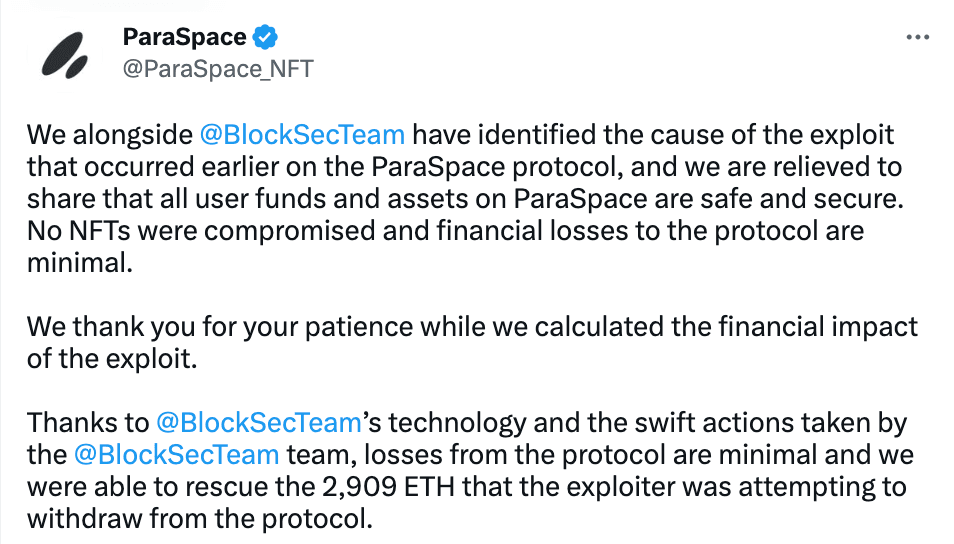
On 2023–03–17 05:48:59 (UTC), BlockSec successfully blocked an attack attempt on ParaSpace (a top NFT lending protocol) and protected crypto assets worth $5M.
As mentioned in the previous blog, we always believe a more proactive threat prevention solution can help to defend against the threats. We have deployed such a system internally in 2022. As of this writing, our system successfully blocked multiple attacks and saved around 14 million USD users’ assets.
See our perspective on proactive threat prevention in this article.
The feasibility and practice of our solution have been widely recognized by the community, and we have collaborated with some top-notch partners in the community. For example, we are working with Compound to develop a risk prevention system for Compound V3 smart contracts.
We always try to build blockchain security infrastructure for the Web3 community, including Phalcon Explorer (a transaction analysis tool for Web3 developers and security researchers), MetaDock (a security toolbox for Web3 users), and MetaSleuth (a fund tracing tool for Web3 users).

Learn more about BlockSec: Website | Document | Twitter | Medium | TG Group



