地址冻结和解冻检查是 USDT 用户频繁且实际的需求。然而,长期以来,通过传统渠道处理这项任务一直很困难。TronScan 和 Etherscan 并未清楚显示冻结状态。一些企业级 KYT 工具提供这些数据,但它们通常缺乏简单开放的搜索界面。
BlockSec 发布了一份关于近 12.6 亿美元被冻结 USDT 的报告以及如何降低冻结风险。此后,我们收到了许多用户关于如何检查地址是否被冻结的请求。为了解决这个问题,我们推出了USDT Freeze Tracker。下面,我们将介绍其四个核心页面中的第一个。
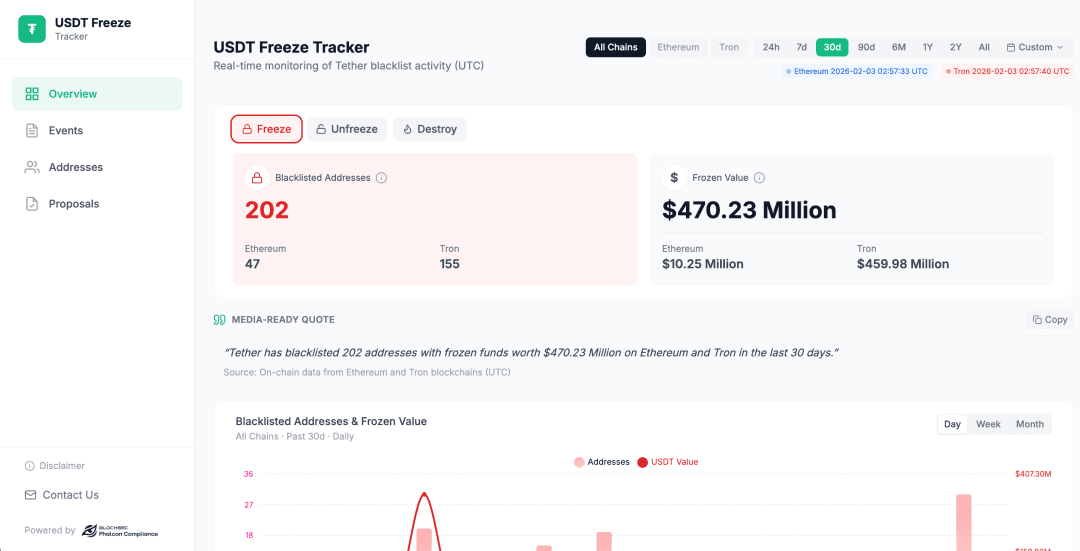
概览:一目了然地了解全局
概览页面充当主仪表盘。它汇总了 USDT 地址冻结、解冻和销毁事件的完整数据。您可以按不同的时间范围过滤结果,包括过去 24 小时、7 天、30 天、90 天、六个月、一年、两年或所有时间。
无需复杂的设置,您可以快速了解任何选定期间内的活动。数据清晰易读。总体趋势一目了然,帮助您更快地掌握信息并做出更好的决策。
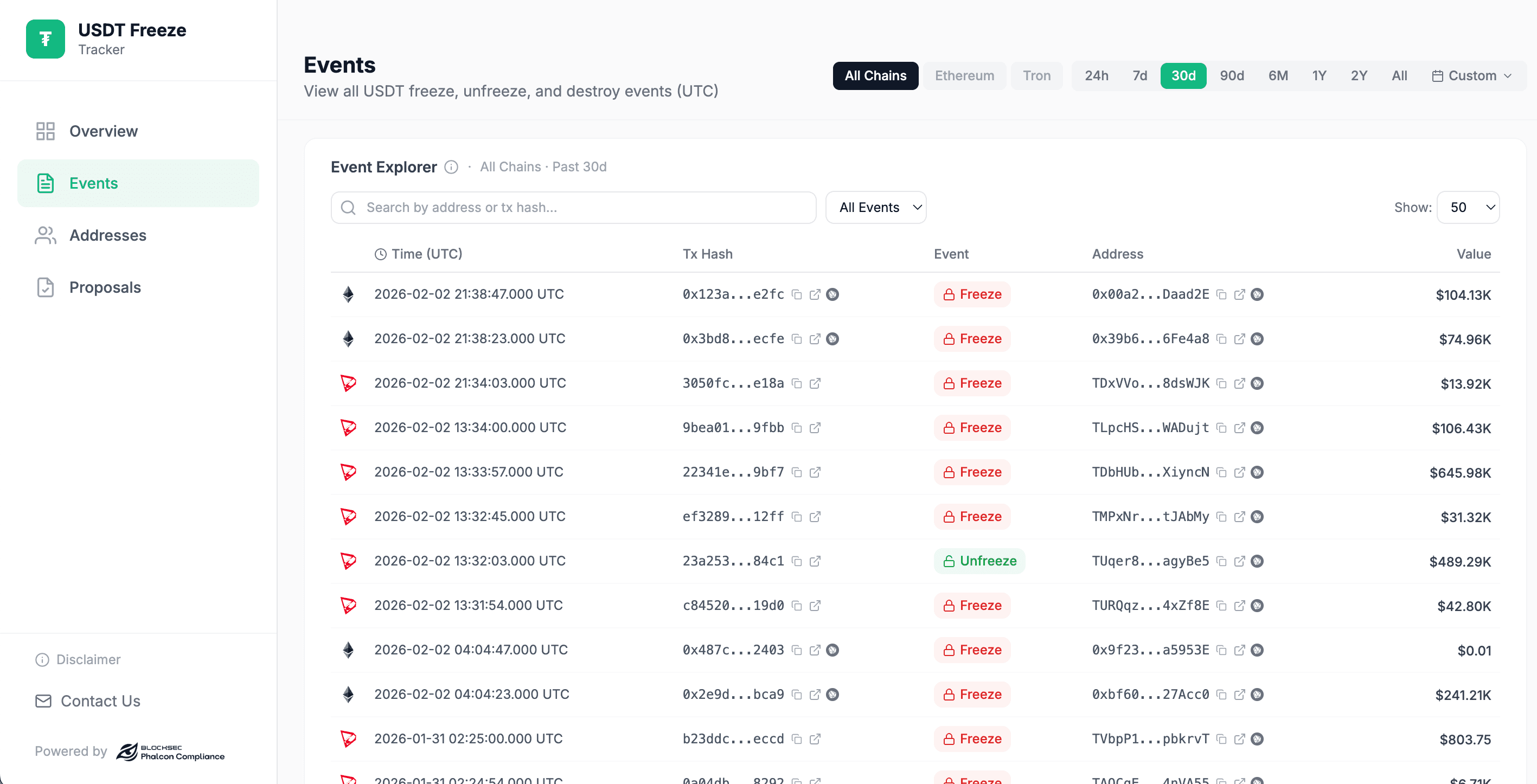
事件:逐一追踪地址活动
事件页面以清晰的列表显示地址活动,按时间顺序排列。每一行都显示单个冻结、解冻或销毁事件及完整详细信息。这使得追踪发生了什么以及何时发生变得容易。
对于每个事件,您可以打开Phalcon Explorer中的相关交易以查看链上细节。您还可以点击受影响的地址以打开Phalcon Compliance并运行风险扫描。这有助于您了解地址被冻结、解冻或销毁的原因以及风险可能来自何处。
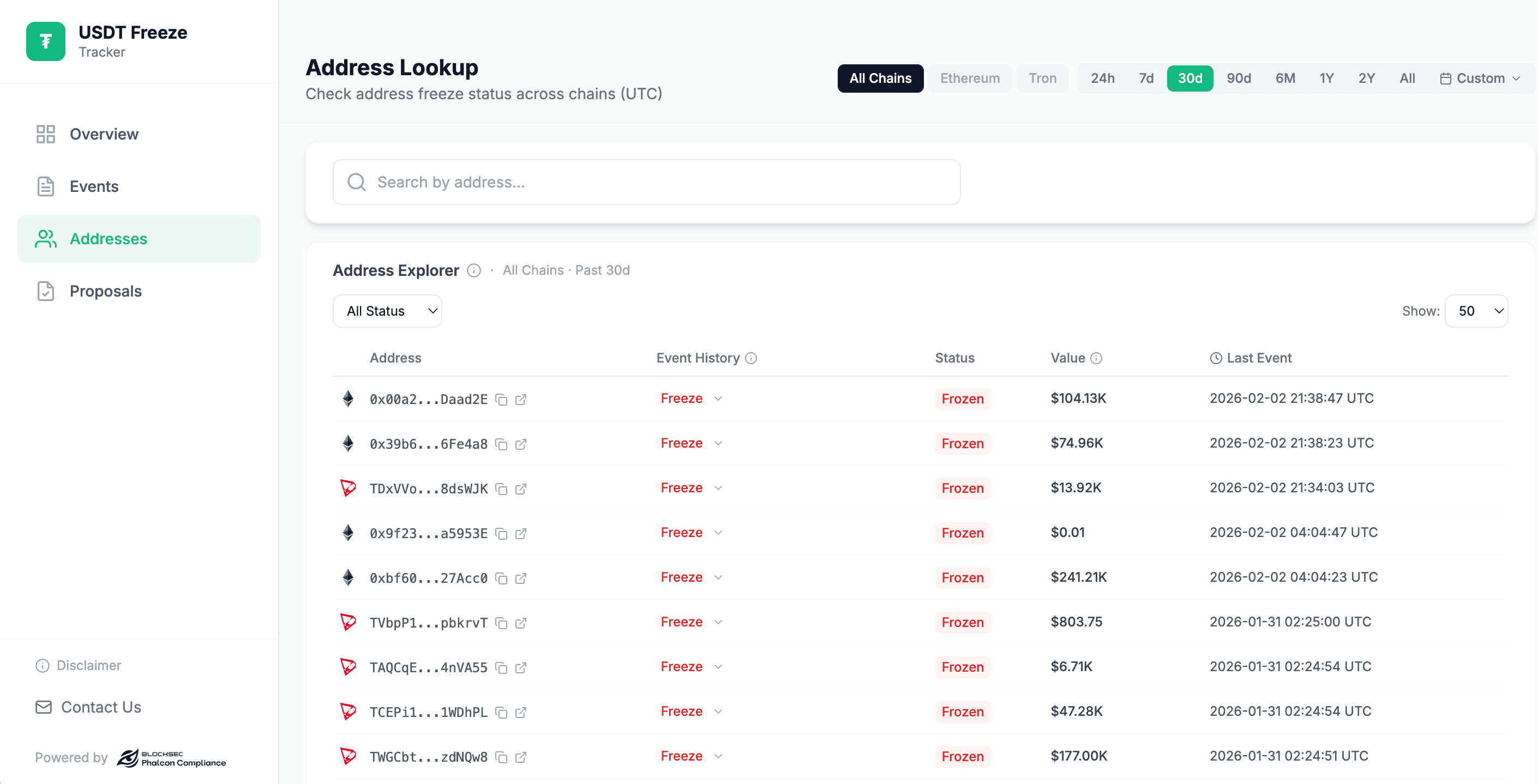
地址:即时搜索并获取结果
在地址页面,您可以输入钱包地址进行直接搜索。系统会快速检查该地址是否在黑名单上,并显示其当前的冻结或解冻状态。
这使您可以立即确认特定地址的状态,并了解它是否受到任何 USDT 限制的影响。
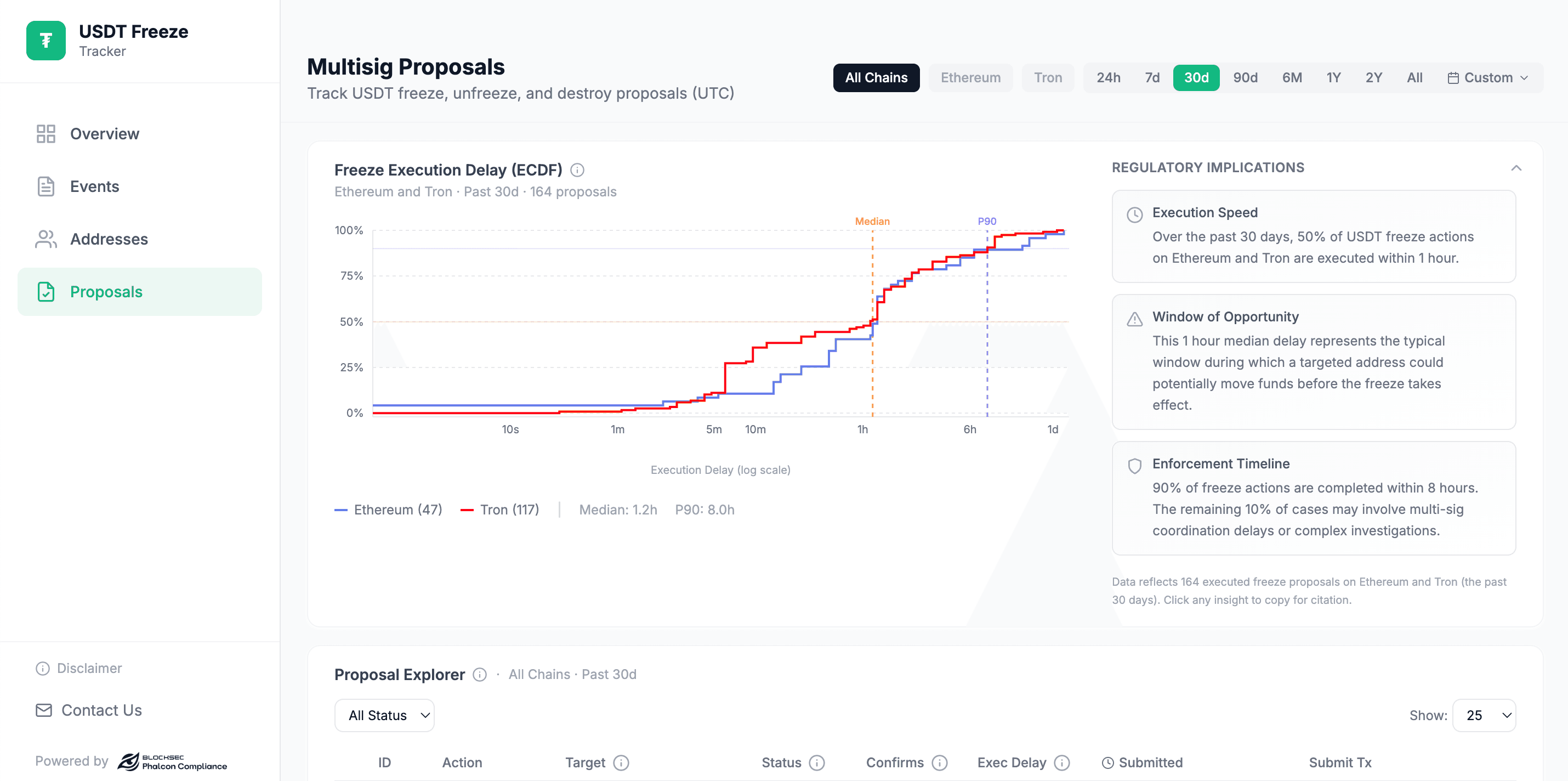
提案:追踪相关的治理行动
提案页面显示与 USDT 冻结和解冻相关的已完成多签提案。它还提供详细的监管影响,以帮助解释每个提案的含义。
您可以查看执行速度、操作窗口和强制执行时间表等关键信息。这让您更清晰地了解冻结决策是如何执行的,以及它们如何与加密行业的更广泛监管实践联系起来。
该工具涵盖了从总体概览到特定地址搜索的所有内容。它有助于事件追踪,并解释冻结背后的规则。它非常适合需要 USDT 地址查询的普通用户和行业专家。所有数据均直接来自原生的以太坊和波场链上源。这确保了准确性并提供实时更新。
为了更好地保护您的平台并确保无缝合规,请探索Phalcon Compliance如何帮助您实时识别、分析和减轻风险。立即开始保护您的加密操作。



