In November 2020, a critical vulnerability in Loopring’s LRC Protocol Fee Vault allowed attackers to exploit access control weaknesses and manipulate token prices via flash loan attacks. This incident highlights the importance of robust access control and continuous DeFi security monitoring to prevent costly exploits.
Introduction to the Loopring (LRC) Protocol Incident
In late 2020, several Ethereum-based DeFi platforms, including Pickle Finance and 88mph, experienced security incidents. To detect such vulnerabilities, BlockSec developed the ThunderForecast system, which identified suspicious transactions involving unusually large trade rate differences and consistent Ether gains by the same external owned account (EOA).
Using our EthScope system, we analyzed these transactions and discovered an exploit targeting a vulnerability in Loopring’s vault protocol, specifically the LRC Protocol Fee Vault (LRCPFV). This blog post details the attack, its impact, and lessons learned for the DeFi security community.
LRC Protocol Fee Vault Overview
Loopring is an open-source decentralized exchange (DEX) protocol on Ethereum. Its native token, LRC (ERC-20), is used within the ecosystem. Loopring’s vault protocol, known as the LRC Protocol Fee Vault (LRCPFV), stores protocol fees and allows swapping fees to LRC tokens.
The vulnerable function in LRCPFV is sellTokenForLRC, which enables swapping tokens for LRC without proper access control, allowing anyone to invoke it.
function sellTokenForLRC(
address token,
uint amount
)
external
nonReentrant
{
require(amount > 0, "ZERO_AMOUNT");
require(token != lrcAddress, "PROHIBITED");
address recipient = tokenSellerAddress == address(0) ? owner : tokenSellerAddress;
if (token == address(0)) {
recipient.sendETHAndVerify(amount, gasleft());
} else {
token.safeTransferAndVerify(recipient, amount);
}
require(
tokenSellerAddress == address(0) ||
ITokenSeller(tokenSellerAddress).sellToken(token, lrcAddress),
"SELL_FAILURE"
);
emit TokenSold(token, amount);
}Because this function lacks access control, attackers could repeatedly invoke it to manipulate token prices and profit from arbitrage opportunities.
Details of the Attack
We analyzed a representative attack transaction: 0x00b2c.... The attack involved six key steps:
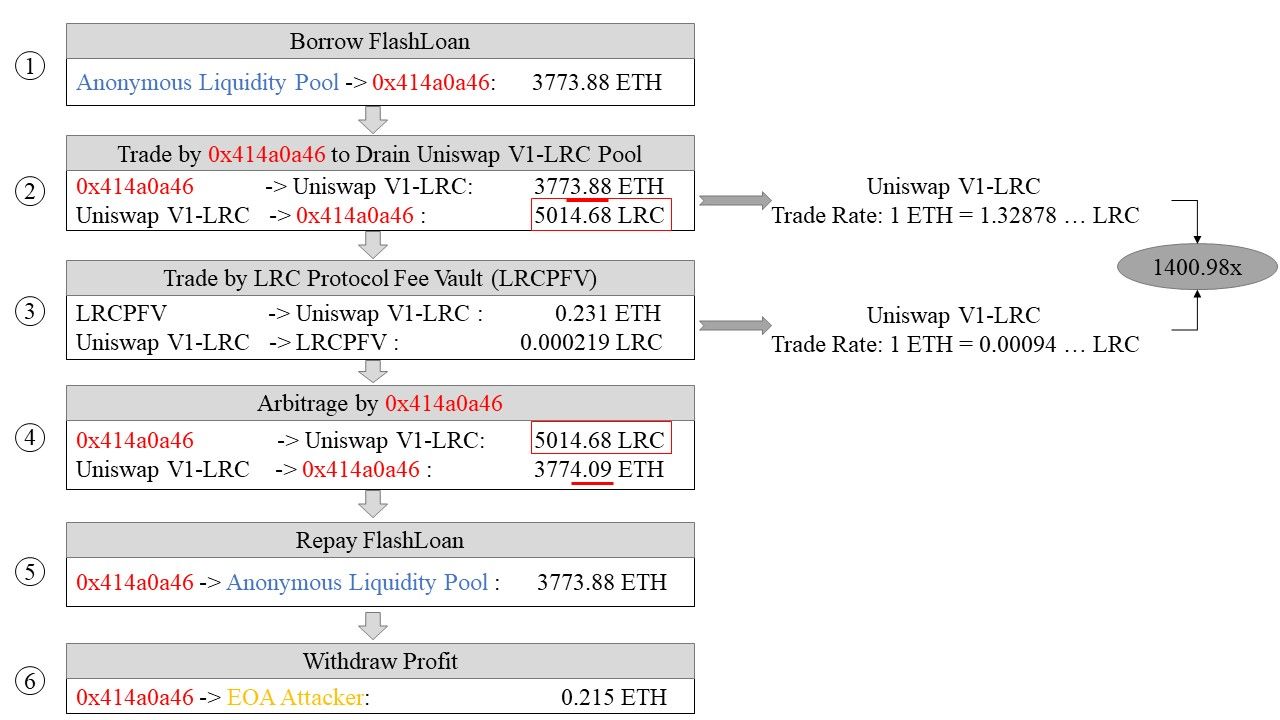
- Flash Loan: Borrowed 3,773.88 ETH from a flash loan provider (
0xEB7e...). - Initial Swap: Converted 3,773.88 ETH to 5,014.68 LRC on Uniswap V1-LRC at a rate of 1 ETH = 1.32878 LRC.
- Fee Vault Swap: Swapped 0.231 ETH fee stored in LRCPFV to 0.000219 LRC by invoking the vulnerable
sellTokenForLRCfunction. This unauthorized call manipulated the LRC price on Uniswap, drastically increasing its value against ETH (1 ETH = 0.00094 LRC). - Profitable Swap: Swapped 5,014.68 LRC back to 3,774.09 ETH on Uniswap V1-LRC, gaining an extra 0.215 ETH due to the manipulated price.
- Loan Repayment: Returned the 3,773.88 ETH flash loan.
- Profit Transfer: Sent the 0.215 ETH profit to the attacker’s EOA.
This exploit leveraged a flash loan attack combined with price manipulation and lack of access control in the vault contract.
Impact and Scale of the Attack
The analyzed transaction occurred on October 13, 2020. Using CoinGecko data, the LRC price was approximately 0.0005175 ETH at that time.
Our investigation uncovered:
- Malicious Contracts: 3 deployed by the attacker (
0xa896...,0x414a...,0xd91d...). - Attack Volume: 90 transactions launched by the attacker’s EOA (
0x81e8...) since block 9,644,449, where LRCPFV was deployed. - Maximum Profit: One transaction (
0x33eab...) yielded 9.89 ETH profit. - Total Profit: Approximately 80.97 ETH (~48,849 USD as of October 1, 2020).
The root cause was the missing access control in the sellTokenForLRC function, enabling repeated exploitation.
Lessons Learned and The End
As the Ethereum DeFi ecosystem grows, security challenges such as access control vulnerabilities become increasingly critical. While high-profile attacks often grab attention, less conspicuous vulnerabilities can cause significant financial losses, as demonstrated by this incident.
Loopring lost approximately 80.97 ETH due to this exploit, emphasizing the need for rigorous smart contract audits and continuous security monitoring.
For DeFi protocols, implementing strict access control, leveraging tools like BlockSec’s Smart Contract Audit and Phalcon Security, and proactive risk management are essential to safeguard digital assets.
Timeline of the Incident
- 2020/11/30: Suspicious transactions detected by ThunderForecast.
- 2020/12/01: Completed detailed analysis using EthScope.
- 2020/12/02: Reported vulnerability to Loopring team.
- 2020/12/03: Vulnerability confirmed; fix implemented.
- 2020/12/03: Public disclosure of incident details.
- 2021/01/03: CVE-2020-35962 assigned to the vulnerability.






