Solidity by Example is a fantastic resource for beginners who are looking to learn Solidity. The website offers numerous examples of source code that developers can utilize and test. The source code can be easily accessed and compiled using the online Remix tool.
In this tutorial, we will explore how to use Phalcon Fork to deploy the compiled contract, send transactions, and debug a transaction using Phalcon Explorer.
Compile The Re-Entrancy Contract
The contract we are using is the demo of the re-entrancy vulnerability and how to attack it. We won’t go through the details of this vulnerability, and there are many useful documents on the Internet.
We first open it on Remix and then compile the contract.

Add Fork RPC
We will use the Injected Provider to use Fork RPC. Please refer to this document for the detailed steps to use Phalcon Fork in Remix. In this case, I have added MetaMask as the injected Provider and used the account 0xb469Efca360131361487F0d4e072EFF758Fcd700 as a testing account.
I also used the Faucet to add enough Ether into this account to have enough gas fees. In this case, I added 22 Ether into this testing account (feeling very good to be rich 😄).
Deploy the contract
We first deploy the EtherStore contract (the vulnerable one) and then deploy the Attack contract.
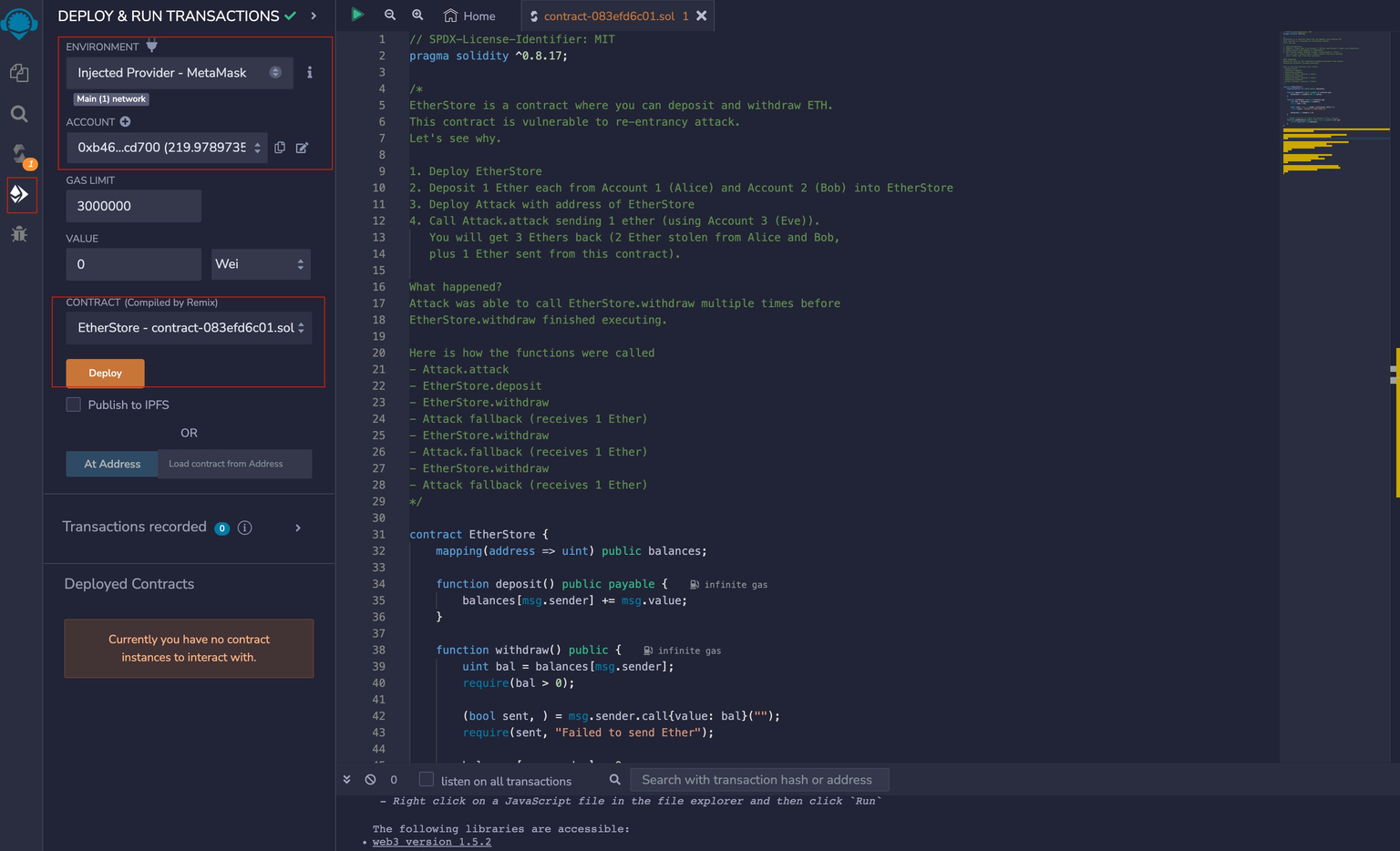
Deploy the EtherStore contract.

Sign the transaction to deploy the contract. Ensure that the RPC is the added Phalcon Fork RPC (the top right of the MetaMask Notification). Otherwise, it will deploy to a new network! Please double-check before clicking Confirming.
The transaction to deploy the contract can be seen in the transaction list of the Fork.
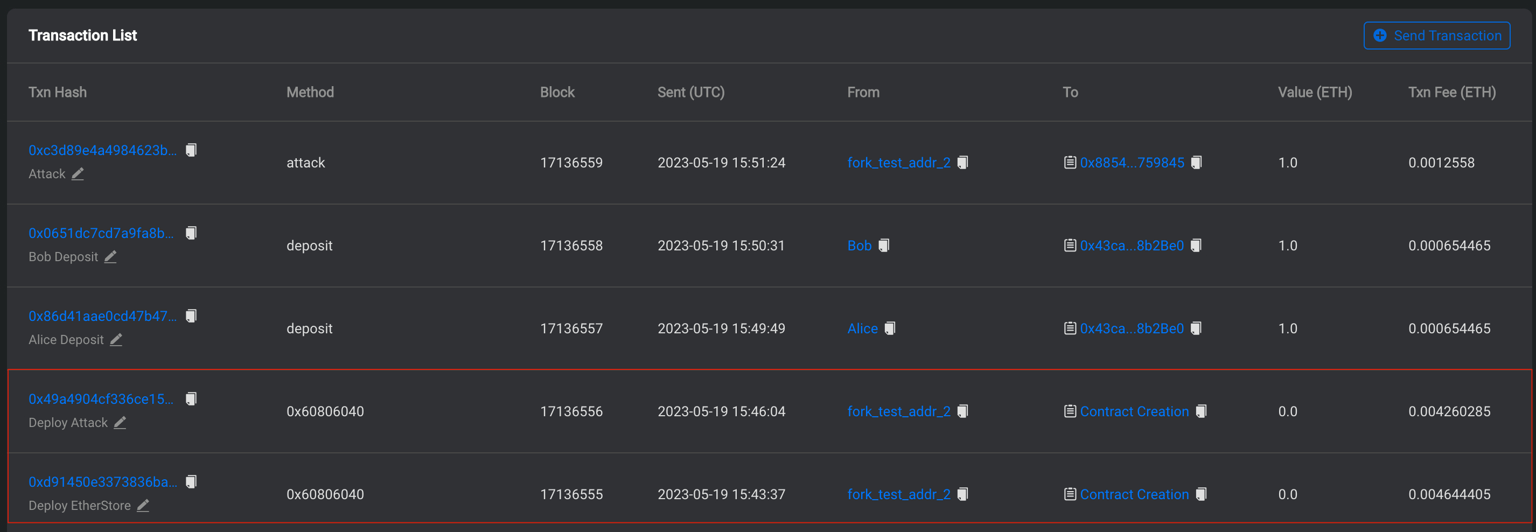
We can use a similar method to deploy the Attack contract. When deploying the attack contract, we must pass an argument (the deployed EtherStore contract address, 0x43caeBEBCe80117B5cA00047a97eD48b928b2Be0 in this case).
Launch the attack
Before launching the attack, two users need to deposit the Ether into the vulnerable contract. We use two addresses for this purpose.
-
Alice:
0x123456781111b5f74706be8d79cde3e4247dd800 -
Bob:
0x123456781111b5f74706be8d79cde3e4247ddb0b
Thanks to the Faucet, we add 2 Ether into Alice and Bob and then invoke the deposit function to deposit 1 Ether from each user into the EtherStore contract.
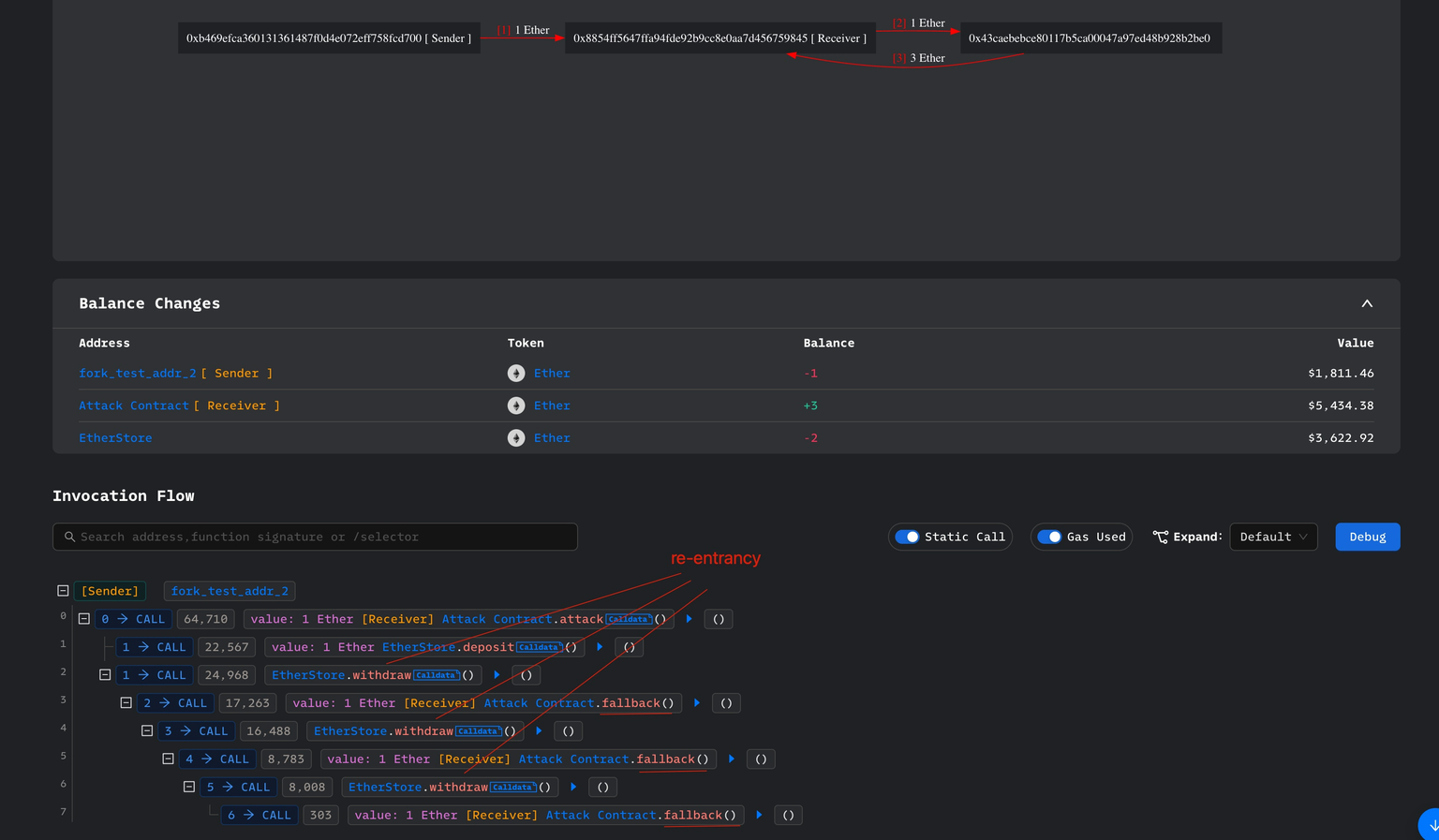
Then we launch the attack method of the Attack contract and send 1 Ether. The attack transaction can be viewed using the Phalcon Explorer in the Phalcon Scan for the Fork.
Summary
In this tutorial, we show how to use the Phalcon Fork to deploy and launch the re-entrancy attack, using the example code from the Solidity by Example.




