Author:JP Intelligence On Chain
Background
The world of crypto has seen a lot of disruption, with thefts amounting to $3.7 billion worldwide in 2022. Even though there was a small drop in these thefts in 2023, the overall trend of online theft is still rising.
The founder of Intelligence Onchain, a research and investigations organization, as well as Armored, which is dedicated to protecting protocols from exploitation through partnerships with reputable partners such as BlockSec. In this blog, JP will provide an insightful overview of Metasleuth, which is essential in visualizing transactions in a way that is meaningful for victims, law enforcement, and lawyers.
Content
I am JP, the founder of Intelligence Onchain, a research and investigations organization, as well as Armored, a company dedicated to protecting protocols from exploitation through numerous collaborations with esteemed partners such as BlockSec.
Today, I'd like to discuss Metasleuth, a tool I use almost daily. It assists me in investigations and visualizes transactions in a way that is meaningful for victims, law enforcement, and lawyers alike. Metasleuth is the preferred visualization tool for all our investigators at IOC for our investigations. Let's delve into why using a tool like Metasleuth is of paramount importance.
Visualization Techniques
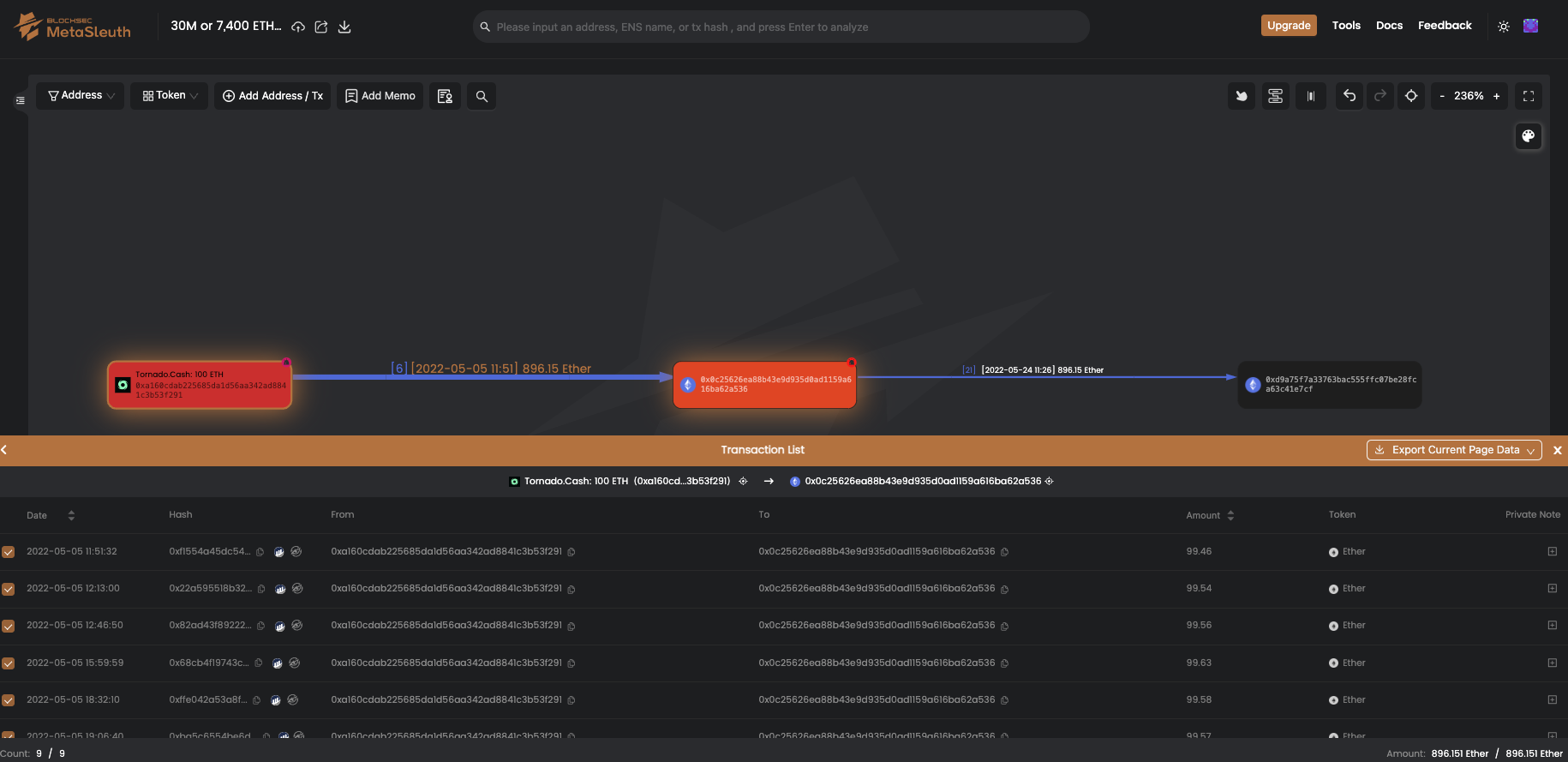
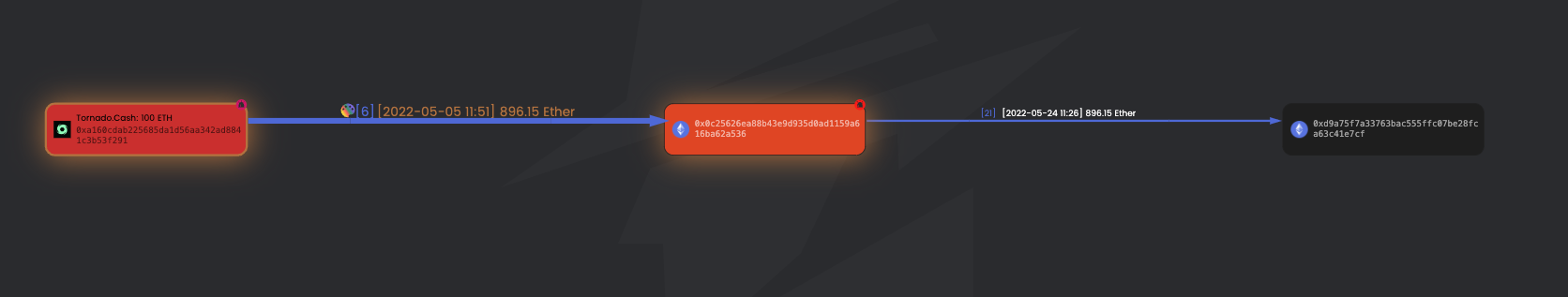
Concerning navigation, funds typically flow from left to right, though there are exceptions, especially as the charts expand. You can interact with various nodes here; for instance, this is a node, and so are these. This one represents a contract.
Tornado Cash is a protocol associated with money laundering and is illegal. Therefore, let's color it red to signify danger. Recognizing that this user is a recipient of funds from Tornado Cash, we could assign them a different shade to indicate their involvement but still denote that they're on the wrong side of the law.
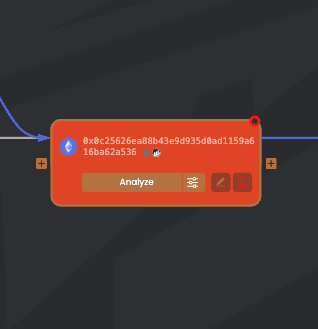
As funds progress, it's theoretically less likely that this individual is the original sender, though this hinges on the transaction details. Metasleuth allows you to deep dive into a specific Ethereum address, filter transactions, and specify what you see, such as ERC-20 tokens, and pinpoint a particular time frame. This functionality is exceedingly helpful.
Analytical Features
If we choose to analyze this address, the 'analyze' feature will showcase all the significant transactions on the left panel. Here we can see that there have been very few transactions. In terms of navigation, we have tabs for related addresses and transfers.
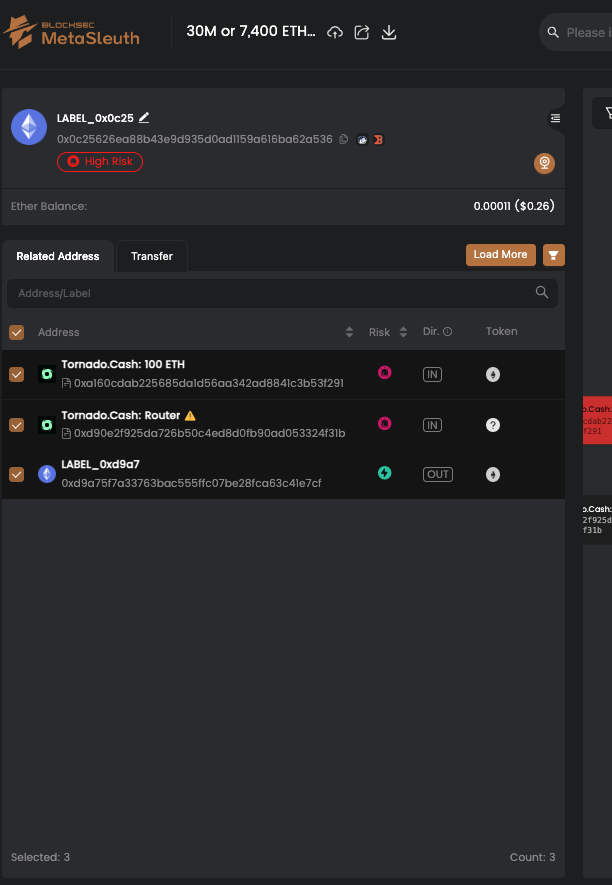
Related Addresses
'Related addresses' tab shows which addresses have had interactions. For example, we notice one transaction with $1,000 from Tornado, marked with a yellow exclamation point, likely indicating a zero-value token or an irrelevant event, perhaps even a scam. We have the option to hide such transactions.
Automatic Layout
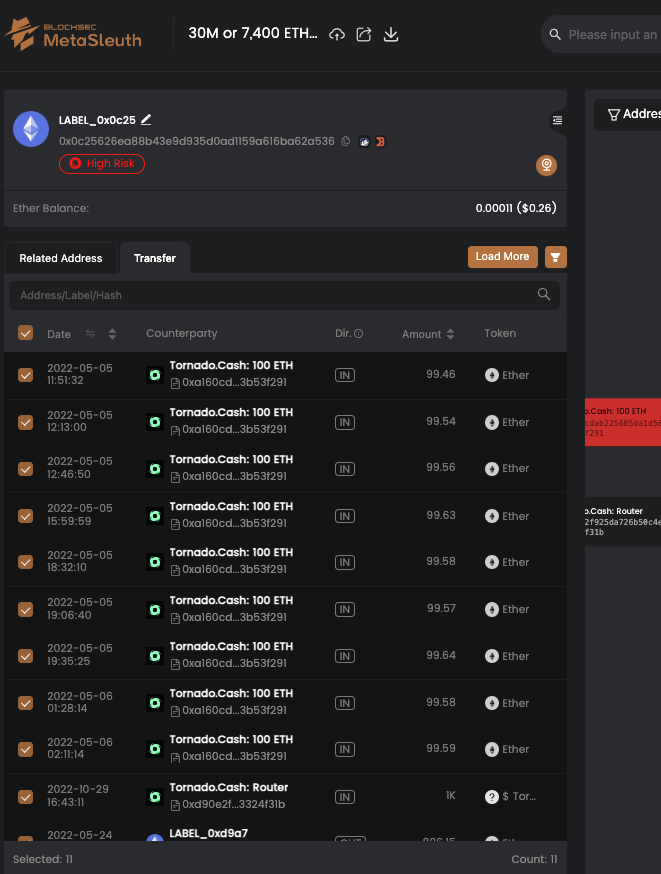
For those who prefer order, the 'automatic layout' button reorganizes everything neatly. It's important to differentiate between the 'related address' and 'transfer' tabs. The former shows a single address as the recipient from Tornado Cash, while the latter displays all incoming transactions.
Edge List
If you click on the line connecting two nodes, it brings up an edge list. Clicking 'details' will reveal all the transaction hashes, links to them, including links to Phalcon, addresses involved, and the amounts transferred. If you're conducting an investigation and are interested in a particular edge, you can export the data to a CSV, which is handy for report generation for victims or law enforcement.
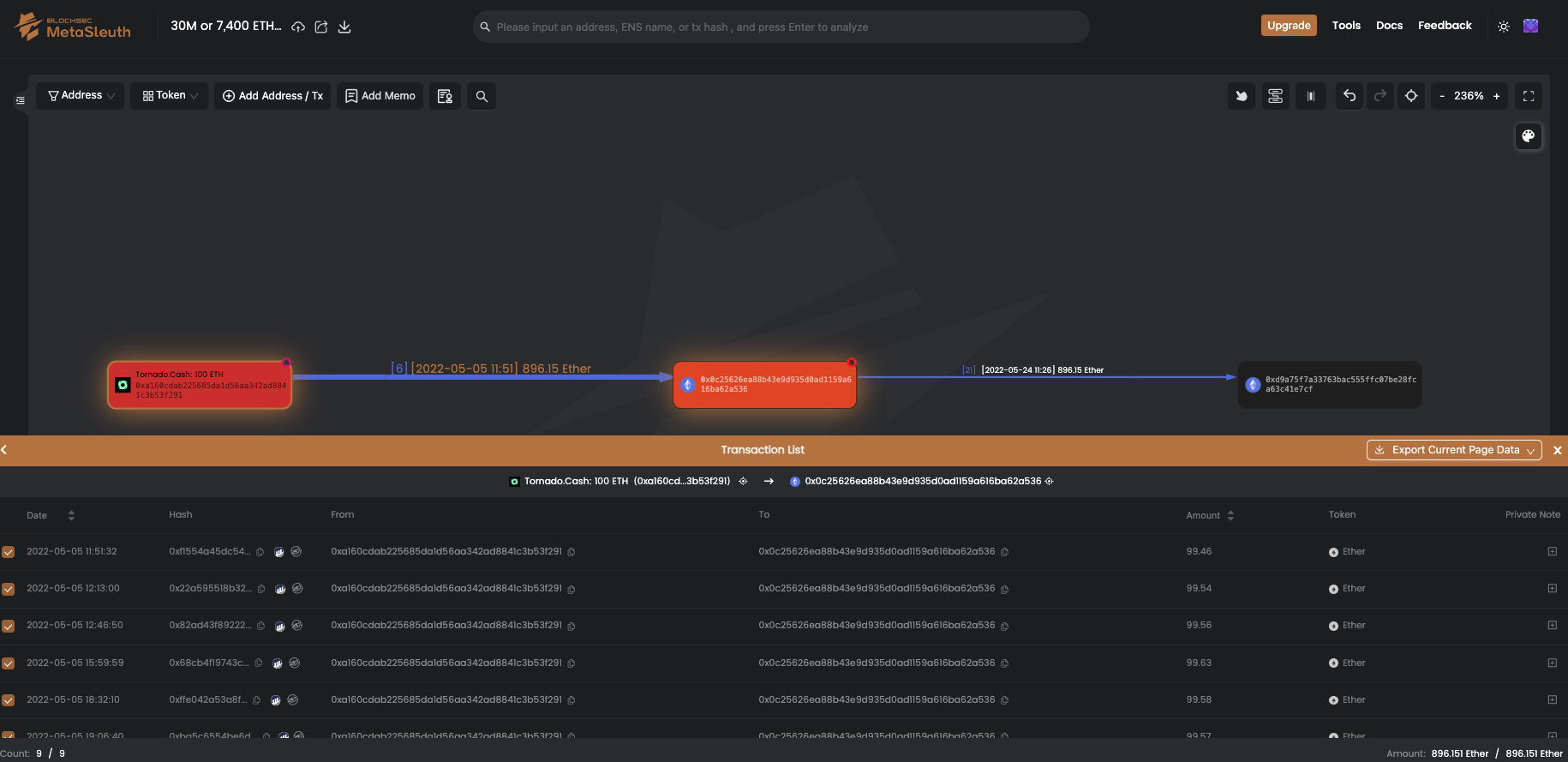
Let's explore further what happened with the money. A substantial amount of ether has been deposited, and sorting icons help track the order of transactions by age. We can observe that a vast sum, around 900 ether worth approximately $3.6 million, has been transferred in and then out to another address.
By analyzing this next address, we can discern a pattern of transactions. Given the limited number of transactions, we may infer it's the same person involved. We'll start a new color scheme to track these transactions. Each color can represent different entities, such as purple for centralized exchanges, white for smart contracts, red for attackers, green for victims, and others as needed.
We still suspect this is the attacker, so we'll color them yellow to follow the trail of funds. We notice several deposits to Binance, which is critical because that centralized exchange deposit address will hold vital information accessible to law enforcement.

Conclusion
Metasleuth's strength lies in its ability to track the journey of assets. We can identify additional significant amounts of ether being moved. To give you an idea of the scale, this closed loop of money laundering through Tornado Cash is about 7,400 ether, or roughly $30 million, all routed through exchanges like Kraken, Simple Swab, and Binance.
In essence, MetaSleuth facilitates the visualization and analysis of complex transaction networks, aiding in the identification and tracking of illicit funds flows.




