Blockscout 区块链浏览器已集成 MetaSuites 的地址标签(支持 Ethereum、Polygon、Gnosis、Optimism 和 Base)以及GPT 驱动的交易解释(支持 Ethereum)功能,并新增了快速访问 Phalcon Explorer 的入口。
地址标签
在区块链浏览器中导航代表地址的复杂代码字符串时,如何有效提取有价值的信息?
凭借深厚的技术知识和长期的 MetaSuites 数据收集工作,我们开发了一个庞大的数据库,涵盖超过 20 个主流公链,拥有超过 3 亿个已标记的地址。借助 MetaSuites,Blockscout 用户可以轻松识别各种类型的地址,例如:
- 交易所的充值和提现地址
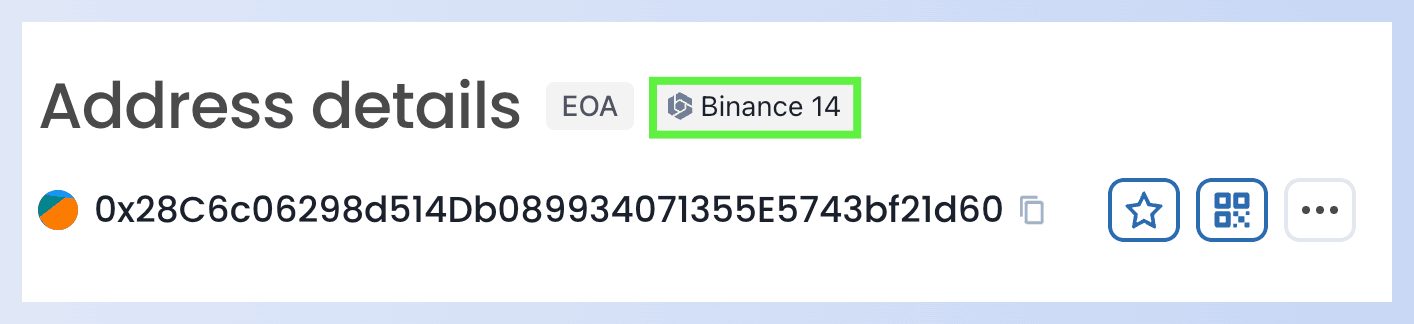
- 项目地址(例如 DeFi 和 NFT 项目地址)
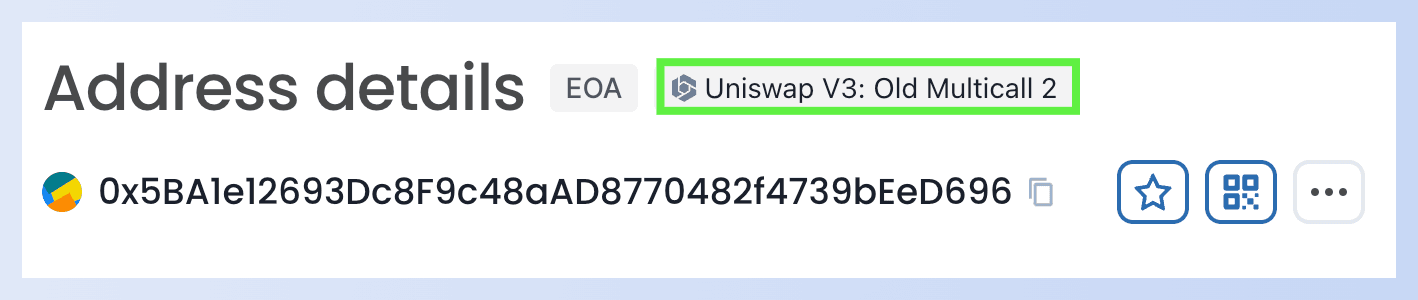
- 白帽黑客地址和黑帽黑客地址
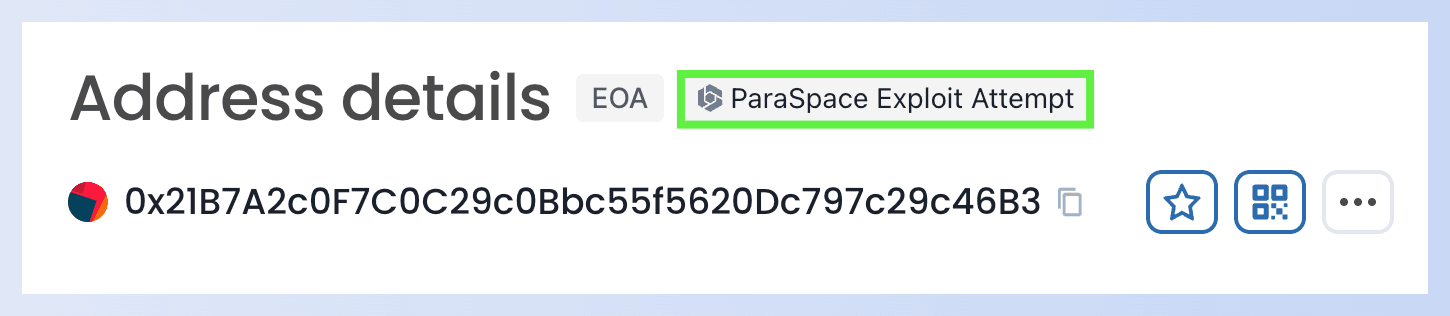
- 诈骗者地址
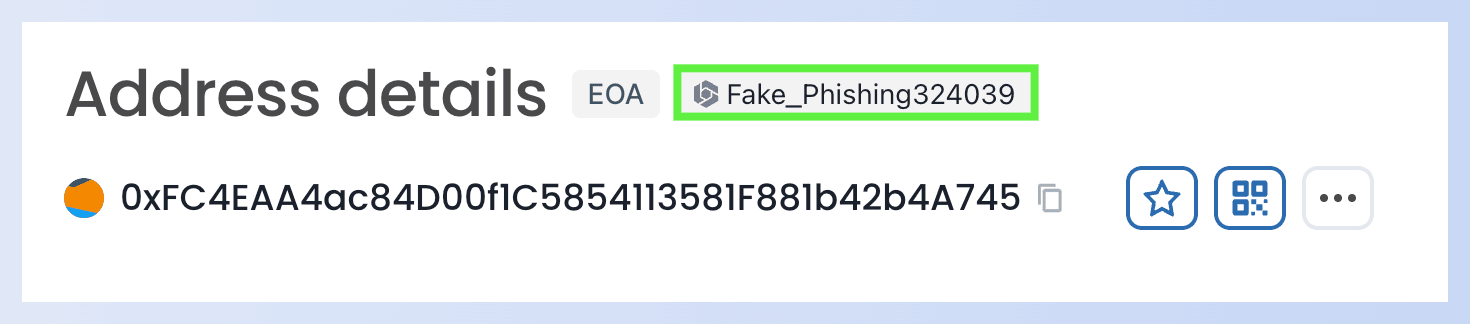
这简化了“自行研究”(DYOR)的过程,使用户能够更好地了解相关实体。
GPT 驱动的交易解释
随着 DeFi 的发展,链上交易已超越传统的记账范畴,涉及复杂的智能合约执行,使得普通用户越来越难以理解这些交易。例如:
- 由于难以理解历史交易,调查交易对手方往往徒劳无功。
- 在使用区块链浏览器调查被盗资金时,您可能会发现自己无法理解发生了什么。
MetaSuites 借助 GPT,通过易于理解的自然语言解释,帮助用户理解交易。
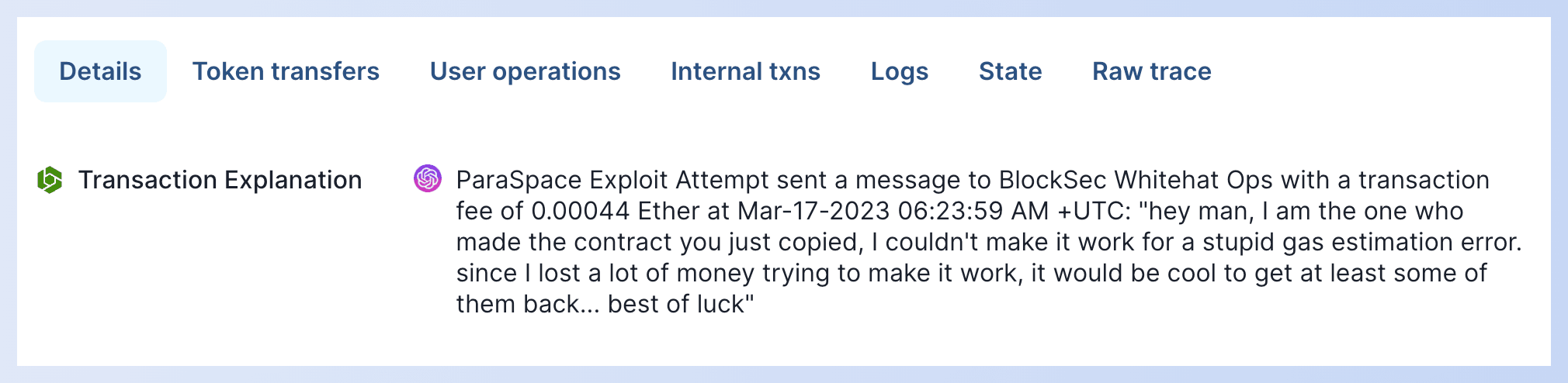
- 1:链上消息
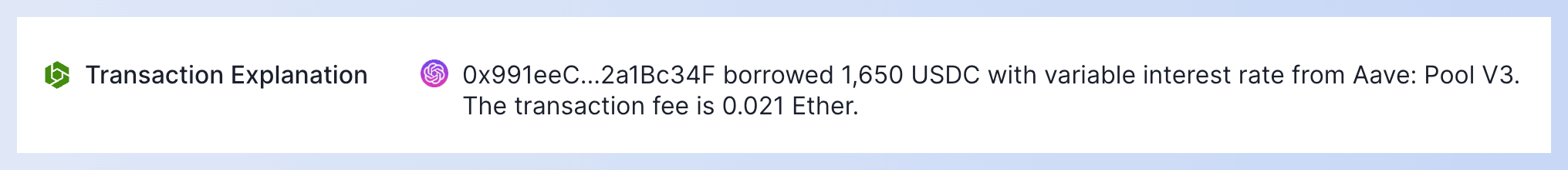
- 2:借贷
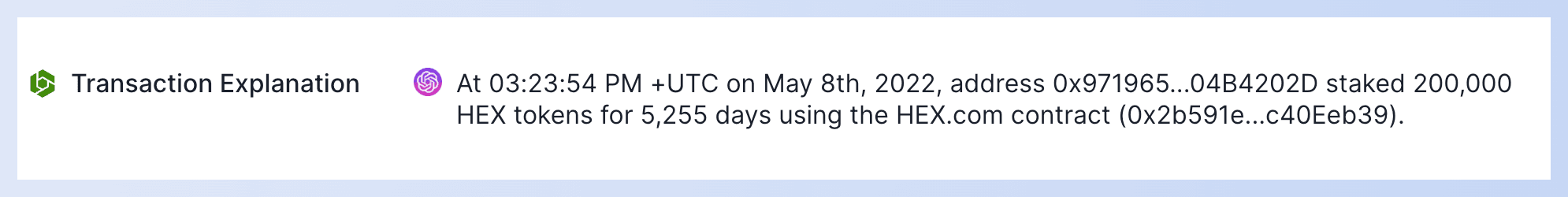
- 3:质押
- 4:网络钓鱼诈骗
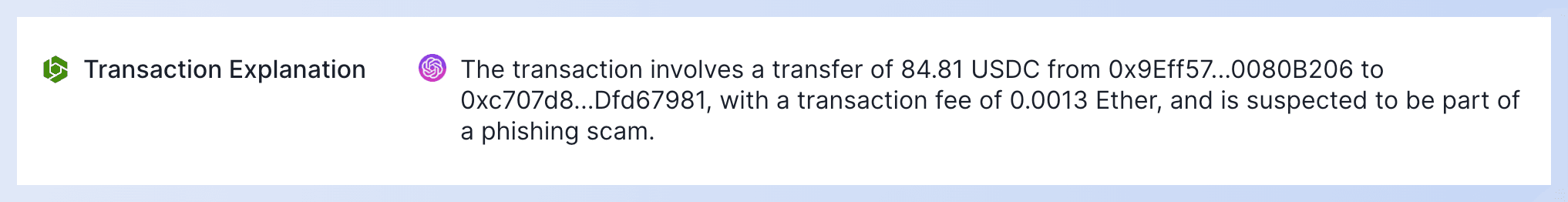
借助交易解释功能,Blockscout 用户现在可以轻松理解交易中发生的事件:何时、哪个地址与另一个地址执行了什么操作,甚至可以获得关于可疑交易或网络钓鱼诈骗的见解。
Phalcon Explorer 快速访问
Blockscout 已集成 Phalcon Explorer 的快速访问。这提升了 Blockscout 用户的体验,因为他们可以直接获得一个交易可视化工具。
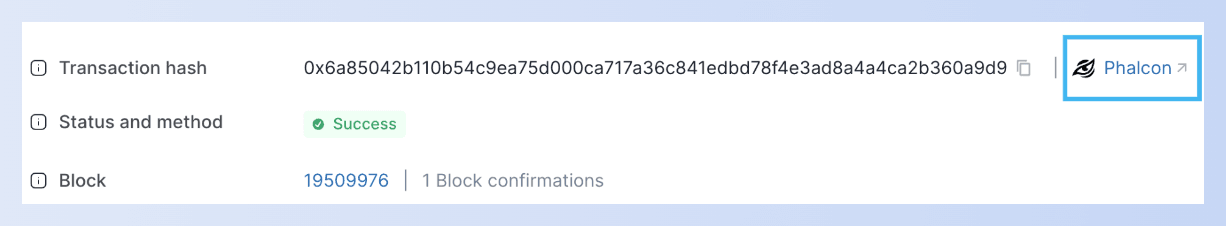
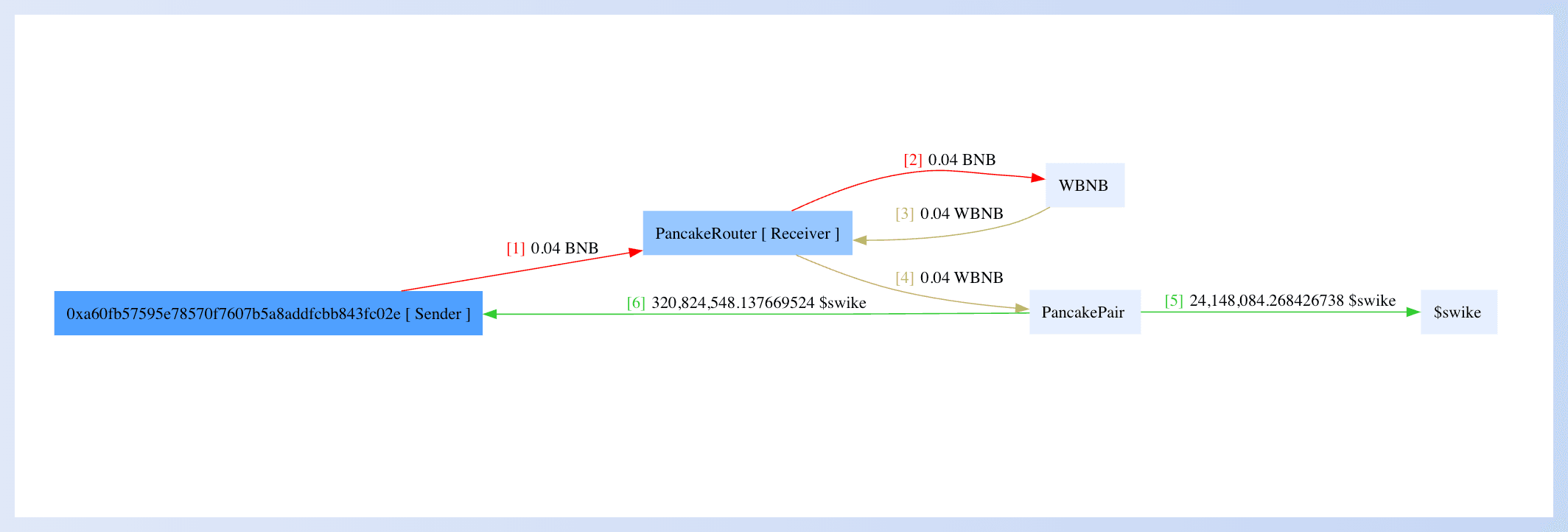
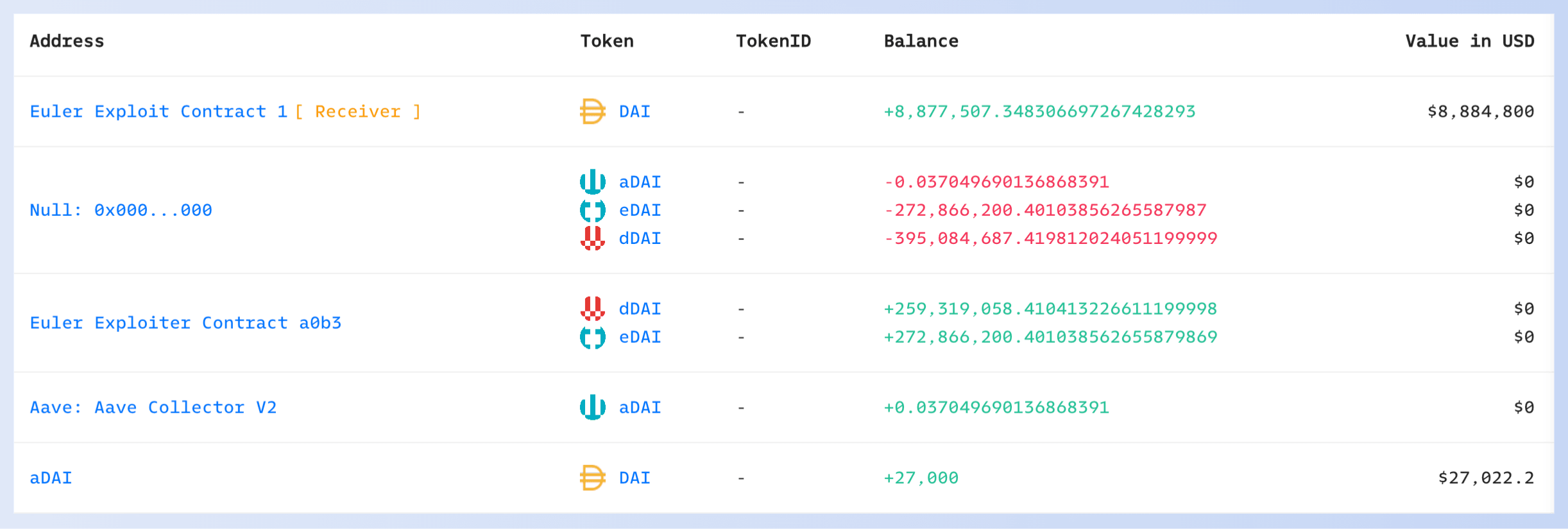
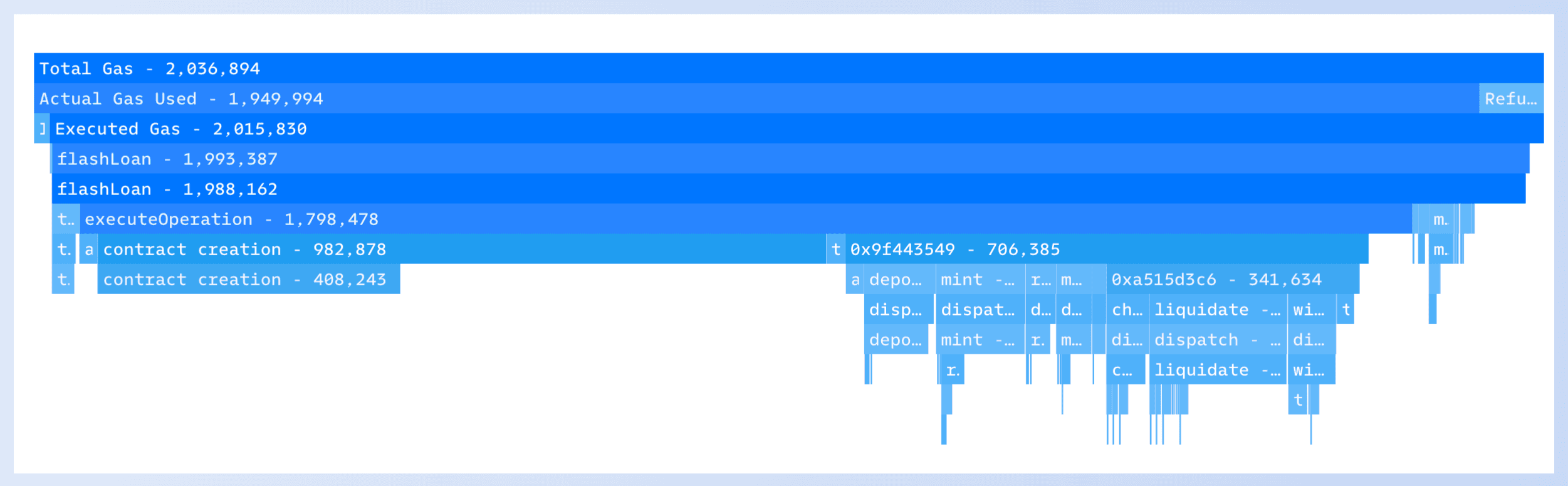
除了基本的交易信息,Phalcon Explorer 还直观地展示了交易的其他详细信息,包括:
- 资金流
- 余额变化
- Gas 分析器
- 状态变化

- 调用流程
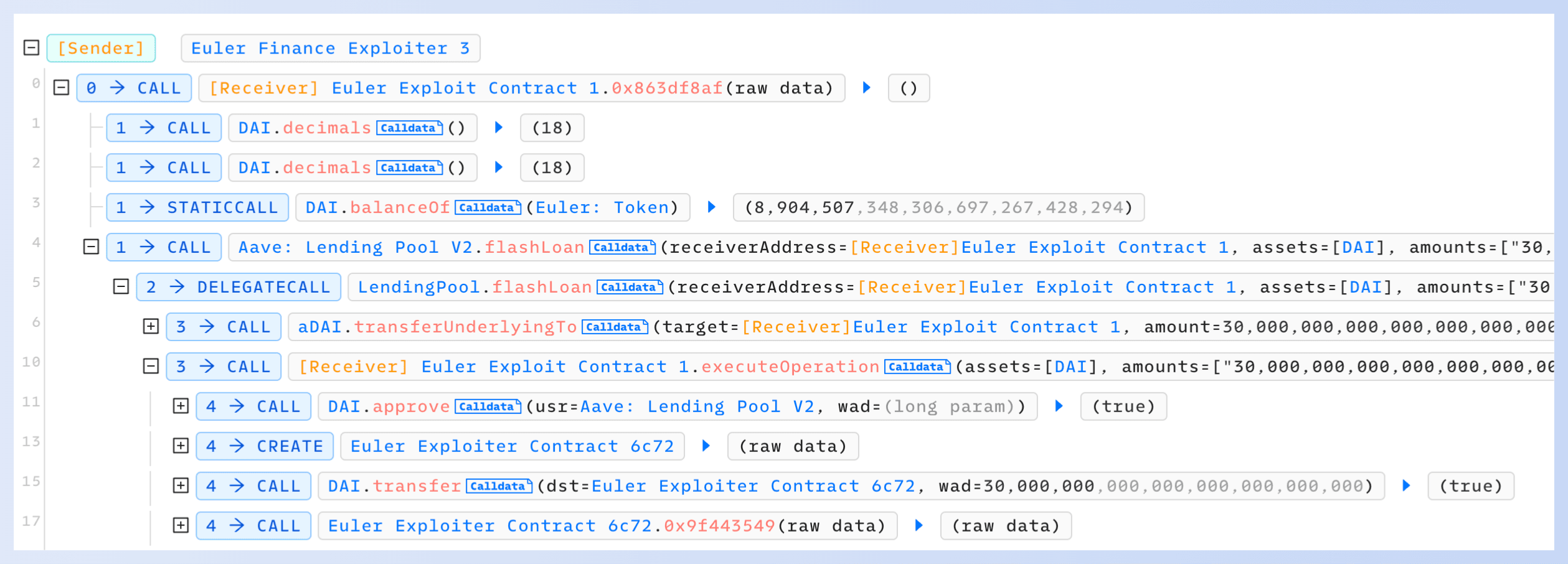
用户还可以在“调用流程”部分一键切换到多屏幕调试模式。
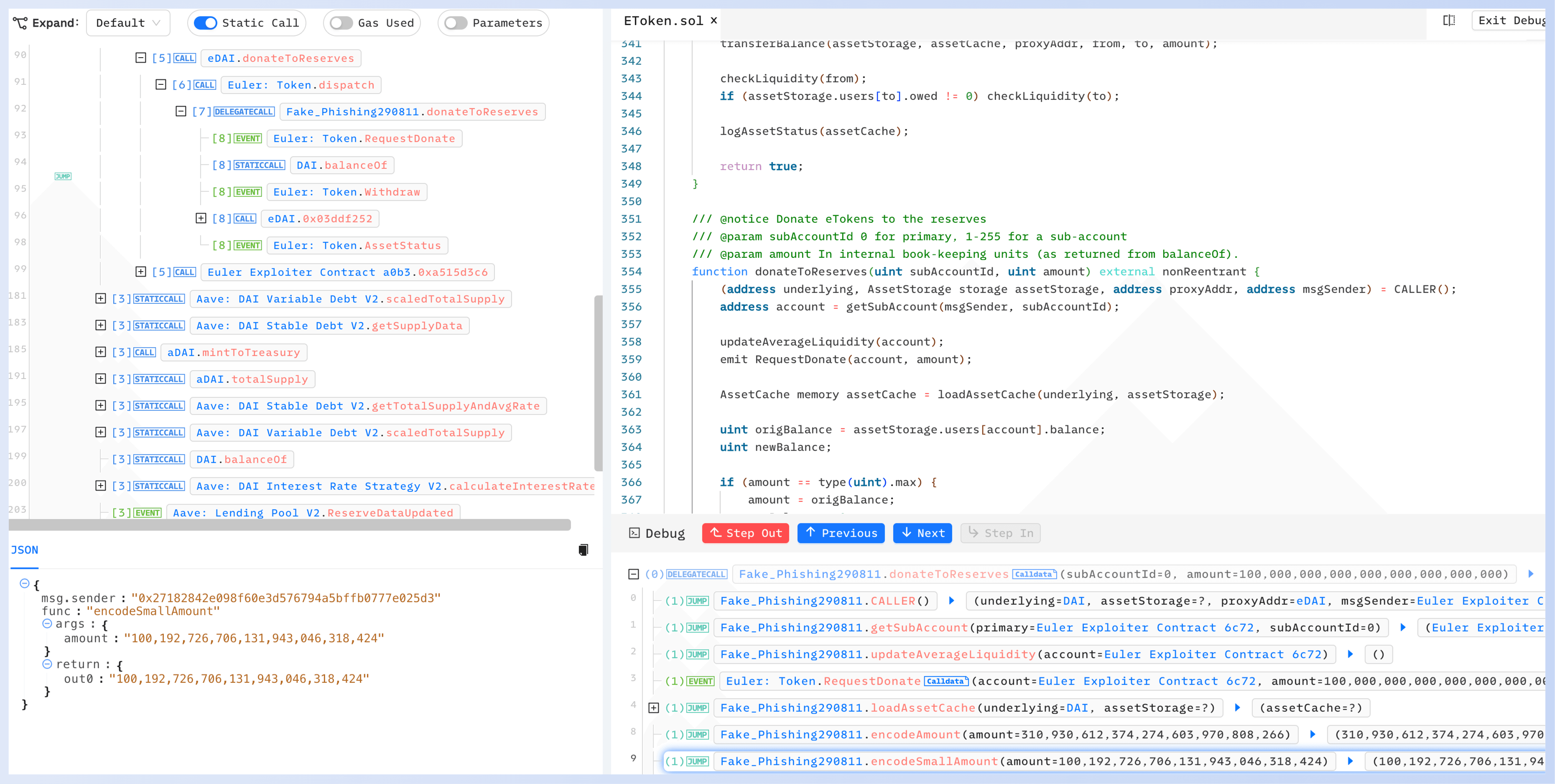
此外,Phalcon Explorer 支持在任何区块高度和位置进行交易模拟,允许用户提前预览执行结果。
Phalcon Explorer 快速访问功能的推出,满足了交易员、开发人员和安全研究人员在进行复杂的交易分析、调试和模拟方面的需求。
结论
我们有信心,此次合作将为 Blockscout 用户提供详细且富有洞察力的地址和交易信息,简化他们的分析流程,并促成更智能、更安全的交易决策。
立即在 Blockscout 上探索这些新功能!
关于 Blockscout
Blockscout 是 EVM 兼容链首选的开源区块链浏览器,拥有超过五年的生产经验。该浏览器为公链、私链、测试网以及许多其他网络提供了可靠、可定制且透明的解决方案。Blockscout 致力于促进去中心化、透明度和社区发展,是 400 多个公共网络的理想选择。
网站:https://www.blockscout.com/
Twitter:https://twitter.com/blockscoutcom
关于 MetaSuites
MetaSuites 是一款浏览器扩展插件,可用于生成资金流、显示地址标签、一键下载数据、模拟交易、查看存储和代理升级等功能,并提供超过 20 种实用工具,支持十多个区块链浏览器。
网站:https://blocksec.com/metasuites
Twitter:https://twitter.com/MetaDockTeam
关于 Phalcon Explorer
Phalcon Explorer 是我们攻击监控和阻止平台 - Phalcon 的支持工具。这款强大的交易浏览器专为 DeFi 社区而设计。它提供了关于调用流程、余额变化和交易资金流的全面数据,并支持交易模拟。这有助于开发人员、安全研究人员和交易员更直观地理解交易。
网站:https://blocksec.com/explorer
Twitter:https://twitter.com/Phalcon_xyz



