About the Ronin Bridge Hack
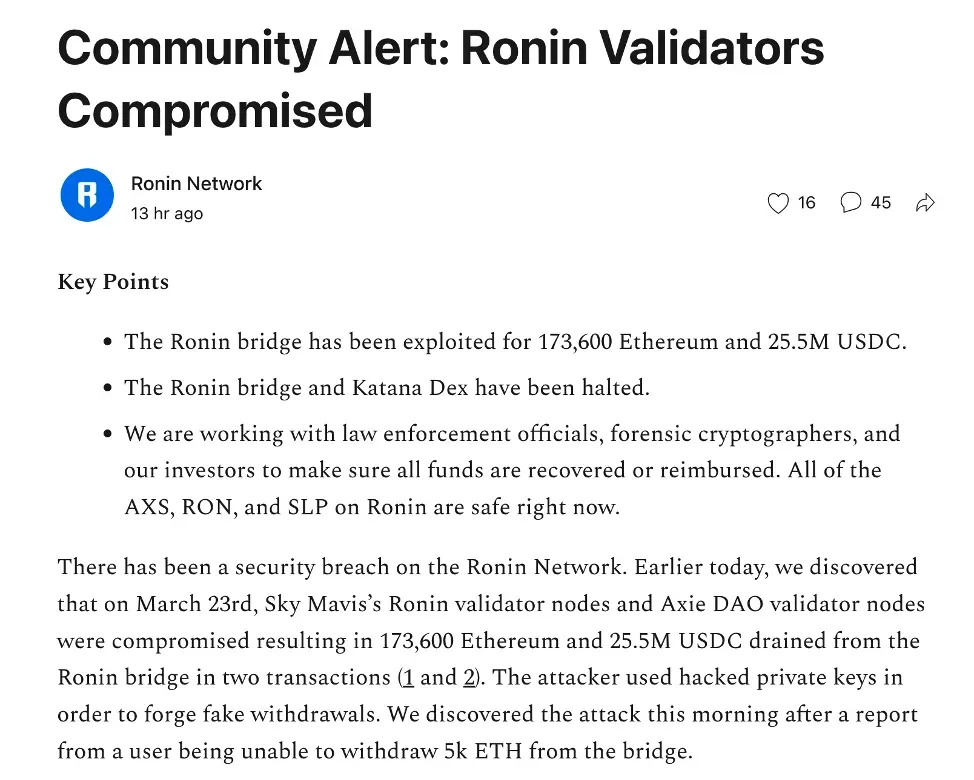
On March 29th, 2022, Ronin Network released an official announcement to alert the community for the Ronin Bridge security incident. Specifically, the attacker first got the private keys by compromising the Ronin validators, and then withdrew 173,600 ETH and 25,500,000 USDC from the Ronin Bridge through two attack transactions.
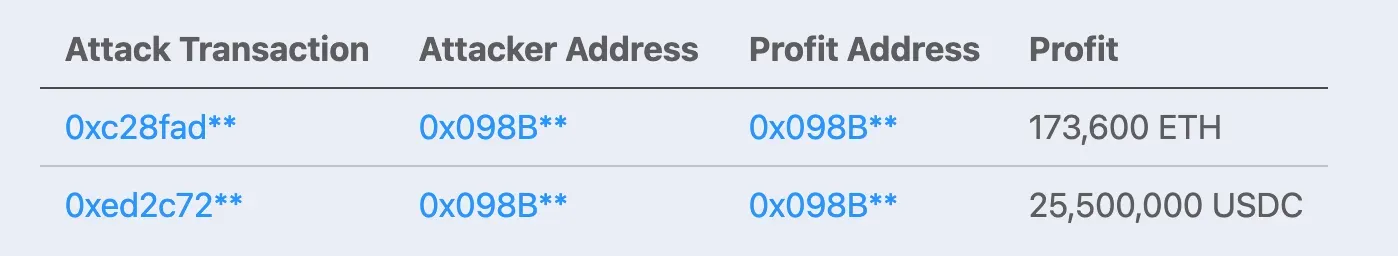
The details of the two transactions are as follows:
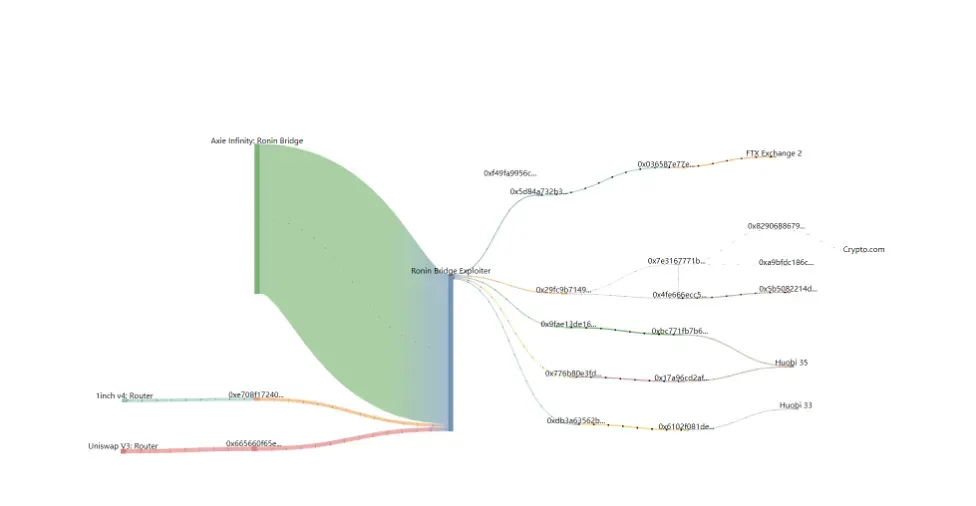
Tracing the Stolen Fund
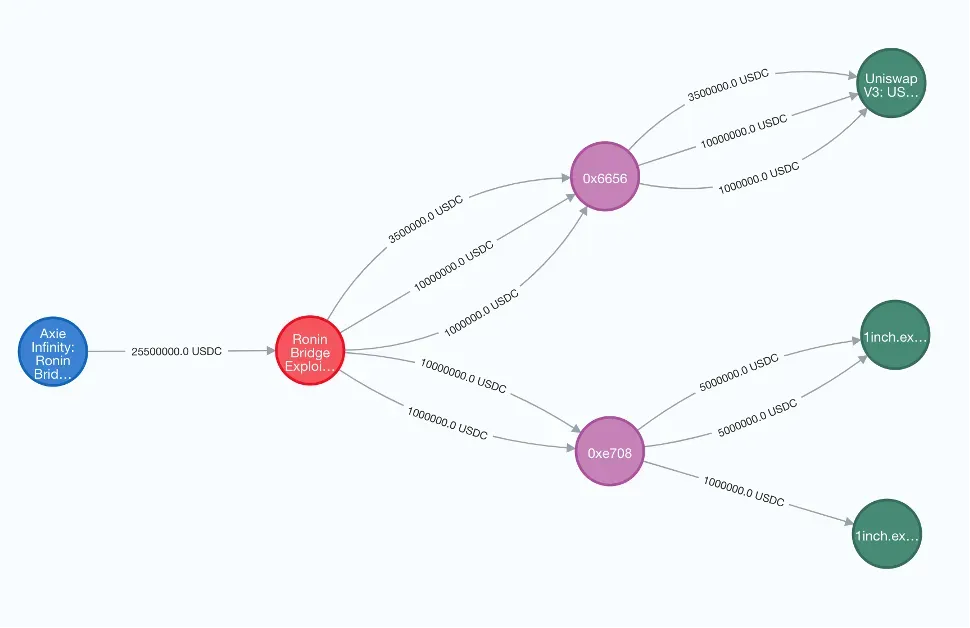
The attacker immediately swap the stolen USDC for ETH after harvesting the profit. Specifically, the stolen USDC were transferred to Uniswap and 1inch, and two intermediate nodes, i.e., 0x6656 and 0xe708, were used to perform the swap back and forth. After the swap, all the stolen fund became ETH.
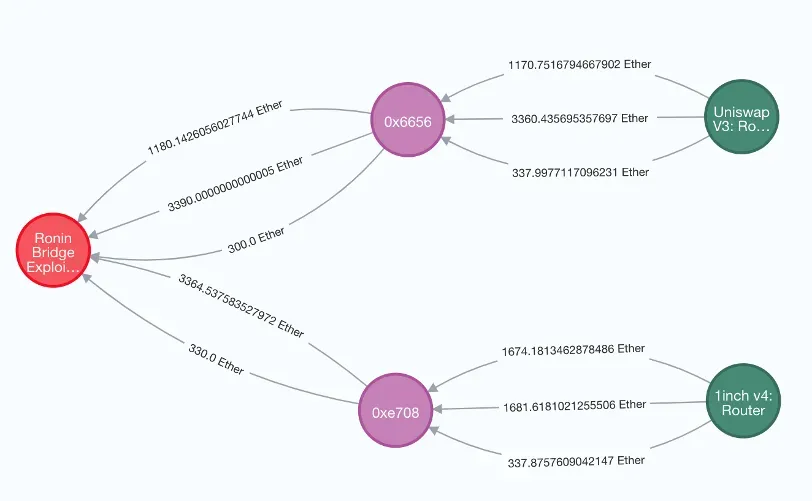

On March 28th, the attacker began to transfer the ETH. Up to March 30th, the attacker has transferred out 6,250 ETH from the attack address to exchanges, including 1,220 ETH to FTX, 3750 ETH to Huobi and 1 ETH to Crypto.com, respectively.
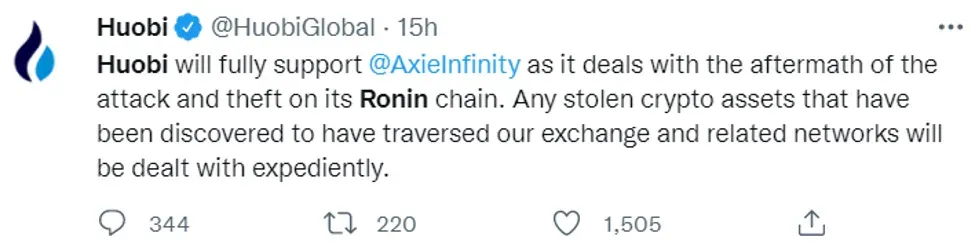
The good news is that these exchanges are willing to help the project to get back the stolen fund.

Conclusion
As of this writing, around 175,913 ETH are still held by the attack address, while 1,279 ETH are on the way to be transferred out. We will continuously monitor the trace of the stolen fund, and share our findings with the community in time.
Some Other Data
The attacker has harvested 182,162.86 ETH. Among them, 173,600 ETH were directly stolen from the project, while 8,562.86 ETH come from the stolen USDC.
- Initial fund: 1.0569 ETH from Binance
- Stolen ETH: 173,600 ETH
- Swapped ETH from the stolen USDC: 8,562.86 ETH (4869.18508653411 to Uniswap and 3693.6752093176137 to 1inch)
- Transferred out: 6,250 ETH
Reference
https://roninblockchain.substack.com/p/community-alert-ronin-validators?s=w
About BlockSec
BlockSec is a pioneering blockchain security company established in 2021 by a group of globally distinguished security experts. The company is committed to enhancing security and usability for the emerging Web3 world in order to facilitate its mass adoption. To this end, BlockSec provides smart contract and EVM chain security auditing services, the Phalcon platform for security development and blocking threats proactively, the MetaSleuth platform for fund tracking and investigation, and MetaSuites extension for web3 builders surfing efficiently in the crypto world.
To date, the company has served over 300 esteemed clients such as MetaMask, Uniswap Foundation, Compound, Forta, and PancakeSwap, and received tens of millions of US dollars in two rounds of financing from preeminent investors, including Matrix Partners, Vitalbridge Capital, and Fenbushi Capital.
Official website: https://blocksec.com/
Official Twitter account: https://twitter.com/BlockSecTeam




