我们在 @AkuDreams 合约中发现了两个严重逻辑漏洞: https://etherscan.io/address/0xf42c318dbfbaab0eee040279c6a2588fa01a961d
第一个漏洞可能导致拒绝服务 (DoS) 攻击,第二个漏洞将导致项目资金(超过 3400 万美元)被永远锁定。
漏洞 I
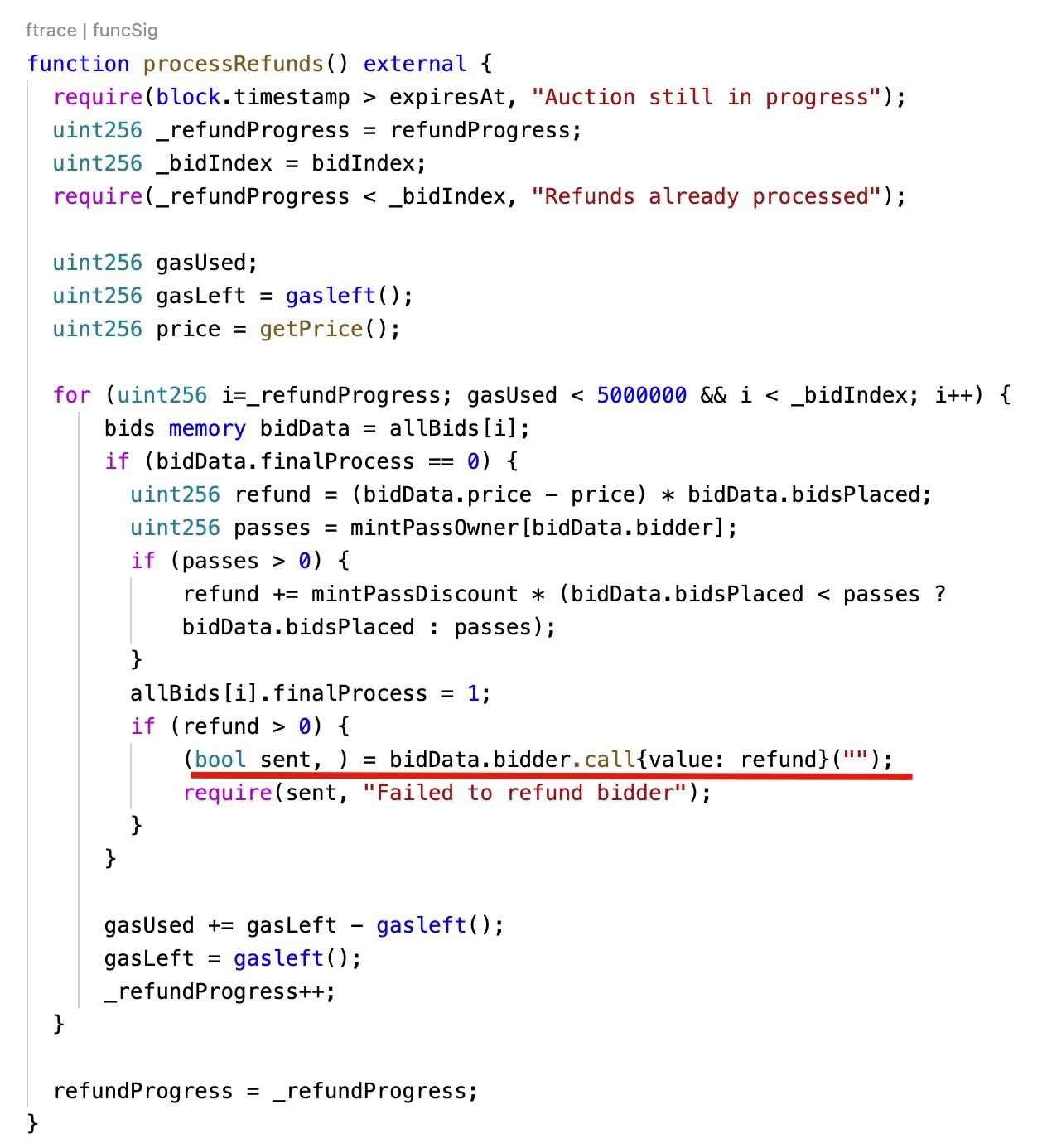
第一个漏洞存在于 processRefunds 函数中。该函数包含一个循环,用于退还每个竞拍用户的资金。然而,竞拍者可能是一个恶意合约,会回滚交易。这可能导致 processRefunds 函数调用回滚,所有用户的退款都将失败。幸运的是,此漏洞尚未被利用。
我们建议合约可以采取以下措施进行退款:
- 确保只有 EOA(外部所有者账户)可以竞拍
- 使用 ERC20 代币,例如 WETH,而不是 ETH
- 提供一个允许用户自行领取退款的函数
漏洞 II
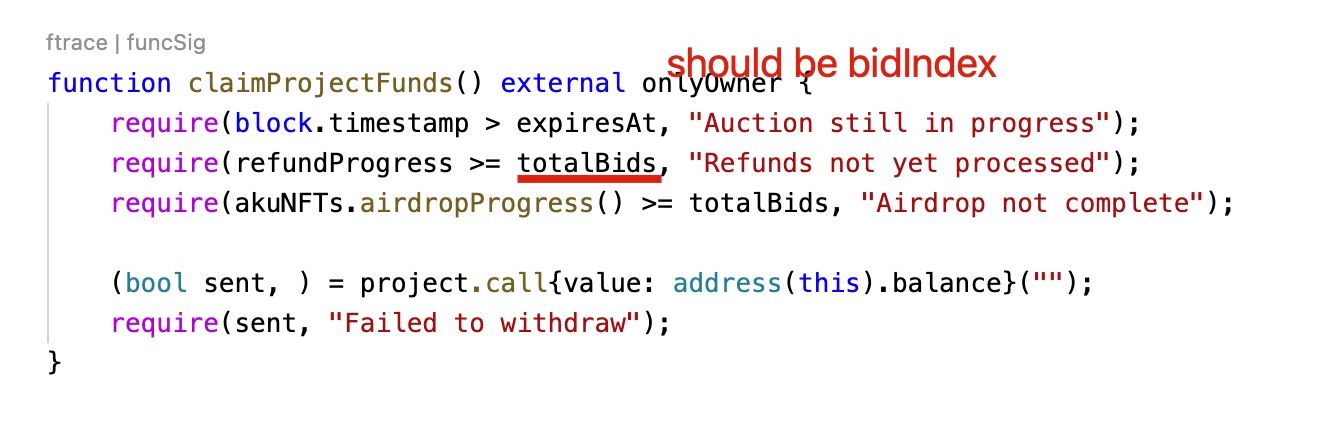
第二个漏洞是一个软件 bug。在 claimProjectFunds 函数中,项目所有者可以提取合约中的 Ether。然而,require(refundProgress >= totalBids, "Refunds not yet processed"); 这个 require 语句存在 bug,它应该将 refundProgress 与 _bidIndex 进行比较,而不是 totalBids。由于这个漏洞,条件永远无法满足,合约中的 Ether(11,539.5 Ether)可能会永远被锁定。
总结
我们再次感到惊讶(继昨天的 NBA NFT 事件之后),一个备受瞩目的项目怎么会忽视基本的软件安全实践。至少,项目应该编写足够的测试用例。不幸的是,我们怀疑项目方可能因为太忙而未能编写测试用例,最终损失了 3400 美元。
关于 BlockSec
BlockSec 是一家开创性的区块链安全公司,由一群全球知名的安全专家于 2021 年创立。公司致力于提升新兴 Web3 世界的安全性和可用性,以促进其大规模采用。为此,BlockSec 提供智能合约和 EVM 链安全审计服务,Phalcon 平台用于安全开发和主动阻止威胁,MetaSleuth 平台用于资金追踪和调查,以及 MetaDock 扩展,供 Web3 构建者在加密世界中高效冲浪。
截至目前,公司已为 MetaMask、Uniswap Foundation、Compound、Forta 和 PancakeSwap 等 300 多家知名客户提供服务,并通过两轮融资从 Matrix Partners、Vitalbridge Capital 和 Fenbushi Capital 等知名投资者那里获得了数千万美元的投资。




