BlockSec Phalcon has been updated to 2.0. Fly with Phalcon and dive into transactions!
Phalcon is a powerful transaction explorer designed for DeFi community. It provides comprehensive data on invocation flow, balance changes, and fund flows for transactions. It also supports transaction simulation.
Phalcon aims to help developers, security researchers, and traders intuitively understand transactions.
This user guide will introduce you to the various features and functions of Phalcon. For better illustration, we use this transaction on Ethereum as an example.
Transaction Search
To search for a transaction, go to the Phalcon Explorerhomepage and enter the transaction hash in the search box. Click on the result to view the transaction parsing details page.
Phalcon currently supports the analysis of transactions on Ethereum, Binance Smart Chain, Polygon, Cronos, and Avalanche C-Chain. More chains are on the way.
Transaction Analysis
The transaction result page is divided into four main modules for a transaction.
- Basic Info
- Fund Flow
- Balance Changes
- Invocation Flow
- Code View (New)
Basic Information
The Basic Info module displays the basic information of the transaction, including the execution status (Status), the sender (Sender), and the recipient (Receiver).
The internal transaction count indicates the number of internal transactions, which can be used to determine the complexity of the transaction. The higher the value, the more complex the transaction.
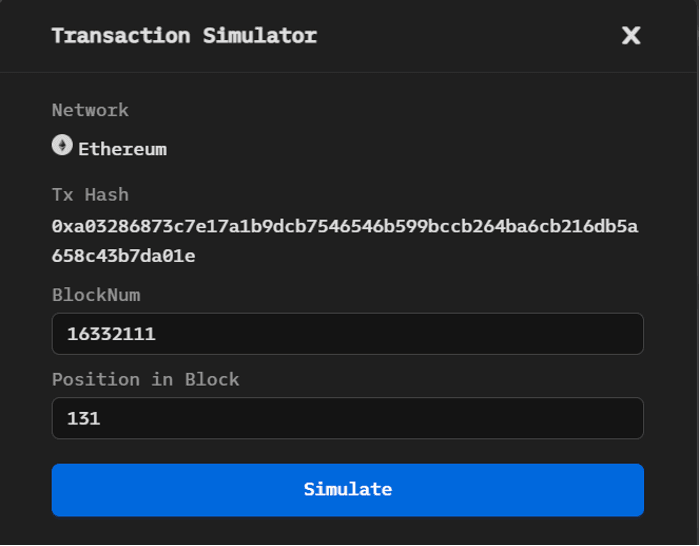
The [Simulate This Tx] button in the top right corner allows you to quickly simulate the results of the current transaction at different Block Number [BlockNum] and position [position in the block] (The transaction simulation be explained in this Section).
Fund Flow
The Fund Flow module illustrates the flow of tokens involved in the transaction as a directed graph. Different nodes represent different account addresses, and a different background color distinguishes nodes representing the sender or recipient of a transaction.
The directed edge and the information on the edge show the transfer direction, the token, and the number of tokens transferred.
- Different serial numbers on the edges are used to distinguish the chronological order of the token transfers.
- Edges of the same color identify transfers of the same token.
- The same directional flow of the same token between two addresses is merged to simplify the transaction’s fund flow map while preserving the characteristics of the token transfer.
The module also provides the ability to zoom in and out of the flow chart in the top right corner. The fund flow graph can be downloaded as SVG or PNG file.
Balance Changes
The Balance Changes module shows the accounts that have a change in the token balance after the transaction is executed.
- The first column lists the addresses with a net inflow or outflow of tokens.
- The second column lists the token information, including the names of the token that flows in or out of the address.
- The third column shows the change in balance, i.e., the token inflow or outflow amount.
- The last column shows the value of the number of tokens flowing in or out of each account when the transaction took place.

Invocation Flow
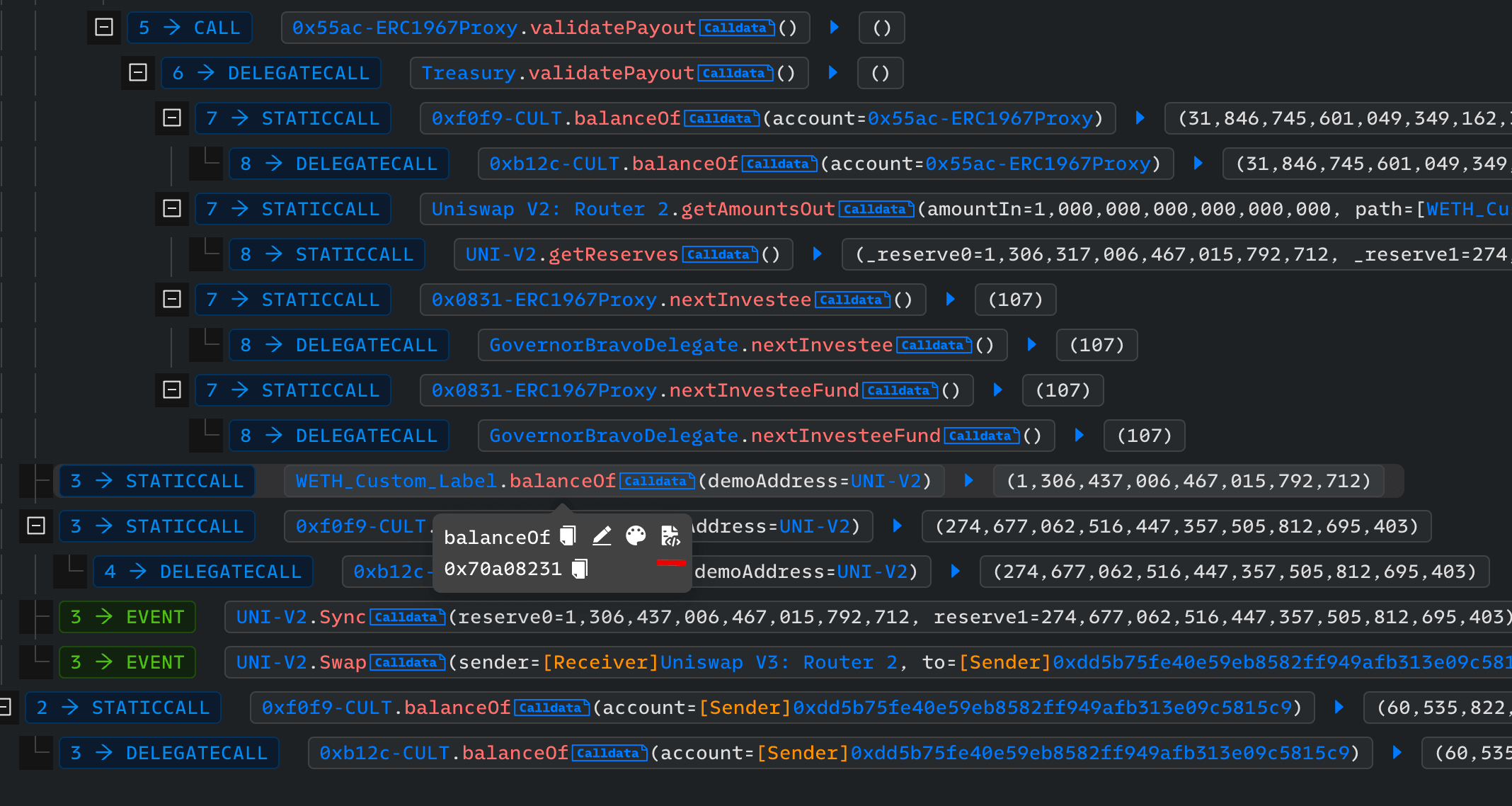
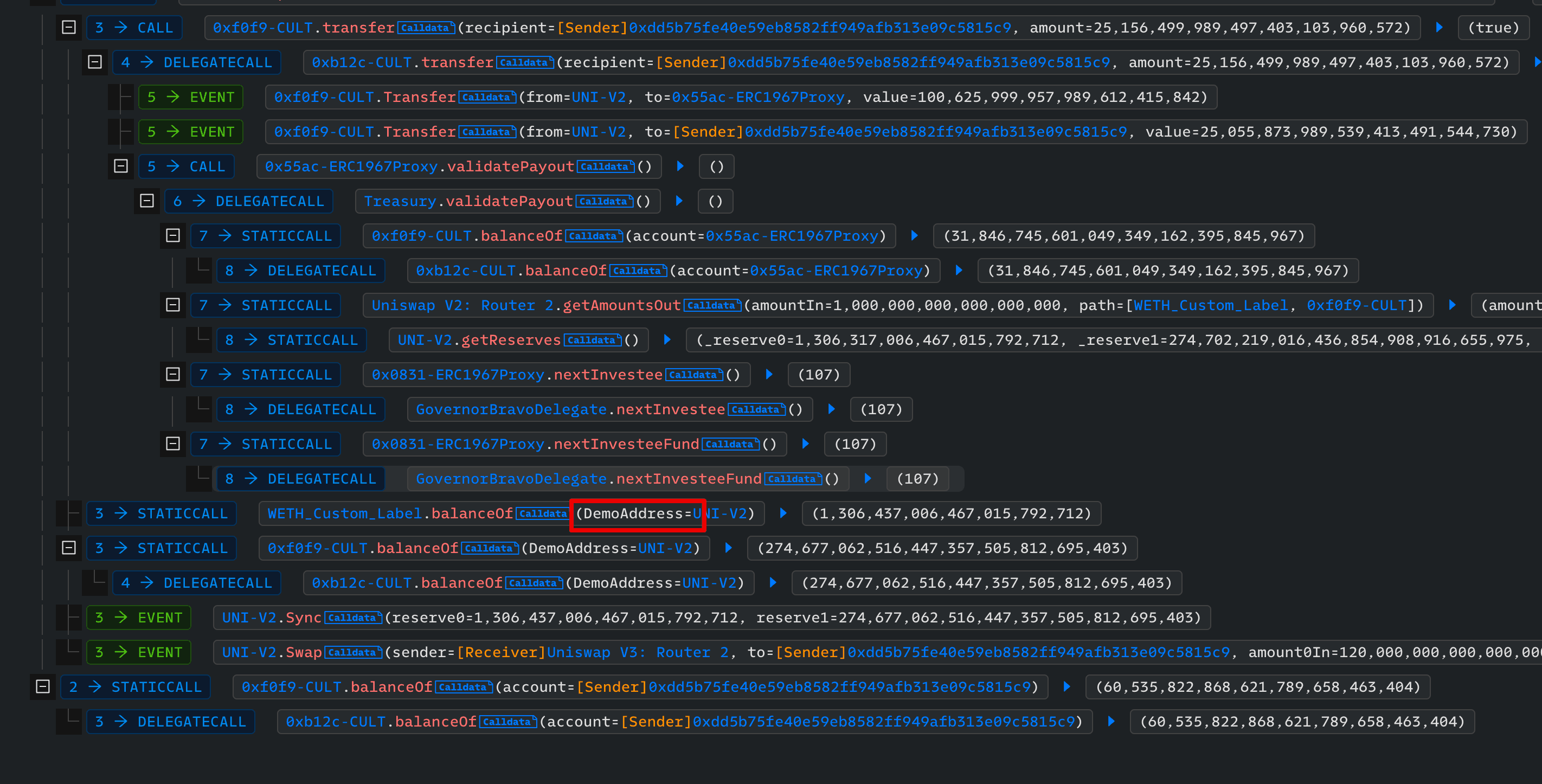
Invocation Flow displays the sequence of function calls in a transaction as a tree structure.
Each node represents a function call or event trigger and includes information such as call stack depth, call type, and call parameters. A search box and a drop-down selection box for call type and expansion are provided at the top of the module to assist users in interpreting the transaction execution flow.
Users can search for and filter desired call flow information by entering an address, function signature, or function selector in the search box. The following figure shows the result of filtering through the WETH address.
The call stack depth can be selected by the user using the drop-down selection box. The following figure shows the call flow display after selecting a call stack depth of 2.
Code View
During the analysis, the code of the verified contract can be shown in the code view. Our code view supports different layouts with the trace, including the support of a separate code view.
-
Trace Only: only show the invocation flow (code trace)
-
Trace & Code (LR): A code view will be shown, with the invocation flow shown on the left and the code view shown on the right. When an invocation of a verified contract is clicked in the invocation flow, the upper part of the code view is the source code of the clicked contract. The bottom part of the code view shows the parameters and return values.
-
Trace & Code (TB): similar to Trace & Code (LR) but the layout of trace/code view is top-bottom instead of left/right.
-
Separate Code View: The code view is in a separate browser tab, which can be moved to another monitor (Good for users with multiple displays.)
Besides, users can quickly switch between different modules at the top of the code view on the right. The history of source code viewing within that transaction is provided so that other source codes can be viewed easily.
Customization
Phalcon supports customizations to facilitate the analysis.
Custom Highlight
During the analysis, the address, function, and event can be highlighted with a custom color.

Custom Label
The address, function, and event can be set with custom labels.

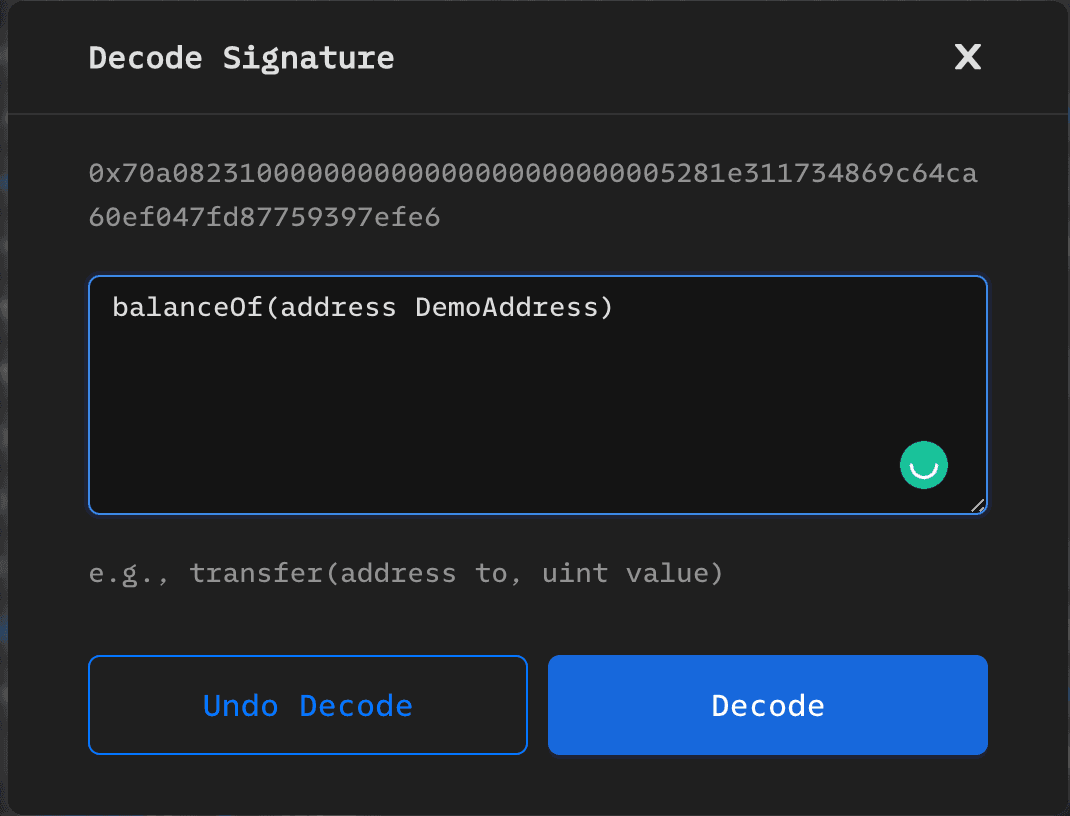
Custom Function Signature
For the calldata of a contract, a custom function signature can be provided to decode the calldata.
Transaction Simulation
Simulate a Custom Transaction
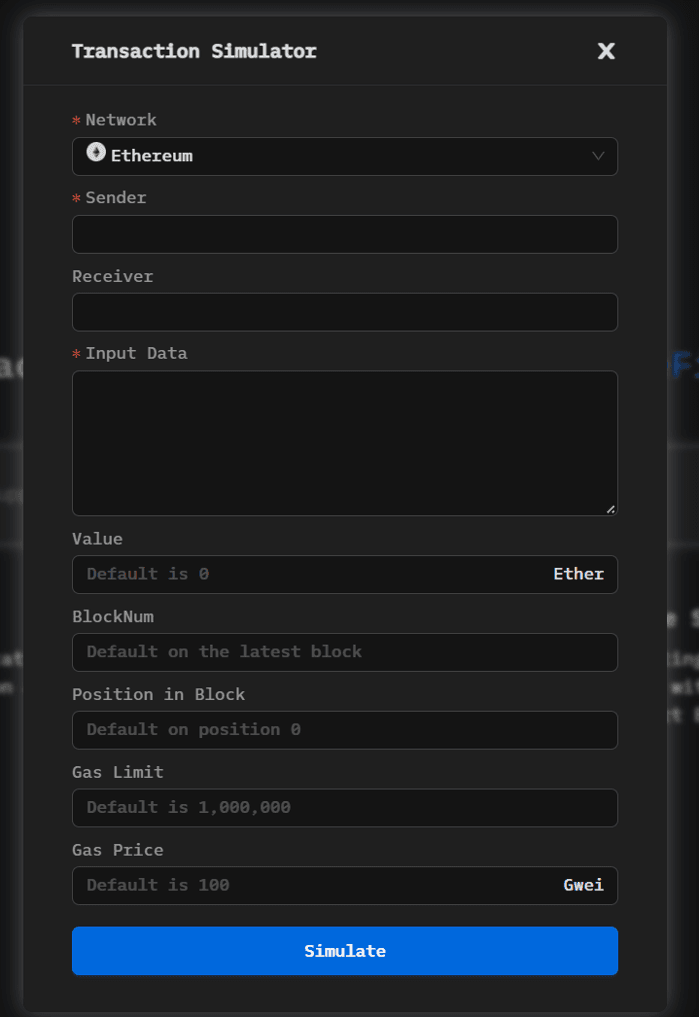
To simulate a transaction, click the [Simulation] button and fill in the required information in the Transaction Simulator panel. Then click the [Simulate] button to view the simulation results on the details page. You can also change the website theme by clicking the icon next to the [Simulation] button.
Simulate an Existing Transaction
The [Simulate This Tx] button in the top right corner of the transaction detail page allows a user to quickly simulate the results of the current transaction at different Block Number [BlockNum] and position [position in the block].