
Last Friday, our monitoring system detected an attack to coin98 smart contract (0x8aaf408e06feed6a6a6182ea3c464035748b9b31 — the victim contract) on BSC. We immediately DMed the project owner through twitter, but got no response. Since the vulnerability still existed at that time, we did not make it public. Then after a couple of hours, we found that the project owner has created a new contract which fixed the vulnerability. As such, it is safe for us to summarize the vulnerability and the fix here.
Attack transaction and the root cause
The transaction raised by our internal monitoring system drew our attention. After a careful investigation, we confirmed that it’s due to the access control of the route parameter (means the router actually) in the swapExactTokensForTokens function, as follows:
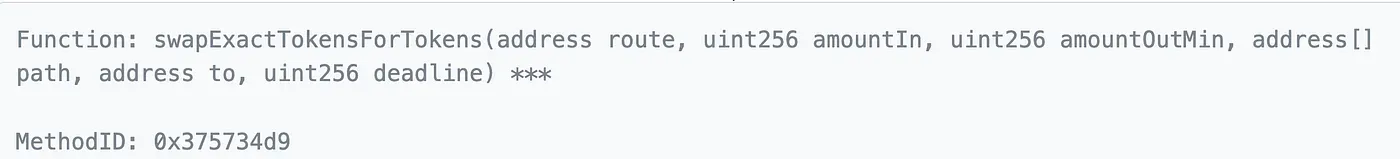
This This contract blindly trusted the route and then invoked the swapExactTokensForTokens function of the router. Before this, it approves all the tokens owned by the victim contract to the route. However, the route could be passed by the attacker. In this case, the attacker can then transfer all the tokens by the victim to itself and then swap for WBNB to make a profit.
The following is one of the attack transaction.

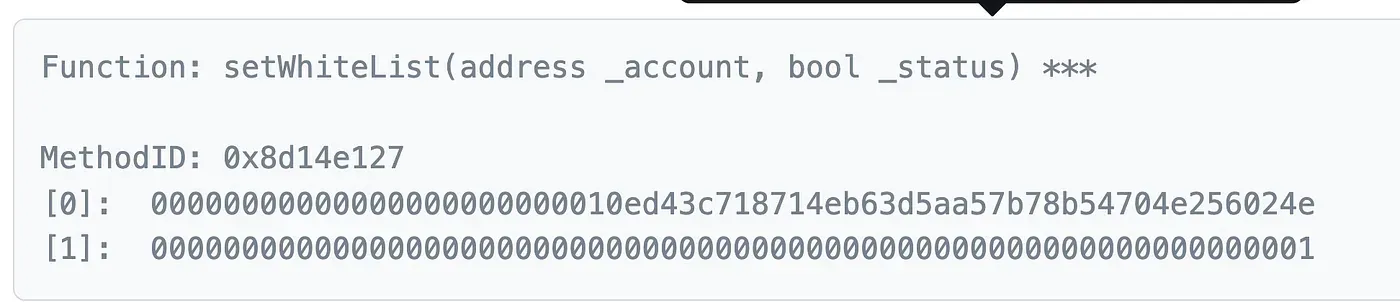
The stealthy fix of the vulnerability
We DMed the project owner on Twitter last Friday, but got no response. We then double checked the contract today and found that there is a new smart contract (0x83f25d16bdf91f51120032f264dad0e1ab1c8227) has been deployed. This new contract has a whitelist for the route:
Conclusion
We have seen many cases that the passed parameter is blindly trusted by the smart contract. This DOES create a severe security hole.
DO NOT TRUST ANY PARAMETERS THAT ARE OUT OF THE CONTROL!
About BlockSec
BlockSec is a pioneering blockchain security company established in 2021 by a group of globally distinguished security experts. The company is committed to enhancing security and usability for the emerging Web3 world in order to facilitate its mass adoption. To this end, BlockSec provides smart contract and EVM chain security auditing services, the Phalcon platform for security development and blocking threats proactively, the MetaSleuth platform for fund tracking and investigation, and MetaSuites extension for web3 builders surfing efficiently in the crypto world.
To date, the company has served over 300 esteemed clients such as MetaMask, Uniswap Foundation, Compound, Forta, and PancakeSwap, and received tens of millions of US dollars in two rounds of financing from preeminent investors, including Matrix Partners, Vitalbridge Capital, and Fenbushi Capital.
Official website: https://blocksec.com/
Official Twitter account: https://twitter.com/BlockSecTeam




