2025年11月19日、米国財務省OFACは、元カナダオリンピックのスノーボーダーであるライアン・ジェームズ・ウェディング氏、およびその主要な協力者や事業を制裁対象とした。この措置により、彼らが米国に保有する全ての資産が凍結され、米国人は彼らとの一切の商取引が禁止された。
その後まもなく、米国国務省は、ウェディング氏の逮捕に繋がる情報提供者への懸賞金を1500万ドルに引き上げた。メキシコ大使館は、情報提供の方法に関するガイドラインを発表した。同時に、FBI、カナダ王立騎馬警察(RCMP)、メキシコ警察は、合同での国際的な捜査を開始した。「オリンピック選手出身の麻薬王」に対するこの作戦は、暗号資産、麻薬密売、連続殺人事件の暗い繋がりを明らかにするものである。
BlockSecは、先進的なオンチェーン追跡と専門的な調査を駆使し、ウェディング氏のスポーツスターから悪名高い犯罪組織のボスへの道を詳細に追跡した。「ライアン・ウェディング暗号資産犯罪ネットワーク」に焦点を当て、彼がいかにブロックチェーン技術を悪用して、違法な資金洗浄のための「隠された」ネットワークを構築したかを分析している。
オリンピック選手から「最重要指名手配犯」へ

1976年、オンタリオ州サンダーベイで生まれたライアン・ジェームズ・ウェディング氏は、かつてはウィンタースポーツの有望なスターであった。鋭い技術と安定したパフォーマンスでカナダナショナルチームに選ばれ、2002年ソルトレイクシティ冬季オリンピックでは男子パラレル大回転に出場し、母国を代表した。当時、彼はカナダのウィンタースポーツ界の著名な顔であった。彼はスポットライトを愛していたが、その注目は彼に早急な成功への危険な願望を掻き立てた。
オリンピック後、ウェディング氏の人生は急転した。チームに残るオファーを断り、スキーキャリアを後にし、代わりに危険なビジネスの世界に足を踏み入れた。後に、国際的な麻薬密売組織と結びついた。2008年、彼はカリフォルニアでコカイン密輸の容疑で逮捕され、2010年に禁固4年の刑を宣告された。 しかし、刑務所は彼を更生させることはなかった。むしろ、それは彼の犯罪キャリアの出発点となり、そこで他の犯罪者と出会い、将来の麻薬ネットワークを構築する手助けを得た。釈放後、彼は「オリンピック選手」という仮面を完全に剥ぎ取り、スペイン語で「ボス」を意味する「El Jefe」というニックネームを名乗るようになった。彼はライアン・ウェディング麻薬密売組織を結成し、現在、当局はこれを主要な犯罪組織としてリストアップしている。
ウェディング氏の組織は、暴力性と高度な組織化で知られている。 彼らは、2024年に米国によってテロ組織と指定されたメキシコのシナロア・カルテルと緊密に協力している。彼らは共に、コロンビアの生産地からメキシコを経由し、最終的に米国とカナダへコカインを密輸している。年間約60トンの薬物を密輸し、年間10億ドル以上の収益を上げている。この違法ビジネスは、カナダの国家安全保障にとって重大な脅威となっている。
ウェディング氏は、このネットワークを守るために致命的な武力を行使している。2023年11月、彼は盗まれた薬物貨物に関して、オンタリオ州の家族への攻撃を命じた。 この残忍な攻撃により、両親が死亡し、一人が重傷を負った。2024年4月から5月にかけて、彼のギャングは、薬物借金を抱えた個人を罰するために、さらに2件の殺人を犯した。 2025年1月、彼はコロンビアで連邦証人を殺害するよう命じ、自身の痕跡を消そうとした。 被害者はレストランで5回撃たれ、即死した。ウェディング氏の弁護士は、この犯罪の計画にも関与し、証人を殺害することで告訴を取り下げるよう提案した。
2025年3月、ウェディング氏は、指名手配犯アレクシス・フローレスに代わって、FBIの「最重要指名手配犯10人リスト」に正式に加えられた。インターポールも彼の逮捕状であるレッド・ノーティスを発行した。現在、彼はメキシコに潜伏しており、「エル・ヘネラル」として知られる高位のカルテル構成員に保護されていると考えられている。ウェディング氏は、暗号化されたメッセージングアプリを使用して犯罪ネットワークを遠隔で運営し、VRG EnergéticosやGrupo RVG Combustiblesのようなメキシコの企業を、犯罪活動を隠蔽するための合法的なフロントとして利用している。
ライアン・ウェディング暗号資産犯罪ネットワークの資金洗浄プロセスを解明する
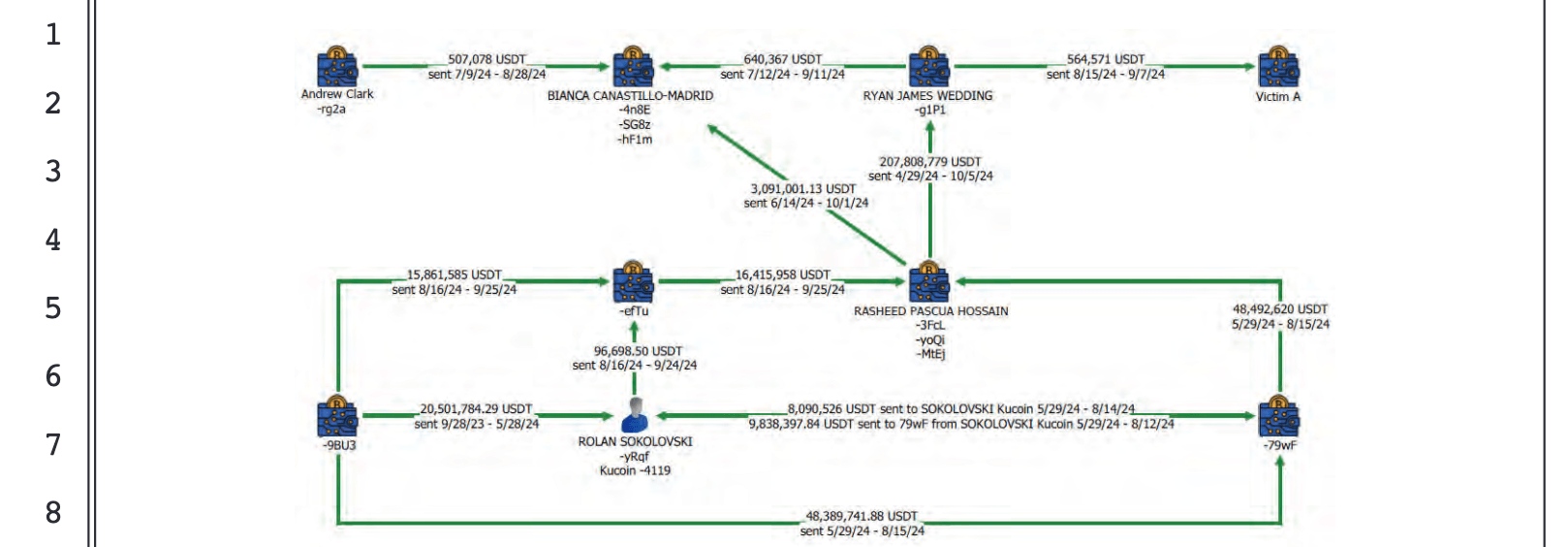
起訴状によると、ウェディング犯罪グループは、米ドル、カナダドル、および暗号資産を使用して薬物収益を洗浄している。暗号資産については、取引の足跡を不明瞭にするために特定の手段を採用している。彼らは、巨額の資金を多数の小額送金に分割し、中間USDTウォレットを通じて迅速に資金を移動させる。最終的に、全ての資金はウェディング氏が直接管理する中央のテザーウォレットに到達する。この洗練されたアプローチは、ライアン・ウェディング暗号資産犯罪ネットワークの特徴である。
いくつかの主要人物がこれらの洗浄業務を担当している。主なオペレーターは、ソコの詳細、ホセイン、カナスティロ・マドリッドである。彼らは、大陪審で知られている者と知られていない者を含む他の個人とも協力している。彼らは共に、「ウェディング犯罪組織」のメンバーとして活動している。
薬物収益の洗浄:暗号資産の流れ
公式な起訴状は、ライアン・ウェディング暗号資産犯罪ネットワークが不正な利益を洗浄するために行われた複雑な手順を詳述している。
- 隠蔽: ウェディング犯罪組織は、コカイン販売による多額の収益を、米ドル、カナダドル、および暗号資産で隠蔽する。
- 洗練されたテザーネットワーク: 暗号資産の使用に関して、資金の出所を不明瞭にするため、ウェディング犯罪組織のメンバーおよび協力者は、洗練されたテザーネットワークを使用して、(1)巨額の資金を小額送金に分割し、(2)中間USDTウォレットを迅速に使用して、最終的に被告人ウェディングが管理するハブテザーウォレットに到達する前に資金を移動させる。
- 主要オペレーター: 被告人ソコの詳細、ホセイン、カナスティロ・マドリッド、および大陪審で知られている、または知られていないその他の個人は、ウェディング犯罪組織のメンバーおよび協力者、すなわち被告人ウェディングおよびクラークとして、彼らの麻薬密売収益を隠蔽し、その収益を使用して組織の目的を遂行し、促進する役割を果たす。この洗浄システムの簡略化されたフローチャートを以下の図に示す。
以下のテキストは、起訴状に概説されている、資金洗浄プロセスの詳細を説明している。
薬物収益の洗浄: overt Act
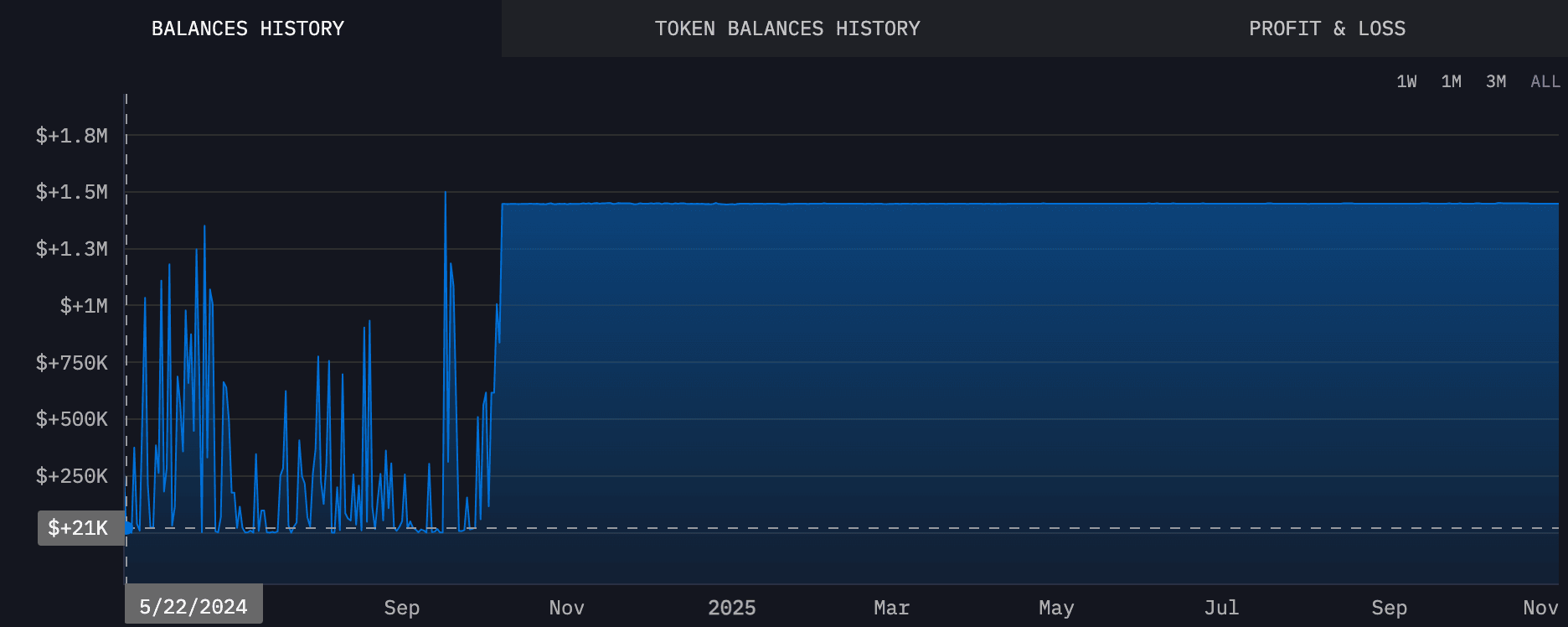
- Overt Act No. 71: 2023年9月28日から2024年5月28日の間、被告人ソコの詳細氏は、共謀者の管理するテザーウォレット(-9BU3)から、自身のKucoinアカウント(-4119)に約20,501,784.29 USDTを受け取った。
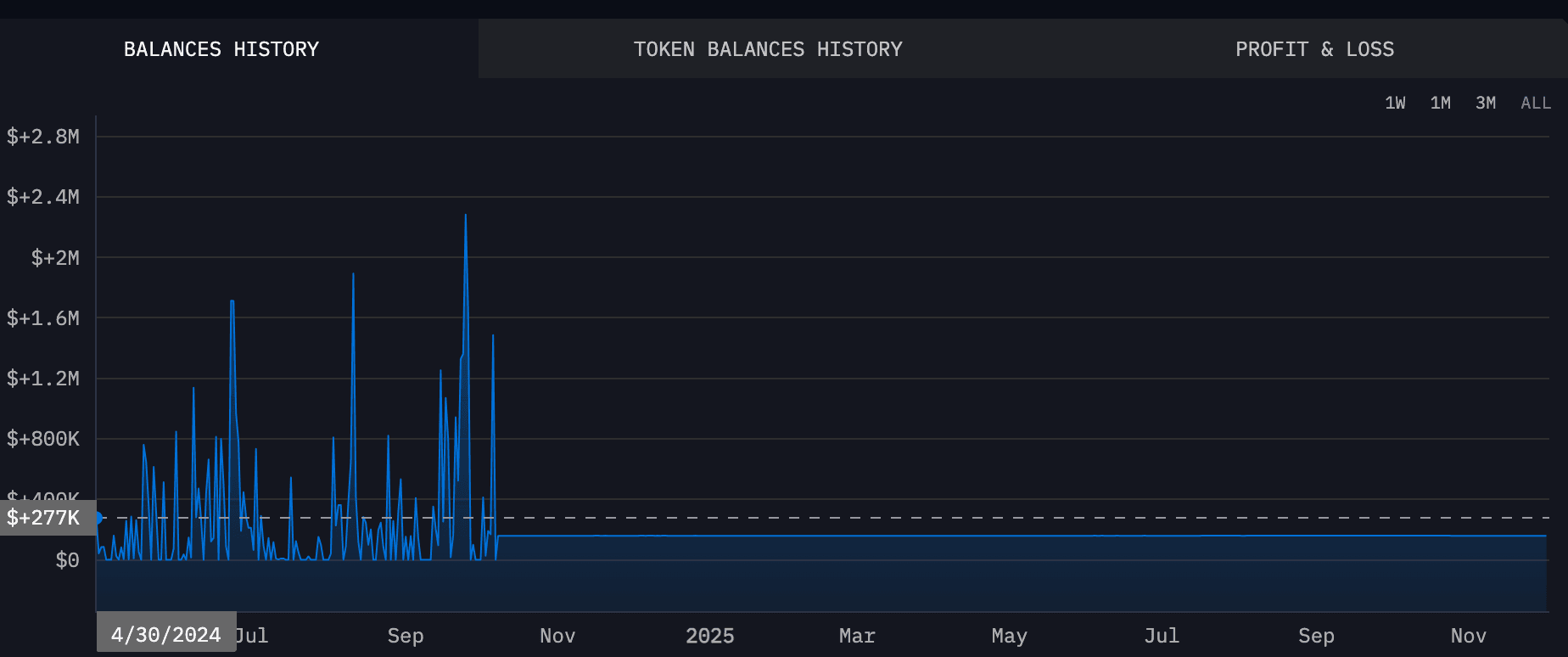
- Overt Act No. 72: 2024年5月29日から2024年8月15日の間、被告人ホセイン氏は、共謀者の管理するテザーウォレット(-79wf)から、自身のテザーウォレット(-3FcL)に約48,492,620 USDTを受け取った。
- Overt Act No. 73: 2024年5月29日から2024年8月14日の間、共謀者の管理するテザーウォレット(-79wf)は、被告人ソコの詳細氏のKucoinアカウント(-4119)に約8,090,526 USDTを送信した。
- Overt Act No. 74: 2024年5月29日から2024年8月12日の間、被告人ソコの詳細氏は、自身のKucoinアカウント(-4119)を使用して、共謀者の管理するテザーウォレット(-79wf)に約9,838,397.84 USDTを送信した。
- Overt Act No. 75: 2024年6月14日から2024年10月1日の間、被告人ホセイン氏は、自身のテザーウォレット(-yoQiおよび-MtEj)を使用して、被告人カナスティロ・マドリッド氏のTRONウォレット(-4n8E)に約3,091,001.13 USDTを送信した。
- Overt Act No. 76: 2024年4月29日から2024年10月8日の間、被告人ホセイン氏は、テザーウォレット(-yoQi)を使用して、その総資金の約98.86%、すなわち約207,808,779 USDTを被告人ウェディング氏のテザーウォレット(-glPl)に送信した。
- Overt Act No. 77: 2024年6月18日、ボニラ氏は、被告人ウェディング氏とクラーク氏への薬物借金を精算するために、約17,300 USDTを被告人ホセイン氏のテザーウォレット(-yoQi)に送金した。
- Overt Act No. 78: 2024年7月9日から2024年11月5日の間、被告人カナスティロ・マドリッド氏は、クラーク氏が管理するテザーウォレット(-rg2a)から、自身の2つのTRONウォレット(-4n8Eおよび-SG8z)に約507,078 USDTを受け取った。
- Overt Act No. 79: 2024年7月12日から2024年9月11日の間、被告人カナスティロ・マドリッド氏は、被告人ウェディング氏のテザーウォレット(-g1P1)から、自身の2つのTRONウォレット(-4n8Eおよび-SG8z)に約640,367 USDTを受け取った。
- Overt Act No. 80: 2024年8月15日から2024年9月7日の間、被告人ウェディング氏は、テザーウォレット(-glPl)を使用して、仲介役として行動していた被害者Aに約564,571 USDTを提供し、コロンビアの被告人リアスコス氏から約300キログラムのコカインを購入させた。
- Overt Act No. 81: 2024年8月16日から2024年9月24日の間、被告人ソコの詳細氏は、自身のKucoinアカウント(-4119)を使用して、共謀者の管理するテザーウォレット(-efTu)に約96,698.50 USDTを送信した。
- Overt Act No. 82: 2024年6月14日から2024年10月1日の間、被告人カナスティロ・マドリッド氏は、被告人ホセイン氏が管理する3つのテザーウォレット(-3FcL、-yoQi、および-MtEj)から、自身の2つのTRONウォレット(-4n8Eおよび-SG8z)に約3,091,001.13 USDTを受け取った。
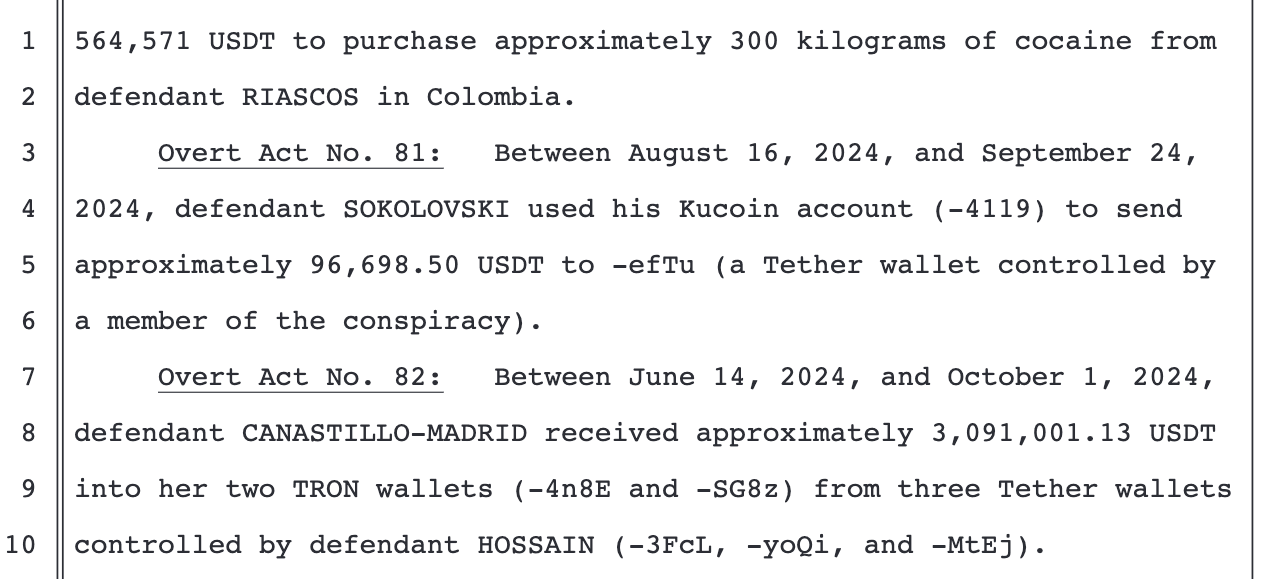
私たちは、BlockSecのオンチェーン分析能力を活用し、以下のチャートで資金洗浄プロセスを可視化しました。
私たちは、これらのアドレスの直接入出金を綿密に分析し、資金の出所と行き先を理解できるようにしました。包括的な関係マップを作成するために、10万ドルを超える送金に焦点を当てました。
暗号資産犯罪ネットワーク内の主要な資金ノードと役割
私たちの関係マップは、ホセイン氏とソコの詳細氏が不正資金の2つの主要な収集センターとして機能していることを明確に示しています。これらのセンターに流入する資金のほとんどは、ウェディング共謀グループとしてラベル付けされたアドレス群から来ています。このグループは、洗浄された「きれいな」資金をチェーンの次のノードに転送する前に、資金洗浄と薬物取引の初期段階を管理しているようです。
その後、資金はこれらの地点から2つの異なる方向に移動します。
- ソコの詳細氏に送金された資金の大部分は、最終的にKuCoinに流入します。これは、彼の主な役割が、中央集権型取引所を利用して洗浄プロセスを完了し、暗号資産を法定通貨に変換することであることを示唆しています。
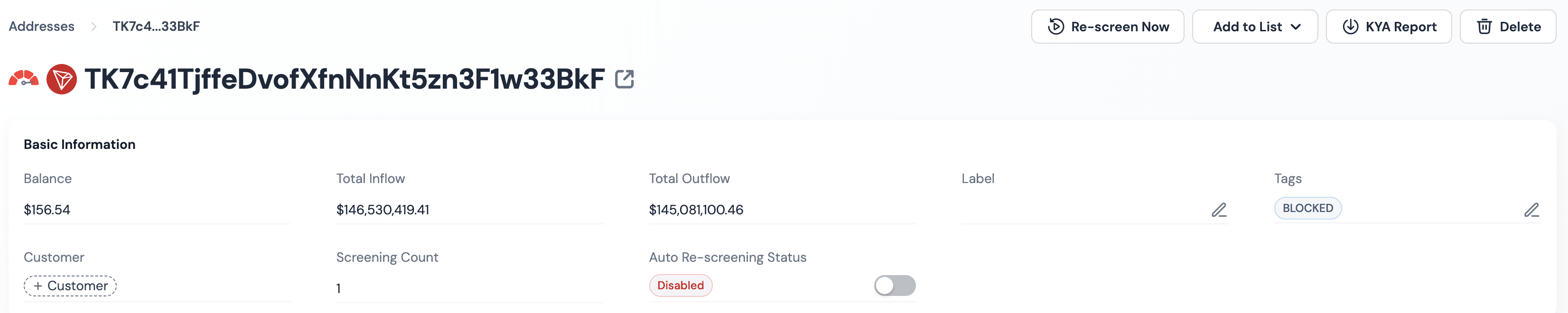
- ホセイン氏に送金された資金は、主にライアン・ジェームズ・ウェディング氏が直接管理するアドレスに移動します。そこから、資金は特定のĐịa chỉ:TK7c41TjffeDvofXfnNnKt5zn3F1w33BkF(SUSPECT-33BkF)に送金されました。このアドレスはその後、Tetherによってブロックされました。
オンチェーン分析によると、SUSPECT-33BkFとWEDDING-g1P1は、ほぼ同時期にアクティブでした。このことから、ウェディング氏がSUSPECT-33BkFをバックアップまたは拡張アドレスとして使用し、ライアン・ウェディング暗号資産犯罪ネットワーク内での資金洗浄活動を継続していたと結論付けるのは妥当です。
**BlockSec Compliance**プラットフォームを使用したSUSPECT-33BkFのさらなる分析により、より重要な詳細が明らかになりました。
- 流入資金の約**99.22%**は、このケースではすべてウェディング氏に関連付けられた、制裁またはフラグ付きアドレスから origin されました。
- 流出資金の約**40%は、現在Tether**によってブロックされているアドレスに送信されました。
これらの資金の出所と行き先は、どちらも高リスクグループと強く結びついています。これは、このアドレスがライアン・ウェディング暗号資産犯罪ネットワークの資金洗浄チェーンにおいて重要な役割を果たしていることを確認しています。
Phalcon: リアルタイム取引分析
Phalconは、複雑なブロックチェーン取引の詳細な洞察を提供する取引分析プラットフォームです。ユーザーはリアルタイムで取引を理解、デバッグ、追跡できます。Phalconの直感的なインターフェースと強力な機能は、開発者、セキュリティ研究者、およびブロックチェーンエコシステムをナビゲートするすべての人にとって不可欠なツールです。
Phalconを探索する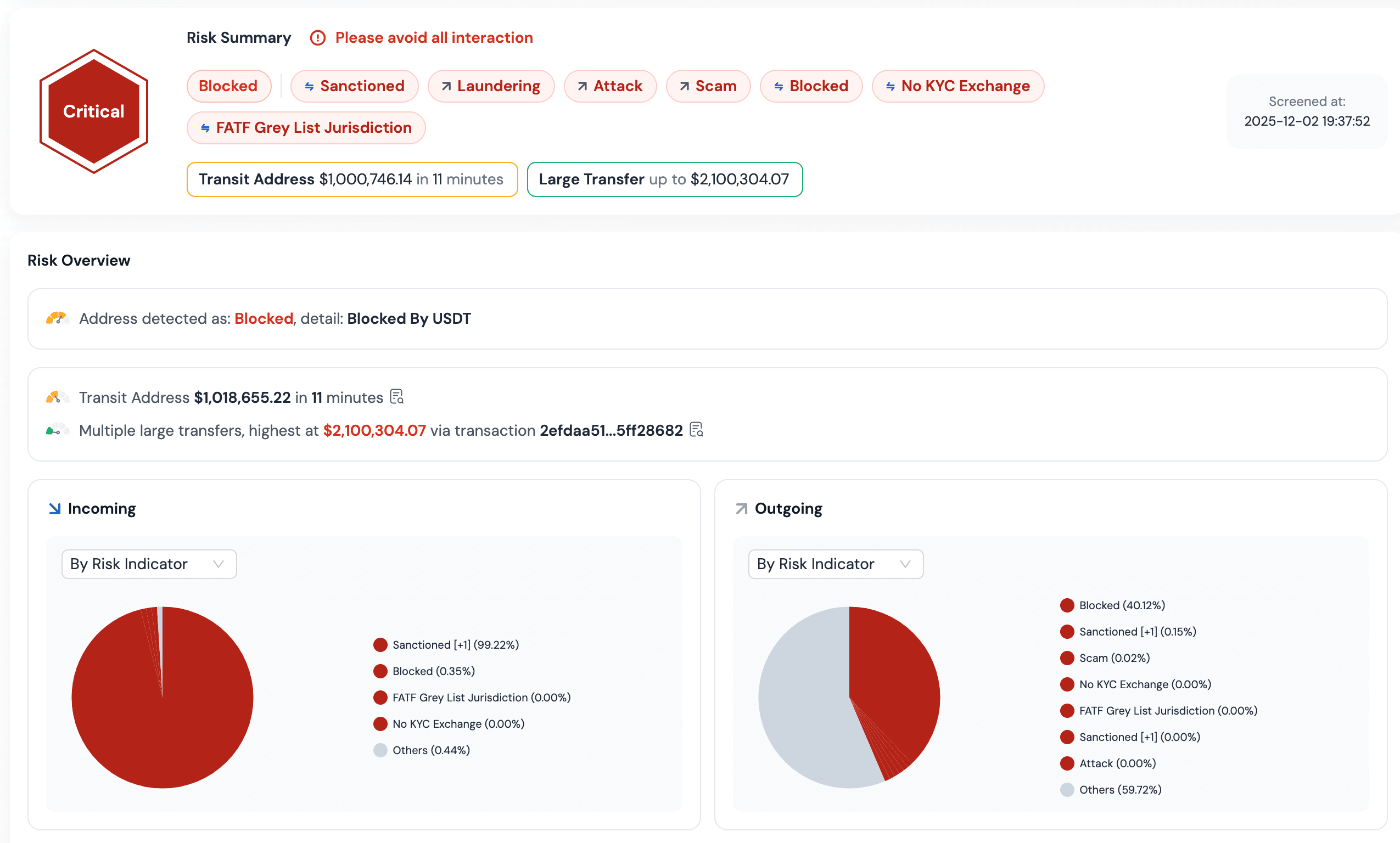
結論:デジタル時代における暗号資産犯罪への対抗
ライアン・ウェディング事件は、孤立した出来事ではありません。BlockSecの調査によると、プライバシーコインが関与する国際犯罪は2024年に187%増加しました。犯罪グループは、暗号資産の使用においてますますプロフェッショナル化し、グローバル化しています。この事件は、規制における重要なギャップを浮き彫りにし、法執行機関およびブロックチェーンセキュリティ企業に貴重な洞察を提供しています。
一般ユーザーにとっては、暗号資産空間で「匿名」が「安全」を意味するという誤解を避けることが重要です。この事件は、専門家でも取引を追跡できることを明確に証明しています。ユーザーが誤って犯罪アドレスとやり取りした場合、資産が凍結されるリスクがあります。規制された取引所を使用し、本人確認を要求しないプラットフォームを避けることが最善です。BlockSecの製品のようなセキュリティツールでウォレットのリスクを定期的にチェックすることも賢明な行動です。
法執行機関および業界にとっては、連携した行動が不可欠です。BlockSecの活動は、犯罪者によって使用されるブロックチェーン技術が、犯罪と戦うための強力なツールでもあることを示しています。アドレスをグループ化し、クロスチェーンの移動を追跡することで、犯罪活動を効果的に暴くことができます。将来的には、各国はデータ共有を強化し、取引所にリアルタイムでの取引監視を義務付ける必要があります。この積極的なアプローチは、不正資金の発生源で阻止し、ライアン・ウェディング暗号資産犯罪ネットワークのような洗練された操作を解体するのに役立ちます。
MetaSleuth: 高度な資金追跡
MetaSleuthは、資金追跡およびフォレンジック分析のための強力なプラットフォームです。セキュリティチームおよび法執行機関が複雑な取引フローを視覚化し、疑わしい活動を特定し、暗号資産の真の出所と行き先を明らかにするのに役立ちます。MetaSleuthを使用すると、ブロックチェーンデータの複雑な網を容易かつ正確にナビゲートできます。
ライアン・ウェディングの転落は悲劇的な物語であり、オリンピック選手から制裁リストに載るまでの道筋を示しています。彼の物語は、テクノロジーは中立的であるが、その応用は善のために導かれる必要があることを思い出させてくれます。BlockSecは、より優れた追跡モデルを構築し、ユーザーを保護し、法執行機関を支援するための最先端のブロックチェーンセキュリティソリューションを提供し続けます。私たちの究極の目標は、安全で、合法で、信頼できる暗号資産の世界です。
現在、ライアン・ジェームズ・ウェディング氏はメキシコに潜伏中です。米国国務省は、1000万ドルの麻薬懸賞金プログラムとFBIからの500万ドルを含む、彼の逮捕に繋がる情報提供者への懸賞金を1500万ドルに引き上げました。メキシコ大使館は、情報提供の方法に関するガイドラインさえも投稿しています。彼の居場所、電話番号、または協力者に関する情報を持つ人は、以下のチャネルを通じて懸賞金を受け取ることができます。
- FBI: www.fbi.gov/wanted/topten の「最重要指名手配犯」ページにアクセスして、情報を提供してください。
- Fiscalía General de la República (FGR): Fiscalía General de la República (FGR) の暗号化プラットフォームを使用してください。
- インターポール: 地域のインターポール事務所に連絡して、合同タスクフォースに詳細を共有してください。
FBIは、全ての情報提供がプライベートであることを保証します。身元を明かすことなく懸賞金を受け取ることができます。



