CVE-2021-39137 是一个在几天前被报告并修复的漏洞。然而,并非所有以太坊节点都应用了此补丁。我们观察到此漏洞已被恶意交易利用。
攻击交易
https://tx.blocksecteam.com/tx/0x1cb6fb36633d270edefc04d048145b4298e67b8aa82a9e5ec4aa1435dd770ce4
该交易有一个指向 0x4 地址的 STATICCALL。这是一个预编译的智能合约 dataCopy。参数如下:
inOffset = 0, inSize = 32, retOffset = 7, retSize = 32。
0x4 智能合约
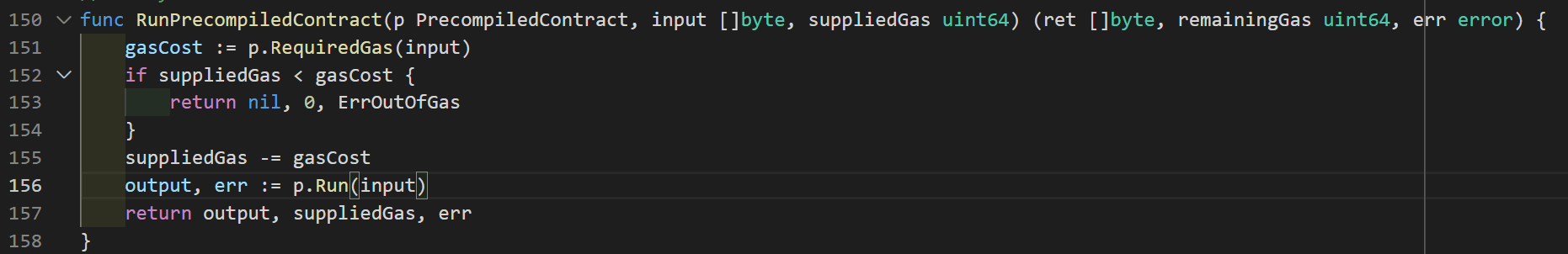
图 1
由于 STATICCALL 的目标是 0x4 预编译合约,它将执行图 1 中的 RunPrecompiledContract 函数。
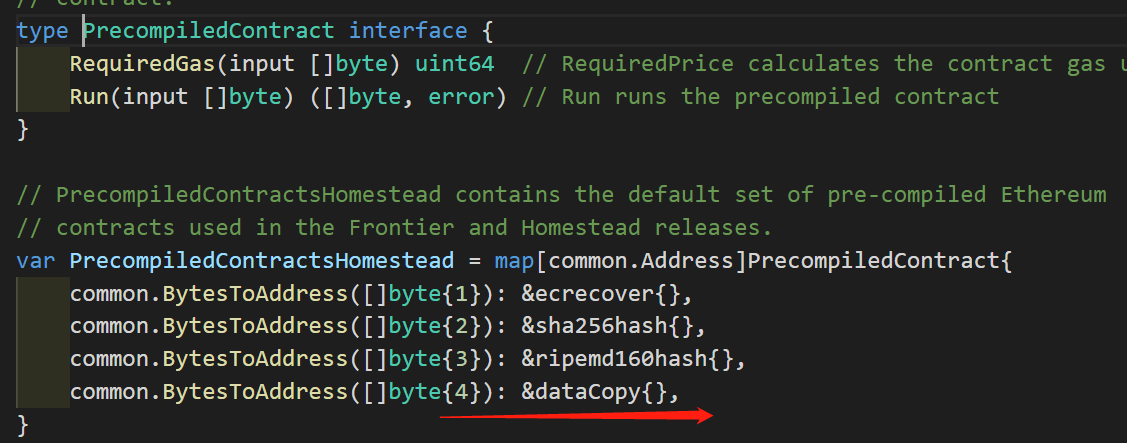
图 2

图 3
根据图 2/3,0x4 智能合约只是返回 in 指针的引用。
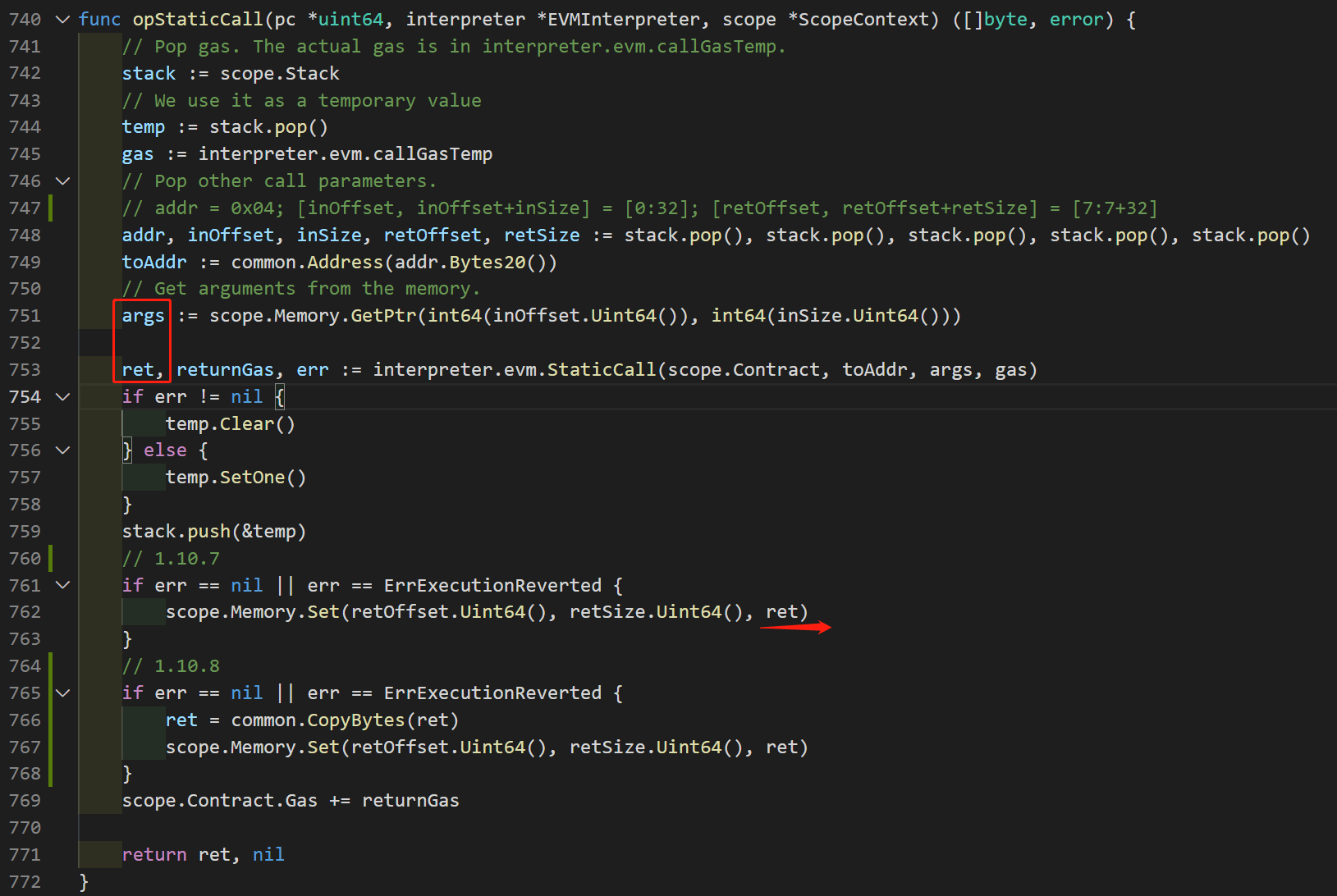
图 4
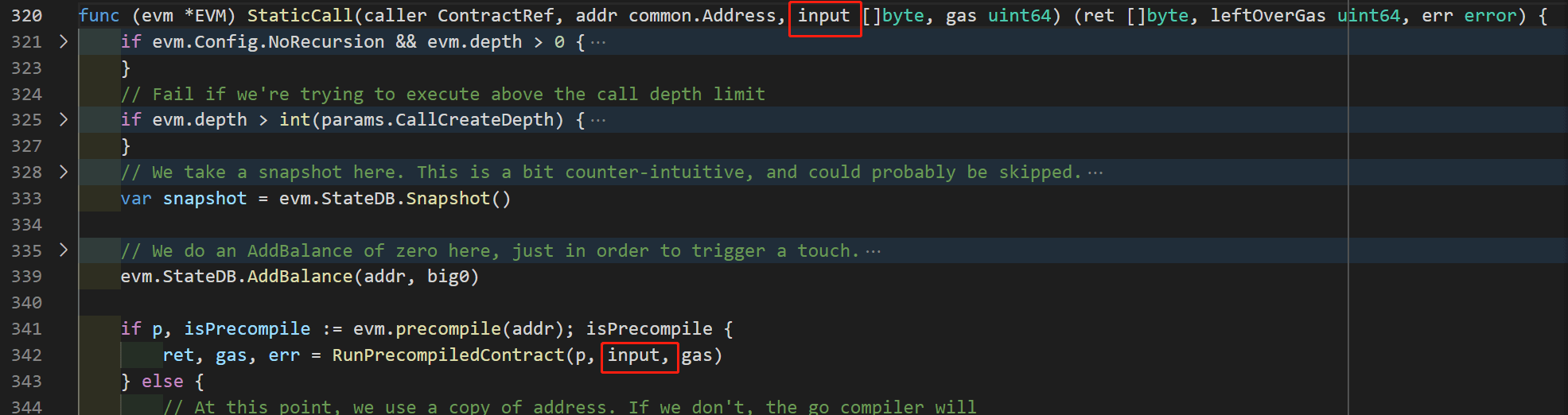
图 5
图 4 是 STATICCALL 操作码的代码。在第 751 行,args 指向 EVM 内存的 [inOffset ~ inOffset + inSize] 部分,即 Mem[0:32]。
根据图 5 以及对 0x04 代码逻辑(图 2/3)的分析,返回值 (ret) 是指向与 args 相同内存的引用。也就是说,它也指向 Mem[0:32]。
漏洞
在有漏洞的代码(版本 1.10.7)中,第 762 行将 ret 的内容复制到 Mem[retOffset : retOffset + retOffset],即从 Mem[0:32] 复制到 Mem[7:7+32]。此操作意外地改变了 ret 的内容。这意味着 0x4 预编译合约的返回值已被修改。
在已修复的版本(1.10.8)中,它复制了 ret(第 766 行)。由于第 767 行的复制操作不会修改 ret 的内容,因此可以修复此漏洞。
由于节点未及时更新补丁,CVE-2021–39137 漏洞被恶意交易利用。此缺陷涉及以太坊虚拟机内存操作中的一个缺陷,但已在 1.10.8 版本中修复。为确保系统安全,建议所有以太坊节点立即更新到最新版本。
致谢
本次攻击由 BlockSec 的 Siwei Wu, Yufeng Hu, Lei Wu, Yajin Zhou 分析。




