Automated incident response can turn a protocol-wide crisis into a contained loss. In Web3 security, the difference between reacting in hours and reacting in seconds can mean the difference between a manageable incident and tens of millions in losses.
In DeFi, no project can promise perfect safety forever. That is why strong preparation matters. But when an attack begins, preparation alone is not enough. Projects also need the ability to respond immediately and cut losses before the damage spreads.
Manual intervention is often too slow. In the Nomad Bridge incident, the project team took more than three hours to respond. In the KyberSwap exploit, the team started pausing protocols nearly two hours after the first attack. That gap is exactly why Phalcon Security matters. In addition to detecting attacks, Phalcon Security can automatically trigger preset response actions, including pausing and frontrunning, in critical situations. That can reduce response time from hours to a single block.
A Recap of the KyberSwap Incident
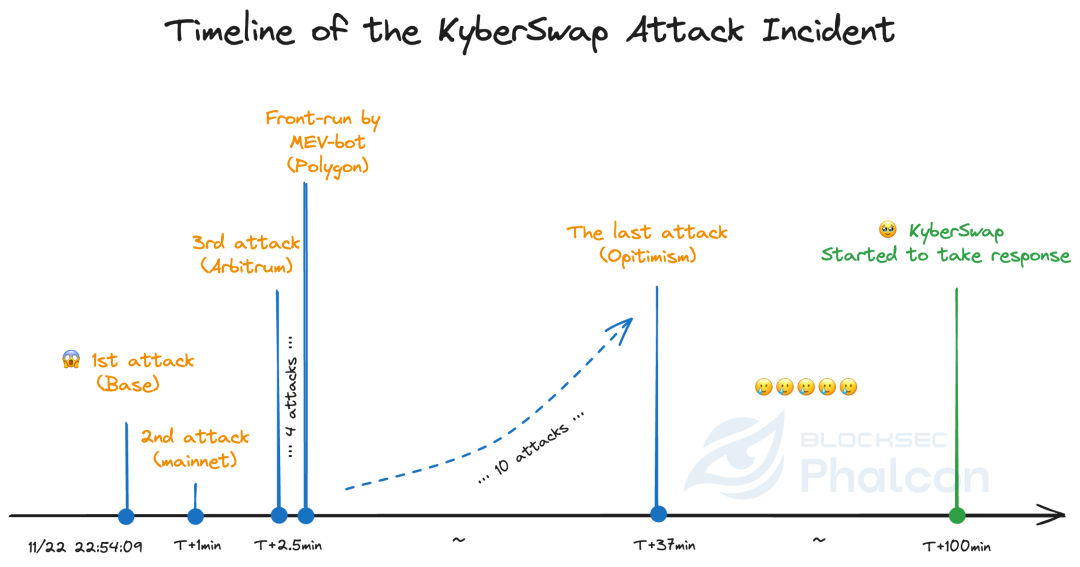
On November 22, 2023 at 22:54:09 UTC, Phalcon detected the first attack against KyberSwap on Base, with a loss of $857,025.
One minute later, Phalcon detected another attack through a private transaction on Ethereum mainnet, with a loss of $64,896.
Starting at 22:56:34 UTC, the attacker launched more attacks on Arbitrum, Optimism, Polygon, and Avalanche. Some of the attacker’s transactions on Polygon and Avalanche were frontrun by another MEV bot, which captured about $5.36 million in profit.
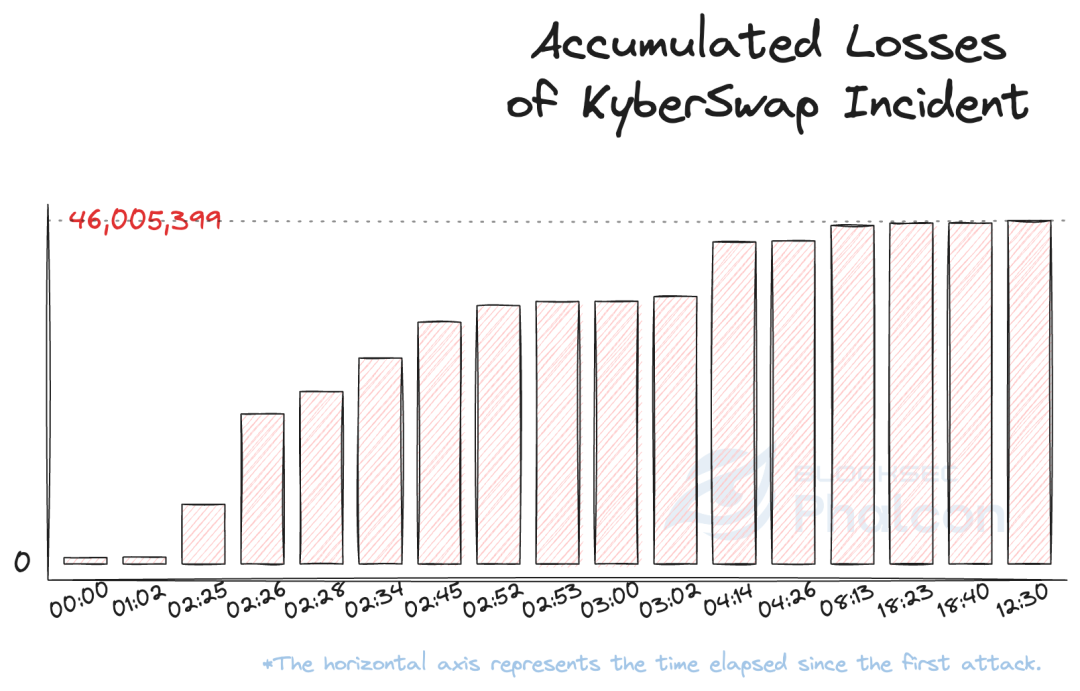
By 23:30:39 UTC, the attacker had finished. In roughly 37 minutes, the attacker launched 17 attack transactions across six chains and caused about $46 million in losses, excluding secondary attacks from imitators.
At 00:36:47 UTC on November 23, 2023, about 100 minutes after the first attack, the protocol team began pausing the protocols on different chains.
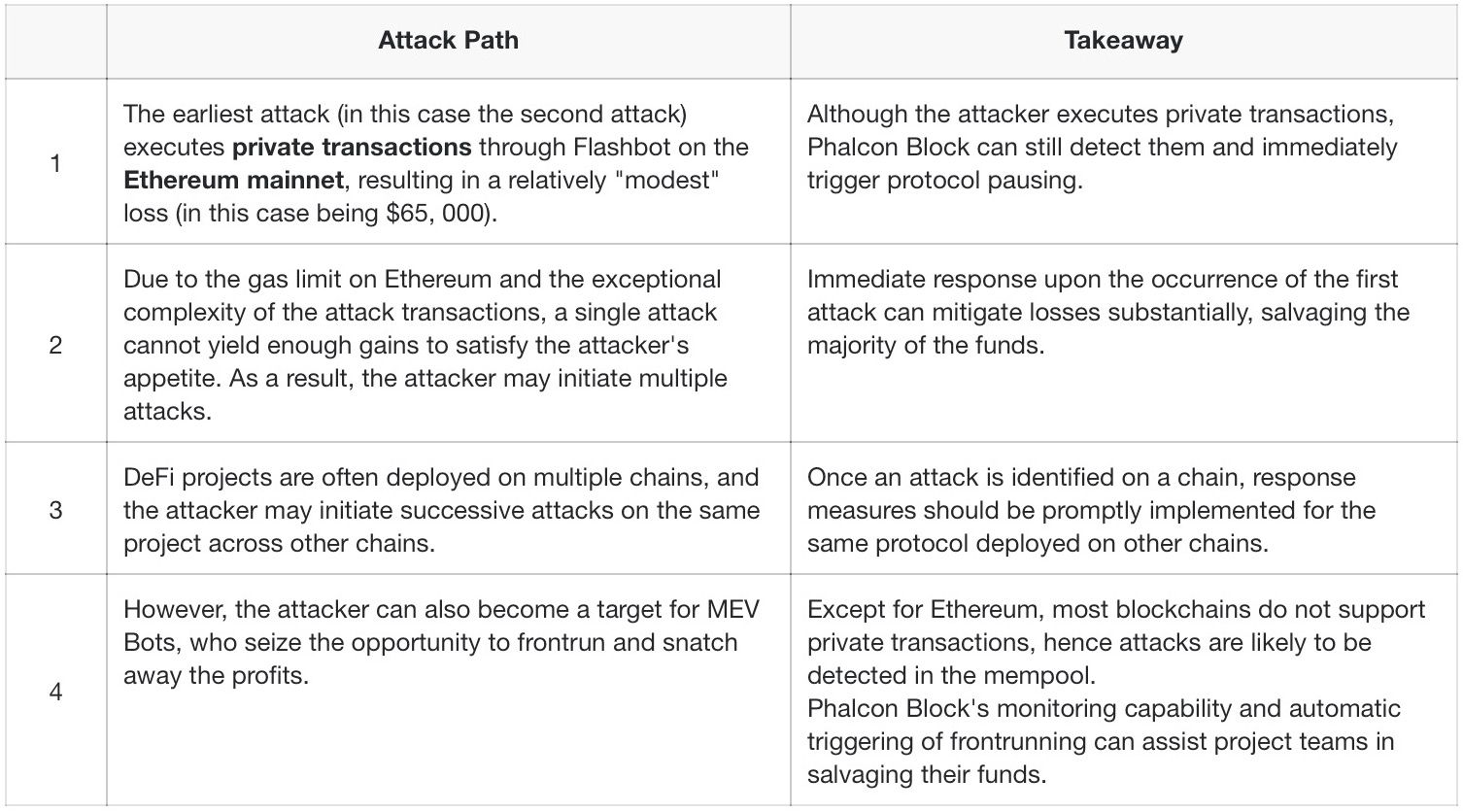
A Typical Attack Path: Private Transaction & Multi-chain Attack
The KyberSwap exploit was not a single isolated action. It moved across chains and included private transactions, public transactions, and follow-up attacks. That pattern matters because it shows how modern attackers behave in practice. They rarely stop after one successful move, and they do not limit themselves to one chain or one transaction type.
Why Is Automated Incident Response Crucial for Web3 Security?
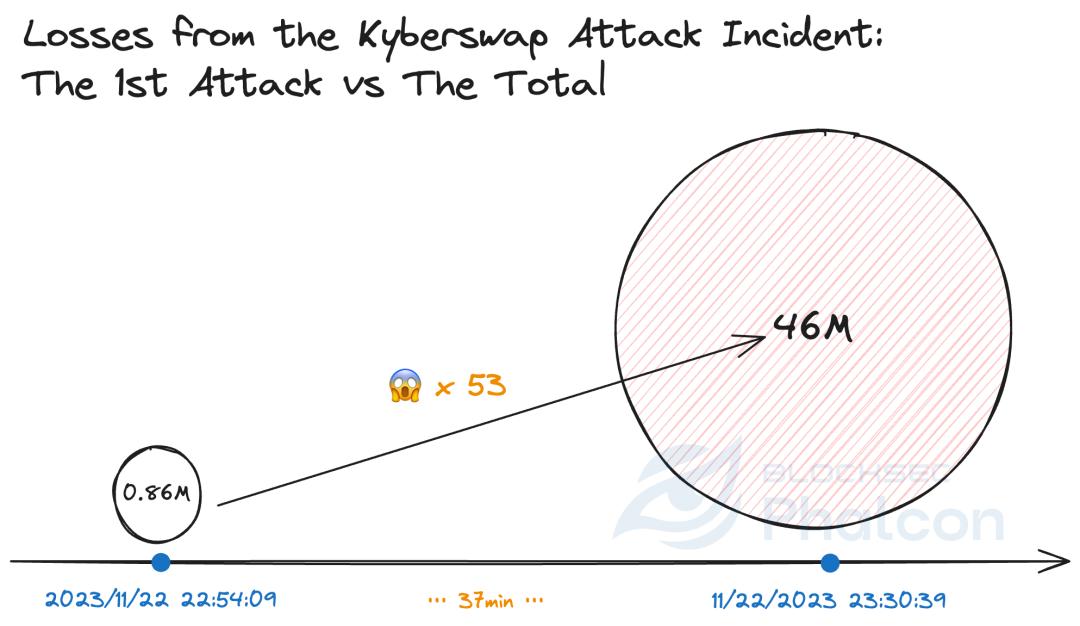
100min vs 12s; $46,000,000 vs $860,000
As soon as Phalcon detects the first attack, it can automatically trigger protocol pausing or other preset response actions. It can also pause the same protocol on other chains at the same time. In the KyberSwap case, that would have reduced the loss to about $860,000, which was the loss from the first attack, instead of roughly $46 million.
Phalcon supports both single-signature and multi-signature setups, which means incident response actions can still execute immediately even in more complex governance environments.
A single private transaction is rarely the end
More than 90% of attackers do not stop after a single private transaction, and attacks rarely happen only on mainnet. In the KyberSwap incident, only three out of 17 attack transactions were private transactions. The first private transaction accounted for just 0.14% of the total loss. All three private transactions together accounted for 16%. The first non-private attack alone caused 2% of the total loss.
The lesson is clear. Even when attackers use private transactions, projects can still reduce losses sharply if the attack is detected early and response actions are triggered in time.
When an attack happens, time becomes the main variable
Because BlockSec had no pre-existing cooperation with KyberSwap, the team could only reach out through public channels after detecting the attack. Even if the threat intelligence reached the protocol team immediately, a manual response would still have been too slow.
For a project with multi-sig governance, the team would still need to verify that an attack was happening, assess the risk, agree on countermeasures, and collect signatures for response transactions. All of that takes time, and every minute matters while the exploit is still in progress.
In the KyberSwap case, more than 100 minutes passed between the first attack and the beginning of the response. That delay is exactly why automated response is so important for blockchain incident response.
By using Phalcon Security, project teams can integrate automated response without abandoning multi-signature governance. The system allows predefined actions to execute immediately when an incident matches preset conditions.
How Can Project Teams Respond to Security Threats?
Project teams generally have two paths.
The first is to build everything themselves. That means setting up a monitoring system instead of relying on alerts from social media, defining risk assessment standards and incident response plans, creating a dedicated response team, and maintaining 24/7 operational coverage. In theory, this works. In practice, it is resource-heavy and difficult to sustain.
The second is to use a platform built for real-time threat detection and response. With Phalcon Security, project teams gain precise external threat monitoring, flexible rule configuration, intelligent risk grading, and automated fast response mechanisms such as protocol pausing and frontrunning. That makes it possible to improve protocol security without building a round-the-clock response organization from scratch.
You can keep your protocol safer without relying on continuous manual intervention.
Related Resources
- KyberSwap Incident: Masterful Exploitation of Rounding Errors with Exceedingly Subtle Calculations
- Yet Another Tragedy of Precision Loss: An In-Depth Analysis of the KyberSwap Incident
- BlockSec Launches Phalcon: The World's First Crypto Hack Blocking System for Web3 Security





