy | NFT (@TransitFinance) 2022年10月6日
在 BlockSec @BlockSecTeam 的帮助下,第 4 位攻击者盗取的约 24.6 万美元已全额退还。https://t.co/G7iB3JvspP
阅读更多关于 我们如何为 TransitSwap(及 BabySwap)追回被盗资金
Saddle Finance:成功挽救 380 万美元
对于 Saddle Finance,我们采取了另一种方式进行救援。其基本理念是:监听以太坊的待处理交易池(Pending Pool),通过我们的交易预执行系统 Mopsus 检测攻击交易,并通过自动合成救援交易来阻止攻击,将易受攻击的资产转移至我们的安全账户中,并利用 FlashBot 抢先于攻击交易执行。下图展示了其架构:
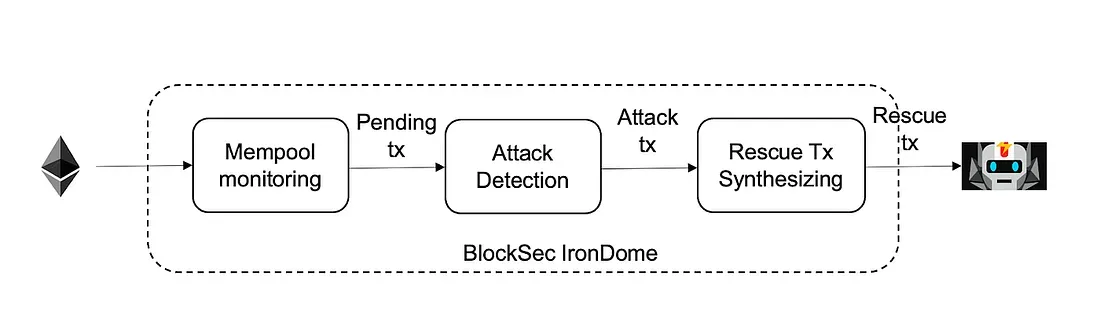
下表展示了我们的系统如何在 2022 年 4 月底 为 Saddle Finance 挽救了 380 万美元。特别值得一提的是,我们的系统在不到一秒的时间内就完成了检测攻击交易并自动合成救援交易的全过程。我们将所有挽救回来的资金都返还给了 Saddle Finance。点击链接查看 原始攻击交易 和 我们的救援交易。
阅读更多:通过主动威胁预防保护 Web3 安全
总结
以上三个案例仅仅是代表性案例。事实上,我们还有更多成功追回资金的案例。
我们始终认为,DeFi 的安全性不能通过单一方法论来解决。没有所谓的“银弹”。BlockSec 已经开发了一系列工具(并将继续开发更多)和服务,以帮助保护整个生态系统。我们拥有 Phalcon(区块链交易浏览器)、安全代码审计服务(涵盖 Solidity、Rust、Go 和 Move 语言)以及 主动攻击缓解服务。我们还为加密货币用户构建了多种打击网络钓鱼攻击的工具,包括加密资产分析工具 MetaSleuth,以及区块链浏览器插件 MetaSuites。我们 持续向 MetaMask 和 Etherscan 举报钓鱼网站及地址。为了保护整个加密生态系统的安全,BlockSec 还与 Cronos、Forta、Tokenlon、KeyStone、Goplus 等合作伙伴进行了协作。
如果您有任何问题,请随时联系我们。
了解更多有关 BlockSec 的信息: 官网 | 文档 | 推特 | 博客 | Telegram 群组



