We are thrilled to release Rustle: the first automatic auditor offered by BlockSec for NEAR community.
Rustle has several great features:
- Rustle can currently detect 20+ types of issues in the NEAR contract. See the section Detectors for the full detector list.
- Rustle is easy to use. We provide thorough installation commands and tutorials. Furthermore, we also prepare a docker for users for quick start.
- Rustle is rather swift, most of the NEAR contracts can be analyzed within 3 minutes.
- Rustle is user-friendly with reports in both CSV and JSON format. We also provide a script to help you import the result to Notion.
Detectors
All vulnerabilities Rustle can detect. The detail documentation can be found here.
| Detector Id | Description | Severity |
|---|---|---|
| unhandled-promise | Detects Promises that are not handled | High |
| non-private-callback | Missing macro #[private] for callback functions | High |
| reentrancy | Finds functions that are vulnerable to reentrancy attack | High |
| unsafe-math | Lack of overflow check for arithmetic operation | High |
| self-transfer | Missing check of sender != receiver | High |
| incorrect-json-type | Incorrect type used in parameters or return values | High |
| div-before-mul | Precision loss due to incorrect operation order | Medium |
| round | Rounding without specifying ceil or floor | Medium |
| lock-callback | Panic in callback function may lock contract | Medium |
| yocto-attach | No assert_one_yocto in privileged function | Medium |
| prepaid-gas | Missing check of prepaid gas in ft_transfer_call | Low |
| non-callback-private | Macro #[private] used in non-callback function | Low |
| unused-ret | Function result not used or checked | Low |
| upgrade-func | No upgrade function in contract | Low |
| tautology | Tautology used in conditional branch | Low |
| inconsistency | Use of similar but slightly different symbol | Low |
| timestamp | Find all uses of timestamp | Info |
| complex-loop | Find all loops with complex logic which may lead to DoS | Info |
| ext-call | Find all cross-contract invocations | Info |
| promise-result | Find all uses of promise result | Info |
| transfer | Find all transfer actions | Info |
How to use
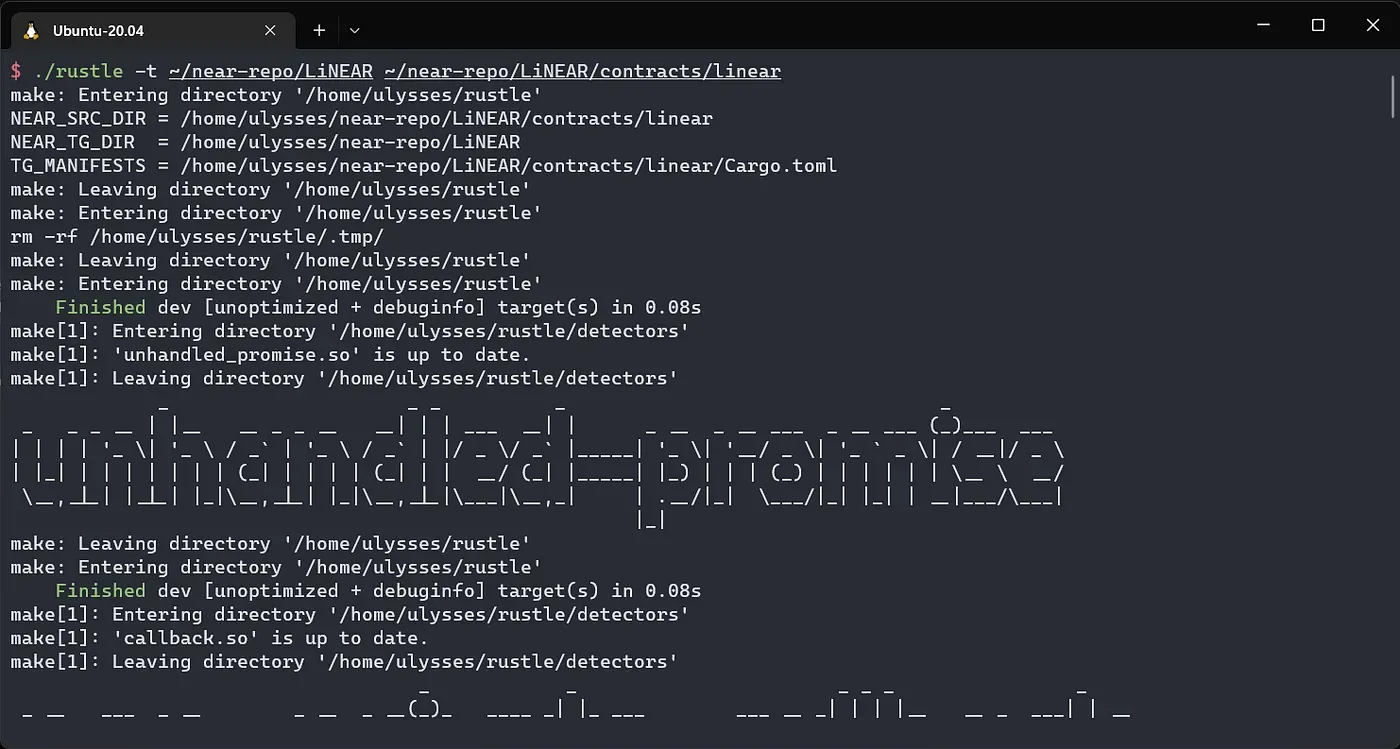
We utilize Rustle to analyze a popular NEAR contract (i.e., LiNEAR). Commands have been tested in Ubuntu 20.04 LTS.
-
Follow the installation manual on the GitHub page. If you want to use docker, skip this and go to the docker manual.
-
Prepare the NEAR contract for Rustle to analyze.
git clone https://github.com/linear-protocol/LiNEAR.git ~/near-repo/LiNEAR -
Start analysis by running
./rustle../rustle -t ~/near-repo/LiNEAR ~/near-repo/LiNEAR/contracts/linear
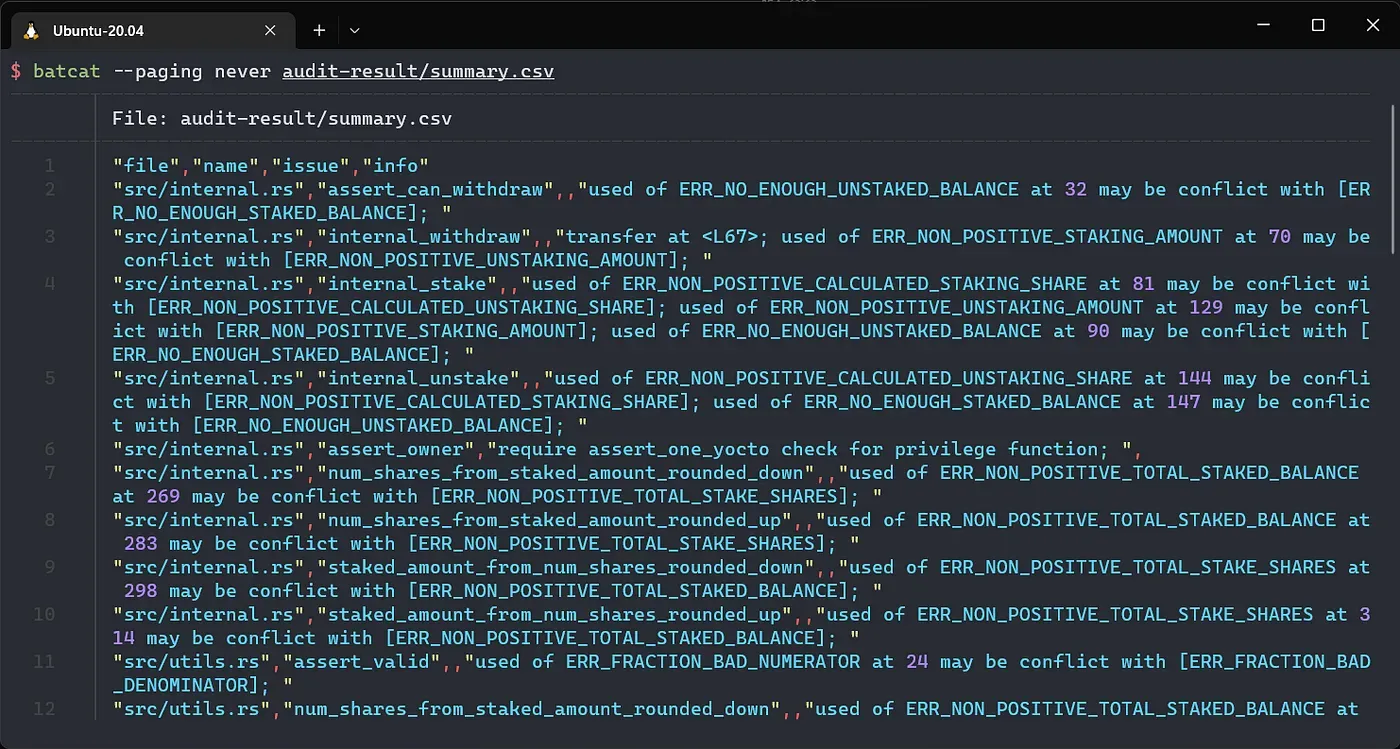
- Check the report at
audit-result/summary.csv
- You can specify which detectors or severity groups to use.
./rustle -h for details.
Example:
./rustle -t ~/near-repo/LiNEAR ~/near-repo/LiNEAR/contracts/linear -d high,medium,complex-loop
One more thing
Rustle can be used in the development process to scan the NEAR smart contracts iteratively. This can save a lot of manual effort and mitigate part of potential issues. However, vulnerabilities in complex logic or related to semantics are still the limitation of Rustle. Locating complicated semantic issues requires the experts in BlockSec to conduct exhaustive and thorough reviews. Contact us for audit service.
Issues and PRs are also welcomed.
About BlockSec
BlockSec is a pioneering blockchain security company established in 2021 by a group of globally distinguished security experts. The company is committed to enhancing security and usability for the emerging Web3 world in order to facilitate its mass adoption. To this end, BlockSec provides smart contract and EVM chain security auditing services, the Phalcon platform for security development and blocking threats proactively, the MetaSleuth platform for fund tracking and investigation, and MetaSuites extension for web3 builders surfing efficiently in the crypto world.
To date, the company has served over 300 esteemed clients such as MetaMask, Uniswap Foundation, Compound, Forta, and PancakeSwap, and received tens of millions of US dollars in two rounds of financing from preeminent investors, including Matrix Partners, Vitalbridge Capital, and Fenbushi Capital.
Official website: https://blocksec.com/
Official Twitter account: https://twitter.com/BlockSecTeam




