On February 2nd, 2023, BonqDAO on Polygon was attacked, resulting in losses of approximately 98.6M BEUR and 113M WALBT. After investigation, we found that the flawed logic used to determine the WALBT token price was the cause of the attack. As a blockchain security company, we closely monitor such exploits that can have far-reaching implications in the DeFi space.
| Date | Attack type | Chain | Lost | Recovered |
|---|---|---|---|---|
| 2023/2/1 | Flawed Price Dependency | Polygon | ~ $120 M | No |
1/ @BonqDAO on Polygon was hacked due to the flawed logic to determine the WALBT token price. Specifically, the attacker staked a small amount of TRB tokens and updated the WALBT token price afterward through TellorPriceFeed (0x8f55). While the updated price was used directly. https://t.co/ZD7M73L0uM pic.twitter.com/4qPLqGj6jY
— BlockSec (@BlockSecTeam) February 2, 2023
Project Introduction
BonqDAO (Bonq Decentralized Autonomous Organization) is a DeFi lending platform deployed on Polygon. Users can provide liquidity to the protocol or take out overcollateralized loans to earn yields, and then they can mint BEUR, a stablecoin pegged to the Euro.
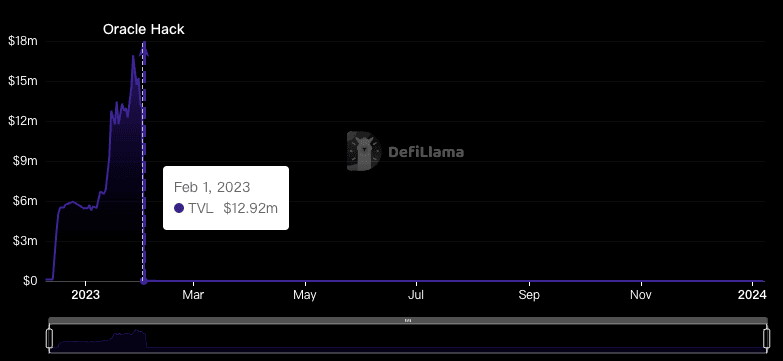
After this attack, BonqDAO's TVL plummeted from $13 million to $44,000, experiencing a 99.66% decline.
BonqDAO subsequently announced that the Bonq protocol had been suspended, and AllianceBlock and the Bonq team minted new ALBT tokens and airdropped them to affected users.
Attack Analysis
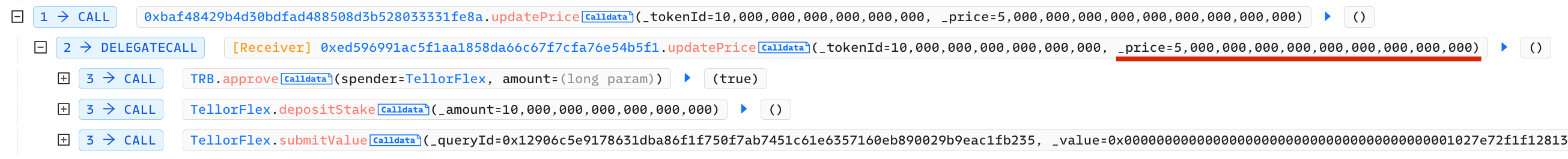
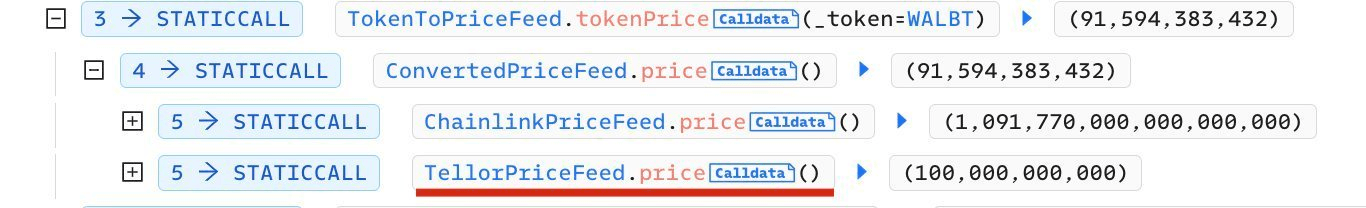
TellorFlex is the Oracle of BonqDAO. It is decentralized and anyone can become a price provider by staking only 10 TRB tokens and modify the oracle price at will.
The attacker carried out profits in two ways during this attack:
- Raise the WALBT's price and then borrow a massive amount of BEUR tokens
- Lower the WALBT's price and then liquidate other use’s WALBT.
The attacker's strategy can be broken down into the following key steps:
- Prepare funds
- The attacker staked a 10 TRB tokens and increased the price of WALBT tokens through
TellorPriceFeed (0x8f55).
- The attacker then deposits 0.1 WALBT and directly uses the updated price to obtain 100M BEUR.
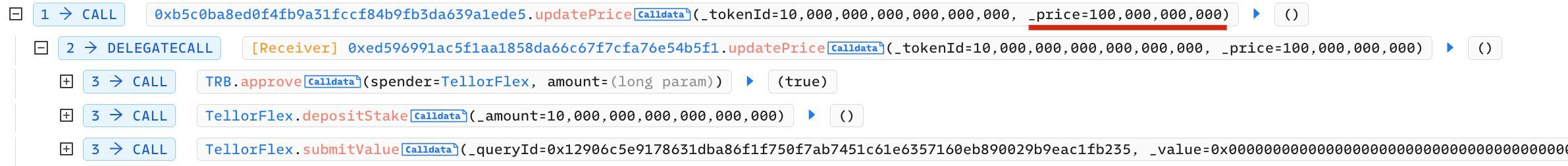
- The attacker used the same method to manipulate WALBT to drop to a low price, liquidate other BonqDAO users’ WALBT collateral, and then resell them for further profit.
Fund Tracking
As a company dedicated to maintaining blockchain security, we have also been closely monitoring the progress of this attack. (Our official Twitter account has been continuously reporting on this incident, and interested readers can follow our account @BlockSecTeam@MetaSleuth to track the movement of these funds together.)
MetaSleuth is a high-performance cross-chain fund flow analytics tool that enhances the transparency of blockchain transaction activity. It allows users to nearly real-time track the trail of affected digital assets. By leveraging MetaSleuth, we can clearly see the relevant fund flow tracking information during the occurrence and follow-up of this attack.
- The profit of the BonqDAO attacker was approximately 98.6M BEUR and 113M WALBT. Specifically, 113M WALBT was burned to unlock 113M ALBT from the ETH chain. Approximately 0.5M BEUR was swapped for 534,535 USDC and then swapped for Ethereum (0xcacf...6642). The attacker still had 98.1M BEUR remaining in their Polygon account.
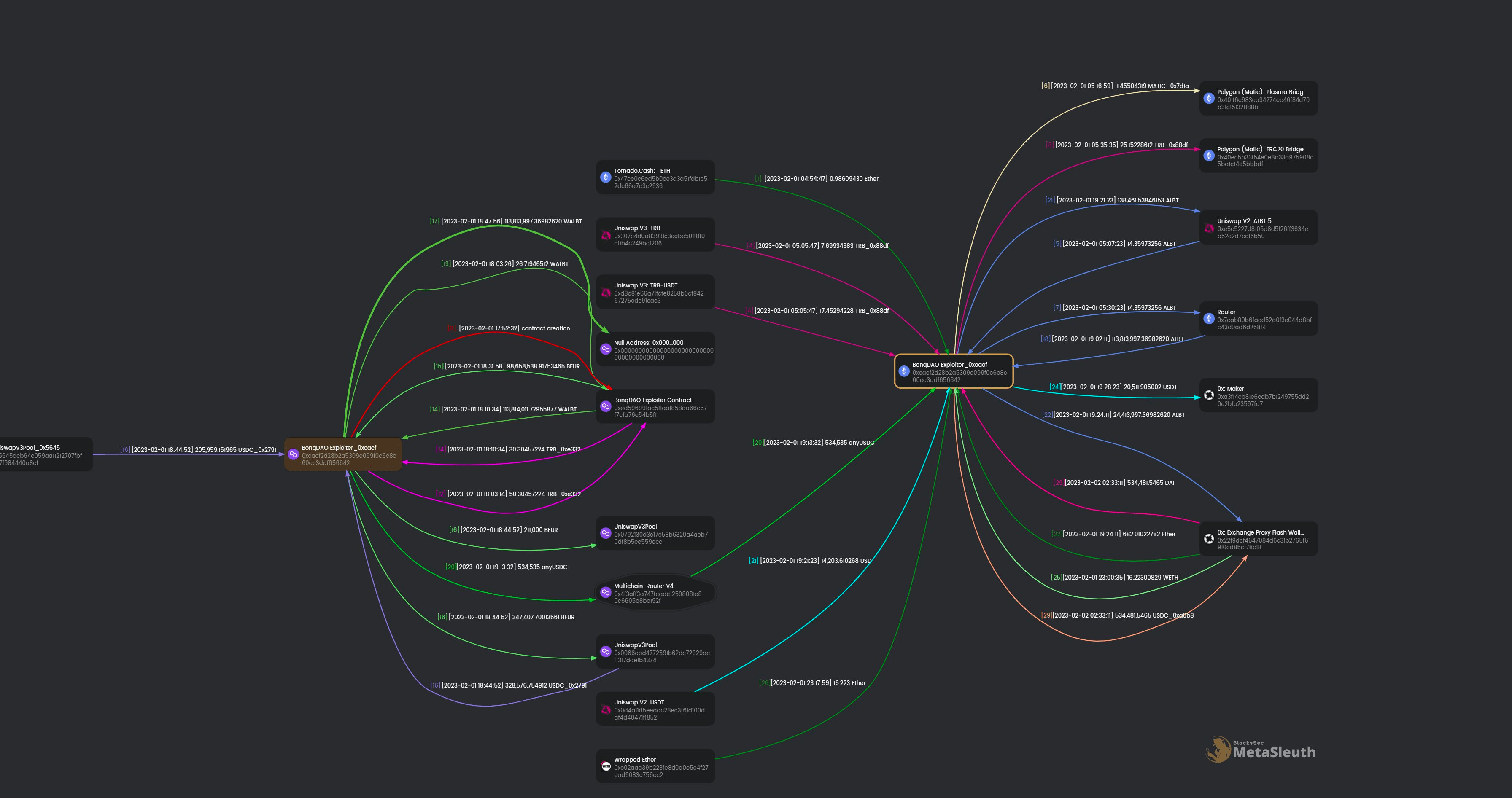
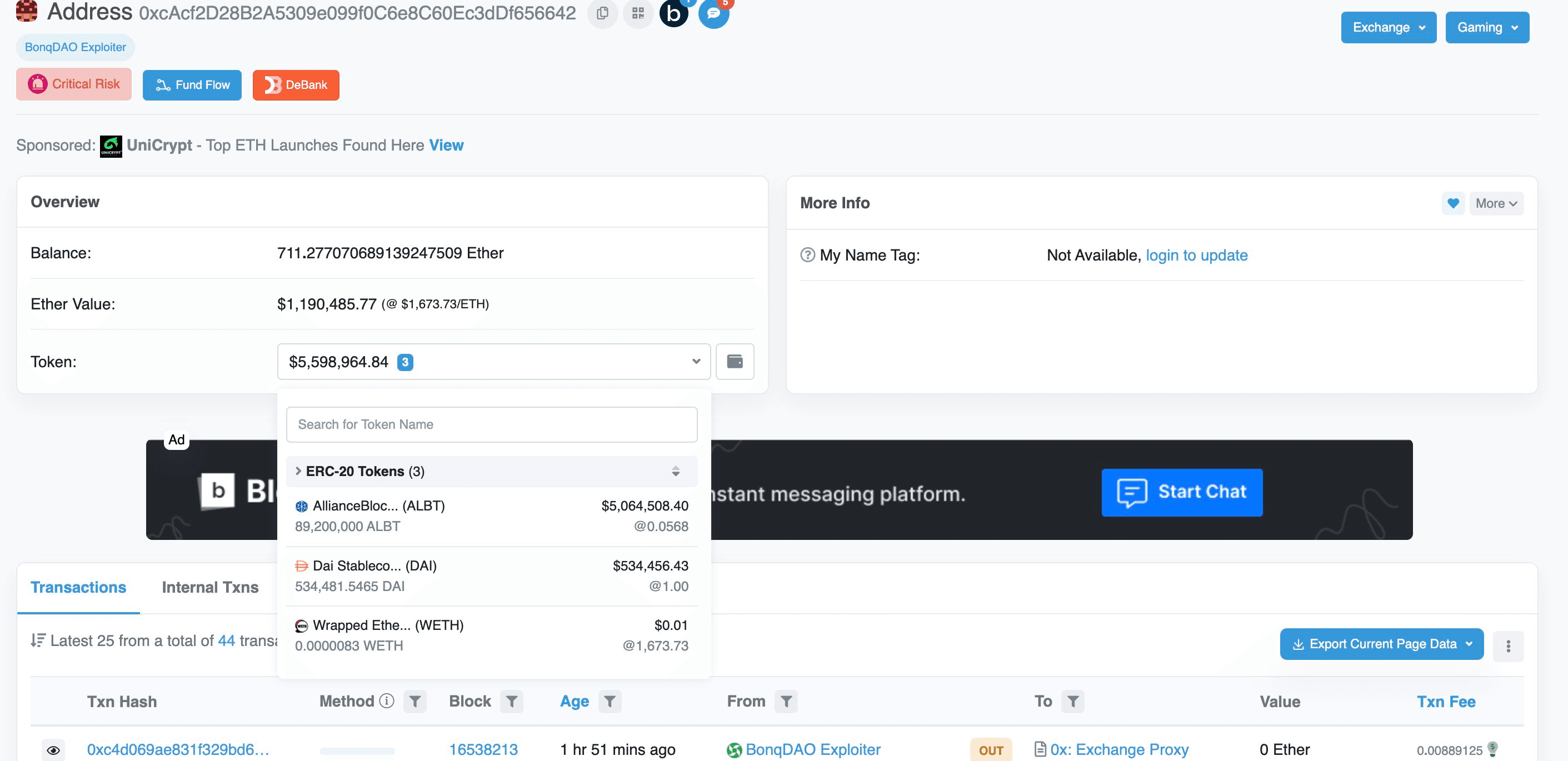
- Regarding the Ethereum address 0xcacf..6642 , it used 0xExchange(@0xproject ) to swap the received USDC for DAI. Additionally, WALBT is swapping into ETH/USDT using 0xExchange and Uniswap. The account currently holds 711 ETH, 534,481 DAI, and 89M ALBT.
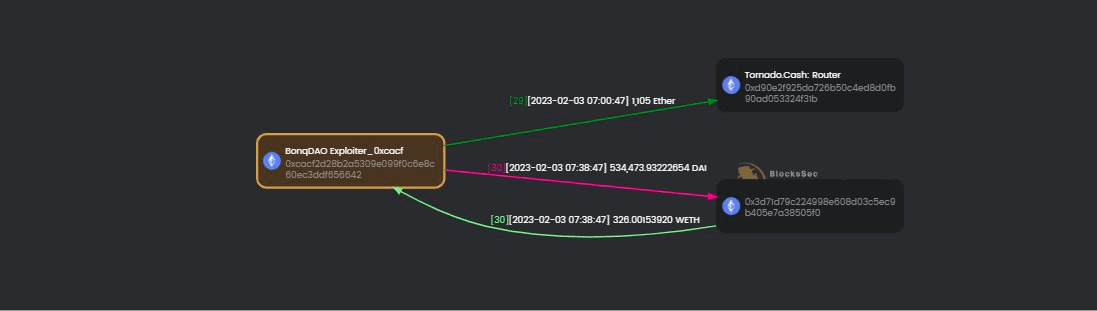
- On Feb 3, 2023, we detected that the attacker had swapped DAI for Ether and laundered 1,105 Ether via Tornado Cash.
Summary
The root cause of this attack is that the cost of collateral required for modifying the quotation of TellorFlex oracle is too low, and the amount of collateral borrowing in the Bonq lending contract is only related to the price reported by TellorFlex oracle. Therefore, attackers can modify the quotation at a relatively low cost and get considerable profits through collateral borrowing.
Read More
The above are just representative cases. In fact, we have more cases focusing on blockchain security analysis.
DeFi Exploit Analysis: The Root Cause of Euler's $200M Loss
About BlockSec
BlockSec offers a full stack security service for blockchain projects, providing assistance from pre-launch to post-launch and incident response. During the development and testing stages, Expert Code Auditing Services and the Phalcon fork testing platform are employed to help identify potential security issues. Ensure robust post-launch security for your blockchain project with BlockSec Phalcon. This streamlined SaaS platform offers incident alerts and automatic blocking to prevent crypto hacks. It employs precise attack detection, scanning both pending and on-chain transactions, allowing you to swiftly intercept hackers. Additionally, MetaSleuth is an intuitive crypto tracking and investigation platform that helps enhance the traceability and transparency of assets.




