我们发现了一种新类型的网络钓鱼方法,它正在变得流行。与部署网络钓鱼合约(安全供应商可能会将其标记)不同,骗子正在滥用一些合法合约来执行攻击。
在这篇博客中,我们将向您展示骗子使用的策略,并提供如何避免被网络钓鱼的建议。
概述
通常,骗子会部署网络钓鱼合约来窃取受害者的代币。具体来说,他们的网络钓鱼合约包含可疑的 payable 和 multi-call 函数。访问网络钓鱼网站的用户会将 ETH 发送或将代币授权给这些合约。然而,安全供应商和钱包可以检测并标记这些网络钓鱼合约,导致禁止向它们进行的交易。
然而,我们发现骗子滥用信誉良好的 Web3 项目部署的合法合约来实现其网络钓鱼目的。而且,这些合法合约无法被标记为网络钓鱼并被阻止。由于它们不部署新合约,而是重复使用现有的合法合约进行网络钓鱼,因此我们将这种方式命名为 Web3 网络钓鱼中的“ROP”(Return-Oriented Programming)。这类似于传统软件安全领域的“ROP 攻击”(或代码复用攻击)。
具体来说,ROP(Return-Oriented Programming)是一种计算机安全漏洞利用技术,它允许攻击者利用现有库中的代码片段。在 Web3 网络钓鱼中,“ROP”指的是利用合法项目部署的合约进行欺诈目的。这一现象最早由 Twitter 账号 @MevRefund 在一篇帖子中报道。
传统的 Web3 网络钓鱼合约如何工作
在 Web3 网络钓鱼的早期阶段,骗子会设置一个外部所有账户(EOA)并引诱用户将 ETH 发送或将其他代币授权给该账户。然而,这种行为现在很容易被钱包检测到,也被用户发现。因此,骗子转向部署网络钓鱼合约。对于 ETH 网络钓鱼,骗子通常会采用一个具有可疑名称(如“Claim”或“Security Update”)的 payable 函数。这些诱人的函数名称会促使用户签署网络钓鱼交易并转移 ETH。
对于 ERC20 和 ERC721 代币网络钓鱼,骗子会引诱用户将他们的代币授权给网络钓鱼合约。随后,网络钓鱼合约中的 Multicall 函数将被调用,以转移用户的代币。特别是,Multicall 函数被设计用于在一次调用中执行多个特定的内部交易。不同的网络钓鱼方案,例如 NFT 零价购买、ERC20 授权网络钓鱼或 ERC20 permit 网络钓鱼,会使用不同的网络钓鱼交易。这使得它们能够配置交易参数并利用 Multicall 根据相应的网络钓鱼方案发起特定的网络钓鱼交易。
现在,许多流行的 Web3 钱包都构建了自己的网络钓鱼账户黑名单。它们会主动通知用户并阻止指向这些欺诈账户的交易。
Web3 网络钓鱼中的“ROP”
为了规避网络钓鱼账户黑名单机制,骗子转向使用一些无法添加到黑名单的账户。具体来说,他们滥用合法项目部署的 Multicall 合约,利用其执行复杂交易的功能。鉴于这些合法合约无法被标记为网络钓鱼账户,骗子会诱使用户将代币授权给这些合约。由于这些合法合约可以被任何人调用(没有访问控制),骗子可以立即滥用它们来转移用户的代币。下图展示了整个过程。
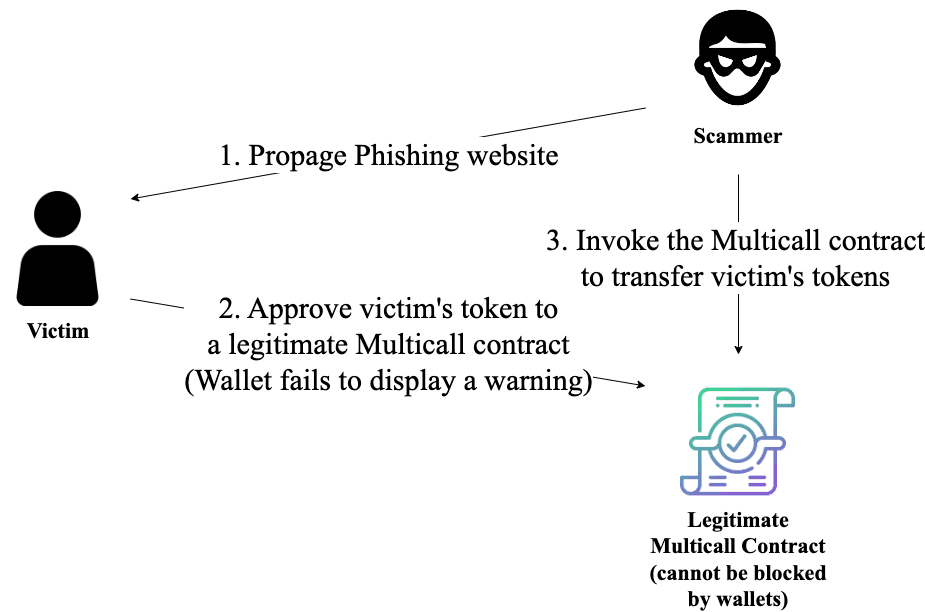
例如,臭名昭著的网络钓鱼犯罪集团 Angel Drainer 已经利用 Uniswap V3: Multicall 2 发起了 89 起网络钓鱼交易。请注意,合法的 multi-call 合约设计初衷是不持有任何资产。所以,按照其设计,被任何人调用是没问题的。然而,骗子在不部署自己的网络钓鱼合约的情况下,滥用了该合约执行网络钓鱼攻击。
建议
我们鼓励用户保持警惕,在进行任何操作之前仔细审查交易详情,尤其是授权交易。始终检查您的授权,并撤销任何可疑的授权。




