On March 13, 2023, Euler Finance, a decentralized finance (DeFi) lending protocol on Ethereum, experienced a flash loan attack resulting in losses of approximately $200 million. The root cause was identified as the absence of a liquidity check in the donateToReserves() function. As a blockchain security company, BlockSec continuously monitors such exploits to improve DeFi security and protect digital assets.
| Date | Attack Type | Chain | Lost | Recovered |
|---|---|---|---|---|
| 2023-03-13 | Business Logic Flaw | ETH | ~$200M | Yes |
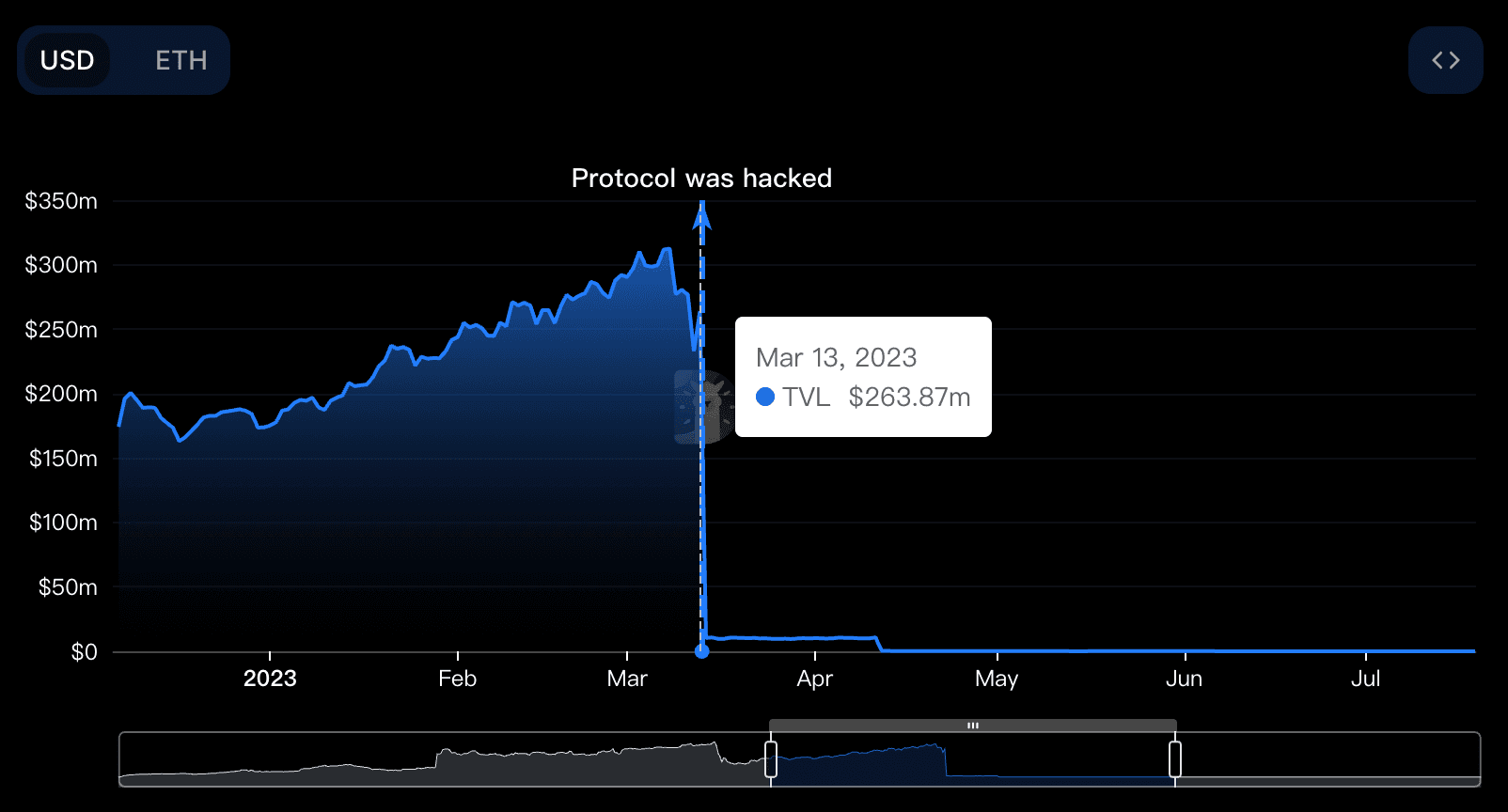
Euler Finance was ranked among the top 30 DeFi protocols on DefiLlama before the attack. Its total value locked (TVL) dropped dramatically from $264 million to $10 million, a 96% decline.
Key Concepts
Understanding Euler Finance’s self-borrow and soft liquidation mechanisms is essential to grasp the exploit:
- Self-borrow: Allows users to mint new assets and increase debt by using newly minted EToken as collateral, effectively enabling leverage.
- Soft liquidation: Permits liquidators to repay debt flexibly for the liquidated party, rather than using a fixed liquidation coefficient.
These mechanisms, while innovative, introduced exploitable vulnerabilities that the attacker leveraged.
Attack Analysis
The attacker executed the exploit through the following steps:
- Flashloaned 30M DAI from AAVE.
- Deposited 20M DAI into Euler Finance and received 20M eDAI.
- Leveraged Euler’s borrowing capability to mint 195M eDAI and 200M dDAI.
- Repaid 10M debt to mint more eDAI, holding 215M eDAI and 190M dDAI.
- Repeated step 4, increasing holdings to 410M eDAI and 390M dDAI.
- Invoked the
donateToReserves()function to donate 100M eDAI.
function donateToReserves(uint256 amount) external {
// Missing liquidity check allows exploit
// Function logic here
}During this process, the attacker’s health factor was not verified, allowing liquidation of their own position to gain profit. The attacker liquidated themselves, extracting 38M eDAI, and repaid the flashloan.
The exploit was a flash loan attack exploiting a business logic vulnerability in the smart contract.
Summary
The core issue was the missing liquidity check in the donateToReserves() function combined with a dynamic liquidation discount mechanism. This created an arbitrage opportunity, enabling the attacker to exploit a large amount of crypto assets without proper collateral or debt repayment.
Follow-up Steps
Remarkably, approximately $135 million of the stolen funds—mainly staked Ether (stETH), Bitcoin, and stablecoins like DAI and USDC—were fully recovered. The attacker was a 19-year-old Argentine named Federico Jaime, who returned all stolen assets three weeks later for moral reasons.[1]
BlockSec has been actively monitoring the incident. Our official Twitter accounts @BlockSecTeam and @MetaSleuth provided continuous updates. On March 18, 2023, the attacker returned 3,000 Ether, followed by 51,000 Ether a week later, with remaining funds returned in subsequent days.
During the refund process, phishing scams emerged exploiting the incident. Fraudsters created a phishing site, eulerrefunds.cxx, tricking some users.
MetaSleuth, BlockSec’s high-performance cross-chain fund flow analytics tool, enabled near real-time tracking of affected digital assets during the attack and refund phases.
More on Blockchain Security
This case is one of many illustrating the critical need for robust blockchain security. BlockSec offers comprehensive security services for blockchain projects, including:
- Smart Contract Audits during development to identify vulnerabilities.
- Phalcon Security, a SaaS platform providing incident alerts and automatic blocking to prevent crypto hacks.
- MetaSleuth, for enhanced traceability and transparency of digital assets.
- Infrastructure Audits to secure the underlying blockchain environment.
Best Security Auditor for Web3
Validate design, code, and business logic before launch
Reference
[1] HE STOLE $200 MILLION. HE GAVE IT BACK. NOW, HE’S READY TO EXPLAIN WHY




