Key Insight: A platform posing as a Hong Kong health-tech group routed approximately $1.6 billion in cumulative USDT volume through TRON over 16 months, an upper-bound figure that includes potential internal fund recycling. On-chain analysis reveals an industrialized fund-routing infrastructure: 8 generations of collection hot wallets, 79 intermediate pass-through addresses, 3 generations of paired payout channels with second-level handoffs, and a shared exchange exit point fed by tens of thousands of suspected deposit addresses. This article reconstructs the full topology, from victim deposit to exchange exit.
Estimated reading time: 8 minutes
Background
VerilyHK presented itself as a legitimate Hong Kong health-tech investment platform. The name itself appears designed to exploit confusion with two unrelated companies: Verily Life Sciences, the Alphabet-owned precision health company known for AI-driven healthcare and medical devices, and a Chinese A-share listed environmental engineering firm (stock code 300190) that has no connection to health tech or cryptocurrency. VerilyHK's website copy, claiming expertise in AI health, big data analytics, and medical devices, closely echoes the real Verily's public positioning. Its marketing evolved over time, from immune-cell therapy and portable ECG devices to AI health, health credit systems, data asset tokenization, and even claiming to have obtained SFC Type 4 and Type 9 licenses for securities advisory and asset management in Hong Kong.
In April 2025, the Heshan District government published a risk advisory explicitly describing the project as exhibiting "obvious pyramid scheme and illegal financial characteristics," and noted its reliance on "overseas cryptocurrency transactions." By late April 2025, multiple anti-fraud monitoring sites had issued collapse warnings. The platform ceased operations in February 2026.
At approximately $1.6 billion in on-chain volume, VerilyHK significantly exceeds other major crypto Ponzi schemes that have faced regulatory action, including Forsage ($300M, SEC-charged) and NovaTech ($650M, SEC lawsuit). Yet until now, no public on-chain analysis of this crypto crime operation existed.
This article does not rely on those public advisories for its conclusions. Everything that follows is based on on-chain data analysis of the TRON USDT stablecoin flows connected to the platform, reconstructing what that infrastructure looks like from the inside, layer by layer.
Starting Point
The investigation began with two TRON addresses provided by a victim: a deposit address and a payout address. Tracing the connection between them revealed not just a single path, but an entire multi-layered, multi-generational fund-routing network.
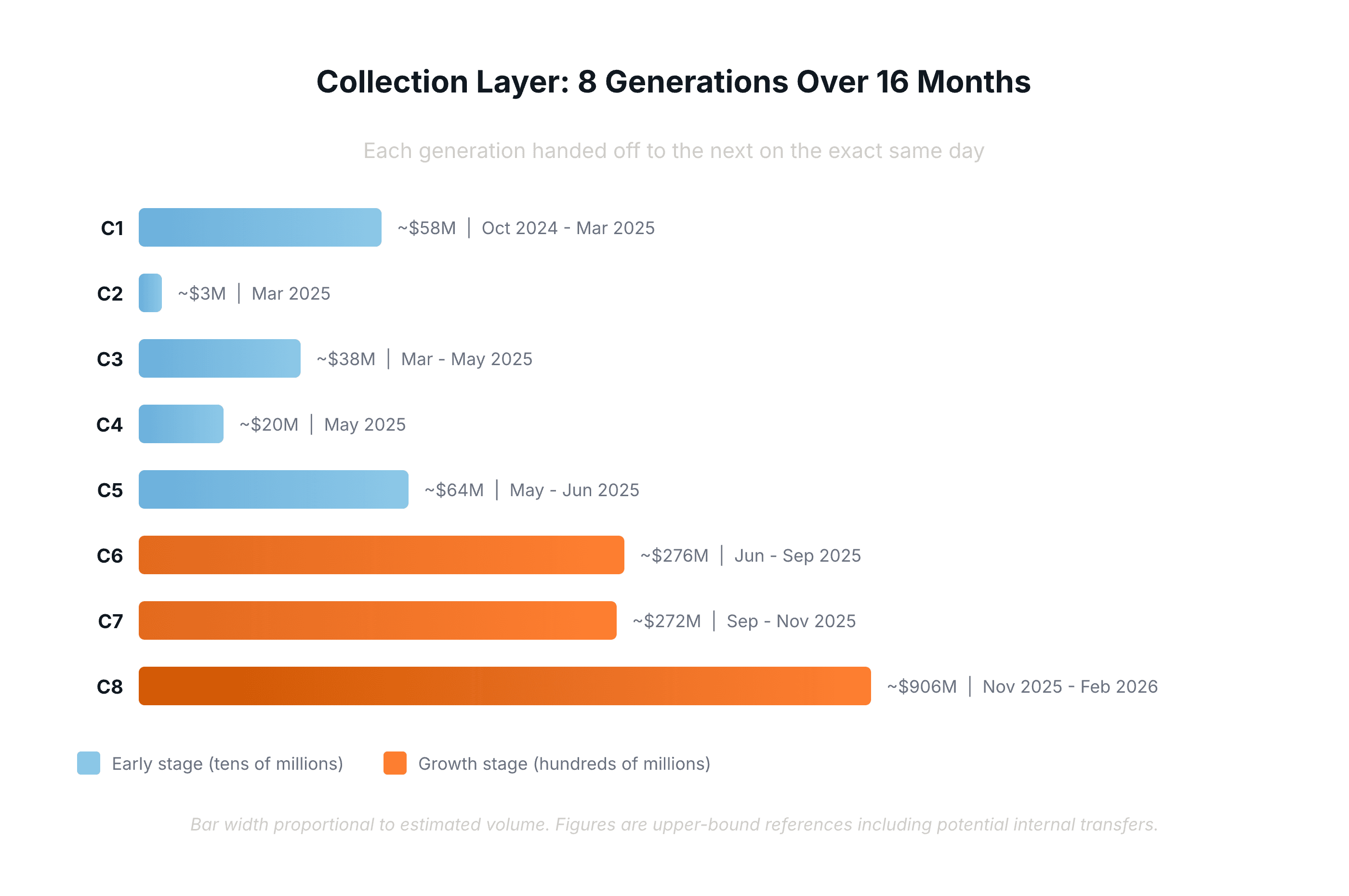
Collection Layer: 8 Generations of Hot Wallets Over 16 Months
VerilyHK did not rely on a fixed set of collection addresses. It used at least 15, organized into 8 distinct generations that rotated in strict chronological sequence over a 16-month period from October 2024 to February 2026.
These addresses were not running in parallel. They operated as a relay chain: each generation's end date coincided precisely with the successor's start date, a pattern of day-precise handoffs that repeated across all eight transitions. Beyond the handoff timing, successive generations shared the majority of their deposit address networks, with overlap rates above 65%, confirming they were operated by the same entity rotating through new wallets.
The volume processed by each generation grew dramatically over time. Early generations handled tens of millions of dollars per month, but by the sixth generation, volumes had entered the hundreds of millions. The final generation processed over $900 million in under four months. The cumulative volume across all generations was approximately $1.6 billion.
These figures, however, should be treated as an upper-bound reference rather than net user deposits. They are derived from full graph aggregation and include potential internal transfers. In a Ponzi structure, "returns" paid to users may be reinvested, causing the same funds to be counted multiple times at the collection layer. The late-stage volume explosion likely reflects both genuine growth and increasing internal fund recycling.
Intermediate Layer: 79 Pass-Through Addresses Converging on Known Hubs
Funds leaving the collection hot wallets did not flow directly to the payout layer. They passed through 79 intermediate pass-through addresses, each with very few inbound sources, multiple outbound targets, and near-zero net retention. Over 80% of the funds flowing through this layer converged to a small number of identified payout channel hubs.
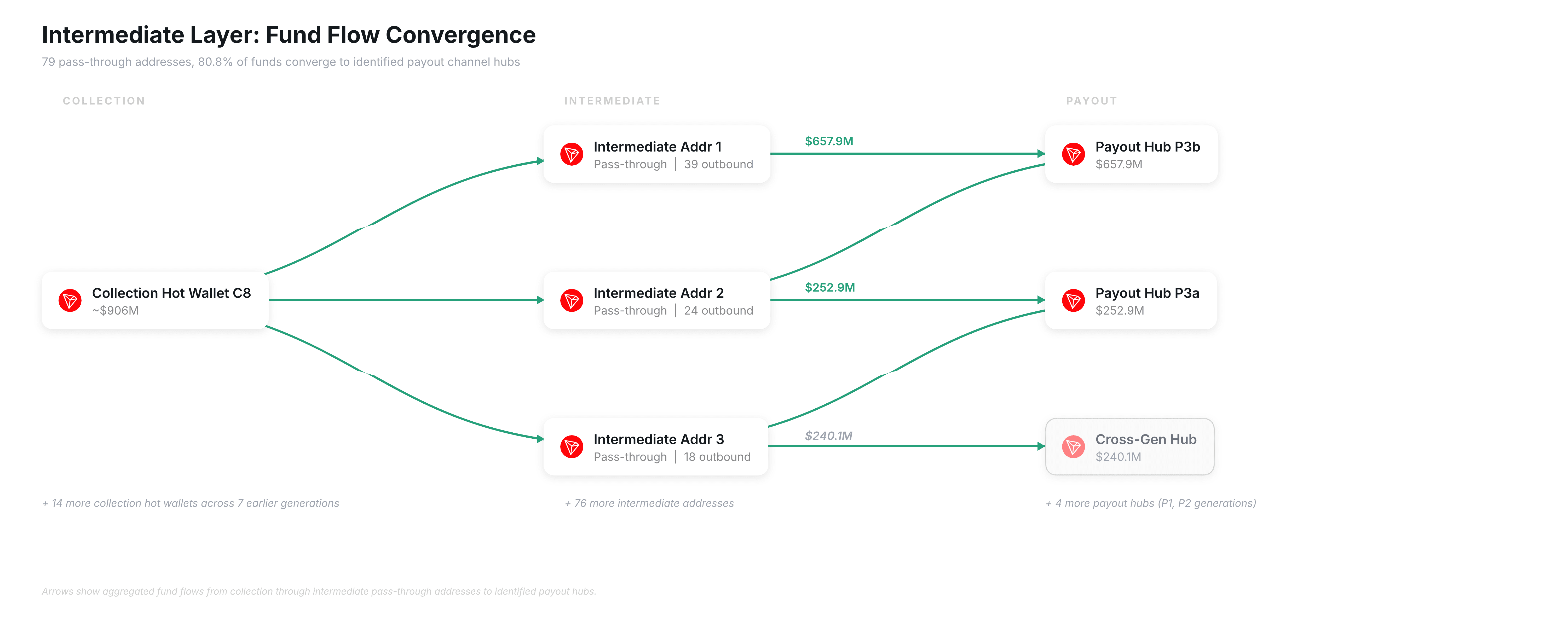
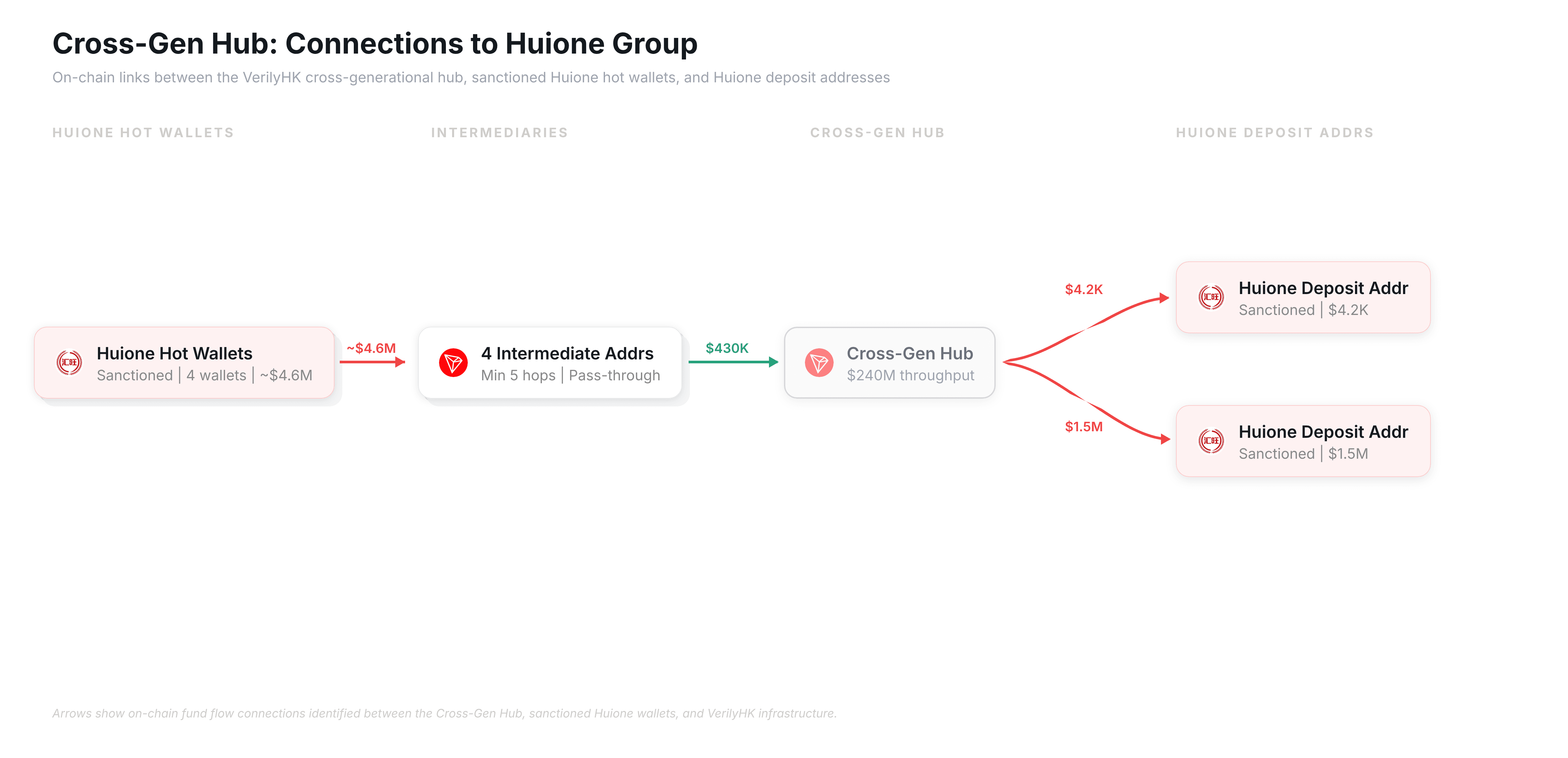
While most of these funds flowed toward the payout layer, one node stood out. A single cross-generational hub received funds from 75% of all intermediate addresses, totaling approximately $240 million across six of the eight collection generations, yet its downstream structure differs significantly from the identified payout channels.
On-chain tracing reveals direct fund flow connections between this hub and multiple wallet addresses associated with Huione Group, a Cambodia-based financial group barred from the U.S. financial system by FinCEN. On the inflow side, at least four Huione Group hot wallets sent funds totaling approximately $4.6 million through a chain of intermediate addresses (minimum 5 hops) before reaching the hub. On the outflow side, the hub sent funds directly to at least two Huione Group deposit addresses, in amounts of $4.2K and $1.5M respectively.
The fund flows between the cross-gen hub and Huione suggest that VerilyHK's fund-routing infrastructure may have utilized Huione's network as a laundering channel, a pattern consistent with FinCEN's finding that Huione served as a "critical node" for laundering proceeds of virtual currency investment scams.
Payout Layer: From Paired Channels to a Shared Exchange Exit
The payout side mirrored the collection side's generational structure. Three generations of payout addresses were identified, with total payout volume of approximately $1.1 billion. As with the collection layer, inter-generational handoffs were precise to the second: on-chain timestamps show that the second-generation channels ceased and third-generation channels activated at the same moment, a pattern difficult to explain as anything other than a pre-planned cutover by the same operating team.
Within each generation, the architecture followed a consistent pattern: dedicated bridge addresses first aggregated intermediate-layer funds, then forwarded them to a pair of parallel payout channels, a primary and a secondary line. Each pair ran in nearly identical time windows, starting within minutes of each other and ceasing within seconds, yet one line consistently processed significantly more volume than the other. This bridge-then-paired-payout structure recurred across all three generations, confirming this was designed infrastructure, not ad hoc wallet creation.
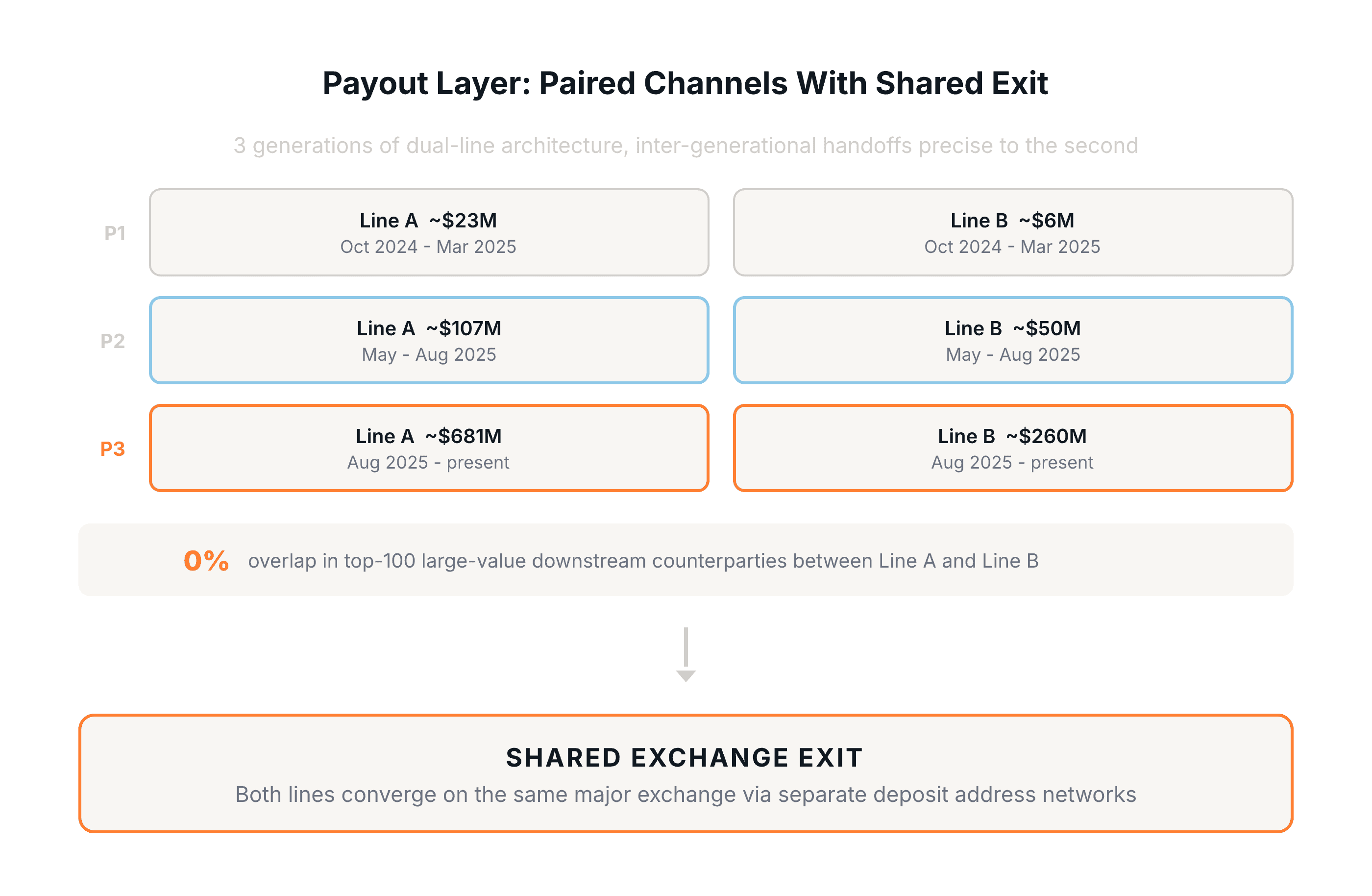
A closer analysis of the third-generation pair reveals the extent of this separation. One channel handled roughly 2.6 times the volume of the other. Comparing their top 100 large-value downstream counterparties, the overlap was zero. Though fed by the same upstream sources and running simultaneously, they operated entirely separate downstream distribution networks.
What the two lines did share was their final exit point. Among their small-value downstream transfers, both lines exhibited the same pattern: funds flowed through tens of thousands of single-use addresses, each with virtually one inbound and one outbound transaction, before converging on the same hot wallet belonging to a major centralized exchange (CEX). Yet even here, the two sets of deposit address intermediaries were almost entirely separate, with only 9 shared addresses out of roughly 60,000, resembling two independent pipelines feeding into one exchange. On-chain data confirms entry into the exchange's processing pipeline, but cannot identify the specific user accounts behind these deposits.
Full Picture: A Four-Layer Funnel
Assembling all findings, VerilyHK's on-chain fund-routing architecture forms a distinct four-stage funnel: extreme dispersion at the front end, high concentration in the middle, re-dispersion at the payout layer, and final exit through exchanges.
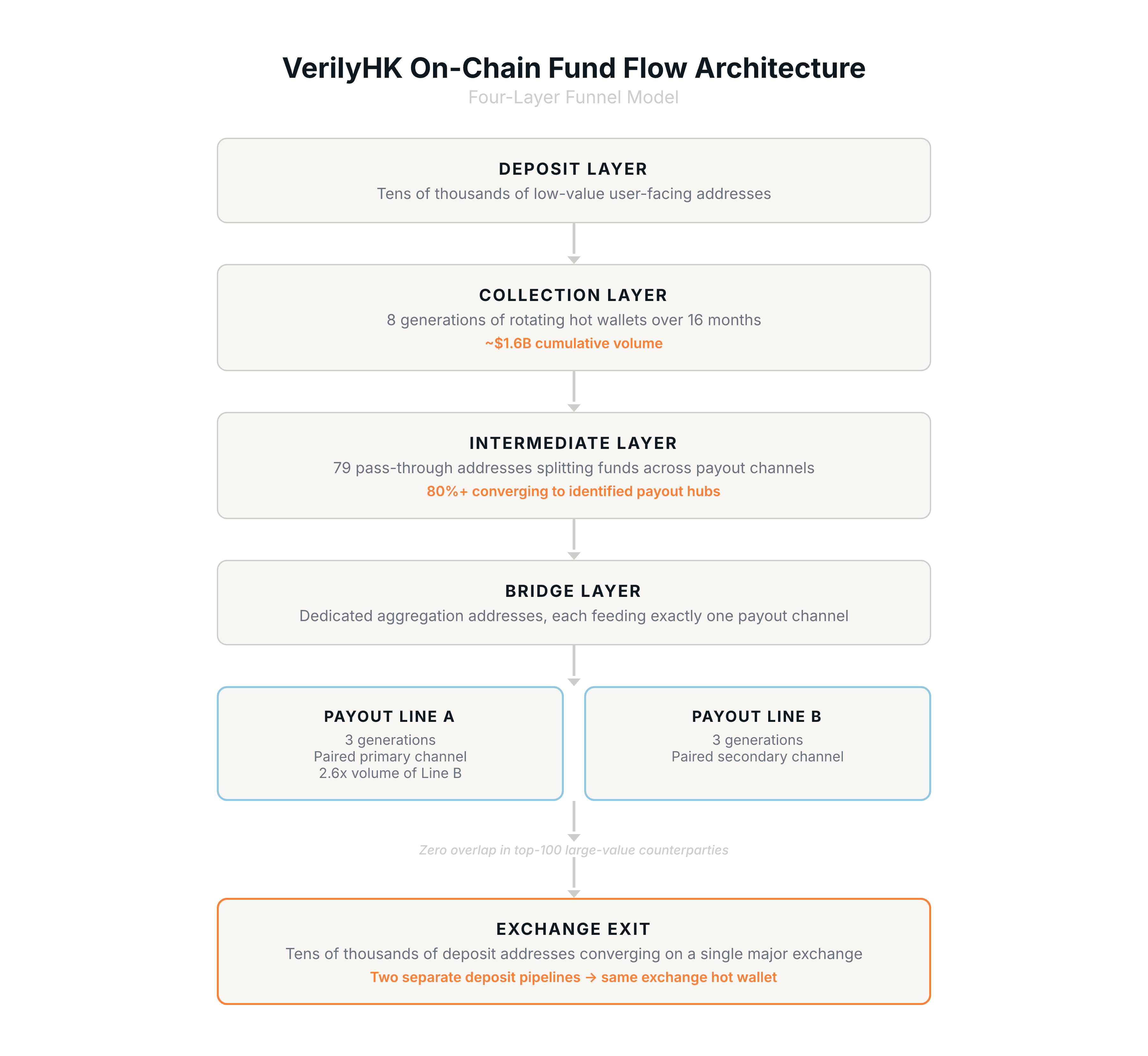
What stands out is the combination of sheer volume, approximately $1.6 billion in cumulative on-chain flow, and the precision of the infrastructure behind it: day-exact generational handoffs, paired payout channels with largely separate downstream networks, and tens of thousands of single-use addresses funneling into a shared exchange exit.
For compliance teams at exchanges, the structural signatures documented here represent actionable detection heuristics, particularly the tens of thousands of single-use deposit addresses converging on a shared hot wallet. For investigators and regulators, the layered architecture illustrates why tracing illicit funds requires looking beyond individual transactions to reconstruct the full network topology.
All on-chain analysis in this article was conducted using the MetaSleuth on-chain analytics toolkit, part of BlockSec's AML and compliance suite. The analysis follows a top-value path methodology, and all conclusions are annotated with evidence strength and applicable boundaries.