
Gain Early Access to Precise Attack Intelligence
Early Detection
Cover Mempool and on-chain transactions, monitor for malicious proposals and contracts, and more.

Precise Detection
Leverage DeFi semantics and AI algorithms to achieve high precision.

Automated Attack Blocking with Customized Actions
Automated Actions
Implement swift and automatic responses to threats.

Multi-Signature Support
Enable automated actions with multi-signature wallets.

Transaction Sending Strategy
Utilize private RPC, gas bidding, and set gas price limits to counteract attacks.

No-Code, Flexible Monitoring Rules Configuration
Ease of Use
Monitor transactions, functions, events, and variables easily without the need for coding.

Pre-Set Templates
Access a variety of monitoring templates covering major security issues for protocols including Lending, DEX, Restaking, Liquid Staking, etc.

Meet Both Security and Operational Monitoring Requirements
Comprehensive Monitoring
Keep an eye on changes to admin keys, role grants, key variables, contract upgrades, time lock, new proposals and price oracles.
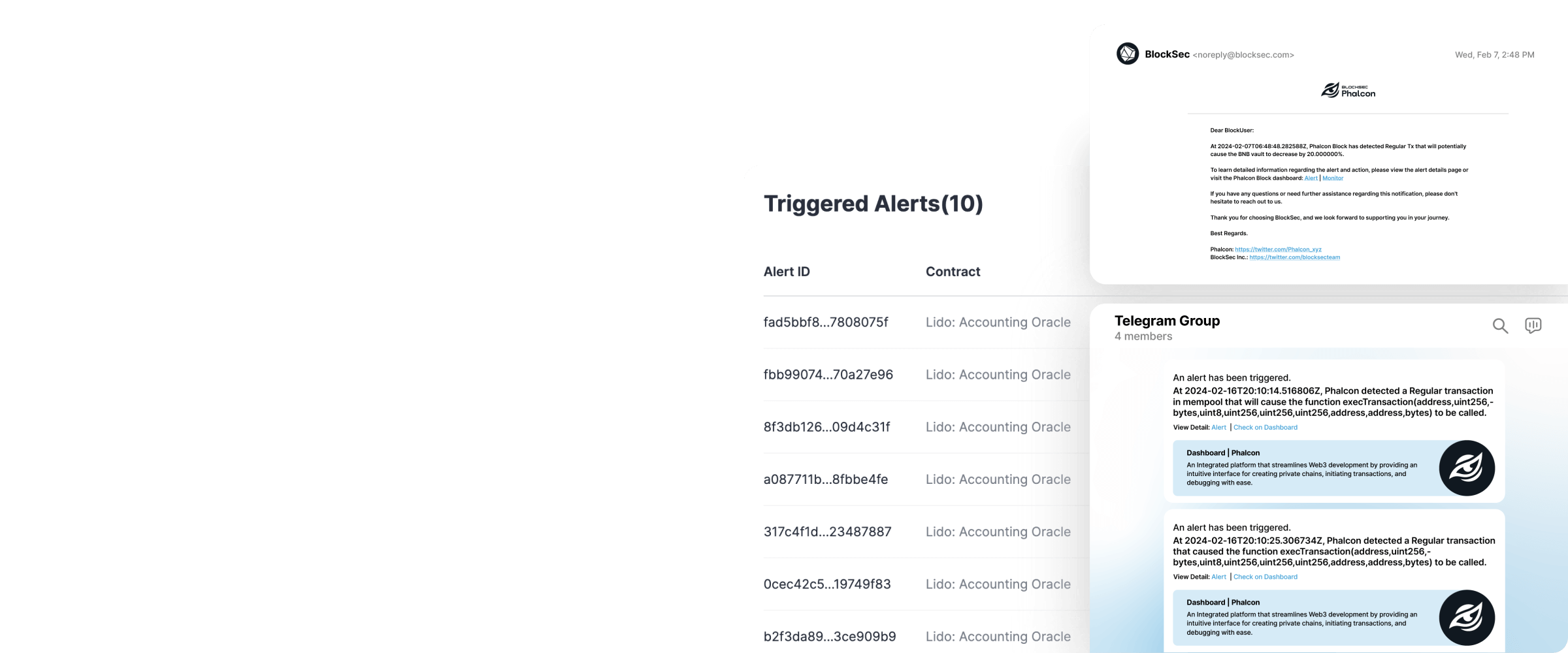
Diverse Notification Channels
Receive alerts through multiple channels including webhooks, Telegram, Slack, email, and more.
Use cases
Three Steps to Navigate Phalcon
Phalcon Toolset
Phalcon Explorer
Dive into Transactions to Act Wisely
A virtualization tool that facilitates the analysis of complex transactions, essential for understanding attack transactions.
Learn morePhalcon Fork
Collaborative testing on mainnet forked chains
A testnet designed for collaborative development and public-mode testing.
Learn more