We find there exist two serious logic vulnerabilities in the @AkuDreams contracts. The first vulnerability can cause a DoS attack and the second vulnerability will make the project fund (more than 34M USD) being locked forever.
Vulnerability I
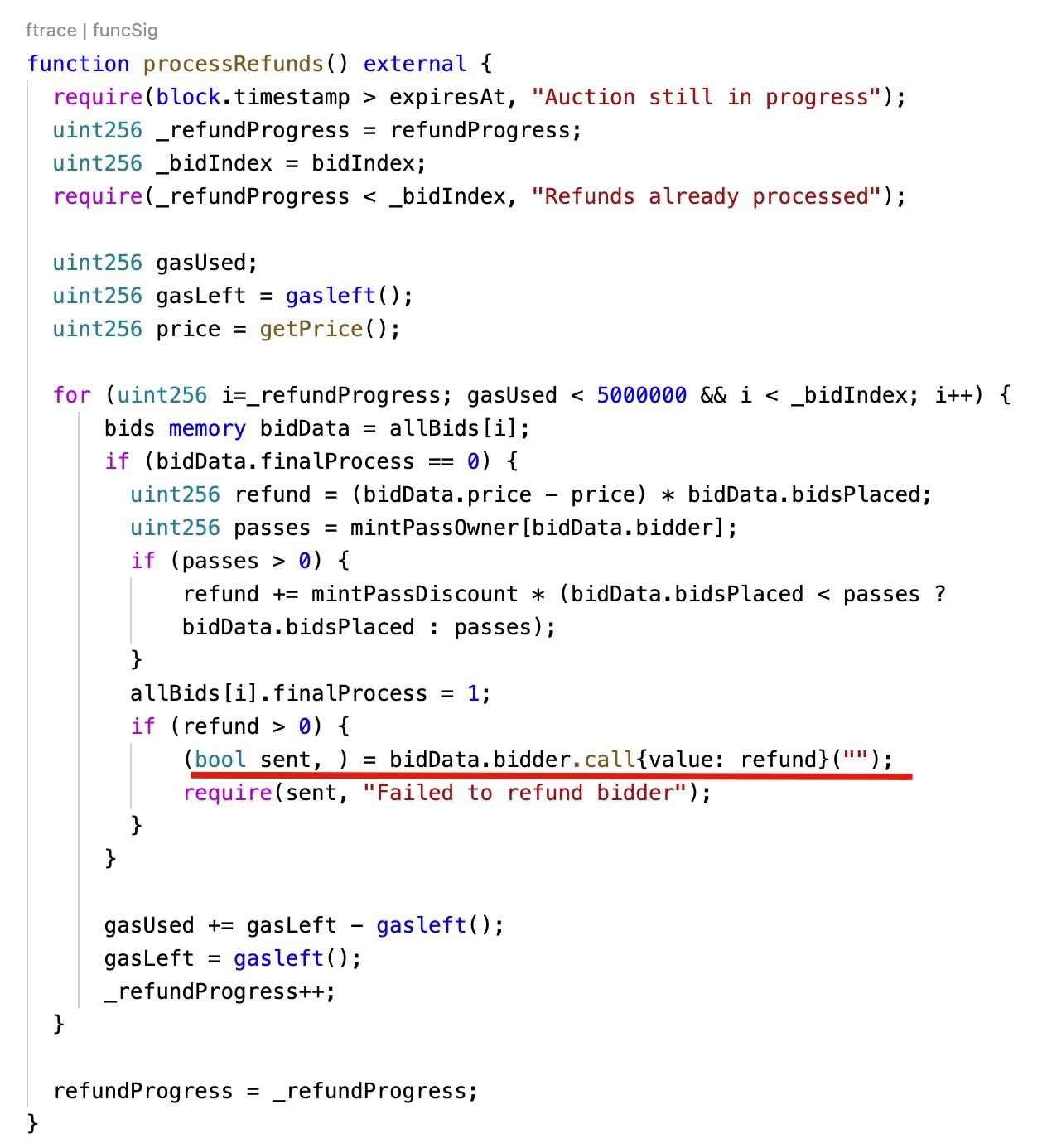
The first vulnerability exists in the processRefunds function. This function has a loop that will refund each bid user's fund. However, the bidder can be a malicious contract that reverts the transaction. This can cause the invocation of processRefunds revert, and none of user's refunds can be successful. Fortunately, this vulnerability has not been exploited.
We suggest that the contract can take the following measures to refund users.
- Ensure that only EOA can bid
- Use ERC20 token, e.g., WETH, instead of ETH
- Has function that allows a user to get the refund by himself
Vulnerability II
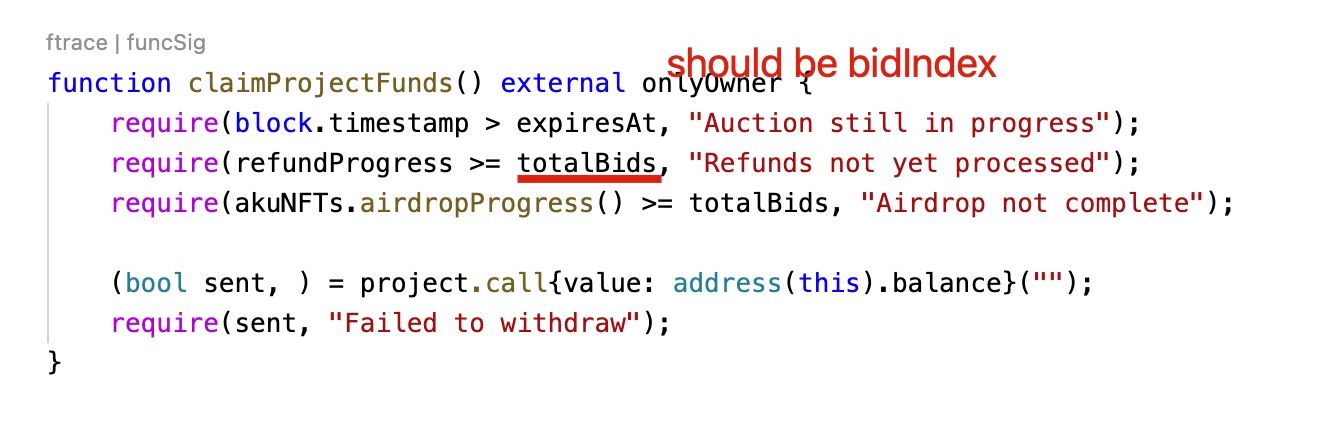
The second vulnerability is a software bug. In the claimProjectFunds function, the project owner can claim the Ether in the contract. However, the require statement require(refundProgress >= totalBids, "Refunds not yet processed"); has a bug, which should compares the refundProgress with _bidIndex instead of totalBids. Due to this vulnerability, the requirement will never be satisfied, and the Ether (11,539.5 Ether) in the contract can be locked for ever.
Summary
We are surprised again (after the NBA NFT case yesterday) that how a high-profile project can neglect the basic software security practice. At least, the project should write enough test cases. Unfortunately, we suspect that the projects are too busy to write the test cases, and lose 3400 USD forever.
About BlockSec
BlockSec is a pioneering blockchain security company established in 2021 by a group of globally distinguished security experts. The company is committed to enhancing security and usability for the emerging Web3 world in order to facilitate its mass adoption. To this end, BlockSec provides smart contract and EVM chain security auditing services, the Phalcon platform for security development and blocking threats proactively, the MetaSleuth platform for fund tracking and investigation, and MetaDock extension for web3 builders surfing efficiently in the crypto world.
To date, the company has served over 300 esteemed clients such as MetaMask, Uniswap Foundation, Compound, Forta, and PancakeSwap, and received tens of millions of US dollars in two rounds of financing from preeminent investors, including Matrix Partners, Vitalbridge Capital, and Fenbushi Capital.
Official website: https://blocksec.com/
Official Twitter account: https://twitter.com/BlockSecTeam




