On Nov 5th, bZX protocol was reported hacked. The attacker drained tokens in the affected smart contracts. After the initial analysis of the attack transactions, we suspect it’s due to the compromised private key of the developer.
Attack process
The process is roughly simple. The privileged function transferOwnership is invoked to transfer the ownership of affected smart contract to a new one, e.g., 0x0acc0e5faa09cb1976237c3a9af3d3d4b2f35fa5. Then the new contract owner can transfer all the tokens that have been approved to the smart contract to arbitrary addresses.
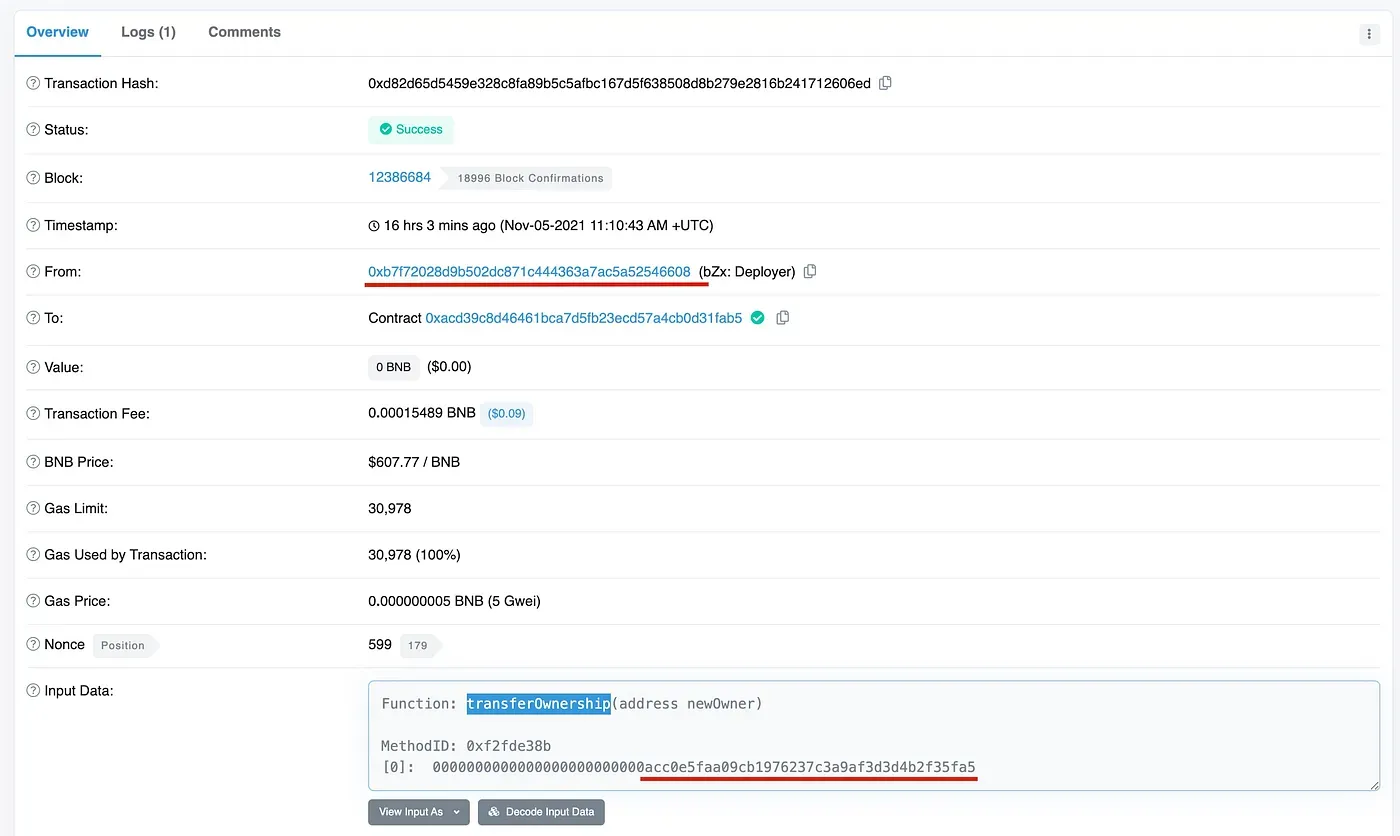
Note that, the privileged function transferOwnership can only be invoked by the current owner of the smart contract. Indeed, we find the caller of this function is 0xb7f72028d9b502dc871c444363a7ac5a52546608, which is the contract creator of the affected smart contract.
We do not know the exact reason why the contract creator transfers the ownership to other addressees. However, we suspect it’s due to the compromised (or leaked) developer private key.
Conclusion
In summary, the security of the private key of DApps is essential to the security of the application, especially for the ones that are not using DAO. We suggest that the project owner can use some new techniques such as confidential computing and MPC to secure the private key.
About BlockSec
BlockSec is a pioneering blockchain security company established in 2021 by a group of globally distinguished security experts. The company is committed to enhancing security and usability for the emerging Web3 world in order to facilitate its mass adoption. To this end, BlockSec provides smart contract and EVM chain security auditing services, the Phalcon platform for security development and blocking threats proactively, the MetaSleuth platform for fund tracking and investigation, and MetaSuites extension for web3 builders surfing efficiently in the crypto world.
To date, the company has served over 300 esteemed clients such as MetaMask, Uniswap Foundation, Compound, Forta, and PancakeSwap, and received tens of millions of US dollars in two rounds of financing from preeminent investors, including Matrix Partners, Vitalbridge Capital, and Fenbushi Capital.
Official website: https://blocksec.com/
Official Twitter account: https://twitter.com/BlockSecTeam




