On January 2, 2021 (Beijing Time 07:25 am), our monitoring system ThunderForecast reported a series of suspicious transactions towards the yCREDIT smart contract. Then, we used the EthScope system developed by our research team to analyze these transactions and confirm that all reported transactions are malicious. In this blog, we illustrate the attack details.
Details
The attack is due to the number of tokens minted is inconsistent with the intended one. As such, the attacker can get many more yCREDIT tokens with lower price. Then these tokens can be sold to gain profits.
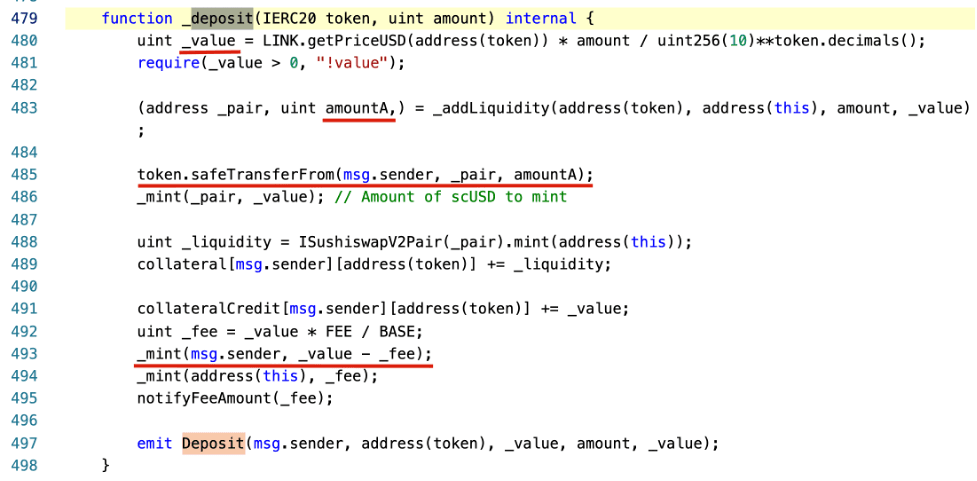
The vulnerable function is in the _deposit function of the StableYieldCredit contract.
In the following, we will use an attack transaction to illustrate the whole process.
The attacker first transferred 1e-8 WBTC and 331.335 yCredit tokens to the WBTC-yCREDIT Pair pool. Then the attacker deposited 0.5 WBTC to the StableYieldCredit contract to launch the attack.
Specifically, the _value is calculated using the amount (0.5) of the token (0x2260fac5e5542a773aa44fbcfedf7c193bc2c599 - WBTC) based on the price oracle provider ChainLink (line 480, _value is 1466786010075). The intention is to calculate the value of the deposited WBTC in USD. Then the contract will transfer the number of yCREDIT tokens (_value - fee) to the one who deposited the WBTC (the attacker). That's because the value of yCREDIT equals one USD (as designed by the system). Everything is fine except the attacker loses a small amount of fee.
Moreover, the contract will add the deposited WBTC to the WBTC-yCREDIT Pair pool. That's because if the deposited WBTC is locked into the contract, it will lose liquidity. As such, it first calculated the value of the token pair (WBTC to yCREDIT) that will be put into the pool. This value is calculated using the function _addLiquidity. Basically, it is calculated based on the existing reserves inside the pool. Since the pool only has 1e-8 WBTC and 331.335 yCREDIT tokens, the amountA calculated is 44 (amountB is 1466786010075). That means the attacker only spends 44e-8 WBTC (line 485) and gets 14667.86010075 - fee = 14594.52080025 yCREDIT tokens (line 493). At the same time, there is a small number of WBTC (1e-8 + 44e-8) and (331.335 + 14667.86010075) yCREDIT tokens leaving in the pool.
To get profits, the attacker can simply trade the gained 14594.52080025 yCREDIT tokens in exchanges. Interestingly, the process to gain profits in this transaction is far more complicated than necessary. We have also observed a clever attacking strategy in other transactions.
There are a serial of transactions involved in the attack, including (but not limited to) the following ones.
Update
2020/01/03: There is an new smart contract that fixes the vulnerability.
Timeline
- 2021/01/01 23:25 UTC, attacks were captured by our system
- 2021/01/02 16:20 UTC, this blog is released




