我们很高兴地宣布,Solana 已集成到我们的综合追踪和调查平台 MetaSleuth 中!
随着 Solana 生态系统的不断扩展,我们认识到需要强大的工具来导航和分析其区块链。现在 Solana 已在 MetaSleuth 上上线,用户可以轻松地探索 Solana、追踪资金和进行尽职调查 (DYOR),并与他人分享宝贵的见解。
Solana 在 MetaSleuth 上的集成
Solana 在数据存储和管理方面的创新方法使其区别于以太坊等其他区块链。特别是 Solana 的代币账户设计提供了独特的优势。为了在 MetaSleuth 上为用户提供清晰的代币资金分析和见解,我们实施了特殊的设计元素:
- Solana 账户的所有者账户信息现已包含在内,可在地址面板中访问。
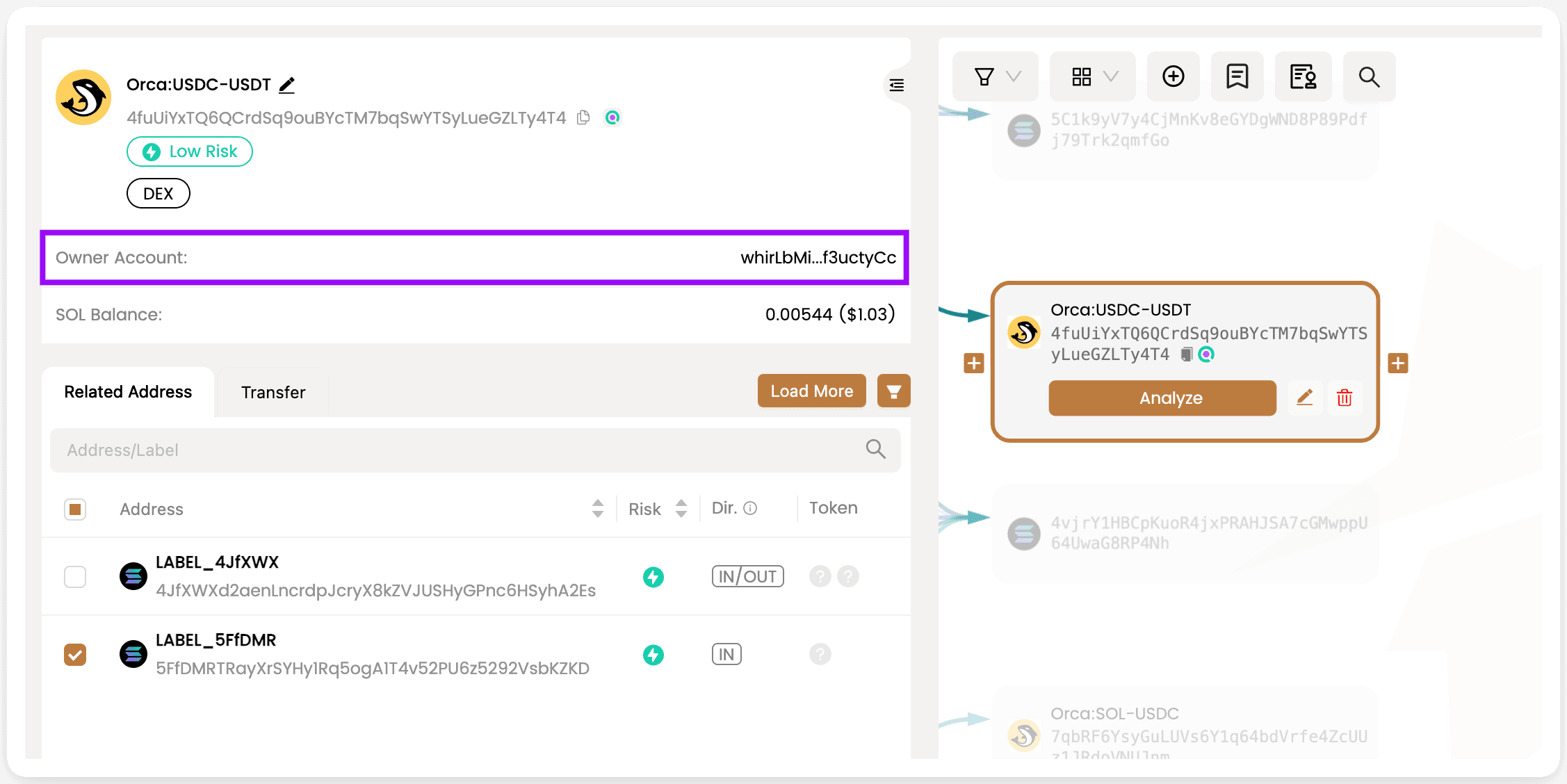
-
为了保持清晰并避免用户因过多的单个代币账户详细信息而不知所措,我们选择不在 MetaSleuth 画布上显示代币账户。
-
相反,当用户输入代币账户进行分析时,我们提供了一个集中的方法。例如,在分析由“Solend 主池金库”拥有的 USDC 代币账户“2bx7rHMpDUthvur8qnUJN9dNUsjKVE9S6tN16B78FoRG”时,我们提供了金库 USDC 资金流的清晰视图。这种定制的分析可以更深入地了解 Solana 生态系统内的资金流动。
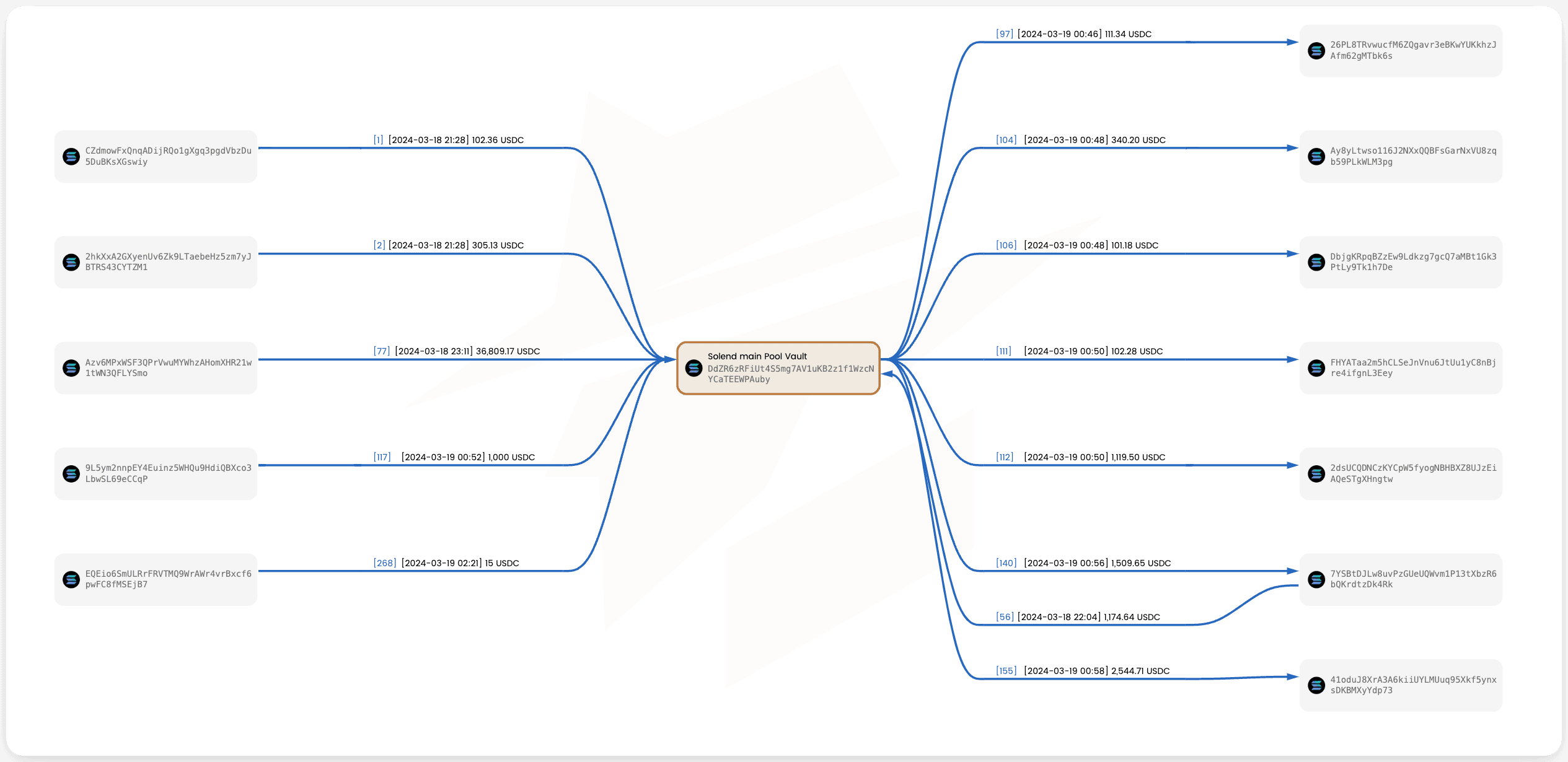
这些优化设计增强了清晰度,并为用户在 MetaSleuth 平台上提供了 Solana 上代币资金的精确分析。请在此处亲自尝试: https://metasleuth.io/result/solana/2bx7rHMpDUthvur8qnUJN9dNUsjKVE9S6tN16B78FoRG
案例研究:Slope 钱包黑客事件
2022 年 8 月,发生了一起重大事件,导致超过 8,000 个 Solana 钱包被盗,损失约 520 万美元。攻击者的利润分布在四个不同的账户中:
GeEccGJ9BEzVbVor1njkBCCiqXJbXVeDHaXDCrBDbmuy
5WwBYgQG6BdErM2nNNyUmQXfcUnB68b6kesxBywh1J3n
CEzN7mqP9xoxn2HdyW6fjEJ73t7qaX9Rp2zyS6hb3iEu
Htp9MGP8Tig923ZFY7Qf2zzbMUmYneFRAhSp7vSg4wxV
要开始调查,请在“保存的图表/共享链接”面板中打开一个带有空画布的新图表。将这四个攻击者账户添加到画布上,然后对于每个账户,单击“展开出站”以追踪被盗资金的去向。似乎攻击者持有资金数月,然后从 2023 年 3 月开始进行转账和洗钱活动。
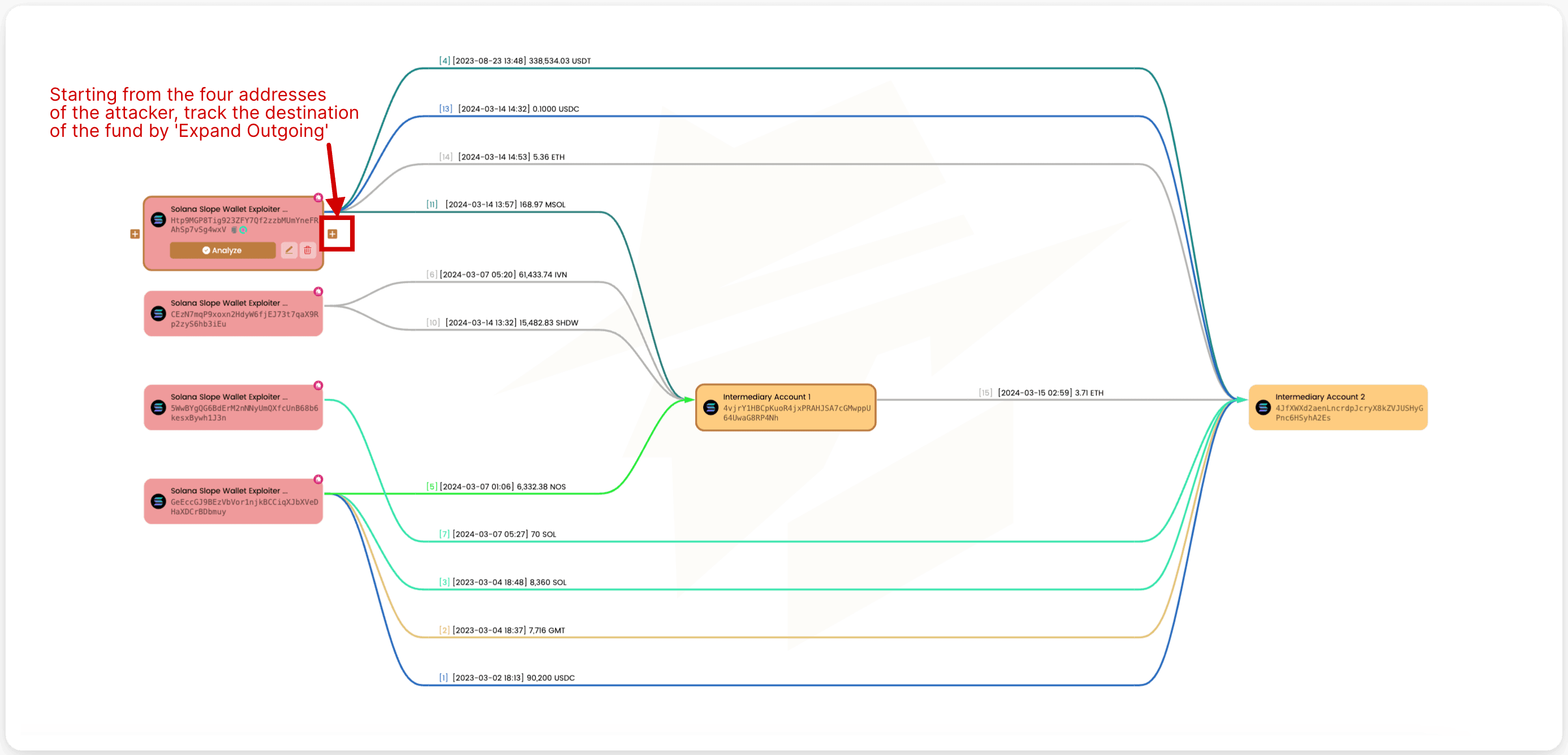
大多数资金的账户4JfXWX,随后被兑换并进一步转账。截至今天,仍有大量资金未在此账户中转出。
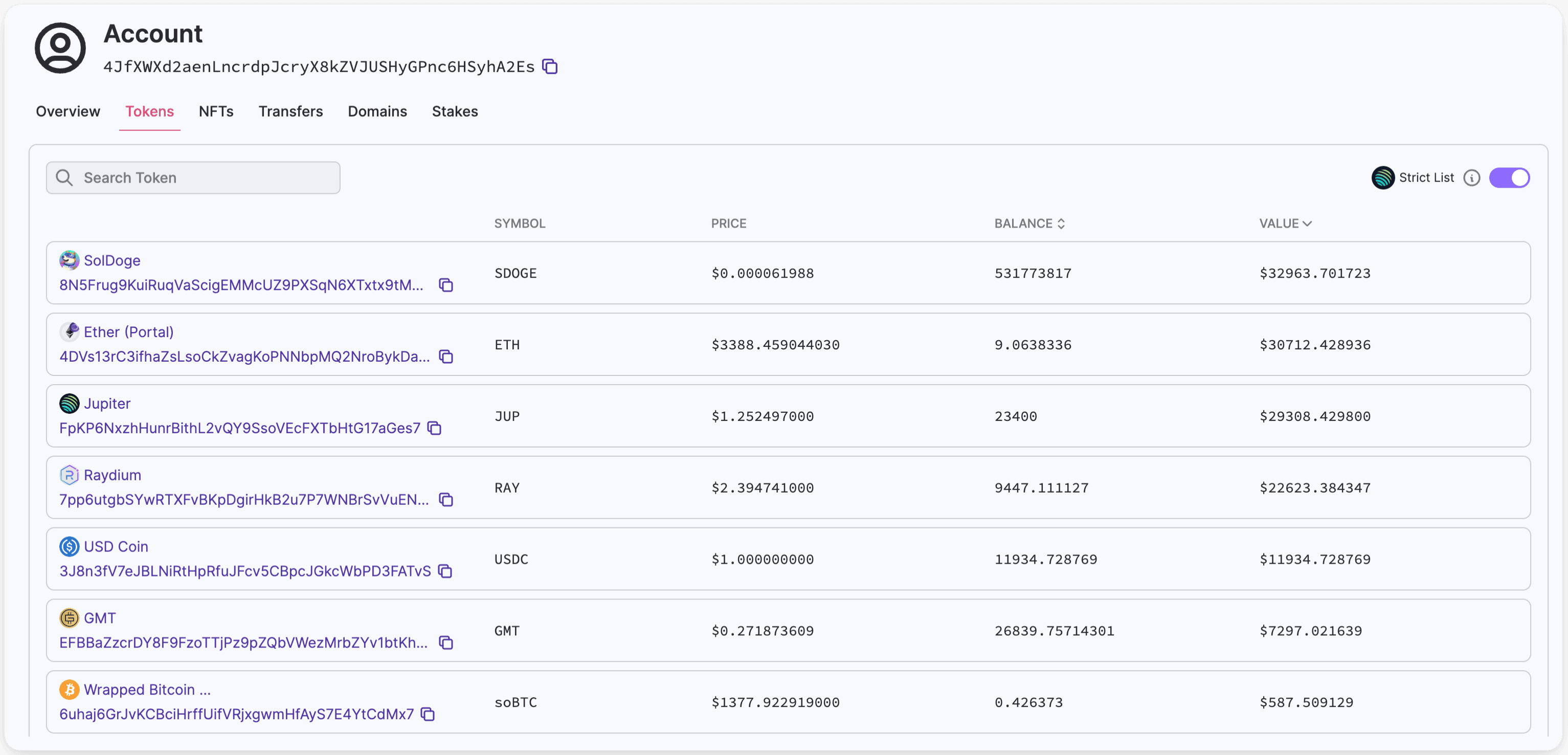 https://solana.fm/address/4JfXWXd2aenLncrdpJcryX8kZVJUSHyGPnc6HSyhA2Es/transactions
https://solana.fm/address/4JfXWXd2aenLncrdpJcryX8kZVJUSHyGPnc6HSyhA2Es/transactions
由于所有 USDT 代币都已从该账户转出,我们的首要任务是追踪 USDT 的后续转账,因为它们可能会提供关键线索。进一步调查发现,这些资金已发送到币安。经过进一步分析,原来攻击者利用了一个即时加密货币兑换服务,该服务依赖币安将资金转移到另一个区块链。对于正在进行的调查,您可以根据从即时加密货币兑换服务获得的信息匹配相应的交易。更多详情,请参阅此推文:
https://twitter.com/zachxbt/status/1711748033954590900
 https://metasleuth.io/result/solana/GeEccGJ9BEzVbVor1njkBCCiqXJbXVeDHaXDCrBDbmuy?source=ff950aab-a7a2-4bd0-a3b0-efb4c60a5a63
https://metasleuth.io/result/solana/GeEccGJ9BEzVbVor1njkBCCiqXJbXVeDHaXDCrBDbmuy?source=ff950aab-a7a2-4bd0-a3b0-efb4c60a5a63
不要犹豫,立即前来试用!
关于 MetaSleuth
MetaSleuth 是 BlockSec 开发的一个综合平台,旨在协助用户有效追踪和调查所有加密货币活动。借助 MetaSleuth,用户可以轻松追踪资金、可视化资金流、监控实时资金动向、保存重要信息,并通过与他人分享他们的发现来协作。目前,我们支持 13 种不同的区块链,包括比特币 (BTC)、以太坊 (ETH)、TRON (TRX)、Polygon (MATIC) 等。
Twitter:@MetaSleuth
Telegram:https://t.me/MetaSleuthTeam




