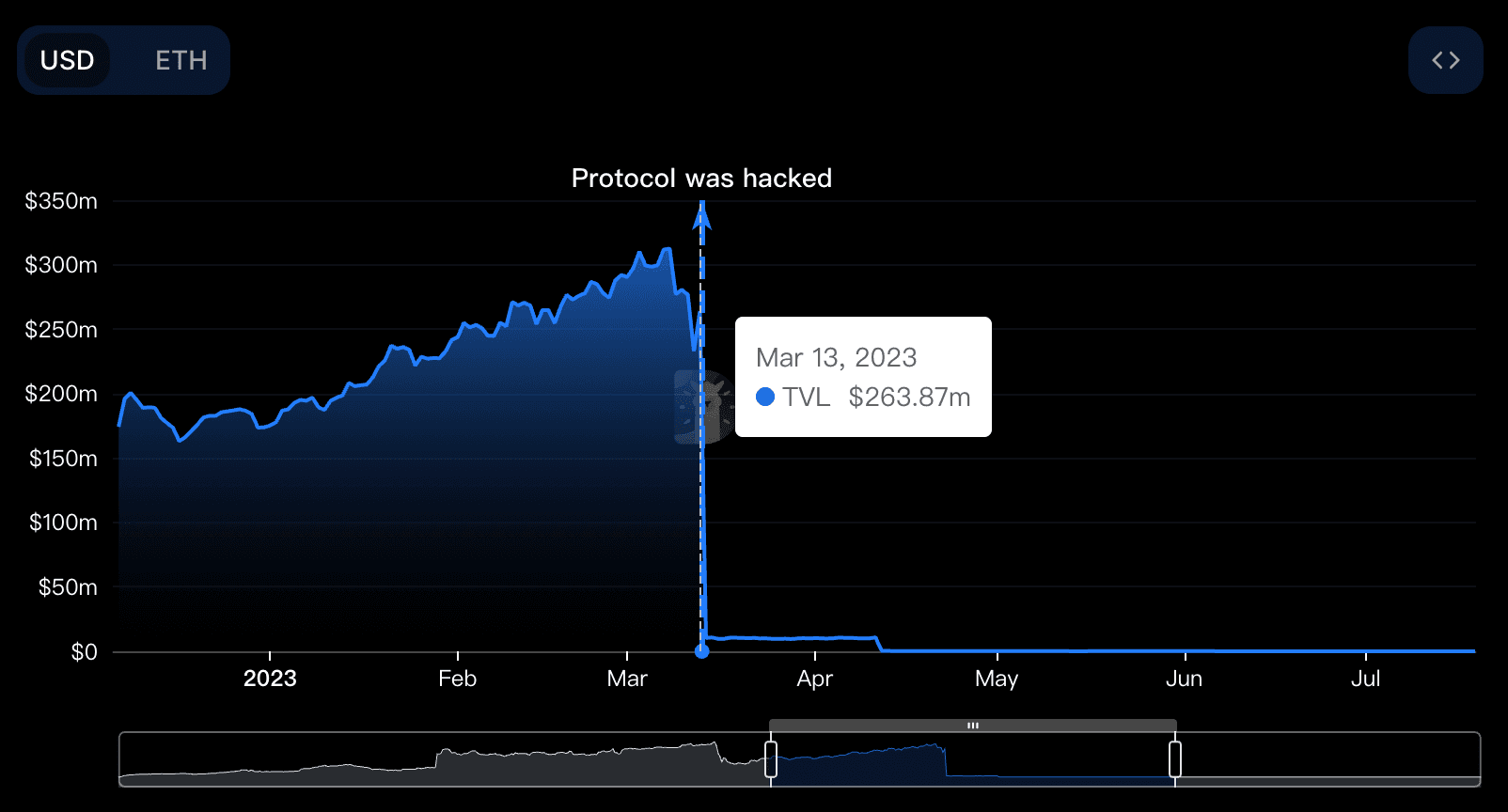
2023年3月13日,以太坊上的去中心化金融(DeFi)借贷协议Euler Finance遭遇了闪电贷攻击,造成约2亿美元的损失。根本原因被确定为donateToReserves()函数中缺少流动性检查。作为一家区块链安全公司,BlockSec持续监控此类漏洞利用,以改进DeFi安全性并保护数字资产。
| 日期 | 攻击类型 | 链 | 损失 | 追回 |
|---|---|---|---|---|
| 2023-03-13 | 业务逻辑缺陷 | ETH | 约2亿美元 | 是 |
在攻击发生前,Euler Finance在DefiLlama上排名DeFi协议前30名。其锁仓总价值(TVL)从2.64亿美元急剧下降至1000万美元,跌幅高达96%。
关键概念
理解Euler Finance的**自借(self-borrow)和软清算(soft liquidation)**机制对于掌握此次漏洞利用至关重要:
- 自借: 允许用户通过使用新铸造的EToken作为抵押品来铸造新资产并增加债务,从而实现杠杆。
- 软清算: 允许清算人灵活地为被清算方偿还债务,而不是使用固定的清算系数。
这些机制虽然具有创新性,但也引入了攻击者利用的漏洞。
攻击分析
攻击者通过以下步骤执行了此次漏洞利用:
- 从AAVE闪电贷3000万DAI。
- 将2000万DAI存入Euler Finance,并获得2000万eDAI。
- 利用Euler的借款能力铸造1.95亿eDAI和2亿dDAI。
- 偿还1000万债务以铸造更多eDAI,持有2.15亿eDAI和1.9亿dDAI。
- 重复步骤4,持有量增加到4.1亿eDAI和3.9亿dDAI。
- 调用
donateToReserves()函数捐赠1亿eDAI。
function donateToReserves(uint256 amount) external {
// 缺少流动性检查允许漏洞利用
// 函数逻辑在此处
}在此过程中,攻击者的健康因子未得到验证,允许他们清算自己的头寸以获利。攻击者自行清算,提取了3800万eDAI,并偿还了闪电贷。
此次漏洞利用是一次闪电贷攻击,利用了智能合约中的业务逻辑漏洞。
总结
核心问题在于donateToReserves()函数中缺少流动性检查,并结合动态的清算折扣机制。这创造了一个套利机会,使攻击者能够在没有适当抵押品或债务偿还的情况下,利用大量加密资产。
后续步骤
值得注意的是,约1.35亿美元的被盗资金——主要是质押的以太坊(stETH)、比特币以及DAI和USDC等稳定币——已全部追回。攻击者是一名19岁的阿根廷人Federico Jaime,他出于道义原因在三周后归还了所有被盗资产。[1]
BlockSec一直在积极监测此次事件。我们的官方Twitter账号@BlockSecTeam和@MetaSleuth提供了持续的更新。2023年3月18日,攻击者归还了3000枚以太坊,一周后又归还了51000枚以太坊,其余资金在后续几天内被归还。
在退款过程中,出现了利用此次事件的钓鱼诈骗。骗子创建了一个钓鱼网站eulerrefunds.cxx,欺骗了一些用户。
MetaSleuth,BlockSec高性能跨链资金流分析工具,在攻击和退款阶段能够近乎实时地追踪受影响的数字资产。
更多区块链安全信息
此案例是众多强调强健区块链安全必要性的案例之一。BlockSec为区块链项目提供全面的安全服务,包括:
- 在开发过程中进行智能合约审计以识别漏洞。
- Phalcon Security,一个提供事件警报和自动阻止以防止加密货币被黑的SaaS平台。
- MetaSleuth,用于增强数字资产的可追溯性和透明度。
- 基础设施审计以保障底层区块链环境的安全。
Web3最佳安全审计机构
在上线前验证设计、代码和业务逻辑
参考
[1] HE STOLE $200 MILLION. HE GAVE IT BACK. NOW, HE’S READY TO EXPLAIN WHY



