背景
对于所有加密货币爱好者来说,Web3 的世界充满了机遇、挑战与危机。每天都有大量新的代币项目进入市场,看似提供了数不尽的财富机会,但实际上,潜在的风险无处不在。随着各类高风险项目层出不穷,用户往往措手不及。在这种情况下,我们该如何评估项目的可靠性,并避开“貔貅盘”(Rug Pull)的陷阱以保护我们的资金呢?别担心,本文将为您提供一套评估“貔貅盘”的综合方法论,助您最大限度地降低资产损失风险。
1. 了解加密安全的基本工具:防范“貔貅盘”的操作指南
观察趋势图并验证交易量
利用多链 DEX 加密分析工具(如 DEX Screener),通过观察代币趋势图,我们可以发现任何异常的买卖比例,从而避开由可疑项目制造的虚假交易量。同样,对于新发行的代币,如果您发现其交易量和单笔交易金额异常巨大,请务必保持警惕。

检查交易记录
像 DEX Screener 这样的工具可以列出所有交易记录,让我们能够轻松审查涉及买卖操作的所有地址。如果您发现同一个地址频繁进行交易(如下图所示),这也是一个非常可疑的信号。
使用蜜罐检测与代币风险监控功能
包括 DEX Screener 和 Advantis.AI 在内的平台提供“蜜罐”(Honeypot)测试及一些基础的代币风险监控功能,这些都能辅助用户评估投资风险。如图所示,当用户搜索某个代币时,平台会自动提供该代币的风险等级,从而让用户决定是否及时撤资。

2. 如何使用 MetaSleuth 检测加密货币投资中的“貔貅盘”
审查部署者的资金来源
对于一个代币而言,除了代币本身的合约地址和交易对地址外,部署者(Deployer)的地址也至关重要。通过观察该地址在区块链上的财务往来关系,我们可以更好地评估项目的风险。
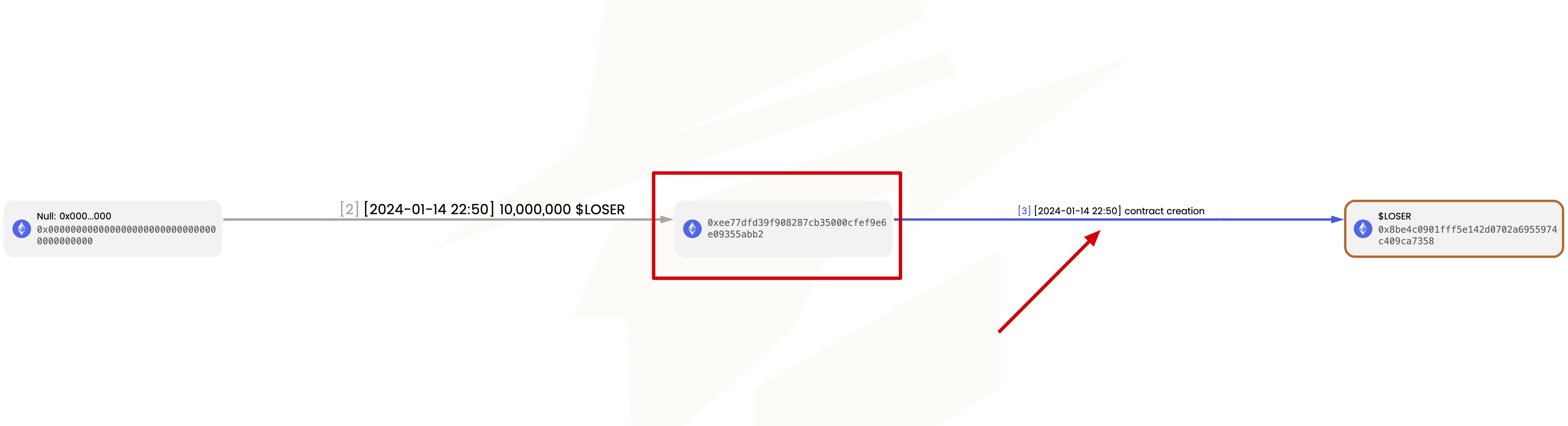
要查找部署者地址,只需将代币的合约地址输入 metasleuth.io。在生成的资金流向图中,寻找“合约创建”(contract creation)节点。该节点对应的交易即为代币合约的创建交易,而该交易的发起人就是部署者。随后,您可以进一步分析部署者的资金来源。
为了有效规避风险,用户可以关注以下常见的部署者资金来源,这些通常预示着高风险:
-
资金来源于混币服务或免 KYC 的闪电兑换服务(例如 Fixedfloat)。这是恶意代币部署者为了避免被追溯真实身份而选择的方法。
-
资金来源不合法。下图展示了一个“貔貅盘”网络,其中的所有代币都在极短的时间内进行了“貔貅”跑路。诈骗者利用上一次跑路的利润将资金转移到下一个地址,该地址随后部署新代币并引诱受害者上钩。
检查流动性来源
诈骗项目方非常善于制造虚假流动性,如下图所示。他们将此前获利的资金分散到许多不同的地址中。其中一些地址仅用于购买代币,而另一些则负责抛售代币。这种虚构的流动性诱导受害者认为该代币非常热门,殊不知,一旦他们投入资金,就会面临被欺诈的风险。
留意前几大持币地址
下图描绘了某代币的持币地址名单,其中排名第二的持有人持有量几乎等同于流动性池中的资产总额。这意味着该持有人有能力随时从池中撤走所有资金。

通过在 MetaSleuth 中进一步追踪该地址的资金来源,我们可以发现该地址正是代币的部署者,他在合约创建时为自己铸造了大量代币。此类项目风险极大。
总结
在投资之前,用户应进行充分的尽职调查(DYOR),利用成熟的分析平台(如 DEX Screener)和资金追踪平台(如 MetaSleuth)辅助投资决策,从而最大程度地规避风险。观察趋势图、验证交易量以及检查交易记录是常用的手段。此外,像 MetaSleuth 这样的工具在追踪部署者资金来源和流动性来源方面具有重要作用,是防范风险的有效方式。确保代币项目的真实性和可靠性,有助于加密货币爱好者做出更明智的投资决策,从而在 Web3 世界中实现更好的投资回报并降低风险。
关于 MetaSleuth
MetaSleuth 是由 BlockSec 开发的一站式平台,旨在帮助用户有效追踪和调查所有加密活动。借助 MetaSleuth,用户可以轻松追踪资金、可视化资金流向、监控实时资金动向、保存重要信息,并通过与他人分享调查结果进行协作。目前,我们支持 13 条不同的区块链,包括比特币 (BTC)、以太坊 (ETH)、波场 (TRX)、Polygon (MATIC) 等。
Twitter:@MetaSleuth
Telegram:https://t.me/MetaSleuthTeam




