Background of the private tx service
The private tx service aims to protect users' transactions without broadcasting the transactions on the chain. This service can help build a healthy ecosystem by protecting users from being sandwich-attacked. For instance, an attacker cannot listen to the pending pool to front-run other transactions. Besides, the private tx service can mitigate the gas fee war between MEV bots. That's because MEV bots can leverage such a service instead of competing in the pending tool that will raise the gas price -- making the normal transactions hard to be packed.
Flashbots is a well-known private service provider on Ethereum and has excellent documents on how the system works. It also provides clear APIs of the private tx data. BNB48 has provided a similar service (Enhanced RPC) on Binance Smart Chain (BSC).
Private tx has been abused by attackers
However, the private tx service can be abused by attackers to make the attack transaction be packed on the chain (without being noticed) in a fast way.
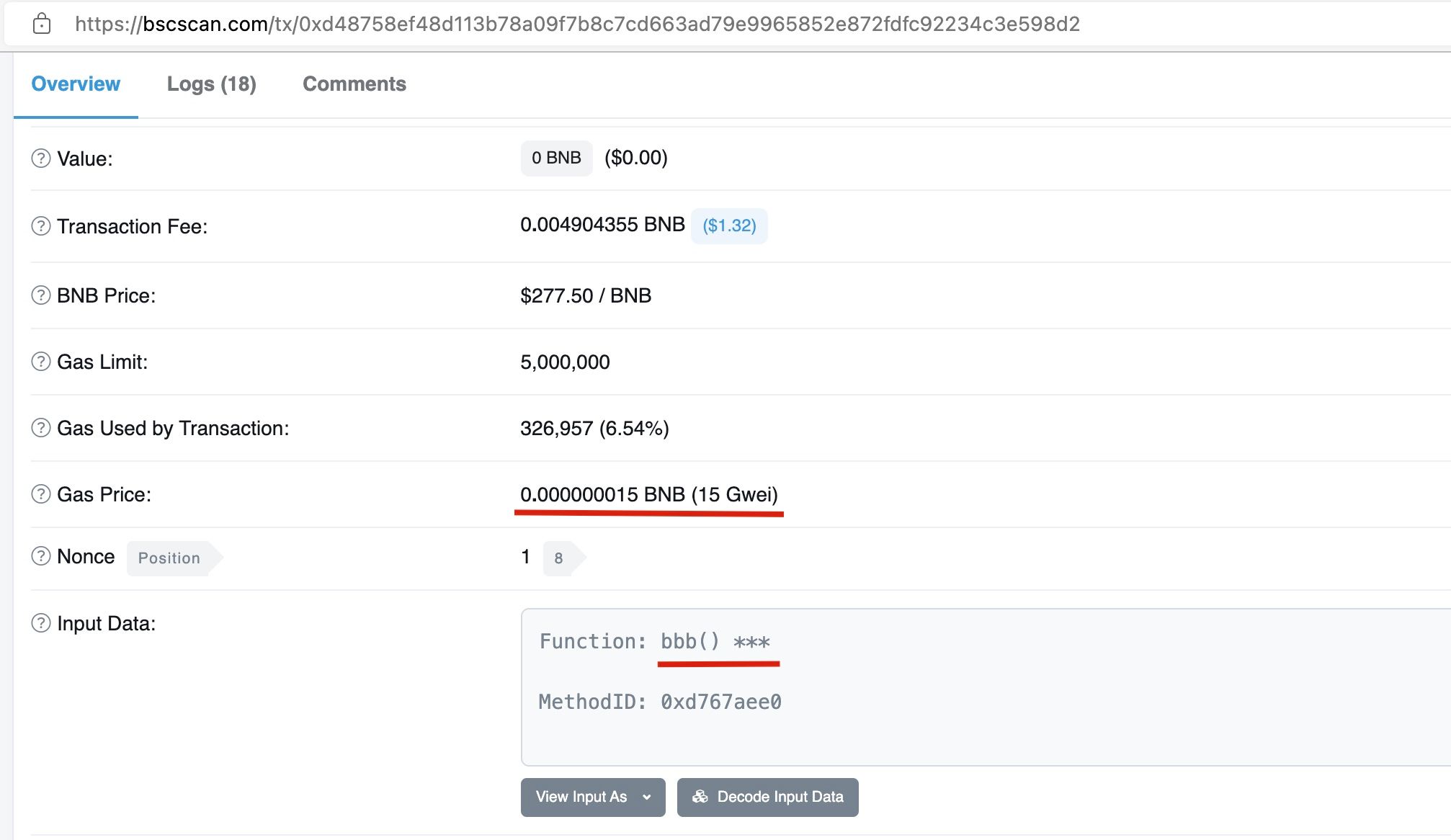
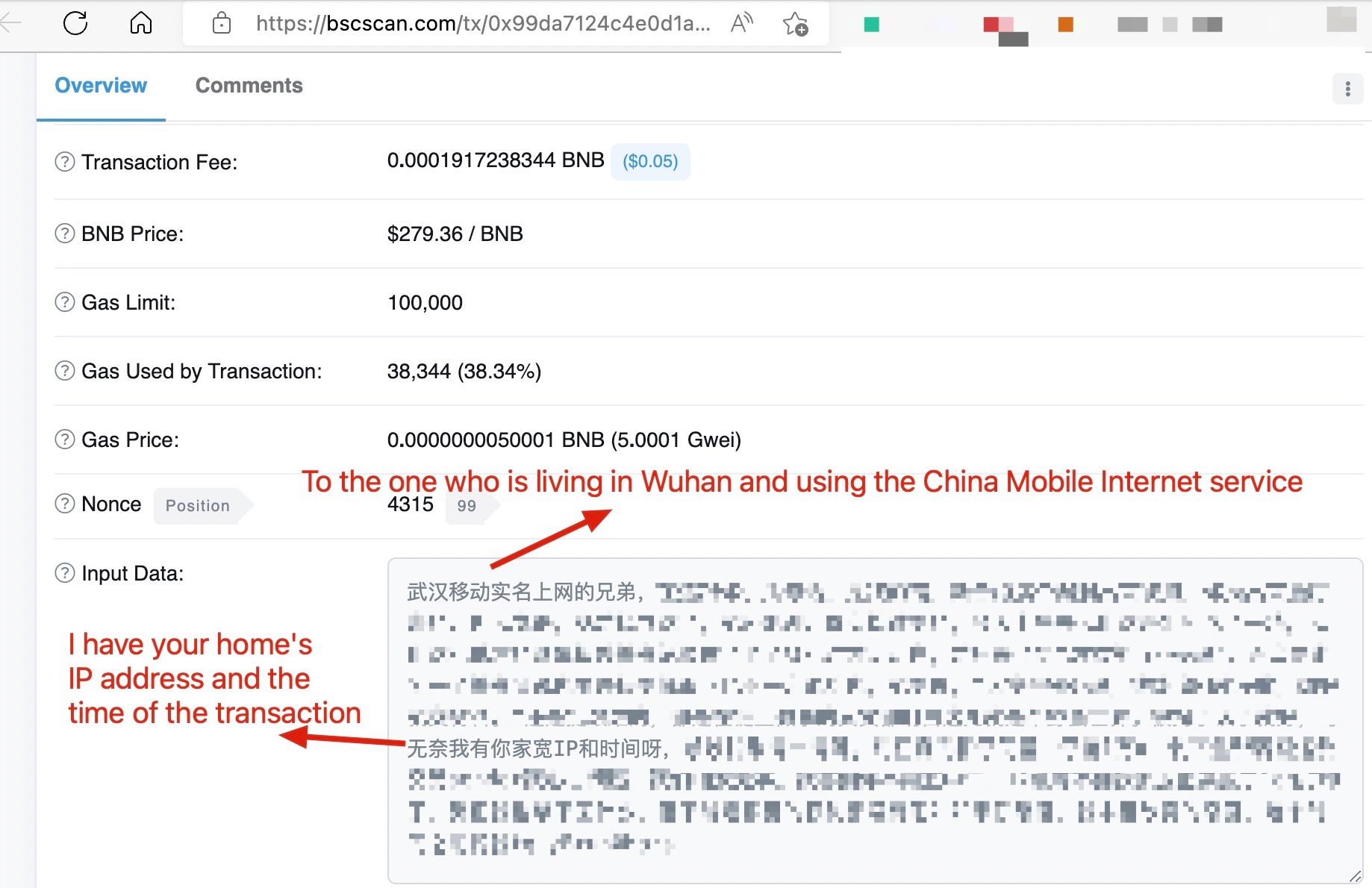
Recently, we have seen an interesting transaction on BSC. The attacker abused the private tx service of BNB48 to hide its attack transaction (The attack profit is around $150K USD). From the following screenshot, we can find that the this transaction was packed by the BNB48 validator with a 15Gwei gas price.
Unfortunately, we did not find a public service that can query transactions that have been packed by the private tx service of BNB48. However, we highly suspect this is the case due to the following two reasons.
- According to BNB48's doc, to use the enhanced RPC, the transaction sender needs to set the gas privce to
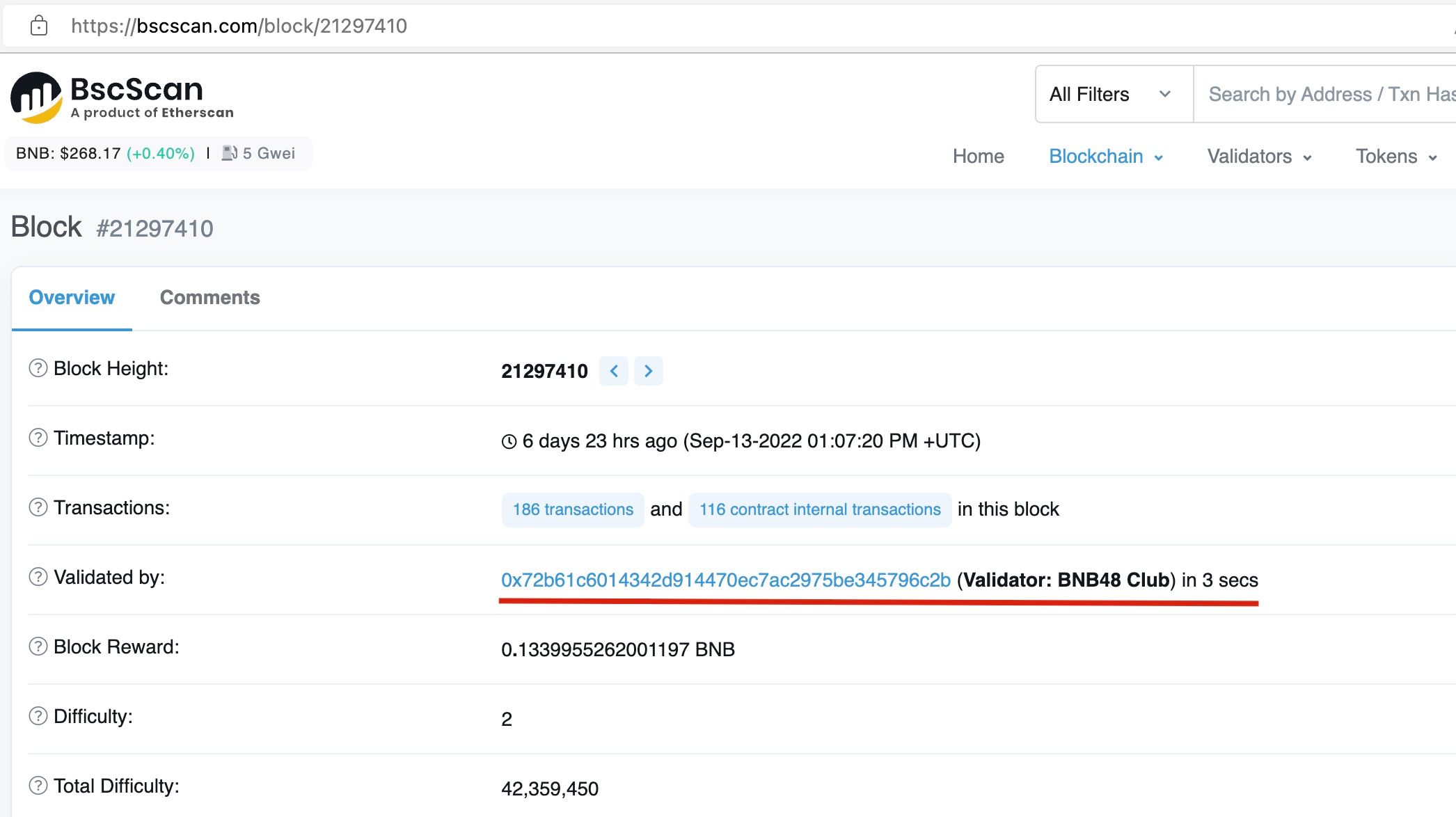
15Gwei. Of course, there still exists a minor chance that the attacker did not use the BNB48 private tx service but happened to use a normal RPC endpoint for the transaction and set the gas price to15Gwei. - Besides, the attacker's contract has a code to limit that the attack transaction can only be executed on BNB48 validator (See the following figure).
From the gas price and the code logic, we highly suspect this transaction abused the BNB48 private tx service.
The attacker's IP has been revealed
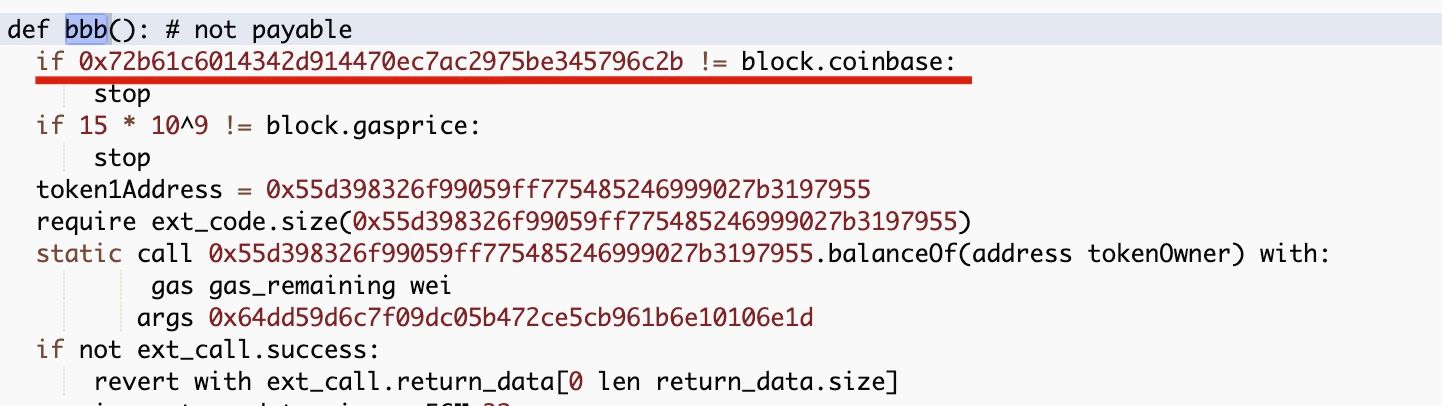
Interestingly, the victim claimed that he/she had successfully identified the IP addresses and the time of the attack transaction. Then the victim sent a message on the chain to ask the attacker to return the funds.
The attacker returned the funds in a serial of transactions [ 1 | 2 | 3 | 4 | 5 | 6].
This raises the question, i.e., if the attack transaction abused the BNB48 private tx service (by sending transactions to the BNB48 RPC endpoint), how the attacker's IP addresses can be identified and leaked? Based on the result that the funds have been returned, the IP address and the geolocation in the message should be real.
Security/privacy concerns of private tx service
We think private tx service is a critical entity in the ecosystem since it protects the transaction from being broadcasted and sandwich-attacked. However, it also raises other security/privacy concerns.
- How to prevent the private tx service from being abused by attackers is an open question. Whether a filtering service is needed in the private tx service is (still) debatable in the community. We are currently developing a system that can help the private tx service provider to monitor the attack service (awareness of the attack is valuable.)
- How to protect the privacy of the users who leverage the private tx service? For instance, the endpoint which accepts the private tx can log the sender's information, such as the IP address and the time. Whether this information is in good protection is unknown.
About BlockSec
BlockSec is a pioneering blockchain security company established in 2021 by a group of globally distinguished security experts. The company is committed to enhancing security and usability for the emerging Web3 world in order to facilitate its mass adoption. To this end, BlockSec provides smart contract and EVM chain security auditing services, the Phalcon platform for security development and blocking threats proactively, the MetaSleuth platform for fund tracking and investigation, and MetaDock extension for web3 builders surfing efficiently in the crypto world.
To date, the company has served over 300 esteemed clients such as MetaMask, Uniswap Foundation, Compound, Forta, and PancakeSwap, and received tens of millions of US dollars in two rounds of financing from preeminent investors, including Matrix Partners, Vitalbridge Capital, and Fenbushi Capital.
Official website: https://blocksec.com/
Official Twitter account: https://twitter.com/BlockSecTeam



