2022年11月08日,我们发现一些攻击成功地从基于Sushi官方KashiPairMediumRiskV1合约(或从其分叉的合约)构建的池中提取了资产。经过调查,我们发现根本原因是由于一个逻辑错误导致代币价格计算失误。
我们立即联系了Sushi的安全团队,他们证实了我们的发现。好消息是,他们正在采取行动保护一些有价值但易受攻击的池免受攻击。此外,他们还提供了赔偿因漏洞利用而损失资金的受害者的程序。因此,我们现在认为披露漏洞和攻击的详细信息是安全的。在本报告中,我们将提供详细的分析。
漏洞分析
在分析了KashiPairMediumRiskV1合约的源代码后,我们得出结论,该bug存在于borrow函数中,该函数在solvent修饰符中使用过时的exchangeRate来验证借款份额。具体来说,验证将基于_isSolvent函数中exchangeRate的当前值进行。
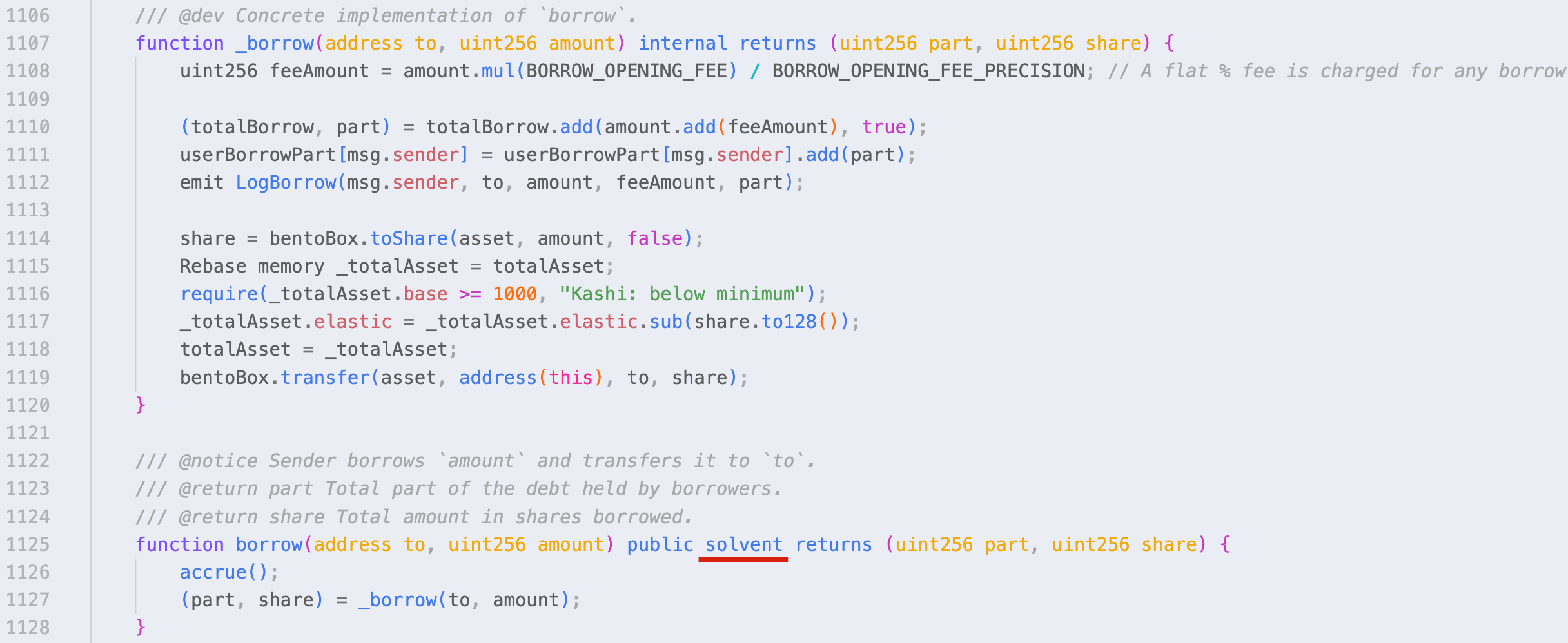
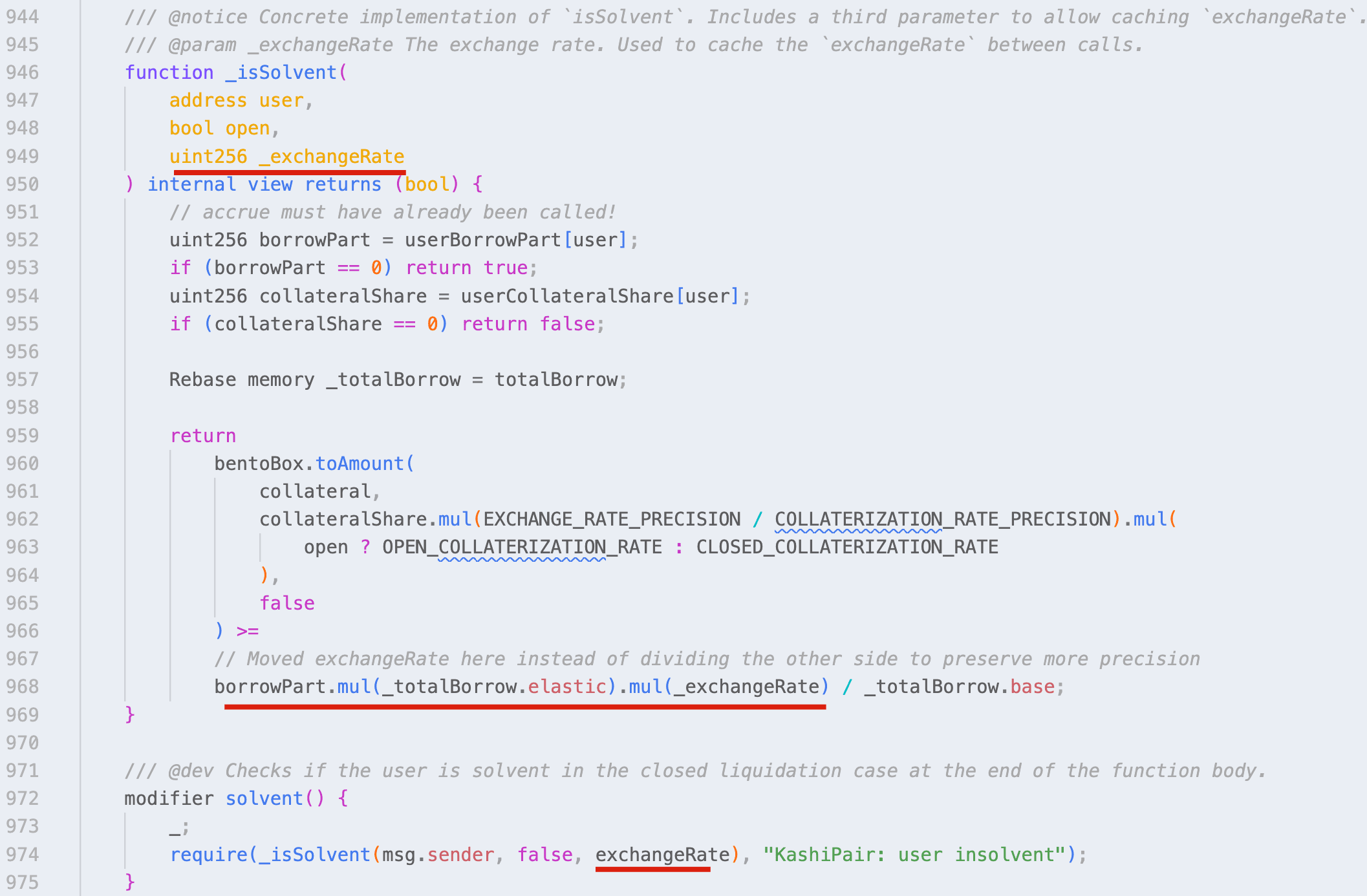
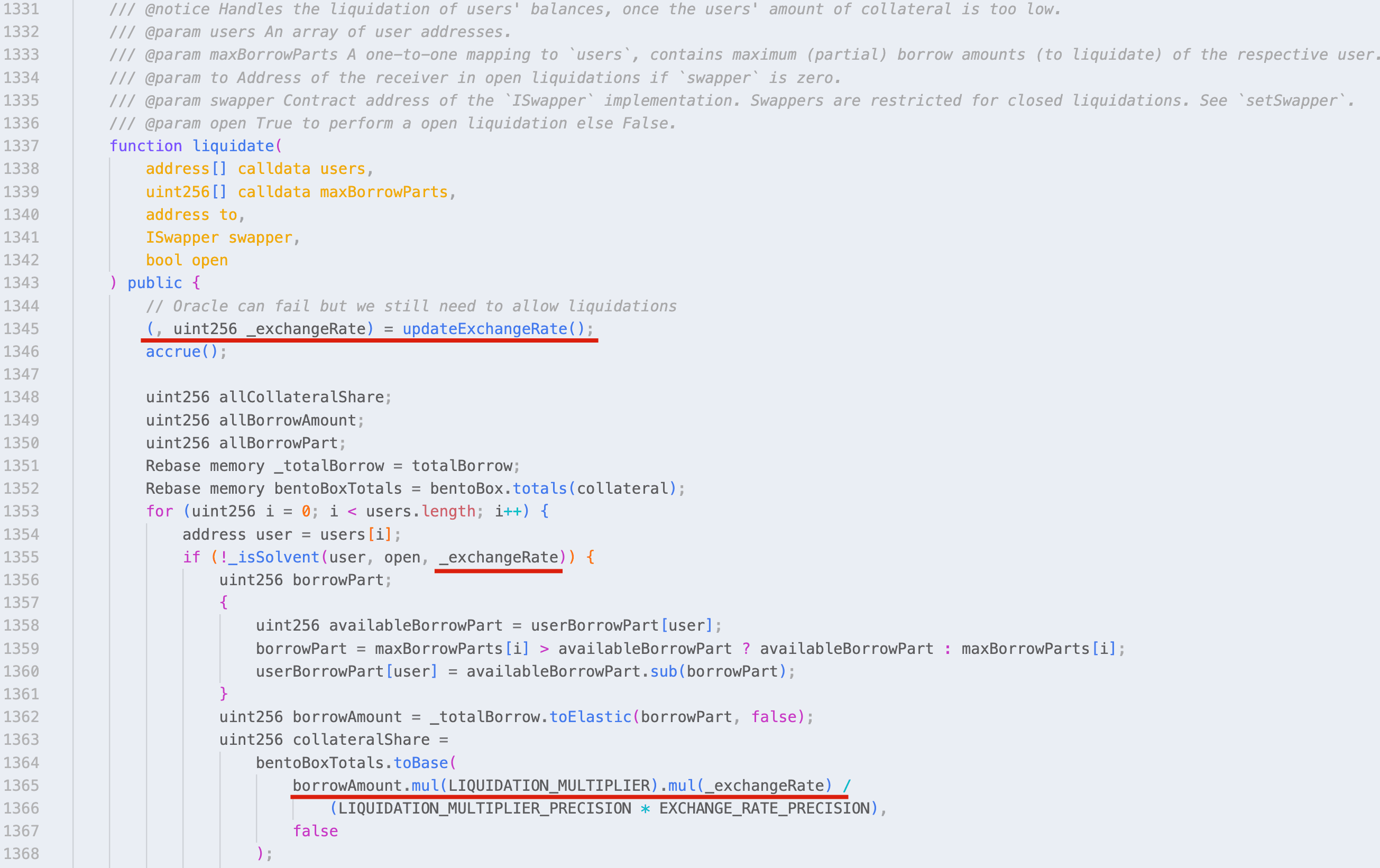
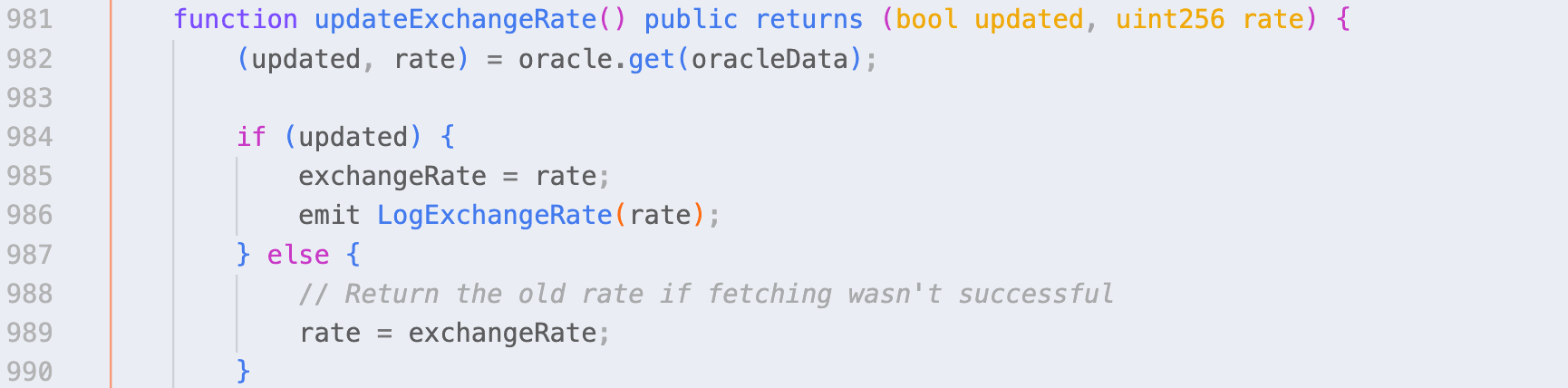
而在liquidate函数中,updateExchangeRate函数在最开始就被调用。因此,验证和计算将基于更新后的值进行。
显然,这个bug可能被利用来导致(巨大的)价格差异。
攻击分析
我们观察到两次攻击:
- 0xcf8f242ea83100b6d43e659f7f53a698d304fc6ac2ca6fe79e3e07ee05fefe58:受害者使用KashiPairMediumRiskV1合约,损失约为9,466 USDC。
- 0x3d163bfbec5686d428a6d43e45e2626a220cc4fcfac7620c620b82c1f2537c78:受害者是一个使用CauldronMediumRiskV1(KashiPairMediumRiskV1的分叉)的策略合约,损失约为110,911 MIM。
请注意,第一次攻击交易是由一个机器人发起的,该机器人抢跑了原始攻击交易:0x7a845d8d2af7919f5b9e22dd5571305cb5347d17986a8402715c1463d515fc18,原始攻击者地址是0xb7ea0f0f8c6df7a61bf024db21bbe85ac5688005。
这里我们以第一次攻击交易为例,该交易包含以下步骤:
- 从
Balancer借入40,900 BADGER和121,904 USDC的闪电贷。 - 将40,900 BADGER和113,599 USDC存入
BentoBox。 - 调用kmBADGER/USDC-LINK的
addCollateral函数,存入40,900,000,000,000,000,000,000份BADGER份额。 - 调用kmBADGER/USDC-LINK的
addAsset函数,存入112,529,000,000份USDC份额。 - 调用
borrow函数,借入120,755,095,093份USDC份额。 - 调用
UpdateExchangeRate函数。 - 调用
liquidate函数进行自我清算。 - 从
BentoBox提取40,899 BADGER和123,006 USDC。 - 偿还闪电贷,获得约9466 USDC的利润。
请注意,步骤6并非必需,因为
borrow函数会调用UpdateExchangeRate函数。
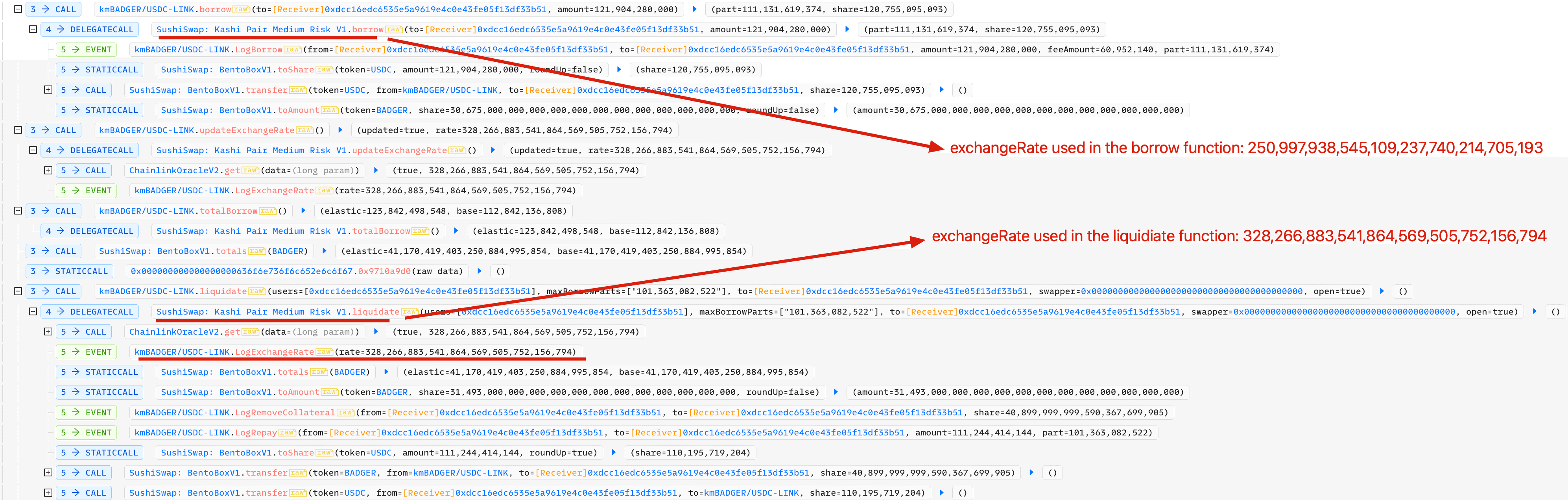
关键步骤如下:
 不难发现,
不难发现,borrow函数中使用的exchangeRate值与liquidate函数中使用的值存在偏差:
- 在
borrow函数中:250,997,938,545,109,237,740,214,705,193 - 在
liquidate函数中:328,266,883,541,864,569,505,752,156,794
影响
有数十个池(在以太坊和BSC上)可能受到此bug的影响。缓解此问题的临时方法是通过(或周期性地)调用UpdateExchangeRate函数来减少或消除偏差。许多受影响的项目已经采用了这种方法,并且可以在实际交易中观察到相应的交易。
启示
确保DeFi项目的安全并非易事。除了代码审计,我们认为社区应该采取积极主动的方法来监控项目状态,并在攻击发生之前阻止它。
关于BlockSec
BlockSec是一家开创性的区块链安全公司,由一群全球杰出的安全专家于2021年创立。公司致力于提升新兴Web3世界的安全性和可用性,以促进其大规模采用。为此,BlockSec提供智能合约和EVM链安全审计服务、用于安全开发和主动阻止威胁的Phalcon平台、用于资金追踪和调查的MetaSleuth平台,以及用于Web3开发者在加密世界高效冲浪的MetaDock扩展。
截至目前,公司已为MetaMask、Uniswap Foundation、Compound、Forta和PancakeSwap等300多家尊贵客户提供服务,并在两轮融资中获得了由Matrix Partners、Vitalbridge Capital和Fenbushi Capital等知名投资者提供的数千万美元投资。
官方网站:https://blocksec.com/ 官方Twitter账号:https://twitter.com/BlockSecTeam




