近期,web3钓鱼网站导致用户遭受巨额损失。这些钓鱼网站伪装成知名项目,诱骗用户签署交易,从而迅速耗尽其加密资产。与此同时,一种新型的“诈骗即服务”(SaaS)模式应运而生。具体而言,服务提供商向合作者提供钓鱼工具包,并要求其利润的百分比,通常为20%或30%作为回报。在这些服务提供商中,“Inferno Drainer”是一个臭名昭著的案例,已给数千名受害者造成数百万美元的损失。在这篇博文中,我们将以“Inferno Drainer”为例,分析其利润分享过程。
探索Inferno Drainer的工作原理:分步操作指南
总的来说,Inferno Drainer 的操作过程可分为五个步骤。
-
“Inferno Drainer”的提供商在 TG、Discord 和 Twitter 上宣传其官方推广渠道。
-
寻求将其流量变现但缺乏技术专长的合作者加入该频道,并与提供商共享其账户。
-
提供商向合作者提供现成的钓鱼工具包和部署说明。
-
合作者上线钓鱼网站。
-
当受害者上当受骗时,其加密资产通常会被转移到一个指定的钓鱼账户。随后,利润会在 Drainer 管理员和合作者账户之间进行分配。
在接下来的段落中,我们将通过分析涉及 ETH 和 ERC20 的两种钓鱼场景来揭示利润分享过程。
ETH 钓鱼场景

上图展示了 ETH 钓鱼场景中的利润分享过程。为了欺骗用户获取其 ETH,诈骗者部署了一个包含可支付函数(如 'mint' 或 'airdrop')的钓鱼合约。受这些函数名称的诱惑,受害者错误地签署了钓鱼交易。在收到受害者的 ETH 后,管理员会迅速调用提现函数,将 80% 的资金转入合作者账户。剩余的 20% 保留在合约中,并在适当的时候进行提取。
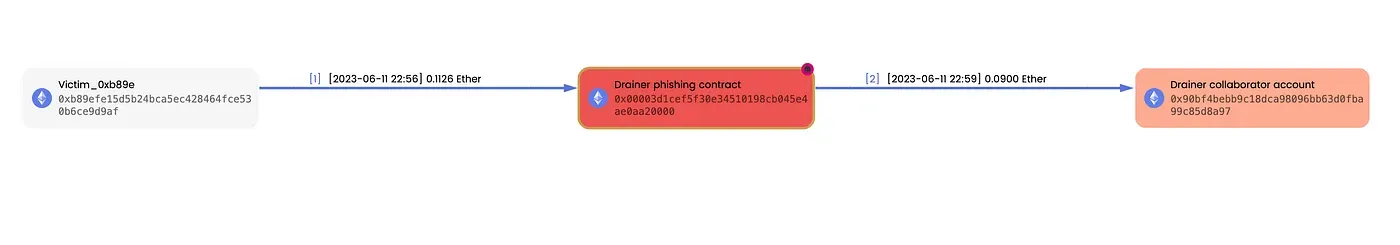
这是 MetaSleuth 描绘的一个真实案例。Victim_0xb89e 无意中向钓鱼合约发送了 0.1126 ETH。随后,该金额的 80%,即 0.09 ETH,被迅速提取并转入合作者账户。
您可以使用以下链接查看资金流向: https://metasleuth.io/result/eth/0xfa59f0531af65c0a16b6c1834e3921e7fa519734d4d90675e479e99722d6f4ba

该图展示了 ERC20 代币钓鱼场景中的利润分享过程。与 ETH 钓鱼不同,在这种情况下,钓鱼账户是 EOA(外部拥有账户)。钓鱼网站最初会提示受害者批准其 ERC20 代币转移到钓鱼账户。随后,钓鱼账户将批准代币的 20% 转给管理员账户,而剩余的 80% 则转给合作者账户。

这是一个具体案例。Victim_0x0a0e 和 Victim_0x1fcd 无意中批准了他们的 USDT 和 DAI 转移到钓鱼账户。随后,钓鱼账户分别将这些代币的 20% 和 80% 转给了管理员和合作者账户。
您可以使用以下链接查看资金流向: https://metasleuth.io/result/eth/0x1ba31a2751259048e1e559df59bcdf80015e15359674aaf64e936cb98630b810?source=d0a430bd-2b7e-46bb-8788-b0f8ba39f366.
关于 Inferno Drainer 系统的关键见解和发现
为了收集利润分享活动的证据,我们对与管理员账户相关的所有历史交易进行了全面分析。需要强调的是,我们仅关注利润分享比例为 20% 或 30% 的情况。在我们的调查中,我们发现了 3,223 笔利润分享交易,涉及总计 502 万美元的资金。在这些交易中,管理员账户已从 351 名合作者处收取了 107 万美元的费用。此外,我们的钓鱼检测系统已识别出 574 个相关的钓鱼网站。
为了保护用户免受 Inferno Drainer 的侵害,我们已将所有这些网站 promptly 报告给 MetaMask (https://github.com/blocksecscamreport/eth-phishing-detect/commits?author=blocksecscamreport&before=01bf4f680061bc39ecd2d55425774fc3092aa3cc+35)。
总结
这种涉及利润分享的 SaaS 模式正在迅速发展。我们将保持警惕,持续监控相关的钓鱼账户和交易。我们敦促用户在批准任何操作之前,提高警惕,并仔细审查交易详情。本博客旨在帮助用户了解利润分享过程,并保护他们在区块链领域免受潜在钓鱼网站的侵害。
关于 MetaSleuth
MetaSleuth 是 BlockSec 开发的一个综合性平台,旨在协助用户有效地追踪和调查所有加密活动。通过 MetaSleuth,用户可以轻松追踪资金、可视化资金流、监控实时资金动向、保存重要信息,并通过与他人分享发现进行协作。目前,我们支持包括比特币 (BTC)、以太坊 (ETH)、波场 (TRX)、Polygon (MATIC) 等在内的 13 种不同的区块链。
Twitter:@MetaSleuth
Telegram:https://t.me/MetaSleuthTeam




