Solana is a fast and scalable blockchain network that has gained significant popularity in cryptocurrency.
As a Solana user, you may want to track your wallet’s activity and transactions for various reasons, such as monitoring your holdings, verifying recent transactions, or investigating suspicious activity. Or sometimes you want to track the smart money in Solana.
One way is to use Solscan. However, the Solscan can only show the SoL or SPL token transfers in one hop. If you want to track more hops, it will not help you.
MetaSleuth is an efficient tool to track Solana wallet and fund flows in multiple hops. It supports more than 20 different chains and cross-chain transactions.
Input an Address to Get Started
To start tracking a wallet, open MetaSlueth's website (https://metasleuth.io) and insert an address to start the tracking.
Let's use the address 9wAfrMnzrJ1XWXXDDmqh7gH7Q9ZBJjLhgou5GrUcHsZy as an example, input the address and press enter. The tool will perform an intelligent analysis to show the initialized result (as shown in the following Figure).
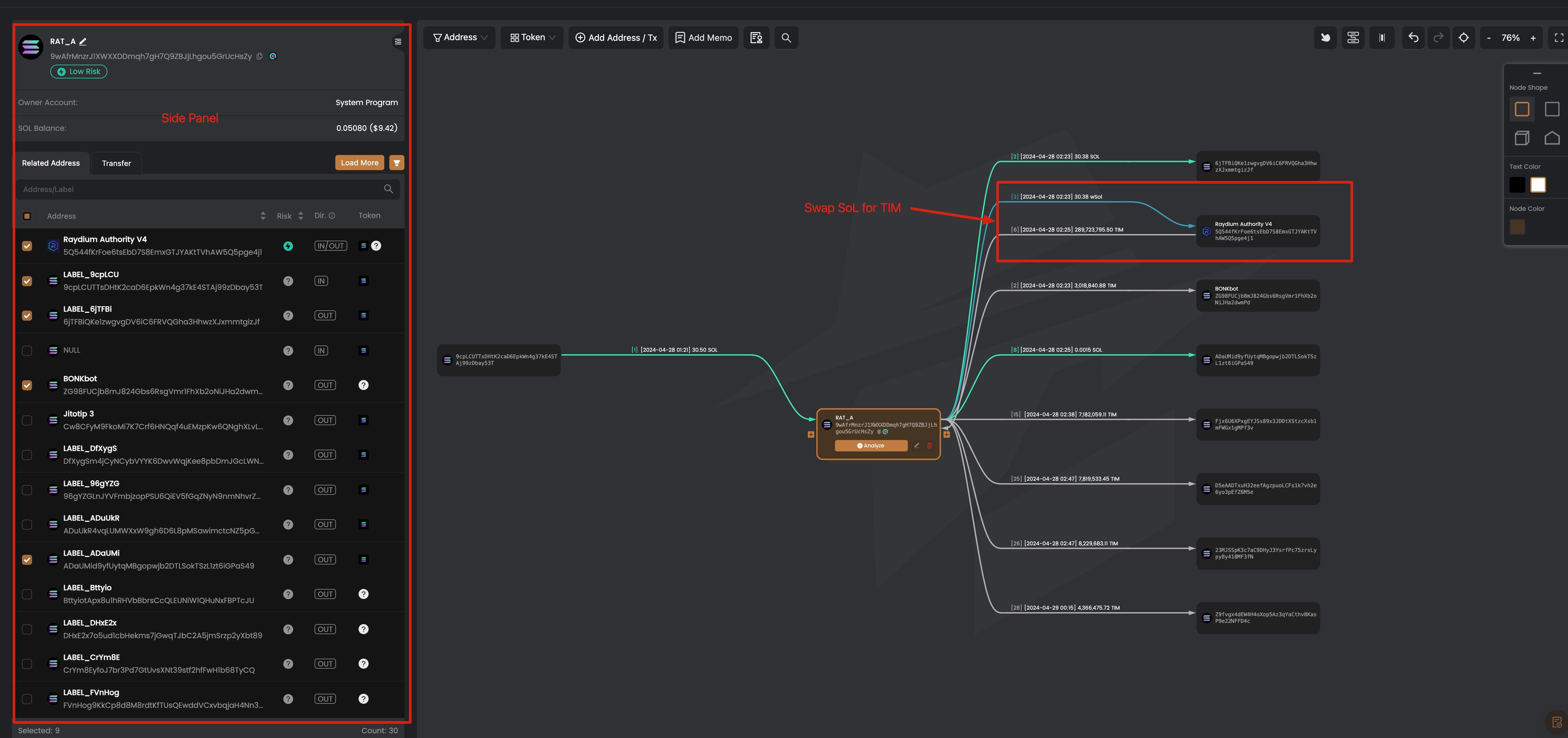
On the left is the side panel of an address, which will be shown when you click an address on the main canvas. The node on the main canvas means an address, and the edge between nodes represents the aggregated token transfers for each token. That means if there are multiple transactions to transfer one token between two nodes, there will be only one edge between them. You can click the edge to show the detailed transactions for the token transfer.
The result shows the token swap in Raydium, with 30.38 wSoL flowing into it and 288,723,795.50 TIM out. As we just said, the edge shows the aggregated token transfers. We can click the edge to see more detailed information.
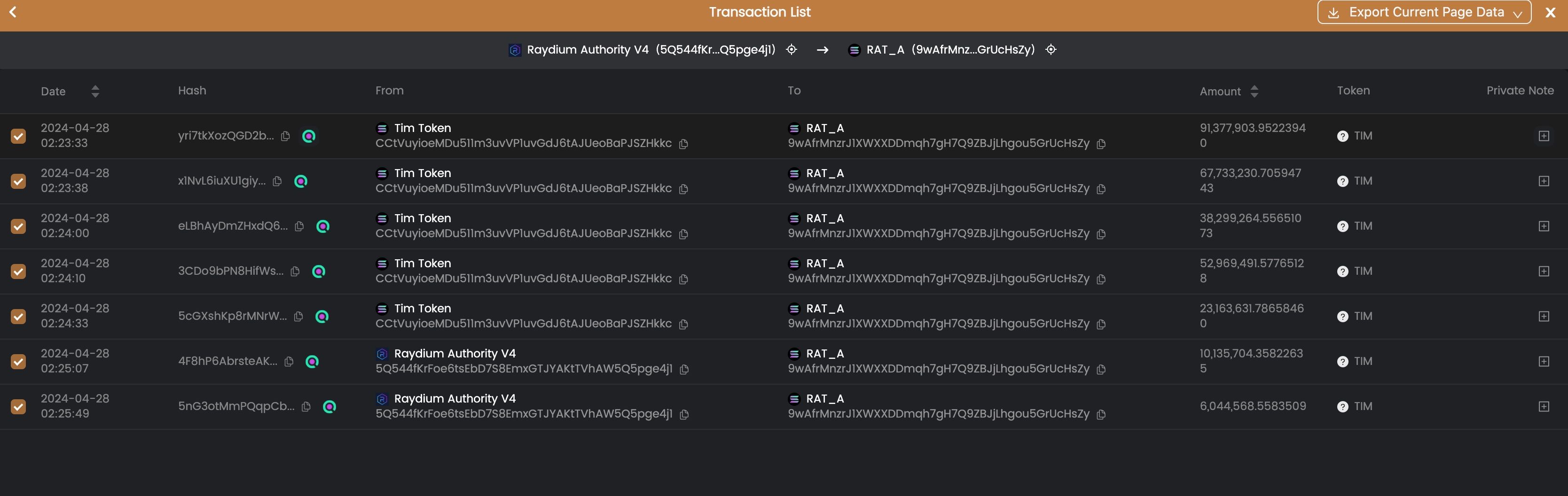
From the transaction list, we can see that the 9wAfr used 30.38 SoL to swap 288,723,795.50 TIM tokens from 04-28 02:33:33 to 04-28 02:25:49 in two minutes.
Track the Fund Flow
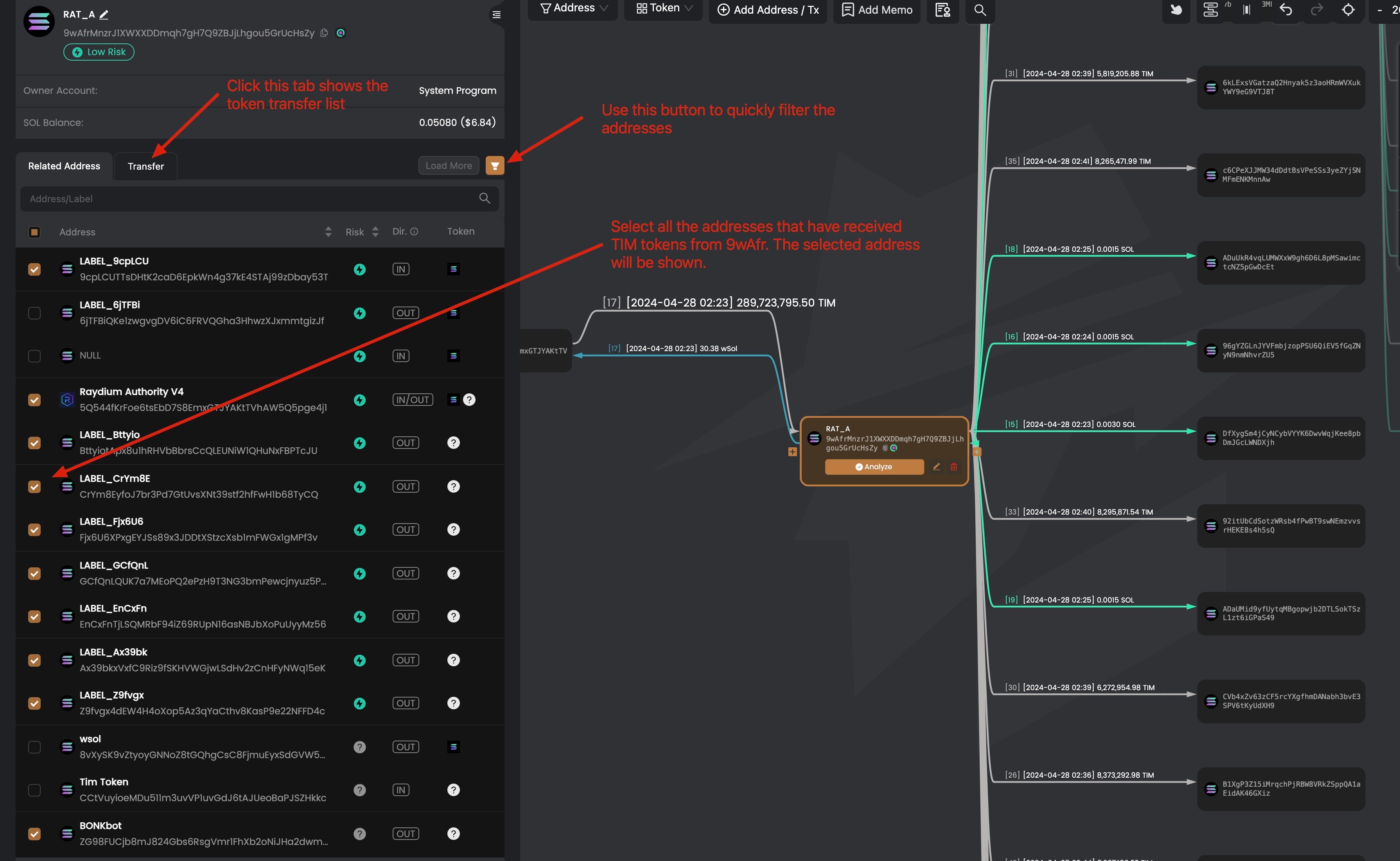
After receiving the TIM tokens, the address 9wAfr wants to sell TIM tokens for profit. Instead of directly selling the tokens using the 9wAfr address, it uses three layers of addresses to hide the trace. How is this achieved?
To track the fund flow, we first find the TIM tokens transferred out from the address 9wAfr. We can click the address 9wAfr to show the side panel, and select all the output TIM tokens.
After selecting the addresses that receive the TIM tokens, we can click the node of the address to track further the token flows. For instance, we can click on the address Ax39bkxVxfC9Riz9fSKHVWGjwLSdHv2zCnHFyNWq15eK, and we find that this address swaps the received TIM tokens to SoL and transferred SoL to DJGiuwGs1WtC1QkEj3GkGtdVoXuEk34uwWmvQvLi72SZ.
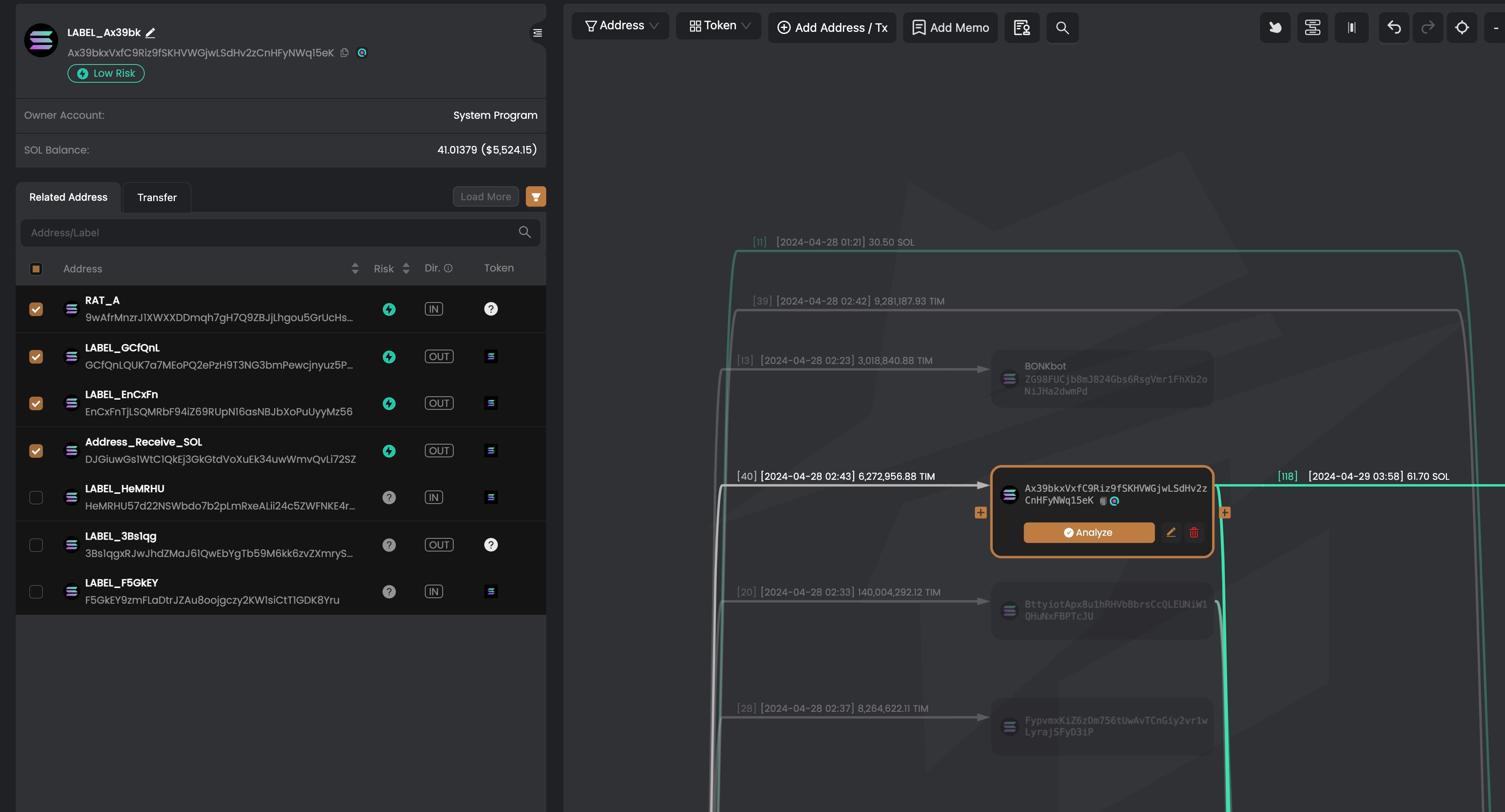
We can use similar methods to track other addresses that receive TIM tokens from 9wAfr.
Subscribe and Enjoy 10% Off Discount
When signing up for MetaSleuth, use BLOCKSEC as the invitation code to enjoy 10% off for the subscription.
https://metasleuth.io/?invite-code=BLOCKSEC





