本博客由中国浙江大学区块链安全研究团队发布*
2020年12月16日,我们的监控系统ThunderForecast报告了一系列可疑交易。随后,我们使用由我们研究团队开发的EthScope系统分析了这些交易,并确认所有报告的交易都是恶意的。在本博客中,我们将详细说明此次攻击,以帮助理解攻击者每种行为的意图。
什么是 Plouto Vault?
Plouto 是一个开放的去中心化资产管理协议。Plouto 协议提出了一个名为“开放金库”(Open Vault)的关键理念。借助这一理念,除了标准的投资策略外,资产管理者还可以将他们的协议部署给其他第三方,甚至可以使用 Plouto Vault 设计自己的策略。在这次攻击中,攻击者利用了Plouto Vault的漏洞,即铸造的代币数量取决于 YPool 中相应代币的数量。最终,攻击者套利了总计 698,775.32 美元的金额。
详细信息
现在,我们将通过一个攻击交易 0x49112d… 来揭示更多攻击细节。
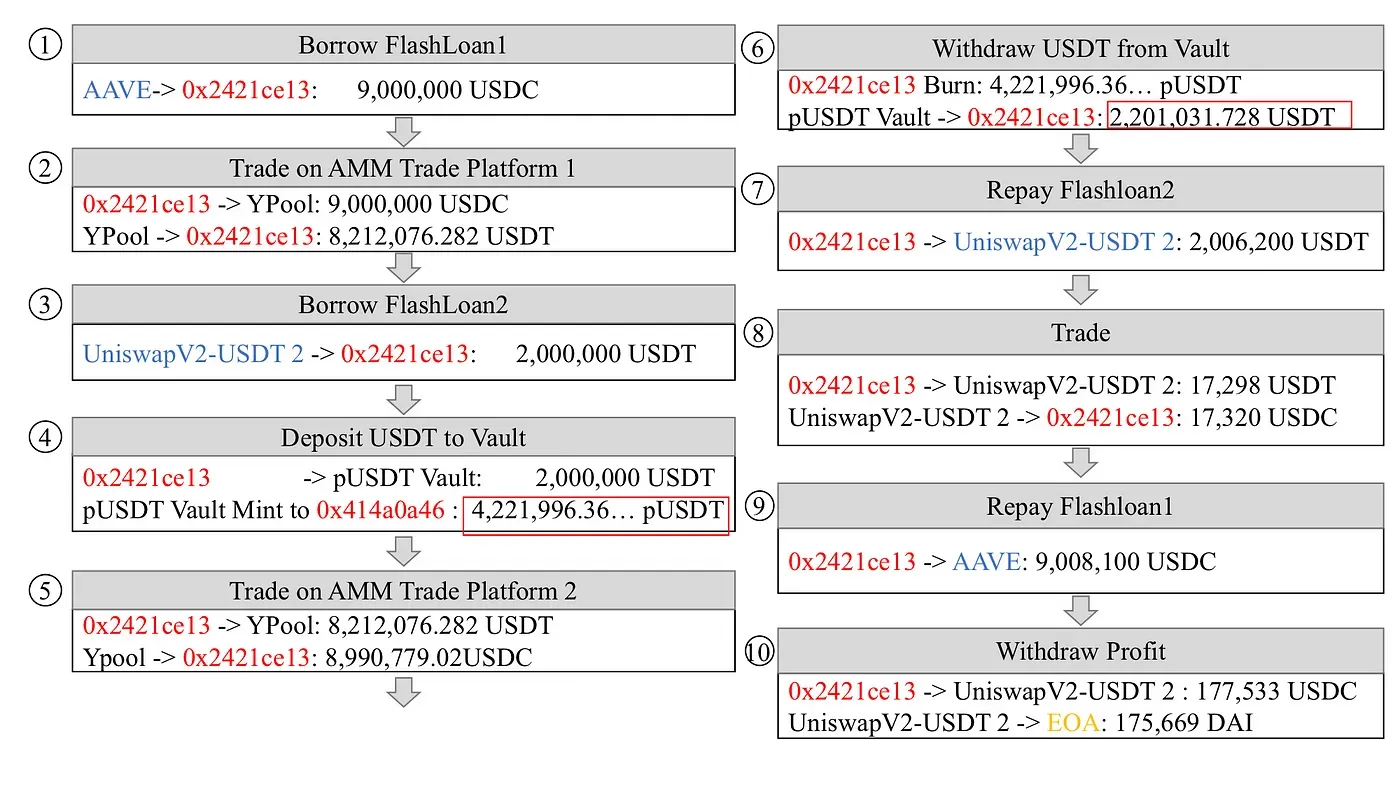
涉及十个步骤:
- 步骤 1:从 AAVE 借入 9,000,000 USDC 的闪电贷。
- 步骤 3:从 UniswapV2 借入 2,000,000 USDT 的闪电贷。
- 步骤 7:偿还 UniswapV2 上借入的 2,006,200 USDT 闪电贷。
- 步骤 8:在 UniswapV2-USDT 池中将 17,298 USDT 兑换为 17,320 USDC。兑换的 USDC 用于偿还 AAVE 上第一笔闪电贷。
- 步骤 9:偿还 AAVE 上借入的 9,008,100 USDC 闪电贷。
- 步骤 10:将 177,533 USDC 兑换为 175,669 DAI,并将利润发送到攻击者的 EOA。
收益与损失
在上述交易中,攻击者操纵了 YPool 中 USDT 的流动性,并从 Plouto Vault 套利了 175,669 DAI。
攻击规模
基于此次攻击的特点,我们检测到攻击者 0x43c162…. 发动了 1 个恶意合约 0x2421ce… 和 8 笔交易(在交易 0x49112d… 事件中获得的最大利润为 175,669.88 美元)。根据 Ehterscan 上的数据,攻击者总共套利了 698,775.32 美元。
结语
随着以太坊上 DeFi 生态系统的发展和 DeFi 服务(闪电贷)的不断更新,安全问题逐渐凸显。在这起攻击背后,闪电贷为攻击者实施流动性操纵提供了极大的“便利”。最近,Harvest 平台遭受了一次攻击,该攻击利用了合约之间强烈的依赖关系。
时间线
- 2020/12/16:发现可疑交易
- 2020/12/17:完成分析
- 2020/12/18:发布详细信息
关于 BlockSec
BlockSec 是一家领先的区块链安全公司,由一群全球知名的安全专家于 2021 年创立。公司致力于为新兴的 Web3 世界提升安全性和可用性,以促进其大规模采用。为此,BlockSec 提供智能合约和 EVM 链安全审计服务,用于安全开发和主动阻止威胁的Phalcon平台,用于资金追踪和调查的MetaSleuth平台,以及供 Web3 构建者在加密世界高效冲浪的MetaSuites扩展。
迄今为止,该公司已为 MetaMask、Uniswap Foundation、Compound、Forta 和 PancakeSwap 等 300 多家尊贵客户提供服务,并在两轮融资中从 Matrix Partners、Vitalbridge Capital 和 Fenbushi Capital 等知名投资者那里获得了数千万美元的投资。




