MetaSleuth is a crypto tracking and investigation platform. It can help monitor market movements, track fund flow of criminal activities, and DYOR to avoid scams. It supports more than 20 blockchains and has been widely used by the community to perform investigations.
In this blog, we will show how to use MetaSleuth to track the "smart" money on the meme TIM token on Solana, which was criticized as the project insider who made millions of USD by buying TIM tokens. The address used in this blog is 9wAfrMnzrJ1XWXXDDmqh7gH7Q9ZBJjLhgou5GrUcHsZy. We use the address 9wAfr in this blog to denote 9wAfrMnzrJ1XWXXDDmqh7gH7Q9ZBJjLhgou5GrUcHsZy in the following.
Start the Search
First, input the address 9wAfrMnzrJ1XWXXDDmqh7gH7Q9ZBJjLhgou5GrUcHsZy inside the MetaSleuth. The tool will perform an intelligent analysis to show the initialized result (as shown in the following Figure).
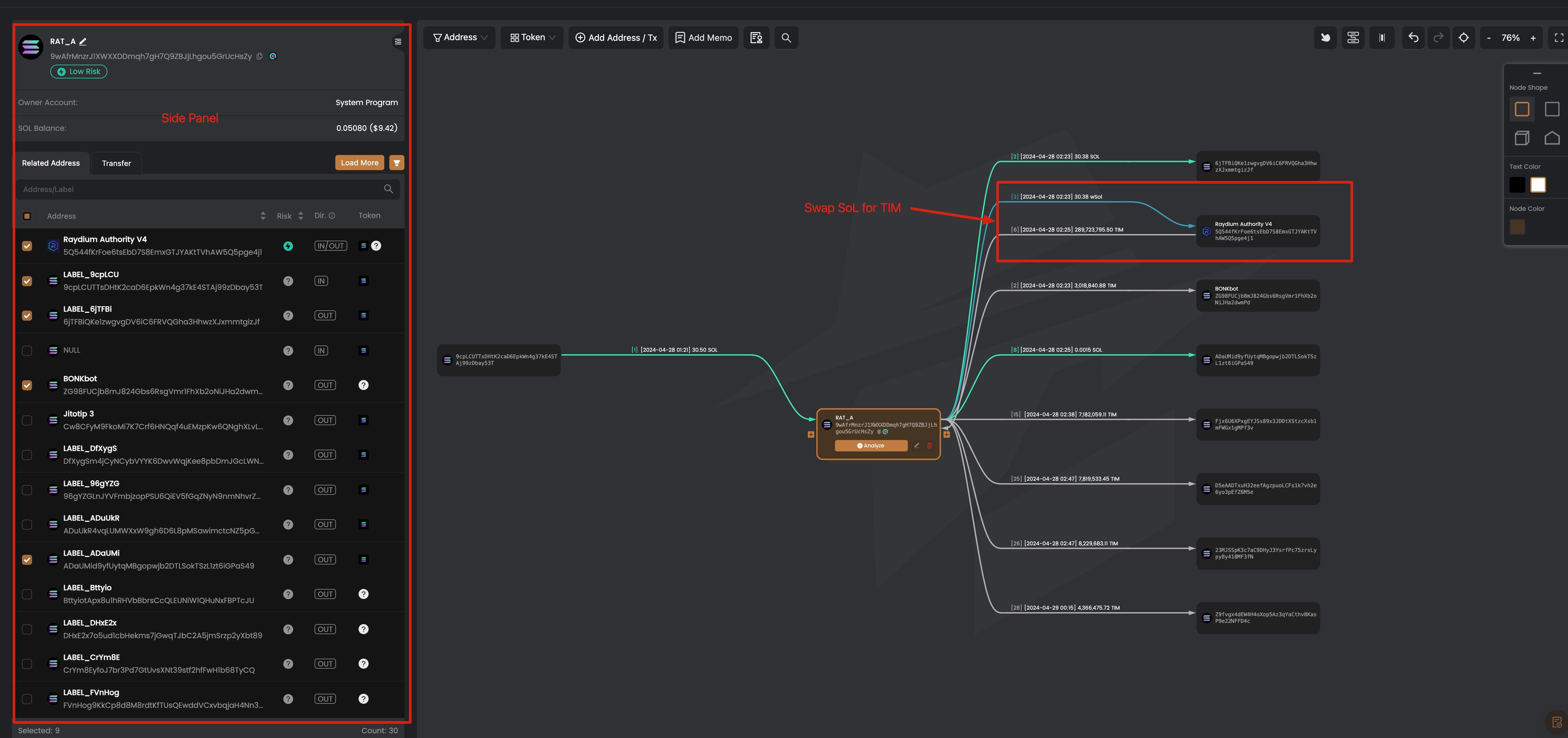
On the left is the side panel of an address, which will be shown when you click an address on the main canvas. The node on the main canvas means an address, and the edge between nodes represents the aggregated token transfers for each token. That means if there are multiple transactions to transfer one token between two nodes, there will be only one edge between them. You can click the edge to show the detailed transactions for the token transfer.
From the result, we can find the token swap in Raydium, with 30.38 wSoL flowing into the Raydium and 288,723,795.50 TIM out. As we just said, the edge is the aggregated token transfers. We can click the edge to see more detailed information.

The transaction list shows the transactions between the address 9wAfrMnzrJ1XWXXDDmqh7gH7Q9ZBJjLhgou5GrUcHsZy and Raydium.
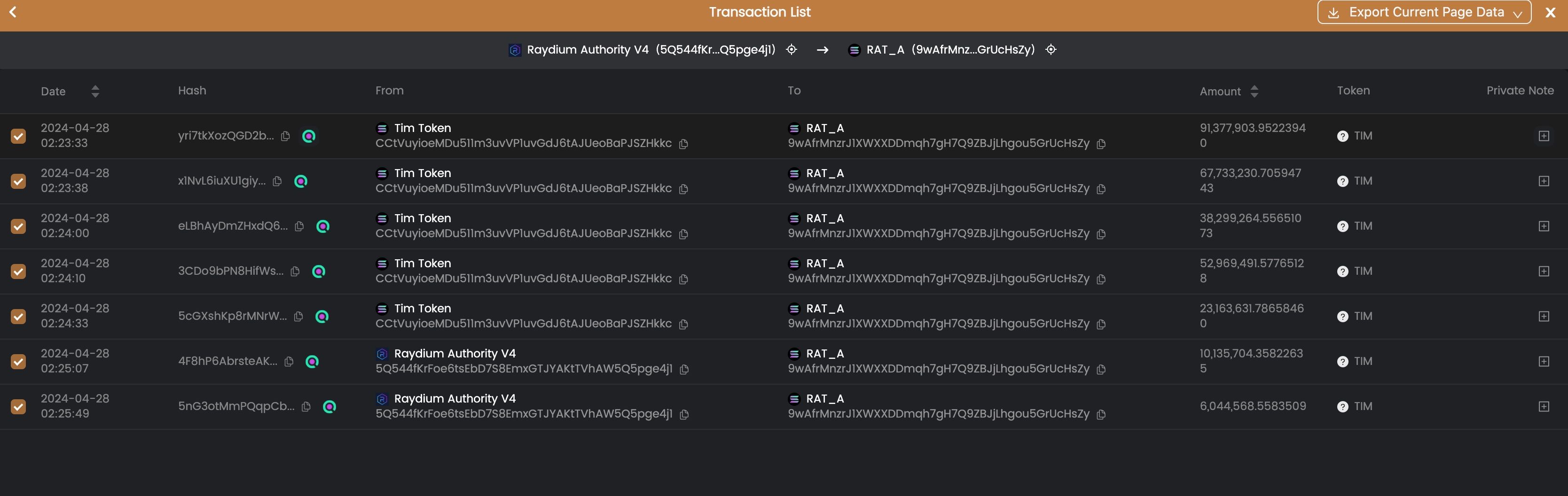
From the transaction list, we can see that the 9wAfr used 30.38 SoL to swap 288,723,795.50 TIM tokens from 04-28 02:33:33 to 04-28 02:25:49 in two minutes.
Track the Fund Flow
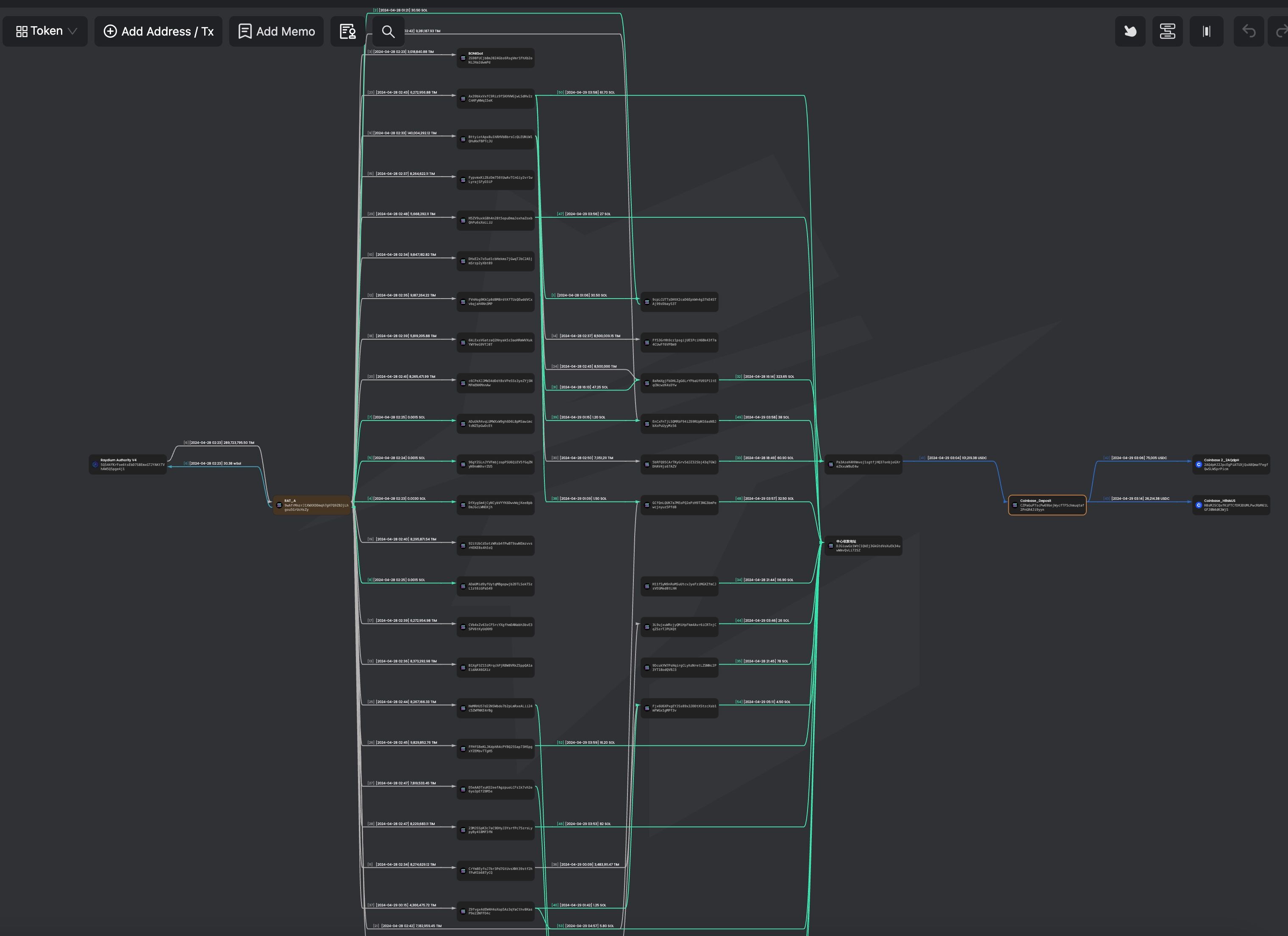
After receiving the TIM tokens, the address 9wAfr wants to sell TIM tokens for profit. Instead of directly selling the tokens using the 9wAfr address, it uses three layers of addresses to hide the trace. How is this achieved?
To track the fund flow, we first find the TIM tokens transferred out from the address 9wAfr. We can click the address 9wAfr to show the side panel, and select all the output TIM tokens.
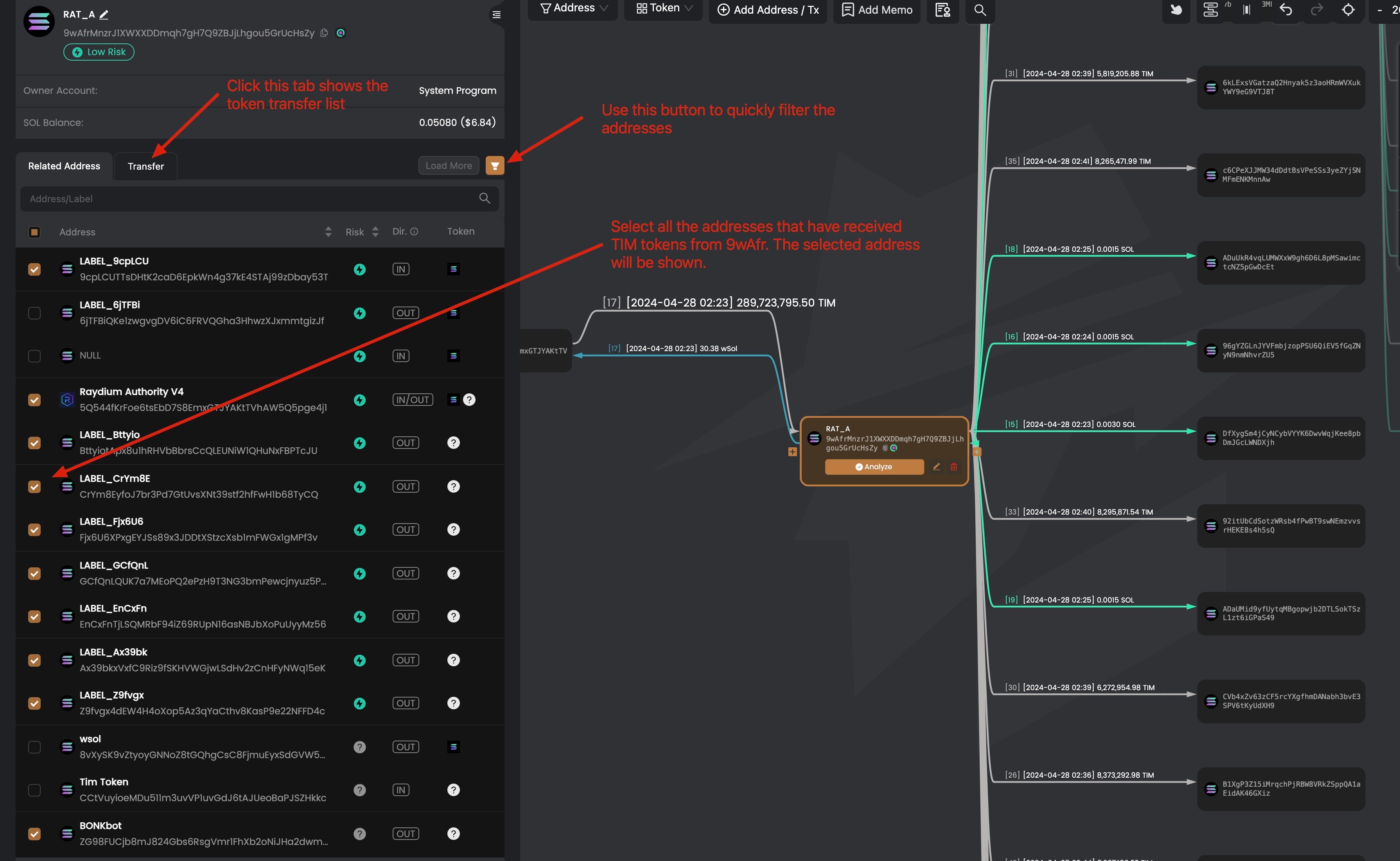
After selecting the addresses that receive the TIM tokens, we can click the node of the address to track further the token flows. For instance, we can click on the address Ax39bkxVxfC9Riz9fSKHVWGjwLSdHv2zCnHFyNWq15eK, and we find that this address swaps the received TIM tokens to SoL and transferred SoL to DJGiuwGs1WtC1QkEj3GkGtdVoXuEk34uwWmvQvLi72SZ.
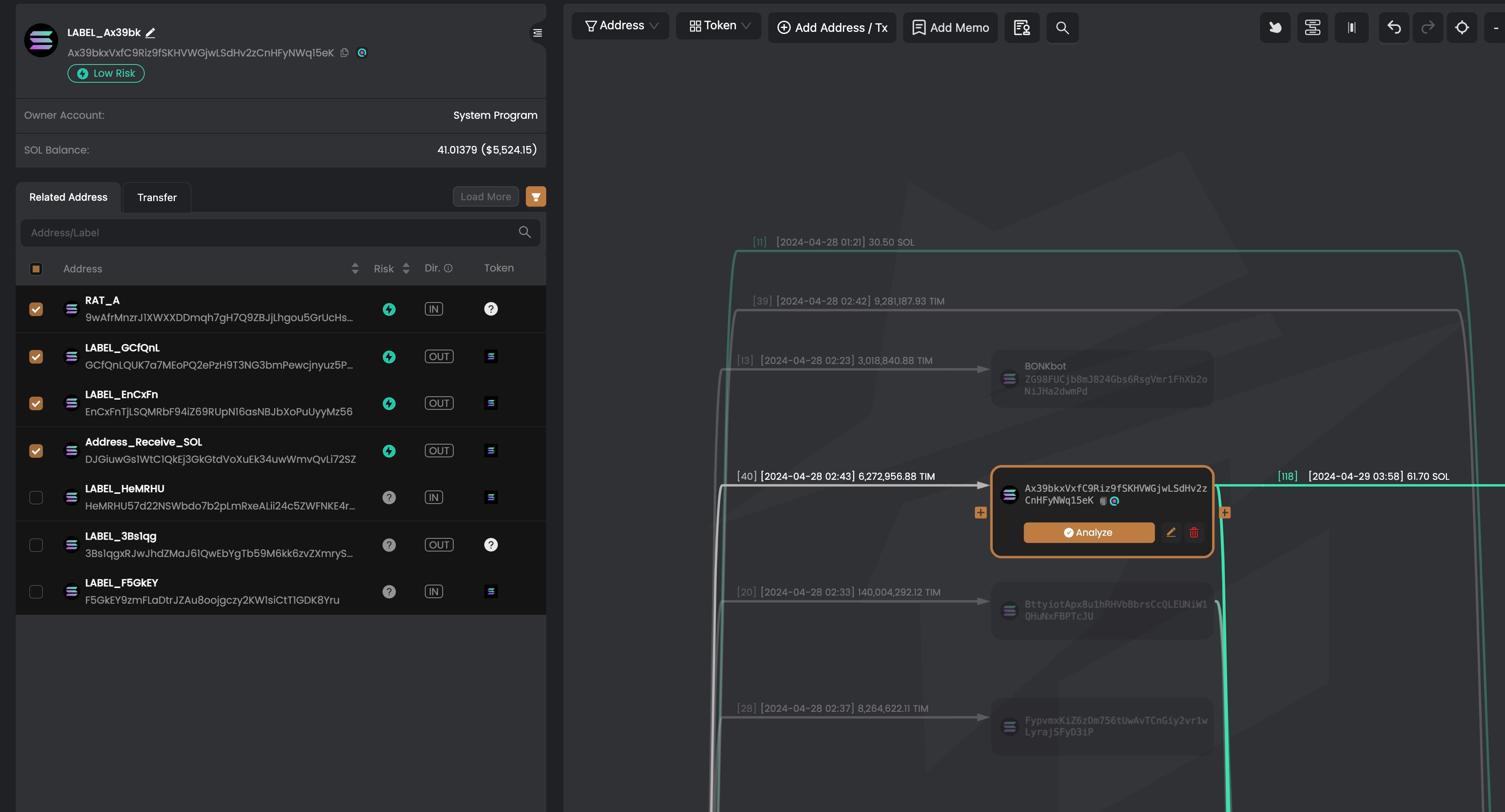
We can use similar methods to track other addresses that receive TIM tokens from 9wAfr. And we found there are three different status of the addresses.
- Status 1: the received tokens are still in the addresses
- Status 2: the received tokens have been swapped to SoL, and transferred to
DJGiuwGs1WtC1QkEj3GkGtdVoXuEk34uwWmvQvLi72SZ - Status 3: the recevied tokens have been swapped to SoL, and transferred to
Pa3AzeK4HHmvoj1sgtfjHQ37onbjoGXreZkxuW8uE4w
Note that, some of them transferred TIM tokens to another layer.
Deposit into Coinbase
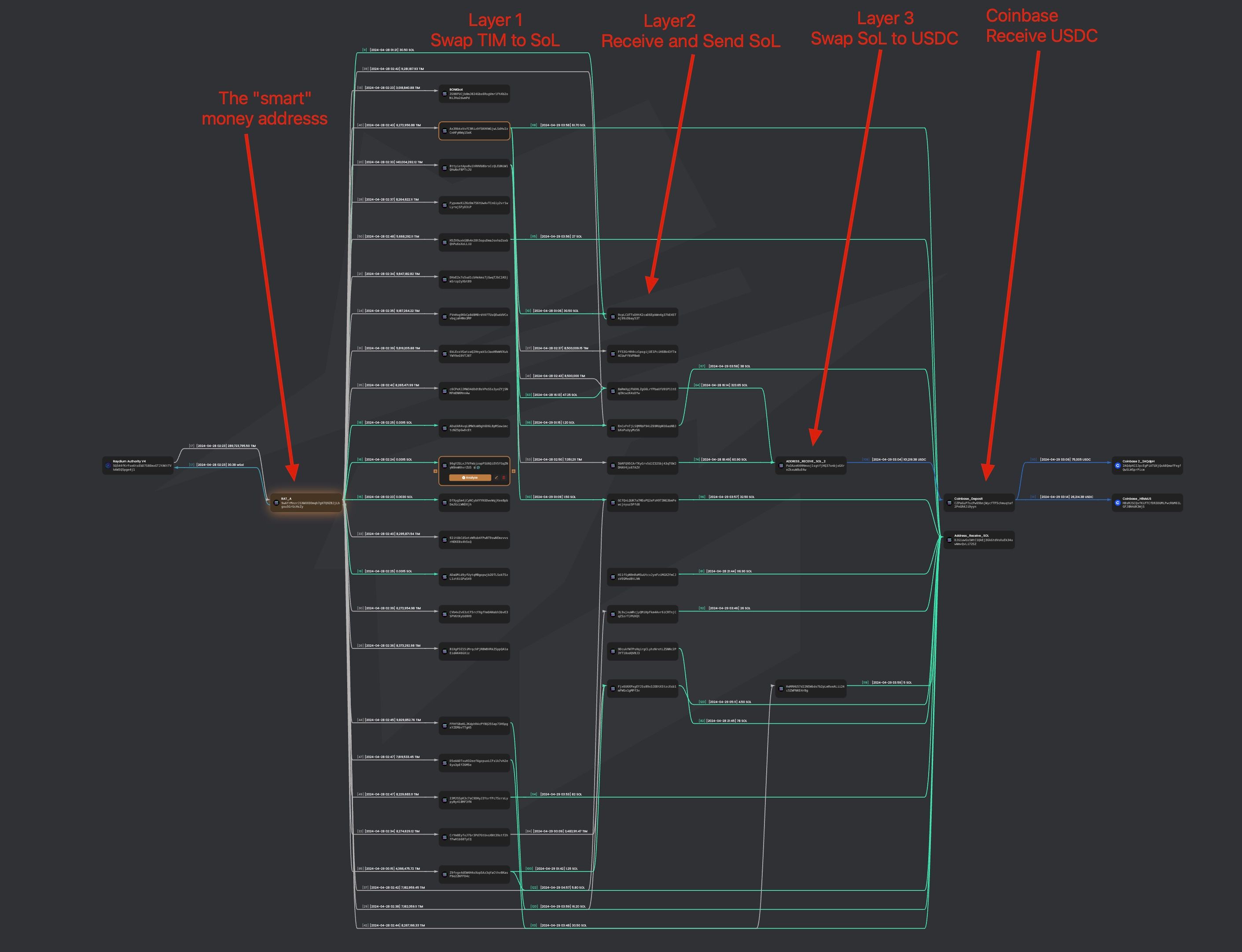
We further found that the SoL will be swapped into USDC and transferred to the Coinbase deposit address CZPaGuP7scPw69bnjWycfTF5chmuqtaf2PnGR4Ji9yyn.
Profits
Let's calcuate the estimated profits of address the address 9wAfr.

We can find that the rate of return is more than 400x (using the current price of 0.00004995 SoL per TIM). The profit is (476 -1) x 30.38 SoL x 130 USD/SoL = 1.8 Million USD.
The graph shows the time to buy and the time to start selling the TIM tokens.

"Smart" Money?
The community suspected that the address analyzed in this blog and another one (DmHDP8BNRUMNkwqD145zudhJGKuEZgAMyZi7BsvEnMNv), which made millions of USD, were inside persons. The reasons are the following.
- The two addresses are new addresses without transaction history
- They received SoL shortly before the token launch and immediately bought a large number of TIM tokens
- They used multiple layers of addresses to hide the fund flow
We do not know the real identities of these addresses. However, all the transactions are public. Anyone can leverage MetaSleuth to do their own research on any project and address.
Please read MetaSleuth documents and website for more information.
I have saved the analysis result; you can click it to see the details.
Subscribe and Enjoy 10% Off Discount
When signing up for MetaSleuth, use BLOCKSEC as the invitation code to enjoy 10% off for the subscription.
https://metasleuth.io/?invite-code=BLOCKSEC





